
Welcome to the DCG 201 Guides for Hacker Summer Camp 2023! This is part of a series where we are going to cover all the various hacker conventions and shenanigans both In-Person & Digital! This year in 2023 somehow bigger than it was in 2022 and thus we will have a total of 15 guides spanning 3 Months of Hacker Insanity!
As more blog posts are uploaded, you will be able to jump through the guide via these links:
HACKER SUMMER CAMP 2023 — Part One: Surviving Las Vegas & Virtually Anywhere
HACKER SUMMER CAMP 2023 — Part Two: Capture The Flags & Hackathons
HACKER SUMMER CAMP 2023 — Part Three: SummerC0n
HACKER SUMMER CAMP 2023 — Part Four: Zero Gravity by RingZero
HACKER SUMMER CAMP 2023 — Part Five: The Diana Initiative
HACKER SUMMER CAMP 2023 — Part Six: BSides Las Vegas
HACKER SUMMER CAMP 2023 — Part Seven: Black Hat USA
HACKER SUMMER CAMP 2023 — Part Eight: SquadCon by Black Girls Hack
HACKER SUMMER CAMP 2023 — Part Nine: DEFCON 31
HACKER SUMMER CAMP 2023 — Part Ten: USENIX + SOUPS
HACKER SUMMER CAMP 2023 — Part Eleven: Chaos Computer Camp
HACKER SUMMER CAMP 2023 — Part Twelve: Wikimania 2023
HACKER SUMMER CAMP 2023 — Part Thirteen: HackCon XI
HACKER SUMMER CAMP 2023 — Part Fourteen: Blue Team Con
HACKER SUMMER CAMP 2023 — Part Fifteen: Hack Red Con
HACKER SUMMER CAMP 2023 — Part Sixteen: SIGS, EVENTS & PARTIES

BLACK HAT USA 2023
Date: Saturday, August 5th (8:00 AM PST) — Thursday, August 10th (6:00 PM PST)
Website: https://www.blackhat.com/us-23/
Location: Mandalay Bay Convention Center (3950 Las Vegas Blvd. South Las Vegas, Nevada 89119)
Black Hat USA Android App: https://play.google.com/store/apps/details?id=com.swapcard.apps.android.blackhat&hl=en_US&gl=US
Black Hat USA iOS App: https://apps.apple.com/us/app/black-hat-events/id1521865489
Platform(s): Black Hat USA CISO Summit as well as the Main Conference including Briefings, Arsenal, the Business Hall, and more, will take place on the Swapcard Virtual Event Platform. Black Hat USA Trainings will be taught online on the GoToTraining virtual classroom platform..
Schedule: https://www.blackhat.com/us-23/briefings/schedule/index.html
Live Streams:
Youtube (KEYNOTES): https://www.youtube.com/user/BlackHatOfficialYT
— Dark Reading —
Wednesday: https://www.youtube.com/watch?v=NE5eBInuZaw
Chat: TBA
Accessibility: Only registered attendees will be able to view the Briefings (Talks) and Workshops attendance not only have a price tag but are filled in by a case-to-case basis. Virtual Business Pass is free and gets you access to the rest of the convention including the Business Hall, Arsenal, Contests, Sponsored Talks and more. See deals for In-Person Vegas later in this guide.
Tickets: https://www.blackhat.com/us-22/registration.html
Code Of Conduct: https://www.blackhat.com/code-of-conduct.html
From its inception in 1997, Black Hat has grown from a single annual conference in Las Vegas to the most respected information security event series internationally. For more than 20 years, Black Hat Briefings have provided attendees with the very latest in information security research, development, and trends in a strictly vendor-neutral environment. These high-profile global events and Trainings are driven by the needs of the security community, striving to bring together the best minds in the industry.
Now in its 26th year, Black Hat USA returns to the Mandalay Bay Convention Center in Las Vegas with a 6-day program. The event will open with four days of specialized cybersecurity Trainings (August 5–10), with courses for all skill levels. The two-day main conference (August 9–10) will feature more than 100 selected Briefings, dozens of open-source tool demos in Arsenal, a robust Business Hall, networking and social events, and much more!
Continuing it’s organizational structure since the 2020 Pandemic Lock-down, the Black Hat hybrid event experience in 2023 offers the cybersecurity community a choice in how they wish to participate. They will host both an in-person experience in Las Vegas and a virtual experience online. When you purchase a Briefings Pass, you can select whether to attend in-person or online.
If you choose the Virtual Only Briefings Pass, you will have access to all the online and recorded Briefings Sessions, Sponsored Sessions, Arsenal Demos and the Business Hall. You will also have access to the recorded sessions for 30 days after the event.
If you choose the In-Person Briefings Pass you will have access to BOTH the in-person Briefings, Sponsored Sessions, Arsenal Demos and the Business Hall activities in Las Vegas, AND access to all the online sessions, including online access to the recordings for 30 days after the event.
This is the BIG corporate convention of the Information Security world. Very suit and tie, bring your resume, talking about numbers and projections type of convention. Get use to hearing the words “cyber”, “mitigation”, “”deployment” “corporate”, “blockchain” and “pipeline” being thrown around like candy on Halloween without eye roll. Attendees will also introduce them selves with their job title and workplace as if they are their last names.
We are happy that the accessibility options of attending in-person or virtually online fromlast year has returned. From the Business Pass being completely free, reduced (but still expensive for Blue Collar prices) and various way to interact these inclusive elements has put the convention back on our radar. If you want to network and rub shoulders with the InfoSec big leagues (or to land a job), this is the convention that will be on your priority list!
PHYSICAL LOCATION RECON


BRIEFINGS PASSES
Briefings Dates: Wednesday, August 9 — Thursday, August 10
There are 2 different Briefings Pass options for 2023.
OPTION 1 — IN-PERSON EVENT at Mandalay Bay Convention Center, Las Vegas, NV
- Includes access to all in-person Briefings, Arsenal Demos, Business Hall Activities & Sessions and more
- Also includes ALL ON-DEMAND benefits listed in Option 2 below
OPTION 2 — ON-DEMAND ACCESS
- Available online one week after live event: August 16 — September 18, 2023
- Includes access to all recorded Briefings, Arsenal Presentations, Business Hall Activities & Sessions and more!
REGISTRATION HOURS
- Saturday, August 5th: 9:00 AM –4:00 PM
- Sunday, August 6th: 8:30 AM — 4:00 PM
- Monday, August 7th: 8:00 AM — 5:00 PM
- Tuesday, August 8th: 8:00 AM — 6:00 PM
- Wednesday, August 9th: 8:00 AM — 5:00 PM
- Thursday, August 10th: 8:00 AM — 4:00 PM
TRAINING PRICES
Training Dates: Saturday, August 5 — Tuesday, August 8
Please check individual Training description pages for Training prices and dates.
All Pricing is in US Dollars (USD) and includes full access to the Black Hat Business Hall on August 8–10. Pricing does not include applicable local taxes.
BUSINESS PASSES
Business Hall Dates: Wednesday, August 9 — Thursday, August 10
There are 2 different Business Pass options for 2023.
OPTION 1 — IN-PERSON EVENT at Mandalay Bay Convention Center, Las Vegas, NV
- Includes access to all Business Hall Activities, Arsenal Demos, Sponsored Sessions and more
OPTION 2 — VIRTUAL EVENT available online
- Includes online access to the Virtual Business Hall, Arsenal Demos, Sponsored Sessions, Sponsored Workshops, and more.
Business Passes do not include Briefings access.
ACADEMIC REGISTRATION
Academic Pass registration is open to any member of the academia who can prove they are either a full-time student or full-time professors at an accredited university. An academic pass gives students and professors access to the Black Hat Briefings during the 2023 series of events.
We welcome those members of the academic community who can provide a valid, accredited university ID and meet any one of the additional criteria below, to apply for the academic rate to attend Black Hat Briefings.
STUDENTS
- Verifiable full-time academic status at an accredited college or university. Full-time students are 9 hours graduate or 12 hours undergraduate.
- Valid University ID
FULL-TIME UNIVERSITY PROFESSOR
- University webpage showing the registrant is a full-time (not adjunct) professor.
- Letter from the registrant’s department head on university letterhead stating full-time status.
RESTRICTIONS
- Standard Terms & Conditions Apply.
- Academic registration may be granted for the Briefings only.
- There are no Academic rates available for Training.
- Academic rate registration is not eligible to combine with any other discounts or promotions.
- Online registration only.
Academic Registrations are ONLY accepted in advance of the event, the deadline to apply is Friday July 22, 2023 by 4:00 PM PT. After this date and time, no further requests will be considered, including on-site. All academic registration requests and required documentation must be received on or prior to July 22, 2023 by 4:00 PM PT.
ATTEND BLACK HAT CHEAP-AS-FREE!
This year thanks to the hybridization, there is some amazing discounted and FREE options available for those of us hackers who want to rub shoulders (6 feet apart of course) with the dapper folks without breaking our already sparse checking accounts.
In-Person Business Passes is $625 (Increased to $650 After August 4th) this year and the Online Business Pass is FREE. With a Business Pass, access the Keynote, the Business Hall and a number of Features, including Arsenal, Sponsored Sessions, Passport to Prizes, and more.
EFF Members attending in-person can get $200 off briefing tickets by using code “EFF2023” when registering online.

EARLY DEF CON 30BADGE REGISTRATION
Upon purchase of Black Hat Briefings and/or Trainings passes, each registrant will also have the option to purchase a single (1) advance ticket to DEF CON 2022, at a rate of $360 per ticket, one ticket purchase per person, up until the close of “Late” registration on August 4, 2022 at 11:59 PM PT.
DEF CON tickets will not be sold on-site at Black Hat USA. After August 4, 2022, DEF CON tickets are only available for purchase at DEF CON during their ticket sales window.
Please note, you must first register and pay for your Black Hat Training/Briefings registration in order to purchase a DEF CON ticket. The option to purchase a DEF CON ticket is not available to individuals who purchase a Black Hat Business Pass only.
DEF CON tickets are non-refundable, once purchased. When you check in to Black Hat, you will receive a DEF CON badge voucher, and after DEF CON staff provide badges to Black Hat, you may then redeem your voucher for a DEF CON badge, generally on the Thursday of the event.

DEF CON BADGE PICKUP
Thursday, August 11, 2022
7:00 AM — 6:00 PM
Mandalay Bay Ballroom Foyer, Level 2
Step 1: Attendees will present their Black Hat badge with DEF CON symbol to staff.
Step 2: Your badge will be hole punched as proof of pick-up.
Step 3: Staff will hand you your badge.
ON-DEMAND & VIRTUAL PLATFORM RESOURCES
Black Hat USA 2023 will offer an on-demand and virtual component. We have provided information and resources below to make your experience at Black Hat a successful one. Please contact Black Hat Registration with any questions or for more information.
When the platform goes live, you will receive an email with a link directing to a login page where you can create a password for accessing the virtual event.
Please note that your event login information will come in an email from
Sender: “Black Hat USA <hello@swapcard.com>”
You should add hello@swapcard.com to your allowed email list to ensure receipt of your login details.
CREDENTIALS
You can access the Swapcard platform directly at login.swapcard.com.
There you can log in by entering the email you used to register for Black Hat USA and creating a password. If you’ve forgotten your password, click on “Send me a magic link” to receive an email to reset your password.
SETTING YOUR PROFILE VISIBILITY
Your profile will be automatically created in Swapcard using the information you supplied when you registered for the event.
You have the option to connect with other attendees and sponsors, just as you would at a live event.
Once you’ve logged into the platform, click on the “Attendee” tab. On the left side of the page, look for the “Visibility” setting to turn your Profile visibility on or off. You may change this setting at any time.

SESSIONS
Learn how to access sessions and content:
NETWORKING
Learn how to network with other attendees:
INTERACTING
Learn how to find virtual exhibit booths:
STAY CONNECTED
In addition to all of the chat and networking opportunities within GoToTrainings and Swapcard, you can stay up-to-date and join the conversations on social media by following and tweeting @BlackHatEvents, using the hashtags #BlackHat, BlackHatUSA, BlackHat2022, #BlackHat22, #BHUSA and #BHTrainings.
TRAININGS VIRTUAL PLATFORM (AUGUST 5 — AUGUST 8)
All Black Hat USA Trainings listed as Virtual will be taught live online via Zoom. Sessions will not be recorded. All courses are presented in Pacific Time (GMT/UTC -7h). Please email blackhatregistration@informa.com if you have any additional questions.
ON-DEMAND PLATFORM (AUGUST 16 — SEPTEMBER 18)
Black Hat USA programs and features including Briefings, Arsenal, Sponsored Sessions & Workshops, the Business Hall, and more will be record on-site in Las Vegas and then made available on-demand on the Swapcard Platform. The on-demand platform content will be available one week after the in-person event. All paid pass holders will receive an email with a link directing to a login page where you can create a password for accessing the on-demand platform.
MAIN CONFERENCE PLATFORM (AUGUST 9 & 10)
Black Hat USA Main Conference including Briefings, Arsenal, the Business Hall, and more, will take place on the Swapcard Virtual Event Platform. When the platform goes live, you will receive an email with a link directing to a login page where you can create a password for accessing the virtual event.
IN-PERSON RESOURCES
BOOKSTORE
August 7–10 | Breakers Registration Desk, Level 2
Come by the official bookstore at the Breakers Registration Desk, Level 2 and browse the latest titles in security. Several Black Hat Speakers and Trainers will be signing copies of their authored books. Brought to you by Professional Programs Bookstore.
Bookstore Hours:
- Monday, August 7: 8:00 AM — 6:00 PM
- Tuesday, August 8: 8:00 AM — 6:00 PM
- Wednesday, August 9: 7:30 AM — 6:00 PM
- Thursday, August 10: 8:00 AM — 6:00 PM

DAY CARE
Black Hat is excited to partner with leading childcare provider Kiddie Corp to offer Black Hat attendees access to an on-site children’s program. The Kiddie Corp program is for children ages 6 months through 12 years old and will be located within the Mandalay Bay Convention Center on the dates below:
- Saturday, August 5: 8:00 AM — 6:00 PM
- Sunday, August 6: 8:00 AM — 6:00 PM
- Monday, August 7: 8:00 AM — 6:00 PM
- Tuesday, August 8: 8:00 AM — 6:00 PM
- Wednesday, August 9: 8:00 AM — 6:00 PM
- Thursday, August 10: 8:00 AM — 6:00 PM
Advance registration is recommended. Availability is limited and handled on a first-come, first-served basis. Although every effort will be made to accommodate on-site registrations, there is no guarantee.
MERCHANDISE STORE
Get your Black Hat-branded T-shirts, jackets, mugs, and more at the Black Hat Merchandise Store located on Level 2. Purchases can be made with any major credit or debit card. Brought to you by Moxie Promo.
MOTHERS ROOM
NOTE FROM DCG 201 to Black Hat Staff: AGAIN THIS YEAR!? *sigh* Please call it Parenting Room next time. Dad’s & Enby’s are parents too!
A private facility for nursing mothers will be available within the Child Care room on Trainings & Briefings days, August 5–10. Additionally, a mothers room is available on Level 3 of the Mandalay Convention Center, in the Jasmine 1 Registration Office, Level 3.
PRAYER ROOM
A private prayer room is available on Level 3 of the Mandalay Convention Center, in the Jasmine 2 Registration Office, Level 3. The room will remain unlocked throughout the event and no reservation or notice is required for its use.
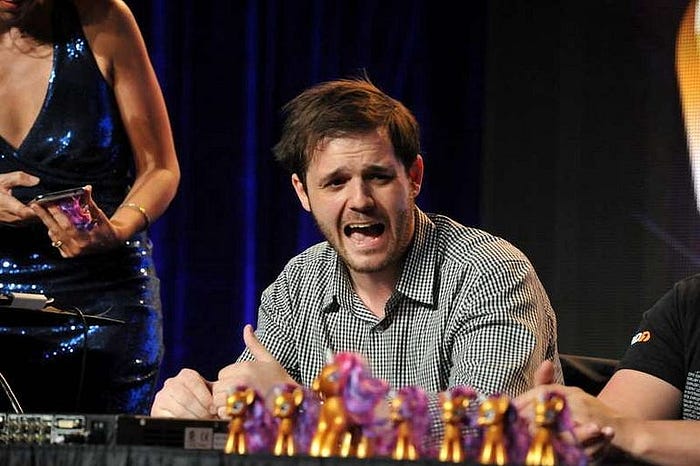
PWNIE AWARDS
Date: Wednesday, August 9 | 6:30pm-7:30pm ( Oceanside D, Level 2 )
Tracks: Pwnie Awards, Special Events
Black Hat USA will once again provide the venue for the Pwnie Awards, InfoSec’s premier award show celebrating the achievements and failures of the security community over the past year.
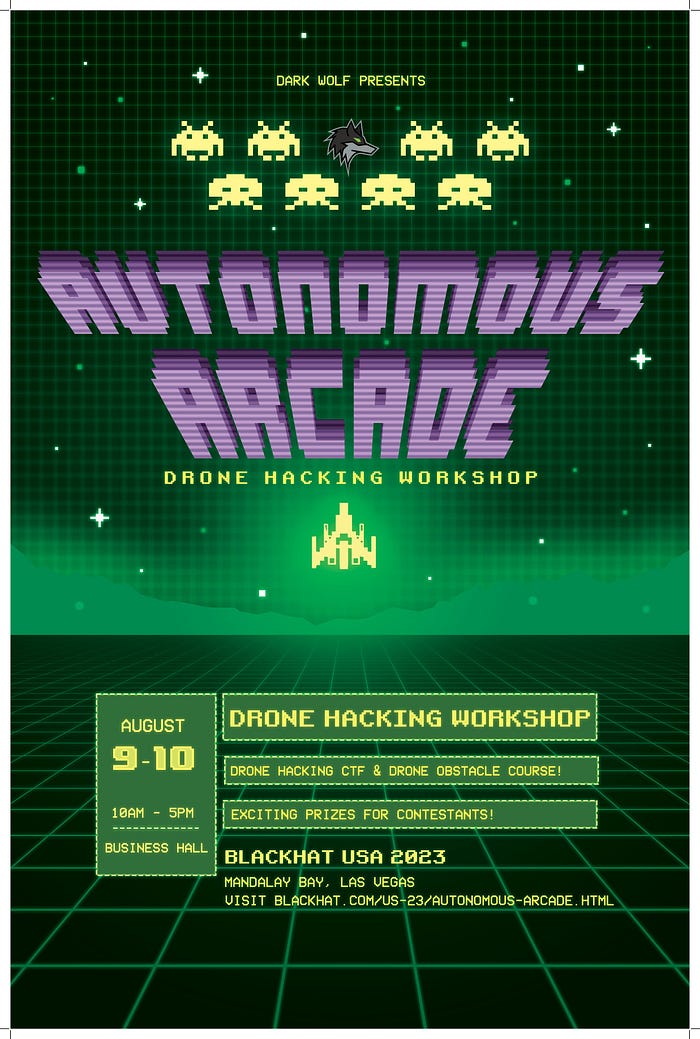
AUTONOMOUS ARCADE
August 9–10 | Business Hall
Autonomous Arcade is a brand-new Business Hall experience offering hands-on hacking challenges for attendees who want to learn more about hacking and controlling autonomous systems. With live classes on the conference floor and a CTF-style challenge that lets you put your newly learned skills to the test and LIVE DRONES, this space will be hard to miss.

BRICKS & PICKS
Visit Bricks & Picks to play with a gigantic pile of genuine LEGO bricks! There will be building activities and competitions with prizes throughout the day judged by the winner of LEGO Masters, NickinBrick. If building under pressure isn’t your thing, you can mingle and relax in our community zone by tagging our 2D graffiti wall or building whatever you like and adding your creation in our Black Hat Gallery. Bulk LEGO pieces have been partially provided by LUGVegas, a local group of Adult Fans of LEGO.
In partnership with Red Team Alliance, the Lockpicking Activity Space at Black Hat USA’s “Bricks & Picks” will provide valuable insights into the world of physical security and help attendees better understand the risks associated with physical security risks. By exploring vulnerabilities in various types of locks and the techniques used to bypass them, participants will be introduced to the hidden flaws in many physical security products. Participants will leave this activity space with more dynamic and innovative ways to approach security concepts and look at ubiquitous hardware in unconventional ways. By shining a spotlight on the topic of lockpicking, we hope to raise awareness of the importance of physical security and help attendees think more creatively about the ways in which to protect their assets.

BLACK HAT STARTUP SPOTLIGHT COMPETITION
WEDNESDAY, AUGUST 9, 2023 | 4:30–5:30 PM
BUSINESS HALL, BAYSIDE ABCD, LEVEL 1, STARTUP CITY THEATER
The Black Hat Startup Spotlight is back for Black Hat USA 2023! This Black Hat special event is a video pitch competition for cybersecurity startup companies to present their products and solutions in front of a live audience at Black Hat USA.
FINALISTS:
Congratulations to our Top 4 Finalists:
JUDGES
The Startup Spotlight Competition will be judged by a panel of industry leaders and innovators and the top four finalists will be announced on Tuesday, June 27.
The four finalists are invited to exhibit in the Startup City area at Black Hat USA 2023 and present their product or solution live to the judging panel and live audience where a winner will be announced.
Startup Spotlight Judges:

Ketaki Borade

Trey Ford

Hollie Hennessy

Maria Markstedter

Lucas Nelson

Robert J. Stratton III

Rik Turner
Hosted by

KELLY JACKSON-HIGGINS
EDITOR-IN-CHIEF, DARK READING
Kelly Jackson Higgins is the Editor-in-Chief of Dark Reading. She is an award-winning veteran technology and business journalist with more than two decades of experience in reporting and editing for various publications, including Network Computing, Secure Enterprise Magazine, Virginia Business magazine, and other major media properties. Jackson Higgins was recently selected as one of the Top 10 Cybersecurity Journalists in the US, and named as one of Folio’s 2019 Top Women in Media. She began her career as a sports writer in the Washington, DC metropolitan area, and earned her BA at William & Mary. Follow her on Twitter @kjhiggins.

COMMUNITY SESSIONS
& MEET-UPS
Open to all pass types, the Community Sessions and Meet-Ups encourage collaboration amongst attendees and presenters. Covering everything from personal digital resilience to mentorship and career-building strategies, attend the Black Hat Community Sessions and Meet-Ups to interact with topic experts and peers alike!
NOTE: The Community & Career tracks are for Briefings Pass holders only.
Civil Cyber Defense: Use Your Resources to Defend Non-Profits as They Combat Human Trafficking and Subvert Authoritarian Regimes
Tiffany Rad | Instructor, U.C. Berkeley
Austin Shamlin | Founder, Traverse Project
Date: Wednesday, August 9 | 10:20am-11:00am ( Jasmine AE, Level 3 )
Format: 40-Minute Briefings
Tracks: Community & Career, Privacy
Civil Cyber Defense volunteers and students challenge high-risk adversaries and threats such as human traffickers, authoritarian regimes, and surveillance being conducted on journalists. By utilizing academic resources, OSINT skills, and free/open-source tools, civil cyber defenders are supporting vulnerable non-profits, protecting volunteers, journalists, and activists while defending human rights.
There is a need in the cybersecurity industry for more civil cyber defenders. Recommendations will be made as to how your organization can support and/or volunteer your time and tools to provide protection to vulnerable organizations that have high risks, face advanced and persistent adversaries, but have modest resources.
Climate Change and Cybersecurity: Building a Resilient Future
Chloé Messdaghi | CEO and Founder, Global Secure Partners
Date: Wednesday, August 9 | 11:00am-11:40am ( South Pacific J, Level 0 )
Track: Community Sessions
Join this session to explore the relationship between climate change, cybersecurity, and information security (infosec) in promoting environmental sustainability. Through interactive Q&A sessions, we will discuss the environmental impact of infosec practices, strategies to make them greener, and the role of infosec in climate resilience. Topics include the carbon footprint of infosec, reducing energy consumption, sustainable procurement, protecting critical infrastructure, and supporting renewable energy systems. Let’s collectively explore solutions for a greener infosec industry and its contribution to climate change mitigation and adaptation.
Neurodiversity is MY Superpower
Dimitri McKay | Principal Security Strategist and CISO Advisor, Splunk
Date: Wednesday, August 9 | 11:30am-12:10pm ( South Pacific I, Level 0 )
Tracks: Meet-ups, Diversity & Inclusion
Embark on a journey of discovery with “Neurodiversity and US,” featuring Dimitri McKay, 20 year veteran in cybersecurity, community leader and author. This event begins with McKay sharing his personal experiences and challenges as a neurodiverse individual in the cybersecurity realm. The session then delves into a comprehensive discussion on the differences and nuances of neurodiversity within the cybersecurity community and the broader industry. McKay emphasizes the remarkable advantages that neurodiversity brings to the table, asserting it as not just an attribute, but a superpower that propels innovation and problem-solving in cybersecurity. Join us for this impactful event that promises to inspire and inform.
AI Security Challenges, Solutions, and Open Problems
Nathan Hamiel | Senior Director of Research, Kudelski Security | Black Hat Review Board
Date: Wednesday, August 9 | 3:20pm-4:00pm ( South Pacific I, Level 0 )
Track: Meet-ups
AI Security has become an incredibly hot topic with no shortage of challenges and open problems, leaving security professionals scrambling to catch up with emerging techniques and very little to go on. While the slow-moving machinery of industry does its best to catch up, that doesn’t help the many who face these challenges today. Where do you start? What can you do? What have you seen work?
Join us for a conversation on the challenges, solutions, and open problems in this evolving space. Meet your peers, share your perspective, and be part of the conversation.
Diversity Microtalks: Perspectives on Creating Change
Andy Ellis | Author, Advisory CISO & Operating Partner, Orca Security & YL Ventures
Meghan Jacquot | Security Engineer, Inspectiv
Olivia Rose | CISO and Owner, Rose CISO Group
Aastha Sahni | Azure Technical Trainer, Microsoft
Sherri Davidoff | CEO, LMG Security
Date: Wednesday, August 9 | 3:20pm-4:00pm ( South Seas AB, Level 3 )
Format: 40-Minute Briefings
Track: Community & Career
Join us for three practical microtalks by cybersecurity industry leaders Andy Ellis, Meghan Jaquot, Olivia Rose and Aastha Sahni.
Reducing Your Team’s Energy Costs: An Inclusion Microtalk (Andy Ellis)
Any time a staff member deviates from the implicit norm of a workplace, they pay an energy cost. They need to work different hours, eat different meals, take different days off, and look different from everyone else. Inclusion is reducing the energy cost people pay just to exist in a space — and it’s critical for building a good culture and effectively turning energy into value. Want some practical examples? I’ll share lots from my tenure as a CSO, such as extending parental leaves, using IM systems effectively, using vacation to remove single points of failure and actually talking about performance all the time. Inclusion is reducing the energy cost people pay just to exist in a space. Stop making them waste energy, so you can turn more energy into more value.
Breaking Barriers: a Data-Centric Approach (Meghan Jacquot and Aastha Sahni)
It is time for action. We know the numbers. Over the last decade, diversity within the workforce has increased — to take one measurement the number of women in cybersecurity has increased from 11% to 25% according to a research study by
ISC2. This is just one area of diversity and there are other groups that are more underrepresented. What has been accomplished and how has it been measured? What barriers exist around mindsets and unconscious bias? In this talk, we’ll focus on how to break those barriers and ways to measure and validate those changes.
Microaggressions and Turnover: Three Ways to Reduce Quiet Quitting (Olivia Rose)
The buildup of microaggressions is the primary reason why minorities decide to leave their workplace. Microaggressions are described as “a death by a thousand paper cuts”. Unfortunately, microaggressions are rooted deeply in human behavior and upbringing, and thus they are highly difficult to identify and address before they end up causing a diverse employee to leave. In this session, Olivia Rose will detail three actionable and realistic recommendations you can start implementing today at your organization to begin to address the retention problem. Olivia is a long-time Security practitioner, three-time CISO, and a Board member for Cyversity, an organization supporting women, underrepresented minorities, and veterans in Cybersecurity; where she developed and now leads the successful Mentorship Program.
Secrets of Submitting to Black Hat: A Guide to Writing a Successful CFP
Lidia Giuliano | DCISO/Security Architect, Health Care Sector
Sheila Berta | Head of Research, DreamLab Technologies
Stefano Zanero | Professor, Dipartimento Di Elettronica, Informazione e Bioingegneria, Politecnico Di Milano
Date: Wednesday, August 9 | 2:00pm-3:00pm ( South Pacific I, Level 0 )
Track: Community Sessions
Creating a compelling and engaging CFP submission can seem intimidating, especially for a major event like Black Hat. You’ve completed the research, you’ve done the hard work, now it’s time to effectively communicate it. Whether you’re a first-timer or a seasoned professional, the CFP process can present challenges that prevent great research from being submitted or accepted. If you’re unsure where to begin or feel your submissions need improvement, this workshop is designed for you.
Join us, the members of the Black Hat review board (Lidia Giuliano, Sheila Berta and Stefano Zanero), as we guide you through the submission process. We will discuss our criteria, dispel myths, and provide examples of successful submissions.
This interactive workshop offers you the opportunity to ask questions, practice writing your own CFP, work through various scenarios, and, most importantly, acquire the knowledge needed for success.
Embracing Ikigai: Overcoming Imposter Syndrome in the Cybersecurity Industry
Vicky Ray | Director, Unit 42 Cyber Consulting & Threat Intelligence, Palo Alto Networks
Date: Thursday, August 10 | 10:00am-10:40am ( South Pacific J, Level 0 )
Tracks: Community Sessions, Healthy Activities
The cybersecurity industry offers diverse career opportunities for students and professionals, driven by rapid technological advancements and growing demand for specialised expertise. To thrive in this ever-evolving field, individuals must continuously adapt to shifting tech and threat landscapes. However, high expectations from the industry and self-imposed pressures can negatively impact individuals, leading to the pervasive “Imposter Syndrome.” While discussions on the syndrome’s effects on cybersecurity professionals are gaining momentum, many hesitate to openly acknowledge their struggles, hindering career growth. The session will focus on highlighting the current challenges, encourage open sharing of ideas as well as discuss possible concepts which can help in overcoming them. The session will also introduce the concept of IKIGAI and how it can be a tool to overcome the growing issues of Imposter Syndrome in the cybersecurity industry which can go a long way in helping individuals un-lock their full potential.
Making and Breaking NSA’s Codebreaker Challenge
Rita Doerr | Academic Outreach Lead, NSA
Date: Thursday, August 10 | 10:20am-11:00am ( South Seas CD, Level 3 )
Format: 40-Minute Briefings
Track: Community & Career
For the past 10 years, the National Security Agency (NSA) has hosted the Codebreaker Challenge. This competition, written and run by NSA’s technical experts, includes a new theme and challenge each year. The challenges are custom designed by NSA to mimic a real-world problem NSA faces in its mission and include up to 10 rounds of increasing difficulty including code analysis and reverse engineering. Starting with only 5 schools in 2013, the program has grown exponentially. In 2022, more than 4,800 participants from 449 schools across the United States competed for bragging rights. Only 104 people (about 2%) successfully completed all 9 rounds of the challenge this past year.
For the very first time at Black Hat, the NSA will publicly share insights and lessons from running the Codebreaker Challenge. We will present details about the design of the 2022 challenge that focused on the NSA assisting FBI agents in responding to a US company that had been crippled by a ransomware attack.
Skills Short, Threats Deep…How to Foster and Retain a Security Team Amongst a Significant Workforce Gap
Jon France | Chief Information Security Officer, (ISC)²
Date: Thursday, August 10 | 2:10pm-2:50pm ( South Pacific J, Level 0 )
Track: Community Sessions
With a global cybersecurity workforce gap of 3.4 million professionals, organizations are facing significant challenges when it comes to staffing and retaining professionals on their security teams. Staffing shortages continue to worsen as economic uncertainty and political conflict impact job markets around the world. To navigate this complex landscape, organizations must empower cybersecurity professionals to limit staff shortages and foster retention, in turn, strengthening defenses to mitigate various cyber threats. Key approaches include guiding internal talent through training initiatives, implementing job rotations, establishing mentorship programs and encouraging non-IT or non-security personnel to join the field and the security team. These measures are vital to maintaining a robust team that can stay ahead of evolving threats. In this presentation, Jon France, CISO at (ISC)², the world’s largest nonprofit association of certified cybersecurity professionals, discusses ways to equip security teams with the necessary resources and support so organizations can build resilient defenses against the evolving threat landscape. Jon will share research-based insights, actionable strategies and effective tactics to enable security teams to thrive amidst the global workforce shortage.
Ask the EFF
Date: Thursday, August 10 | 11:20am-12:00pm ( South Pacific I, Level 0 )
Track: Meet-ups
Join the Electronic Frontier Foundation — the leading non-profit fighting for civil liberties in the digital world- to chat about the latest developments in Tech and Law and how these can help each other to build a better future. Half of this session will be given over to question-and-answer, so it’s your chance to ask EFF questions about the law and tech.
Blue Teaming For Your Mental Health
Sarah Young | Senior Cloud Security Advocate, Microsoft
Date: Thursday, August 10 | 2:00pm-2:40pm ( South Pacific I, Level 0 )
Tracks: Meet-ups, Healthy Activities
There’s no question that any role within the cyber security industry is mentally taxing. Although there has been more focus on mental health in the past few years, there is still stigma and shame attached to this topic. Outside factors can play a significant role in how well our mental health is — family, finances, careers, etc. During this meet-up, Sarah Young will share her personal experiences on how she learned to manage her mental health whilst coping with both general life struggles and exacerbating factors from one of her previous cyber security jobs. She will also provide practical tips and recommendations on how you can manage mental health. After all, everyone has a secret struggle that you might know nothing about: be kind!

BLACK HAT CISO SUMMIT
The Black Hat CISO Summit is an approval-only event during Black Hat USA which brings together top security executives from global corporations and government agencies for a full day of unique discussions. Offered the day before the main Black Hat USA Briefings sessions, the CISO Summit is intended to give CISOs and other InfoSec executives leading-edge insight into the latest security trends, technologies, and enterprise best practices.
CONTINUING PROFESSIONAL EDUCATION (CPES)
Those who are certified through (ISC)2 can earn 5.5 Continuing Professional Education (CPE) credits for attending the CISO Summit.
Black Hat does not maintain records of earned CPE credits. However, we will report your credits to (ISC)2 on your behalf after the event. Please provide your (ISC)2 member number when registering for the event.
For questions about credits for CISO attendees, e-mail cisosummit@blackhat.com.
AGENDA
MONDAY, AUGUST 7
5:00–7:00 PM
CISO Summit Welcome Reception
TUESDAY, AUGUST 8
8:00–9:00 AM
Networking Breakfast
9:00–9:10 AM
Welcome and Introductions
- Jeff Moss, Founder, Black Hat + DEF CON
- Steve Wylie, General Manager, Black Hat
- Jeremiah Grossman, MC
9:10–9:40 AM
Tales from the Breach
- Jason Haddix
9:40–10:10 AM
Building Real Offensive Security Teams — Lessons Learned
- Chris Gates
10:10–10:30 AM
Networking Break
10:30–11:00 AM
CISO Success in the Board Room
- Richard Seiersen
11:00–11:30 AM
Personal Privacy & Security for CISOs
- Caleb Sima
11:30 AM — 12:00 PM
Using Data to Prioritize Cybersecurity Investments
- Scott Stransky
12:00–1:30 PM
Lunch
1:30–2:00 PM
AI vs. Software, Society, and Security Programs
- Daniel Miessler
2:00–2:30 PM
Cyber Preparedness — Future Conflicts Will Include Non-Military
- Rich Baich
2:30–3:00 PM
Cyber Security Economics
- Fernando Montenegro
3:00–3:20 PM
Networking Break
3:20–4:00 PM
How Institutional Investors Evaluate Your Vendors
- Roger Thornton
- Bill Ryckman
- Chenxi Wang
- Justine Bone, Moderator
4:00–4:30 PM
Your Threat Model is Too Narrow: A Broader Look at Supply Chain Ecosystem Attacks
- Mike Hanley
4:30–4:55 PM
CISO Liability — Lessons Learned
- Joe Sullivan
4:55–5:00 PM
Closing Remarks
5:00–6:00 PM
Cocktail Reception

Black Hat — Omdia Analyst Summit
TUESDAY, AUGUST 8, 2023
This event will be in-person only and admission is by approval only — and is not guaranteed.
You’re Invited To Apply to Attend The Omdia Analyst Summit at Black Hat USA 2023
The third annual Omdia Analyst Summit returns to Black Hat USA featuring the industry’s leading cybersecurity analysts. Delegates will hear about the latest cybersecurity trends, market updates, observations, projections and insights through keynote, panel and fireside chats at this day-long in-person Summit.
The theme for 2023 is Cybersecurity: Maximum Attention, Minimum Budget. Join our experts and you’ll get new insights into:
- Omdia’s Security Decision-Maker Report 2023 — What Are Security Functions Focusing on Today and in the Near Future?
- The business challenges faced by security budgets
- Where organizations focus their security spending
- Clarity around and the emergence of proactive security platforms
- And much more!
AGENDA
TUESDAY, AUGUST 8, 2023
9:15–9:20 AM
Welcome and Introductions
9:20–9:50 AM
Keynote:
Cybersecurity: Maximum Attention, Minimum Budget
- Maxine Holt, Senior Director — Research
- Rik Turner, Senior Principal Analyst (via video)
9:50–10:10 AM
Proactive Security: Cyber-Resiliency’s Innovation Wave
- Eric Parizo, Managing Principal Analyst
- Andrew Braunberg, Principal Analyst
10:10–10:30 AM
Getting SASE with Security Delivery
- Fernando Montenegro, Senior Principal Analyst
10:30–10:50 AM
Investigating the Acronym Soup of Cloud Security
- Ketaki Borade, Senior Analyst — Infrastructure Security
- Rik Turner, Principal Analyst (via video)
10:50–11:10 AM
Networking Break with Analysts11:10–11:30 AM
Build or Buy? A CISO IT Security Services Guide
- Adam Etherington, Principal Analyst — Digital Enterprise Services
11:30–11:50 AM
Data Security 2.0: The Rise of Data Security Posture Management
- Adam Strange, Principal Analyst, Data Security
- Rik Turner, Senior Principal Analyst (via video)
11:50 AM — 12:10 PM
Decentralized Identity: Hype or Reality?
- Don Tait, Senior Analyst
12:10–12:20 PM
Fireside Chat
- Sponsored by: TBA
12:20–1:35 PM
Lunch
1:35–1:55 PM
How Does Generative AI Actually Help Cybersecurity?
- Curt Franklin, Senior Analyst
- Ketaki Borade, Senior Analyst — Infrastructure Security
1:55–2:15 PM
IT vs. Industry: Existing Investments or Specialized Solutions?
- Hollie Hennessy, Senior Analyst
- Katelyn Galer, Senior Analyst
2:15–2:50 PM
Stories from the Field: Successes in Industry-Specific Cybersecurity
- Chaired by Hollie Hennessy, Senior Analyst
- + Sponsor TXOne Networks
2:50–3:10 PM
Networking Break with Analysts3:10–3:30 PM
Why Managed Detection and Response (MDR) Is So Hot Right Now
- Jon Ong, Senior Analyst
- Adam Etherington, Principal Analyst — Digital Enterprise Services
3:30–3:40 PM
Fireside Chat
- Sponsored by: TBA
3:40–4:25 PM
Analyst Panel and Audience Q&A:
How Organizations Are Addressing Economic Challenges While Driving Improved Security
- Chaired by Eric Parizo, Managing Principal Analyst
- Adam Etherington, Principal Analyst — Digital Enterprise Services
- Hollie Hennessy, Senior Analyst
- Andrew Braunberg, Principal Analyst
4:25–4:30 PM
Closing Remarks
- Maxine Holt, Senior Director — Research
4:30–5:30 PM
Networking Reception with Omdia Analysts
MICRO SUMMITS
Micro Summits have returned to Black Hat.
Micro Summits are designed to foster education and collaboration on focused topics that have wide applicability to the Information Security industry. Leading experts will share their insights on key topics and enable attendees to connect with fellow attendees, speakers, and industry leaders to better understand critical issues and solutions.
Each Micro Summit is a half-day program combining subject matter expertise and networking opportunities. All-day attendance is not required. Micro Summits take place during Briefings. Attendees can easily participate in both programs. No pre-registration is required.
A Black Hat Briefings Pass is required to attend.
CYBER INSURANCE
Wednesday, August 9, 1:30–5:00 PM
Oceanside D, Level 2
Cyber liability insurance, like it or not, already has and will continue to have a profound impact on the entire Information Security industry. Everyone in the industry will be affected because no matter how many resources an organization invests in various security controls, there will always be latent risk of breach and financial loss. That’s one of the main reasons why organizations find it attractive to transfer their risk to an insurance carrier. As these business decisions are made it becomes vital for InfoSec pros to become familiar with cyber-insurance policies in what they cover and don’t cover; how claims are made, which are paid vs denied, how the incident response process may be altered; and how carriers influence what security controls their clients implement.
The Integration Cyber Security and Insurance: The Journey of Cysurance
Kirsten Bay | CEO, Cysurance
Date: Wednesday, August 9 | 1:30pm-2:10pm
Track: Cyber Insurance
Leverage and Demonstrate Value with your Cyber Insurance Renewal
Erik Decker | Vice President and Chief Information and Security Officer
Date: Wednesday, August 9 | 2:30pm-3:00pm
Track: Cyber Insurance
Why Cyber Insurance Should be Your SOC’s New Best Friend
Catherine Lyle | Head of Claims, Coalition
Date: Wednesday, August 9 | 3:20pm-4:00pm
Track: Cyber Insurance
Bridging Cyber and Insurance
John Caruthers | Executive VP & Chief Information Security Officer, Triden Group
Date: Wednesday, August 9 | 4:20pm-5:00pm
Track: Cyber Insurance
ENTREPRENEUR
Thursday, August 10, 10:20 AM — 3:00 PM
Oceanside D, Level 2
Don’t miss the Black Hat Entrepreneur Summit, a gathering designed to help cybersecurity inventors, creators, and leaders transform innovative ideas into thriving ventures. This event unites the brightest entrepreneurial minds in the hacking world, offering valuable insights from seasoned entrepreneurs and industry experts on navigating investment, boot-strapping strategies, and core aspects of cybersecurity entrepreneurship. Engage in interactive discussions that cover critical topics such as cybersecurity business modeling, market research, funding strategies, and effective team building. Join us in exploring the unique challenges and opportunities within the cybersecurity industry, equipping yourself with the knowledge and skills needed for a successful entrepreneurial journey.
Entrepreneur’s Dilemma: Managing Growth and Dedication to Product Quality
Mario Vuksan | Co-founder and CEO, ReversingLabs
Date: Thursday, August 10 | 10:20am-11:00am ( Oceanside D, Level 2 )
Format: 40-Minute Briefings
Track: Entrepreneur
Join Mario Vuksan, co-founder and CEO of ReversingLabs and a veteran of the security industry in discussing his experiences of growth and survival in the industry beset by on one hand by FUD and rapid expansion and on the other by constant change driven by criminal and state sponsored actors.
In this talk, Mario will discuss how to maintain product quality and continuity with strong customer engagement while evaluating pros and cons of relying on others to grow your company. As different stages of growth bring out different calculus, Mario will draw on his experience in discussing bootstrapping and when possibly to make a direction change, deciding on when, why and if to fundraise. Examples of navigating through product evolution and team growth, along with challenges of building non-technical teams and considering multi-track exit paths will be discussed.
Idea to Realization: Cybersecurity Entrepreneurship
Jon Oberheide | Entrepreneur
Date: Thursday, August 10 | 11:20am-12:00pm ( Oceanside D, Level 2 )
Format: 40-Minute Briefings
Track: Entrepreneur
Join Duo Security co-founders and Arbor Networks founding members, Dug Song and Jon Oberheide, for a valuable session at Black Hat’s Entrepreneur Micro Summit. Drawing from their experience in building successful cybersecurity companies, they will share practical advice for aspiring founders on transforming ideas into reality.
In this talk, attendees will learn the initial steps of their entrepreneurial journey and how to overcome common challenges in the cybersecurity industry. By the end, participants will gain a clear understanding of the practical steps to launch their cybersecurity startups, learning from two industry veterans who have successfully navigated the entrepreneurial landscape.
Entrepreneur Journeys: What it Takes to Start a Startup
Varun Badhwar | Founder & CEO, Endor Labs
Umaimah Khan | CEO & Co-founder, Opal
Travis McPeak | Co-founder & CEO, Resourcely
Eitan Worcel | Co-founder & CEO, Mobb
Caleb Sima | Chief Security Officer, Robinhood
Date: Thursday, August 10 | 1:30pm-2:10pm ( Oceanside D, Level 2 )
Track: Entrepreneur
Join us for an inspiring and thought-provoking panel discussion as leaders from four new companies shed light on their extraordinary journeys of building and scaling their companies. CEOs and founders from Endor Labs, Mobb, Opal, and Resourcely will delve into the intricate aspects of launching a startup, navigating the evolving market dynamics, and overcoming hurdles along the way. By highlighting their unique perspectives, the panelists will provide valuable insights into the strategies, innovations, and adaptations that have propelled their ventures forward. Attend this session to learn what to expect in your first year of a cyber startup.
A Q&A with a16z’s Zane Lackey: Unlocking the Secrets of Cybersecurity Entrepreneurship
Zane Lackey | General Partner, Andreessen Horowitz
Date: Thursday, August 10 | 2:30pm-3:00pm ( Oceanside D, Level 2 )
Format: 30-Minute Briefings
Track: Entrepreneur
Join us for an insightful Q&A session with Zane Lackey, General Partner at Andreessen Horowitz and former CISO of Etsy, at the inaugural Black Hat Entrepreneur Micro Summit. In this interactive discussion, Zane will share his experiences and answer questions about transitioning from a security engineer or CISO to a founder and ultimately, a venture capitalist in the cybersecurity industry.
As the co-founder of Signal Sciences, which was acquired for $825M in 2020, Zane offers a unique perspective on various stages of the entrepreneurial journey. Attendees will have the opportunity to ask questions about not only raising capital but also about founding a cybersecurity startup, building a successful team, and navigating the challenges faced by entrepreneurs in this rapidly evolving field.
Don’t miss this chance to learn from an accomplished entrepreneur and investor who has successfully traversed the cybersecurity landscape, providing valuable insights for both aspiring and experienced entrepreneurs looking to make the leap from security engineer or CISO to founder.

BLACK HAT CERTIFIED PENTESTER
Black Hat has been an industry leader in providing and facilitating cutting edge security briefings and training for over two decades. Driven by innovation and research, the annual conferences provide attendees various avenues to learn and progress in the different sectors of information security. This year, in partnership with The SecOps Group, Black Hat is pleased to announce its own certification: Black Hat Certified Pentester (BCPen).
What is Black Hat Certified Pentester Certification?
The Black Hat Certified Pentester (BCPen) is an intermediate level exam, intended to be taken by professional pentesters, bug-bounty hunters, red and blue team experts, SOC analysts and anyone wanting to evaluate or appraise their existing knowledge in topics involving hands-on pentesting. This practical, in-person exam covers a wide variety of topics and in order to successfully complete each section, attendees will have to obtain flags associated with every topic.
The pass criteria is as following:
- Attendees scoring over 60% marks will be deemed to have successfully passed the exam.
- Attendees scoring over 75% marks will be deemed to have passed with merit.
How long is the exam?
The exam will be for 7 hours (9 AM to 5 PM). However, an hour of lunch break can be taken during the exam. The exam can be taken on any one of the following four days:
- Saturday, August 5, 2023
- Sunday, August 6, 2023
- Monday, August 7, 2023
- Tuesday, August 8, 2023
What topics are covered?
The exam will cover the following topics of pentesting:
- Web Hacking (50%) — 3.5 hours (210 mins); 210 Marks*
- Infrastructure Hacking (50%) — 3.5 hours (210 mins); 210 Marks*
The complete list of topics can be found in the exam syllabus section below.
*Note:
The marks allocated for every question also indicates the time that an attendee is expected to spend in solving a question. For e.g. a question worth 30 marks, will require roughly 30 minutes, for it to be solved.
What is the format of the exam?
The exam will be a Capture The Flag (CTF) style Hackathon. It will be a full day event requiring attendees to capture flags as they go on identifying and exploiting various system vulnerabilities and score points, after submitting the flags and answering the associated questions.
What is the experience needed to take the certification and what level of difficulty can be expected from the exam?
We recommend a minimum of 2 years of professional penetration testing/bug bounty experience (both network and application pentesting) before taking this exam.
In terms of difficulty, on the scale of beginner, intermediate and advanced, this exam has been rated as intermediate. The exam tests attendees’ practical knowledge in identifying and exploiting vulnerabilities in real life pentesting scenarios.
To explain this a bit more, we expect attendees to be able to identify and exploit vulnerabilities such as SQL Injection and obtain relevant flags, however, we are not testing them on advanced web hacking concepts such as that of Second-order SQL Injection, within this exam. Similarly, to cite another example for infrastructure hacking, attendees are expected to use common hacking tools and techniques to demonstrate how to compromise a Windows Active Directory infrastructure, but they are not expected to write custom exploits, use or create 0-day exploits or perform reverse engineering etc.
Can I participate with my friends and colleagues as a team?
One can only participate in an individual capacity (i.e. teamwork is not allowed).
What tools/laptop do I need to bring?
Attendees must use their own laptop and can use hacking tools of their choice. Internet access will be available during the course of the exam but no assistance will be provided with regards to installation/configuration of any tools. The hacking challenges can be solved using freely available tools and scripts.
What will attendees get?
Each attendee will receive:
A certificate of participation. The certificate will mention pass/fail and merit status. In addition to this, attendees will be able to download a PDF report, which will have detailed scores for each section of the exam, allowing them to identify and focus on areas of improvement for future qualification and training.
Will you provide any training that can be taken prior to the certification?
Being an independent certifying authority, we (The SecOps Group) do not provide any training for the exam. Attendees should carefully go over each topic listed in the syllabus and make sure they have adequate understanding, required experience and practical knowledge of these topics.
What is the exam retake policy?
Candidates who fail the exam must purchase a new exam voucher for every attempt.
How long is the certificate valid for?
The certification does not have an expiration date. However, the passing certificate will mention the details of the exam such as the exam version and the date. As the exam is updated over time, candidates should retake the newer version as per their convenience.
What is the exam syllabus?
The exam syllabus is listed below:
Web Hacking
- Google Hacking, Dorking and OSINT Techniques.
- Identification and Exploitation of OWASP Top 10 Vulnerabilities
- Cross-Site Scripting
- SQL Injection
- XML External Entity attack
- Cross-Site Request Forgery
- Practical Cryptographic Attacks
- Authentication related Vulnerabilities
- Brute force Attacks
- Username Enumeration
- TLS Security
- Identification of TLS security Misconfigurations.
- Server-Side Request Forgery
- Authorization and Session Management related Flaws
- Insecure File Uploads
- Code Injection Vulnerabilities
- Business Logic Flaws
- Directory Traversal Vulnerabilities
- Common Security Misconfigurations.
- Information Disclosure.
- Vulnerable and Outdated Components.
- Common Security Weaknesses affecting Cloud Services such as a S3 Bucket.
- Security Best Practices and Hardening Mechanisms.
Infrastructure Hacking
- Common OSINT Techniques
- Network Mapping and Target Identification
- Brute-force Attacks.
- Vulnerability Identification and Exploitation using Common Hacking Tools.
- Application Server Flaws.
- Insecure Protocols
- *nix Vulnerabilities.
- Insecure File permissions.
- Security Misconfigurations Leading to Privilege Escalation Attacks.
- Windows Active Directory Attacks.
- OS Credential Dumping and Replay.
- Kerberoasting; golden and silver tickets.
- Password Attacks and Password Cracking.
- Administrative Shares Exploitation
- Persistence Techniques
- Lateral Movements
- Enumerating Cloud Services, Policy, and Roles
- Abusing Serverless Services
- Abusing API Tokens and Cloud Credentials
- Vulnerability chaining
- Exploiting docker environments and breaking out of containers
About: The SecOps Group
The SecOps Group is a globally recognized IT security company having extensive and varied experience of providing cyber security consultancy and education services. At The SecOps Group, we believe that security is a continuous process, which has to progress with time and in accordance with the customer needs and constantly evolving threats. Our core business comprises of two units:
- Consultancy:
Pentesting and Advisory
The SecOps Group are cybersecurity experts offering CREST accredited security consultancy services. - Education:
Cyber Security Certifications
Through our exams, we provide an authentic and credible certification program that is modern, relevant and represents real life business risks. - Vulnmachines (A Pentest Learning Platform)
The SecOps Group runs a free pentest learning platform called “Vulnmachines”.

BLACK HAT NETWORK OPERATIONS CENTER (NOC)
The Black Hat Network Operations Center (NOC) provides a high security, high availability network in one of the most demanding environments in the world — the Black Hat event. This is accomplished with the help of best of breed solutions providers and seasoned security and engineering teams led by Black Hat’s esteemed NOC Team Leads. Together this team provides the security, stability, and visibility of a world-class enterprise network.
Each year this hand-selected team meets months before Black Hat to incorporate the latest infrastructure and security solutions into a workable network design. The team reconvenes just days before Black Hat for a compressed deployment of a network that must be operational for the opening day of the event. Black Hat attendees can visit the NOC for a glimpse into this state-of-the-art network. The Black Hat NOC program is a testament to engineering know-how and teamwork.
Live Stream Hours
- Tuesday, August 8: 9:00 AM — 6:00 PM
- Wednesday, August 9: 9:00 AM — 6:00 PM
- Thursday, August 10: 9:00 AM — 6:00 PM
NOC Presentations (South Pacific J, Level 0)
- Wednesday, August 9: 10:20 AM — 10:40 AM & 2:30 PM — 2:50 PM
- Thursday, August 10: 11:00 AM — 11:20 AM & 1:30 PM — 1:50 PM
NOC Visiting Hours (Surf EF, Level 2)
- Saturday, August 5: 9:00 AM — 7:00 PM
- Sunday, August 6: 9:00 AM — 6:00 PM
- Monday, August 7: 9:00 AM — 6:00 PM
- Tuesday, August 8: 9:00 AM — 6:00 PM
- Wednesday, August 9: 9:00 AM — 6:00 PM
- Thursday, August 10: 9:00 AM — 6:00 PM
The 9th Annual Black Hat USA Network Operations Center (NOC) Report
Neil Wyler | Global Lead of Active Threat Assessments, IBM Security X-Force
Bart Stump | Senior Systems Engineer, NetWitness
Date: Thursday, August 10 | 4:20pm-5:00pm ( Oceanside A, Level 2 )
Format: 40-Minute Briefings
Tracks: Network Security, Application Security: Defense
Back with another year of soul-crushing statistics, the Black Hat NOC team will be sharing all of the data that keeps us equally puzzled, and entertained, year after year. We’ll let you know all the tools and techniques we’re using to set up, stabilize, and secure the network, and what changes we’ve made over the past year to try and keep doing things better. Of course, we’ll be sharing some of the more humorous network activity and what it helps us learn about the way security professionals conduct themselves on an open WiFi network.

BLACK HAT DAY ZERO
Before diving into two jam-packed days of hacks and research, hear insider’s recommendations on how to make the most of your time, including a synopsis of this years can’t-miss Briefings, Arsenal Tools, and special Features from Black Hat Review Board Members, Speakers and Presenters.
Open to all pass types, Day Zero is designed to welcome both first-time and long-time Black Hat attendees. Join us on Tuesday, August 8 to kick off your Black Hat experience and begin building your schedule and network with an inside look at what’s in store and the tools available to help you make the most out of your time.
All Black Hat pass types are welcome. No pre-registration is required.
TUESDAY, AUGUST 8, 4:00 PM — 7:00 PM
Location: South Pacific EF, Level 0
4:00 PM — 4:20 PM
How to have Two Productive Days (and Best Party-Nights!) at Black Hat
by Sheila A. Berta, Head of Security Research, Dreamlab Technologies
Black Hat is a highly anticipated event for both newcomers and attending veterans. The conference is evolving, and it could be overwhelming to navigate an event of this size. Briefings, Arsenal, Sponsored Sessions, Business Hall, there are plenty of options and it might be hard to know what to do, where to go, what to attend and how to get party tickets… This talk will give you useful advice to make the most of your time, select the right content which fits your needs and have a successful experience at Black Hat USA 2023.
4:20 PM — 4:45 PM
Must-See Briefings at Black Hat USA 2023
by Tara Seals, Managing Editor, Dark Reading
With 100+ briefings, sessions and keynotes scheduled at Black Hat USA 2023, sifting through the agenda for the must-sees can be a big task. The agenda is once again filled with brand-new research into threat groups, malware, exploits, and new attack patterns from top cyber experts and analysts. There are also opportunities to gain deep insights into the business and operational side of cybersecurity. How to choose? In this session, Dark Reading Managing News Editor Tara Seals will give you a sneak-peek at some of the hottest Black Hat USA talks that you won’t want to miss.
4:45 PM — 5:00 PM
Break
5:00 PM — 5:20 PM
Build Your Personal Brand — Conferences and You
by Stephanie Domas, Chief Security Technology Strategist and Senior Director of Security Architecture and Engineering, Intel
It’s always a good time to build your personal brand. Whether you are looking to make that jump to your next career, or simply elevate your reputation. Come learn some strategies for building your brand and how conferences play a critical role.
5:20 PM — 5:40 PM
An Introvert’s Guide to Optimizing Your Black Hat Experience
by Chris Eng, Chief Research Officer, Veracode
The size and scale of Black Hat can be overwhelming for first time attendees, especially if you’re not used to constant stimuli from all directions and the sustained level of “peopling” over multiple days. In this session, we’ll discuss how to navigate the social struggles of a big conference, helping you to network efficiently and stay engaged without compromising your sanity.
5:40 PM — 6:00 PM
Staying Connected, and Surviving, on the Black Hat Network
by Bart Stump, Senior Systems Engineer, Netwitness and Neil Wyler, Global Lead of Active Threat Assessments, IBM X-Force
The Black Hat network is often the subject of quiet whispers, fear, and sometimes laughter. “Don’t even connect to it.” “Use a burner laptop.” “Take the battery out of your phone!”
Come talk to the guys who stand up and maintain, what is considered by many, to be one of the most hostile networks in the world. Find out what you can expect while staying connected at Black Hat, and tips you can use to try and stay safe. It’s a jungle out there, you should really have a guide.
6:00 PM — 7:00 PM
Day Zero Reception
Join fellow attendees after the Day Zero program for a reception. Kick off Black Hat USA with refreshments and appetizers; the reception is open to all Black Hat USA pass holders.
ARSENAL
August 9–10, 2023
Arsenal brings together researchers and the open-source community to showcase their latest open-source tools and products in an open, conversational, and virtual environment where presenters are able to interact with the attendees.
Arsenal is now featuring the Lab at all regional events. The Arsenal Lab is an interactive, hands-on environment designed for hacking enthusiasts of all skill-level to learn about specialized tools and targets that may be difficult to access otherwise. Join our industry experts to discover new skills or take existing skills to the next level.
ARSENAL HIGHLIGHTS:
AntiSquat — An AI-Powered Phishing Domain Finder
Date: Wednesday, August 9 | 10:00am-10:59pm ( On-Demand )
Track: Network Defense
Session Type: Arsenal
If you host a domain on the internet representing an individual or organization, chances are that there exists a phishing domain designed specially to attack the users of your product or website.
AntiSquat is an AI-Powered typo-squatting domain finder that checks for phishing domains based on misspellings. It has a flagging system that leverages a combination of Machine Learning Models as well as various other checks such as web page similarity matching. These are performed in real-time on the target domain, thus making sure that the results are impactful.
eBPFShield: Unleashing the Power of eBPF for OS Kernel Exploitation and Security.
Date: Wednesday, August 9 | 10:00am-10:58pm ( On-Demand )
Track: Network Defense
Session Type: Arsenal
Are you looking for an advanced tool that can help you detect and prevent sophisticated exploits on your systems? Look no further than eBPFShield. Let’s take a technical look at some of the capabilities of this powerful technology:
DNS monitoring feature is particularly useful for detecting DNS tunneling, a technique used by attackers to bypass network security measures. By monitoring DNS queries, eBPFShield can help detect and block these attempts before any damage is done.
IP-Intelligence feature allows you to monitor outbound connections and check them against threat intelligence lists. This helps prevent command-and-control (C2) communications, a common tactic used by attackers to control compromised systems. By blocking outbound connections to known C2 destinations, eBPFShield can prevent attackers from exfiltrating sensitive data or delivering additional payloads to your system.
eBPFShield Machine Learning feature, you can develop and run advanced machine learning algorithms entirely in eBPF. We demonstrate a flow-based network intrusion detection system(IDS) based on machine learning entirely in eBPF. Our solution uses a decision tree and decides for each packet whether it is malicious or not, considering the entire previous context of the network flow.
eBPFShield Forensics helps address Linux security issues by analyzing system calls and kernel events to detect possible code injection into another process. It can also help identify malicious files and processes that may have been introduced to your system, allowing you to remediate any security issues quickly and effectively.
During the workshop, we’ll delve deeper into these features and demonstrate how eBPFShield can help you protect your systems against even the most advanced threats.
Hands-on RF Hacking: Your Table is (always) Ready
Dates: Wednesday, August 9 | 10:00am-11:30am ( Business Hall — Arsenal Lab )
Thursday, August 10 | 2:30pm-4:00pm ( Business Hall, Arsenal Lab )
Track: Arsenal Lab
Session Type: Arsenal
Network Monitoring Tools for macOS
Date: Wednesday, August 9 | 10:00am-11:30am ( Business Hall — Arsenal Station 8 )
Tracks: Malware Defense, Network Defense
Session Type: Arsenal
As the majority of malware contains networking capabilities, it is well understood that detecting unauthorized network access is a powerful detection heuristic. However, while the concepts of network traffic analysis and monitoring to detect malicious code are well established and widely implemented on platforms such as Windows, there remains a dearth of such capabilities on macOS.
Here, we will present various tools capable of enumerating network state, statistics, and traffic, directly on a macOS host. We will showcase open-source tools that leverage low-level APIs, private frameworks, and user-mode extensions that provide insight into all networking activity on macOS:
Specifically we’ll demonstrate:
* A network monitor that allows one to explore all network sockets and connections, either via an interactive UI, or from the commandline.
* A DNS monitor that uses Apple’s Network Extension Framework to monitors DNS requests and responses directly from the Terminal.
* A firewall that monitors and filters all network traffic, giving users with the ability to block unknown/unauthorized outgoing connections.
Thunderstorm: Turning Off the Lights in Your Data Center
Date: Wednesday, August 9 | 10:00am-11:30am ( Business Hall — Arsenal Station 3 )
Tracks: Internet of Things, Exploitation and Ethical Hacking
Session Type: Arsenal
One of the main premises of any IT installation, is to protect the entire infrastructure against possible failures. In addition to firewalls and other network elements, one of the vital points is the electrical system.
Thanks to uninterruptible power supplies (UPS), it is possible to cover and manage these issues economically. The main problem, is that many of these systems inherit the same bugs as other IoT devices, which makes them vulnerable to all kinds of attacks.
In this presentation, we will explain how it has been possible to develop different zero-day vulnerabilities thanks to social engineering, some investment, and a bit of common sense. Among other things, these flaws would make it possible to compromise the electrical system of an office or even that of a Data Center.
Since these devices share common components, it would be possible to obtain remote code execution (with the highest possible privileges) and/or denial of service on more than 100 different manufacturers. Moreover, all of this has been automated in a single framework, making it possible to detect and exploit these vulnerabilities easily, simply and fully automatically.
Easy EASM — The Zero Dollar Attack Surface Management Tool
Date: Wednesday, August 9 | 11:30am-1:00pm ( Business Hall — Arsenal Station 1 )
Track:
Session Type: Arsenal
Easy EASM is just that… the easiest to set-up tool to give your organization visibility into its external facing assets.
The industry is dominated by $30k vendors selling “Attack Surface Management,” but OG bug bounty hunters and red teamers know the truth. External ASM was born out of the bug bounty scene. Most of these $30k vendors use this open-source tooling on the backend.
With ten lines of setup or less, using open source tools, and one button deployment, Easy EASM will give your organization a complete view of your online assets. Easy EASM scans you daily and alerts you via Slack or Discord on newly found assets! Easy EASM also spits out an Excel skeleton for a Risk Register or Asset Database! This isn’t rocket science.. but it’s USEFUL. Don’t get scammed. Grab Easy EASM and feel confident you know what’s facing attackers on the internet.
SinCity: Build Your Dream Lab Environment
Date: Wednesday, August 9 | 11:30am-1:00pm ( Business Hall — Arsenal Station 2 )
Tracks: Network Defense, Exploitation and Ethical Hacking
Session Type: Arsenal
Security practitioners are still wasting time today building and maintaining lab environments through “manual” and cumbersome processes. In doing so, they are missing out on the potential DevOps methodologies and Infrastructure-as-Code (IaC) practices offer. This daunting work must end now.
This arsenal demonstration will introduce SinCity, a GPT-powered, MITRE ATT&CK-based tool which automates the provisioning and management of an IT environment in a conversational way. SinCity reduces the efforts needed to build a full-blown lab environment from months to minutes by providing an abstraction layer for customizing network topologies, crafting attack scenarios, and tuning security controls.
Attendees who frequently sandbox malware, analyze TTPs, or evaluate detection capabilities — this arsenal will save you precious time.
AI Risky Business: Hands-on AI Payload Analysis
Dates: Wednesday, August 9 | 12:15pm-1:45pm ( Business Hall — Arsenal Lab )
Thursday, August 10 | 10:00am-11:30am ( Business Hall, Arsenal Lab )
Tracks: Arsenal Lab, Vulnerability Assessment
Session Type: Arsenal
In their rush to adopt new AI technologies, many companies are turning to open source software, data and tools. But many do so without considering unmanaged risk in the AI Supply Chain. For example, current cybersecurity tooling does not account for ML-specific software vulnerabilities (e.g., arbitrary code execution in pytorch binary files), data vulnerabilities (e.g., corrupted datasets), or ML-specific behavioral vulnerabilities (e.g., universal triggers).
This is where the AI Risk Database comes in. Like a “VirusTotal for AI”, it provides an interface for community-driven reports about open source files, models and datasets. Only just released at the end of March 2023, the newly released tool has helped security researchers discover file vulnerabilities and model vulnerabilities in open source models generated by one provider. A major update at BlackHat arsenal will also include software scanning vulnerabilities provided by another 3rd-party provider.
In this hands-on demonstration, we’ll create vulnerable AI payloads and demonstrate their risk through the automated vulnerability scanning that powers AI Risk Database.
HazProne: Cloud Vulnerability Simulator
Date: Wednesday, August 9 | 1:00pm-2:30pm ( Business Hall — Arsenal Station 8 )
Tracks: Vulnerability Assessment, Exploitation and Ethical Hacking
Session Type: Arsenal
HazProne is a Cloud Vulnerability Simulator Framework that emulates close to Real-World Scenarios by deploying Vulnerable-By-Demand AWS resources enabling you to pentest Vulnerabilities within, and hence, gain a better understanding of what could go wrong and why!!
HIDE & SEEK: An Open Source Implant for Red Teams
Date: Wednesday, August 9 | 1:00pm-2:30pm ( Business Hall — Arsenal Station 1 )
Tracks: Hardware / Embedded, Exploitation and Ethical Hacking
Session Type: Arsenal
Many Enterprises are shifting away from dedicated workstations and cubes, and moving to a more flexible workspace with thin client and desk hoteling. This creates the ideal landscape for hardware implant attacks. The current implant market, as it exists today, has not kept up with this shift. While closed source for-profit solutions exist, by their nature they lack the flexibility and customization to adapt to large scale targeted deployments. Open source projects similarly exist but focus more on individual workstations (dumb keyboards and remote terminals) relying on corporate networks for remote control and are easily detectable. Neither solution today is able to meet the needs of a modern Red Team.
This presentation introduces an open source, freely available hardware implant which adopts modern IoT technologies, leveraging non-standard communication channels to create a remotely managed mesh network of hardware implants. Attendees will learn about the new techniques and tactics that we used to create a new breed of open-source hardware implant. Topics covered in this presentation will include the scaling of implants for a stealthy enterprise takeover, creating and utilizing a flexible command and control mesh network, creating a new class of remote access shells that survive idle screen lock, and more. Attendees will leave the talk with new tactics and a new platform from which to innovate their own custom implants from. Live demos will be used to demonstrate these new tactics against real world infrastructure.
Previous hardware implant talks have covered: basic implants, their benefits, injecting keystrokes, Wi-Fi connectivity, and attack scripts. This presentation builds off of those but shows attendees how to leverage new techniques and technologies to push the innovation of hardware implants forward evolutionarily for use in today’s modern Red Team operations.
Identity Threat Hunting with Kestrel
Paul Coccoli
Sulakshan Vajipayajula
Ritesh Kumar
Date: Wednesday, August 9 | 1:00pm-2:30pm ( Business Hall — Arsenal Station 6 )
Tracks: , Network Defense
Session Type: Arsenal
Damn Vulnerable Bank
Rewanth Tammana
Hrushikesh Kakade
Akshansh Jaiswal
Date: Wednesday, August 9 | 2:30pm-2:30pm ( Business Hall — Arsenal Station 8 )
Track: Android, iOS and Mobile Hacking
Session Type: Arsenal
With over 2.5 billion devices and millions of apps, Android is ruling the market. Developers had additional responsibility to protect the information and integrity of their users. Considering these high numbers, preventive measures should be taken to secure Android applications used by people across the globe.
We built an open-source vulnerable Banking application, a clone close to real-world banking applications. The existing vulnerable applications cover only basic OWASP vulnerabilities. Our vulnerable application covers multiple things like Binary analysis, Debugger detection bypasses, Frida analysis, writing custom code to decrypt data, and a lot more along with basic OWASP vulnerabilities. This product will be a one-stop place for android application security enthusiasts.
SSHook: A Lightweight Syscall Hooking Tool for Uncovering Hidden Malicious Instructions
Date: Wednesday, August 9 | 2:30pm-4:00pm ( Business Hall — Arsenal Station 6 )
Tracks: Android, iOS and Mobile Hacking, Malware Defense
Session Type: Arsenal
Most Android hook ways aim at watching APIs for Java or Native code. However, some malicious apps try to escape hooking and access sensitive data using syscall directly, so it is crucial in order to uncover hidden code that some malicious apps use to bypass standard hooking techniques and access sensitive data directly through system calls. We have implemented a syscall hooking tool based on Seccomp-BPF named SSHook, which gives better balance between performance and compatibility.
Seccomp-BPF was introduced into Linux kenel to filter syscalls and their arguments, we transform this security feature into a syscall hook framework which support devices range from Android 8.1 to Android 13. Our tool SSHook combined Seccomp-BPF with throwing an exception to catch syscall, and resuming instructions for normal execution by preparing additional threads earlier, which avoids frequent interruptions and possible risks like deadlocks, suspensions, or crashes. For performance improvement, we have implemented a flag that determines whether to resume execution using either the inactive parameter or the higher 4 bytes of an integer type, but the program can still run normally without any impact. Besides, SSHook is a lightweight framework but performs efficiently and robustly compared with other invasive or complicated solutions, which keep stable and reliable by standing on the shoulders of kernel features.
SSHook can help to identify suspicious behavior in malicious Apps which abuse syscall to steal privacy files or collect sensitive data like MAC, applist, which can be integrated into sandbox environment to conduct more complete dynamic analysis. Furthermore, SSHook allows us to replace syscall arguments and bypass hooking tools to evade detection, which is particularly useful in preventing the collection of device fingerprints and protecting user privacy against tracking.
Z9 — Malicious PowerShell Script Analyzer
Date: Wednesday, August 9 | 2:30pm-4:00pm ( Business Hall — Arsenal Station 4 )
Tracks: Reverse Engineering, Malware Defense
Session Type: Arsenal
Reversing a malicious PowerShell script can be a very tedious and time-consuming process, especially when the script is obfuscated. Z9 provides an efficient solution to this problem. It is a PowerShell script analyzer that can quickly deobfuscate the script and determine whether it is malicious or not. Z9 leverages several detection engines to make an informed decision.
* Obfuscation Detection
* Randomized String Detection
* URL Extractor
* Blacklist
* AI (Logistic Regression)
* Sandbox
EmploLeaks: Finding Leaked Employees Info for the Win
Gabriel Franco
Javier Aguinaga
Date: Wednesday, August 9 | 4:00pm-5:30pm ( Business Hall — Arsenal Station 8 )
Tracks: Exploitation and Ethical Hacking, OSINT — Open Source Intelligence
Session Type: Arsenal
BLE CTF — A Bluetooth Low Energy Security Research Platform
Date: Thursday, August 10 | 10:00am-11:30am ( Business Hall — Arsenal Station 7 )
Track:
Session Type: Arsenal (ALSO AT DEFCON 31)
BLE CTF is a series of Bluetooth Low Energy challenges in a capture the flag format. It was created to teach the fundamentals of interacting with and hacking Bluetooth Low Energy services. Each exercise, or flag, aims to interactively introduce a new concept to the user.
Over the past few years, BLE CTF has expanded to support multiple platforms and skill levels. Various books, workshops, trainings, and conferences have utilized it as an educational platform and CTF. As an open source, low cost of entry, and expandable education solution, BLE CTF has helped progress Bluetooth security research.
This demo will showcase the BLE CTF platform and its new variants. This will be the first public release of the CTF’s newly supported hardware and companion firmware. Along with firmware for newly supported devices, a new expansion for the modular BLE CTF Infinity will be exhibited.
Dracon, Security Engineering Automation, No Code, At Your Fingertips
Spyros Gasteratos
Vijendra Patel
Date: Thursday, August 10 | 10:00am-11:30am ( Business Hall — Arsenal Station 9 )
Track:
Session Type: Arsenal
Dracon is an open source, Application and Cloud Security Orchestration and Correlation (ASOC) platform, empowering organisations to establish and manage comprehensive application security programs. By creating customizable pipelines, Dracon enables the execution of a wide range of security tools against any target. During a pipeline execution Dracon runs user-configured tools in parallel. Concurrently, results from each tool are deduplicated, enriched with information based on organisational or regulatory policies, compliance requirements, and more, before being forwarded to any visualisation or data processing sink.
The primary objective of Dracon is to offer a scalable and flexible framework that enables execution of arbitrary security tools on code and infrastructure while processing the results in a versatile manner. Under the hood, Dracon runs parallel user-configured security tools(Producer Stage), aggregates, and transforms the results into an internal format.
Once results are normalised, Dracon can apply user defined information enrichment. An enricher is custom code that allows users to enhance the information presented based on internal policies and compliance requirements. Out of the box, Dracon supports Deduplication, Policy and SBOM information enrichers, while writing a new enricher is made easy for the user with the help of provided libraries.
Finally, Dracon directs enriched results to a layer of user-configurable Consumers. A consumer can be any data visualisation, alerting or vulnerability management solution. This powerful, extensible platform simplifies security engineering and enables organisations to strengthen their cybersecurity posture.
Emulating Any HTTP Software as a Honeypot with HASH: A Deceptive Defense Against Cyberattacks
Date: Thursday, August 10 | 10:00am-11:30am ( Business Hall — Arsenal Station 2 )
Tracks: Web AppSec, Network Defense
Session Type: Arsenal
HASH (HTTP Agnostic Software Honeypot), an open-source framework for creating and launching low interaction honeypots. With simple YAML configuration files HASH can simulate any HTTP based software with built in randomization capabilities to avoid being identified.
GodEye: Advanced Geo-Localization Through AI-Powered Visual Analysis
Tung Cao Hoang
Son Le Duy
Hieu Nam Tran Ngoc
Anh Nguyen Ngoc
Date: Thursday, August 10 | 11:30am-1:00pm ( Business Hall — Arsenal Station 6 )
Track: OSINT — Open Source Intelligence
Session Type: Arsenal
God Eye is an innovative AI-powered geo-localization tool that can estimate a photograph’s location without the need for EXIF data extraction. God Eye aims to improve the accuracy of current geolocation estimation techniques by combining cutting-edge models and techniques. The tool has a straightforward web-based interface that allows users to upload images and receive location estimates automatically. God Eye constantly improves its accuracy and expands its capabilities by comparing and training with open street view data and other crawled data sources. God Eye’s primary applications are in open-source intelligence (OSINT) and cybersecurity, where it aids forensic investigations by identifying image source and location. God Eye, with its robust technology and user-friendly design, is poised to become an indispensable tool for professionals in a variety of fields who require precise and dependable image-based geolocation.
CLExtract: An End-to-End Tool Decoding Highly Corrupted Satellite Stream from Eavesdropping
Minghao Lin
Minghao Cheng
Yueqi Chen
Xu Zheng
Dongsheng Luo
Date: Thursday, August 10 | 1:00pm-2:30pm ( Business Hall — Arsenal Station 2 )
Tracks: Internet of Things, Hardware / Embedded
Session Type: Arsenal
While satellite communication with ground stations can be eavesdropped on using consumer-grade products, the received signals are oftentimes highly corrupted and cannot be effectively decoded using the traditional finite-state machine (FSM) based approach.
To this end, we develop a tool named CLExtract which utilizes contrastive learning techniques to decode and recover corrupted satellite streams. Unlike the traditional FSM-based approach which relies on critical fields that become unreliable after corruption, CLExtract directly learns the features of packet headers at different layers and identifies them in a stream sequence. By filtering out these headers, CLExtract extracts the innermost payload which contains sensitive and private data. Further, CLExtract incorporates data augmentation techniques to entitle the trained contrastive learning models with robustness against unseen forms of corruption.
To evaluate CLExtract, we performed eavesdropping on the spectrum range from 11 GHZ to 12.75 GHZ in a suburban area of a metropolis with more than 10 million of population in Asia, covering radio signals from seven commercial satellites. CLExtract can successfully decode and recover 71–99% of the total 23.6GB eavesdropped data, a significant improvement over the traditional FSM-based approach implemented by GSExtract which only recovers 2%.
During the arsenal presentation, we will make CLExtract open source and demonstrate its usage to the security community using real-world satellite streams. This way, we hope to foster future research on satellite offense and defense techniques.
PurpleOPS — A Simple Tool to Help Track and Share Purple Team Data
Willem Mouton
Harrison Mitchell
Date: Thursday, August 10 | 1:00pm-2:30pm ( Business Hall — Arsenal Station 3 )
Track:
Session Type: Arsenal
Purple team exercises are probably one of the most useful types of activities that organizations can engage in these days. Key to effective purple teaming is good communication, data collection and knowledge sharing. For us, this has been a bit of a pain point having to try and manually keep track of activities, actions and events. We did find some tools to aid with this, but none of them truly opensource or flexible enough to allow us to do what we wanted to do. So we built PurpleOPS, which is at its core a data collection tool aligned to MITRE ATT&CK and integrated into other fantastic open-source projects such as Atomic Redteam. It is easy to customize with your own internal knowledge base and test cases, plus it’s also written in python3 using Flask, so it’s super easy to adjust to your needs.

BLACK HAT USA MEET & GREETS
This year, attendees will be able to connect with select industry experts through new Meet & Greet Sessions scheduled during both days of the conference. Participate in a Meet & Greet to ask a speaker from your favorite session a question, introduce yourself to a Review Board member, or take a photo with a new connection.
WEDNESDAY | 11:00AM
- Meet & Greet with Sharon Brizinov
- Speaker: Sharon Brizinov
- Track: Meet & Greet
- Location: Meetup Lounge, Business Hall
WEDNESDAY | 12:00PM
- Meet & Greet with Allison Miller
- Speaker: Allison Miller
- Track: Meet & Greet
- Location: Meetup Lounge, Business Hall
- Meet & Greet with Daniel Woods
- Speaker: Daniel Woods
- Track: Meet & Greet
- Location: Meetup Lounge, Business Hall
WEDNESDAY | 1:00PM
- Meet & Greet with Ali Ahmed
- Speaker: Ali Ahmed
- Track: Meet & Greet
- Location: Meetup Lounge, Business Hall
- Meet & Greet with Trevor Rosen
- Speaker: Trevor Rosen
- Track: Meet & Greet
- Location: Meetup Lounge, Business Hall
WEDNESDAY | 2:00PM
- Meet & Greet with Zhenpeng Lin
- Speaker: Zhenpeng Lin
- Track: Meet & Greet
- Location: Meetup Lounge, Business Hall
WEDNESDAY | 3:00PM
- Meet & Greet with Michael Kouremetis
- Speaker: Michael Kouremetis
- Track: Meet & Greet
- Location: Meetup Lounge, Business Hall
- Meet & Greet with Stiv Kupchik
- Speaker: Stiv Kupchik
- Track: Meet & Greet
- Location: Meetup Lounge, Business Hall
WEDNESDAY | 4:00PM
- Meet & Greet with Mika Devonshire
- Speaker: Mika Devonshire
- Track: Meet & Greet
- Location: Meetup Lounge, Business Hall
- Meet & Greet with Matthew Canham
- Speaker: Matthew Canham
- Track: Meet & Greet
- Location: Meetup Lounge, Business Hall
WEDNESDAY | 5:00PM
- Meet & Greet with Guanxing Wen
- Speaker: Guanxing Wen
- Track: Meet & Greet
- Location: Meetup Lounge, Business Hall
- Meet & Greet with Jonathan Birch
- Speaker: Jonathan Birch
- Track: Meet & Greet
- Location: Meetup Lounge, Business Hall
WEDNESDAY | 5:30PM
- Meet & Greet with Jason Healey
- Speaker: Jason Healey
- Track: Meet & Greet
- Location: Meetup Lounge, Business Hall
- Meet & Greet with Justine Bone
- Speaker: Justine Bone
- Track: Meet & Greet
- Location: Meetup Lounge, Business Hall
THURSDAY | 11:00AM
- Meet & Greet with Jen Easterly
- Speaker: Jen Easterly
- Track: Meet & Greet
- Location: Meetup Lounge, Business Hall
- Meet & Greet with Alex Ionescu
- Speaker: Alex Ionescu
- Track: Meet & Greet
- Location: Meetup Lounge, Business Hall
THURSDAY | 12:00PM
- Meet & Greet with Michael Bargury
- Speaker: Michael Bargury
- Track: Meet & Greet
- Location: Meetup Lounge, Business Hall
- Meet & Greet with Zach Edwards
- Speaker: Zach Edwards
- Track: Meet & Greet
- Location: Meetup Lounge, Business Hall
THURSDAY | 1:00PM
- Meet & Greet with Daniel Moghimi
- Speaker: Daniel Moghimi
- Track: Meet & Greet
- Location: Meetup Lounge, Business Hall
- Meet & Greet with Stephen Reynolds
- Speaker: Stephen Reynolds
- Track: Meet & Greet
- Location: Meetup Lounge, Business Hall
THURSDAY | 2:00PM
- Meet & Greet with Brian Smith-Sweeney
- Track: Meet & Greet
- Location: Meetup Lounge, Business Hall
- Meet & Greet with Kaileigh McCrea
- Speaker: Kaileigh McCrea
- Track: Meet & Greet
- Location: Meetup Lounge, Business Hall

SPONSORED SESSIONS & WORKSHOPS HIGHLIGHTS (PST)
Purple Teaming with Detection-as-Code for Modern SIEM
Ken Westin | Field CISO, Panther
Date: Wednesday, August 9 | 10:20am-12:20pm ( Oceanside E )
Format: Half-Day Sponsored Workshop
Tracks: Security Operations & Incident Response, Cloud Security
We will demonstrate how modern organizations use Purple team techniques to develop hypotheses for new detections and strengthen their defenses against future attacks.
Our approach: We will use open-source offensive security tools to simulate attacks against lab infrastructure and use an investigative approach to learn and build new detections & manage them using detection-as-code principles to eliminate noise and false positives.
Who should attend?
This hands-on workshop is perfect for detection & security engineers who are expected to develop and write detections to support new log sources, threat models, and vulnerabilities that are exploited in the wild
Purple Teaming with Detection-as-Code for Modern SIEM
Ken Westin | Field CISO, Panther
Date: Wednesday, August 9 | 10:20am-12:20pm ( Oceanside E )
Format: Half-Day Sponsored Workshop
Tracks: Security Operations & Incident Response, Cloud Security
We will demonstrate how modern organizations use Purple team techniques to develop hypotheses for new detections and strengthen their defenses against future attacks.
Our approach: We will use open-source offensive security tools to simulate attacks against lab infrastructure and use an investigative approach to learn and build new detections & manage them using detection-as-code principles to eliminate noise and false positives.
Who should attend?
This hands-on workshop is perfect for detection & security engineers who are expected to develop and write detections to support new log sources, threat models, and vulnerabilities that are exploited in the wild
Anatomy of a Social Engineering Attack
AJ Nash | Vice President & Distinguished Fellow of Intelligence, ZeroFox
Date: Wednesday, August 9 | 10:55am-11:15am ( Mandalay Bay L )
Format: 20-Minute Sponsored Session
Tracks: Data & Collaboration Security, Risk, Compliance and Security Management
In this presentation we walk through the process of a social engineering attack:
• Reconnaissance: How adversaries choose targets, conduct research, and set up infrastructure to support a successful social engineering attack. This includes looking at the role the Dark Web and covert communications channels (e.g., Discord and Telegram) in creating and growing motivations that lead to target lists and operational plans for attacks that begin with social engineering.
• Setting the Hook: How adversaries engage their target(s) and build relationships that become the foundation for witting or unwitting compromises of targeted organizations.
• Extraction: The common steps for eliciting or stealing access and information. We’ll provide examples of tactics used to turn conversation into compromise.
• Disengagement: How adversaries disconnect from social engineering victims.
- Basic: Overtly threatening a victim to maintain silence
Advanced: Disengage without a victim realizing they’ve been targeted
Finally, we’ll provide tips for more safely engaging with new people online and in the real world.
Raising Files From Ransomware Ashes — How To Beat Intermittent Encryption
Andy Thompson | Research Evangelist, CyberArk
Date: Wednesday, August 9 | 11:30am-12:20pm ( Mandalay Bay J )
Format: 50-Minute Sponsored Session
Tracks: Data & Collaboration Security, Security Operations & Incident Response
Intermittent encryption is the latest trend in ransomware — it’s faster than traditional encryption methods and can fly under the radar of many EDR solutions. Though it presents malicious actors with a massive opportunity — it does have an Achilles heel. White Phoenix, a new open-source tool created by CyberArk Labs, takes advantage of the fact that the kidnapped files aren’t entirely encrypted and can, in the right circumstances, salvage content from the unencrypted portions of the files.
Come learn about how to leverage bugs in ransomware to recover files and see exactly how White Pheonix works.
Discovering New Value Equations that Phishing Simulations Can Have on Your Team
Tiffany Ricks | CEO & Founder, HacWare
Date: Wednesday, August 9 | 12:05pm-12:25pm ( Start-Up City Theater )
Format: 20-Minute Start-Up City Sponsored Session
Tracks: Managed Security Services, Risk, Compliance and Security Management
Organizations are targeted by 700+ social engineering and BEC attacks annually, but many struggle to implement the right-sized cybersecurity training for their teams. Effective training educates users on how to recognize and report attacks while taking company cultural norms, industry attack vectors, phishing level of difficulty and timing into account — but a comprehensive training program alone is not enough to create change in an organization.
In this 20-minute session, Tiffany Ricks will leverage her background in ethical hacking and security awareness training to highlight the mistakes security teams make when implementing and running their training programs. She’ll discuss the opportunity created for hackers when organizations fear employee backlash more than real phishing attacks, and how common mistakes by security teams can lead to hostile work environments and insider threats from disengaged or disgruntled employees.
Ricks will speak to security team challenges and the risk of end user disengagement from first hand experience as the founder and CEO of HacWare, an innovative, AI-driven security awareness training platform. Using her knowledge of the industry alongside interviews with behavioral psychologists and other security awareness practitioners, Ricks will showcase the ways security teams and users can work together to create new value equations for cybersecurity and human risk management.
AI in Action: Protecting the City of Las Vegas from Every Stage of the Attack Lifecycle
Matt Bovbjerg | VP, Integrations Architecture, Darktrace
Michael Sherwood | Chief Innovation Officer, City of Las Vegas
Date: Wednesday, August 9 | 12:40pm-1:30pm ( Business Hall Theater A )
Format: 50-Minute Sponsored Session
Tracks: Security Operations & Incident Response, Risk, Compliance and Security Management
With over 40 million visitors a year and high-profile events like the 2023 Formula 1 Grand Prix and the 2024 Super Bowl; the City of Las Vegas is under constant pressure to innovate, while also mitigating risk. The desire to remain one step ahead has become even more challenging in a threat landscape completely transformed by generative AI technologies, yet The City of Las Vegas is up for the task. Join this session to hear real-world examples and the technical details underpinning how AI is being put to practical use to mitigate an active security incident, determine the most effective path to eradicate the threat and recover to an operational state; therefore providing a complete lifecycle approach to cyber resilience. Darktrace experts will be joined by the City of Las Vegas to demonstrate how the latest innovations in AI-based cyber security can not only anticipate attacks, but withstand, recover from, and adapt to a whole range of emerging, yet to be categorized cyber threats.
Passkeys: Preventing Social Engineering Attacks in the Era of Generative AI
Anna Pobletts | Head of Passwordless, 1Password
Date: Wednesday, August 9 | 1:50pm-2:10pm ( Mandalay Bay L )
Format: 20-Minute Sponsored Session
Tracks: Identity and Access Management (IAM), Cloud Security
Online identity is rapidly evolving, but still reliant on humans protecting themselves from cyber threats. As major advancements in AI threaten to upskill the attacker, we’ll see more sophisticated, hyper-realistic, and strategic attacks. The ultimate goal should be removing human error altogether. A passwordless future with passkeys promises to do just that.
Join this session with Anna Pobletts, head of passwordless at 1Password, to discuss the evolution of social engineering attacks against authentication and identity systems and the crucial role that passkeys play in protecting users, their digital identities and shaping the future of security.
Secrets, Secrets Are no Fun: How Attackers Can Crack SSO to Steal Data
Brian Vecci | United States, Varonis
Date: Wednesday, August 9 | 3:00pm-3:20pm ( Business Hall Theater C )
Format: 20-Minute Sponsored Session
Tracks: Cloud Security, Security Operations & Incident Response
How secure is your Salesforce data? Let’s find out. We’ll walk you through how an attacker can use simple security tools, API calls, and scripting to steal Salesforce data and more. Posing as the threat actor, we’ll discover secrets through a public GitHub repo and use those findings to impersonate a user. From there, we’ll escalate privileges in Salesforce to find and exfiltrate sensitive data. Join us to see the attack unfold in real time and learn how to detect and defend against it every step of the way.
Addressing the OWASP API Security Top 10 2023
Filip Verloy | Field CTO, Noname Security
Date: Wednesday, August 9 | 3:35pm-3:55pm ( Business Hall Theater C )
Format: 20-Minute Sponsored Session
Track: Application Security
Now that the OWASP API Security Top 10 has seen its second release, we’ll dive into the changes from the previous version, dive into each category and show you how to address each one using a dedicated API security platform.
Join this session to understand the critical capabilities you need to protect your APIs, why it has become such a serious problem in the first place, and how we confidently move forward.
As API security is a team sport, we’ll address;
API security testing
API discovery
API posture management
API runtime security &
API access control
In just 20m you’ll get the insights you need to start or continue your journey towards secure APIs.
Cyber within the Air Force Civilian Service
Carlos Dye II | Software Developer/Air Force Civilian Service, Air Force Civilian Service
Steven G. Waters | Innovation Director/805 Combat Training Squadron/Shadow Operations Center-Nellis, Air Force Civilian Service
Date: Wednesday, August 9 | 4:10pm-5:00pm ( Mandalay Bay I )
Format: 50-Minute Sponsored Session
Track: Government & Nonprofit
Format: 2-person panel discussion.
Carlos Dye II aims to provide valuable insights into the challenges faced, accomplishments achieved, and possible growth potential opportunities within/outside the organization. With anecdotal experiences, Carlos Dye will go into depth about the dynamic nature of his profession, key factors that would contribute to a successful career, and the numerous opportunities that exist for employees to advance and thrive. Furthermore, Carlos Dye will unveil the captivating world of Federal Department of Defense employment and explore the cutting-edge technologies that make it an exhilarating choice for aspiring professionals.
Steven G. Waters’ presentation aims to highlight potential opportunities for cyber careers within the Air Force. In addition, Steven G. Waters will cover the process, challenges, and benefits associated with civilian service.
Session will conclude with a 10-minute Q&A.
Thirty Years of Arguing with Adults
Paul Dant | Senior Director, Cybersecurity Research, Illumio
Date: Wednesday, August 9 | 4:10pm-4:30pm ( Business Hall Theater C )
Format: 20-Minute Sponsored Session
Tracks: Security Operations & Incident Response, Cloud Security
In this talk, you’ll hear hilarious stories from a former child hacker that eerily predict the treacherous security landscape of today. Do you want to know why we’re still losing to ransomware? Attend this talk to find out and get insight into how you can start actually solving security problems and prepare your organization for the inevitable breach.
Security Fundamentals for Apple Platforms
Devin Byrd | Director of Threat Intelligence, Kandji
Date: Wednesday, August 9 | 4:45pm-5:05pm ( Mandalay Bay L )
Format: 20-Minute Sponsored Session
Tracks: Endpoint Security, Risk, Compliance and Security Management
Securing Apple devices have unique challenges for organizations that want to deliver productivity on these platforms. In this session, you will learn the fundamentals of security on macOS with some iOS as well. Get hands-on with the native Apple security tools and learn where security professionals can deliver additional value to their organizations.
1. This session will give you a comprehensive overview of security tooling on Apple platforms, especially macOS
2. You will become familiar with Xprotect, Gatekeeper, SIP, MRT, and more native tools that provide valuable protection against basic attacks
3. Learn about the Endpoint Security Framework, a new API for monitoring file events to protect against infection and spread of threats
4. Persistence on Apple devices can be achieved through a few means, see what those are and how to monitor them
5. You’ll see next steps to continue learning on a wide range of security topics for Apple operating systems
2023 AT&T Cybersecurity Insights Report: Edge Ecosystem
Theresa Lanowitz | Head of Cybersecurity Evangelism — AT&T Business, AT&T Cybersecurity Services
Date: Wednesday, August 9 | 5:20pm-5:40pm ( Business Hall Theater C )
Format: 20-Minute Sponsored Session
Track: Managed Security Services
The AT&T Cybersecurity Insights Report is an annual thought-leadership report based on a global survey of over 1,400 IT, security, networking, development, and line of business professionals across seven industries. The research is vendor-neutral, forward-looking, and actionable.
The journey to edge is a collaborative endeavor that begins to erode organizational silos and foster closer working relationships. The right edge ecosystem partners bolster resilience and security — critical elements of edge computing solutions, especially as the attack surface expands.
The AT&T Cybersecurity InsightsTM Report: Edge Ecosystem examines how organizations are changing to support edge, why planning for the edge takes an ecosystem of partners, why investing in edge use cases drives competitive differentiation.
The discussion provides insight into:
• What the business drivers are for edge use cases
• Where edge use cases are being deployed
• How budgets are shifting to support edge
What Current Dark Web Threats Matter? Spotlighting the Threats Enterprises Should Care About
Thomas “Mannie” Willkan | Senior Dark Web Analyst, Cyber Threat Intelligence, Accenture
Date: Thursday, August 10 | 10:20am-11:10am ( Mandalay Bay I )
Format: 50-Minute Sponsored Session
Tracks: Risk, Compliance and Security Management, Security Operations & Incident Response
Decision makers, analysts and researchers across industries face a deluge of information about emerging threats and the latest cyber-security developments. Although this influx of analysis provides numerous benefits, the amount of data contributes to information overload and decision fatigue, leading to “analysis paralysis” when timely action is the most paramount.
In this presentation, the Accenture Cyber Threat Intelligence (ACTI) Recon Team will examine and explain which current Dark Web threat matter, how they impact victims and why these should be prioritized by businesses for mitigation. Leveraging proprietary research, real-world case studies and in-depth experience in exploring Dark Web sites, the team will provide valuable insights for businesses to prioritize their enterprise efforts.
We will examine the key threats, including the escalating risk to macOS systems, as well as the pervasive threat of pure data extortion, the emergence of a new breed of information-stealers, a rising dark-web focus on operational technology (OT) environments and the rapidly advancing dangers posed by deepfakes. Through a comprehensive analysis of these threats, attendees will gain a better understanding of threat implications and will be equipped with actionable strategies to safeguard their organizations based on information allowing enterprises to better prioritize mitigation of dark web threats.
Keeping Assets Secure in the Quantum Era
Jen Sovada | President, Public Sector, SandboxAQ
Date: Thursday, August 10 | 12:40pm-1:00pm ( Business Hall Theater C )
Format: 20-Minute Sponsored Session
Tracks: Risk, Compliance and Security Management, Application Security
As innovation in quantum technology accelerates, it is imperative for government agencies and enterprise companies to invest in cryptographic management to secure their assets and mitigate risk. As the cybersecurity threat landscape continues to evolve and attacks become more sophisticated, organizations must transition to PQC and implement cryptographic agility in order to protect their most sensitive data, transactions and communications — even before quantum computers arrive.
Jen Sovada, President of Public Sector for SandboxAQ, will discuss what steps leaders must take to protect U.S. and allied national security, business integrity and citizens’ privacy.
The Mesh is the next Web.
Manu Fontaine | Founder & CEO, Hushmesh Inc.
Date: Thursday, August 10 | 1:15pm-1:35pm ( Start-Up City Theater )
Format: 20-Minute Start-Up City Sponsored Session
Tracks: Infrastructure Protection, Identity and Access Management (IAM)
The Web has “World Wide Weaknesses”. Its reliance on human administration and weak relational links leave it vulnerable to maladministration. Such architectural vulnerabilities cannot be eliminated no matter how much security is bolted on after the fact.
Data has become as critical to society as stable electricity and clean water. The recent emergence of Confidential Computing gives us new groundbreaking capabilities to fundamentally rethink the foundations of our global digital infrastructure, with cryptographic security built in.
Join this session to learn how the Mesh solves global identity, trust, data security, authenticity, confidentiality and privacy for everyone and everything.
Enterprise Browser in the Evolving Security Landscape
Kiran Nair | Product Manager, Chrome, Google Chrome
Date: Thursday, August 10 | 1:50pm-2:10pm ( Mandalay Bay L )
Format: 20-Minute Sponsored Session
Tracks: Data & Collaboration Security, Endpoint Security
The web browser has become an integral part of an enterprise’s security strategy in recent years, as more and more work is being done on the web. To shed light on the current cybersecurity landscape and to help enterprises stay ahead of the game, we are hosting a session to discuss the best practices to ensure the safety of your users while enabling them to work productively on the web.
Two Truths and One Falsehood about AI and Cybersecurity
Ryan Alban | Director, Global Solution Leads, Secureworks
Date: Thursday, August 10 | 3:00pm-3:20pm ( Mandalay Bay L )
Format: 20-Minute Sponsored Session
Tracks: Security Operations & Incident Response, Managed Security Services
With AI at the center of most cybersecurity discussions today, we’ll take a practical view to separate the hype from what can drive real value in your security operations. In this session, Secureworks’ Ryan Alban, Director of Global Presales Strategy and Operations, will share practical experience from Secureworks as well as information about real models leveraging large volumes of data. He’ll share two things every cybersecurity professional should know about AI — and one falsehood that might otherwise lead you astray. Join this session and learn to decipher the truth from the hype.

DCG 201 TALK HIGHLIGHTS FOR BLACK HAT USA 2023 (PST)
This is the section where we have comb through the entire list of talks on both days and list our highlights for the talks that stand out to us. Note that this does not invalidate any talks we didn’t list, in fact, we highly recommend you take a look at the full convention schedule beforehand and make up your own talk highlight lists. These are just the talks that for us had something stand out, either by being informative, unique or bizarre. (Sometimes, all three!)
WEDNESDAY, AUGUST 9th
Keynote: Guardians of the AI Era: Navigating the Cybersecurity Landscape of Tomorrow
Maria Markstedter | Founder, Azeria Labs
Date: Wednesday, August 9 | 9:00am-10:00am ( Shoreline Ballroom, Level 2 )
Format: 60-Minute Keynote
Track: Keynote
As we usher in the Age of AI, cybersecurity stands at the precipice of unprecedented challenges and transformative opportunities. This keynote is designed for those at the forefront of this evolution — cybersecurity professionals ready to understand, adapt, and innovate in a world reshaped by AI.
We’ll start our journey with a brief history of information processing — from the invention of the printing press to today’s world of artificial intelligence for data processing and decision making. Which milestones have brought us here? Each step along this path has steadily increased our interconnectivity and, by extension, our vulnerabilities.
The current year has witnessed a dramatic surge in use cases for generative AI. How is AI reshaping the world, and consequently, the cybersecurity landscape? What are the potential benefits and risks associated with the democratization of certain AI capabilities?
AI’s capabilities can be a double-edged sword — a potent tool for both advancing the effectiveness of our existing security products and the emergence of more sophisticated threats.
What challenges will AI bring to the cybersecurity industry? How will the relentless pace of AI development affect our ability to navigate new attack surfaces? How can we as cybersecurity professionals evolve with the AI revolution and use it to our advantage?
As we stand on the edge of possibility, it’s time to delve into the future of cybersecurity in a world dominated by AI.
Civil Cyber Defense: Use Your Resources to Defend Non-Profits as They Combat Human Trafficking and Subvert Authoritarian Regimes
Tiffany Rad | Instructor, U.C. Berkeley
Austin Shamlin | Founder, Traverse Project
Date: Wednesday, August 9 | 10:20am-11:00am ( Jasmine AE, Level 3 )
Format: 40-Minute Briefings
Tracks: Community & Career, Privacy
Civil Cyber Defense volunteers and students challenge high-risk adversaries and threats such as human traffickers, authoritarian regimes, and surveillance being conducted on journalists. By utilizing academic resources, OSINT skills, and free/open-source tools, civil cyber defenders are supporting vulnerable non-profits, protecting volunteers, journalists, and activists while defending human rights.
There is a need in the cybersecurity industry for more civil cyber defenders. Recommendations will be made as to how your organization can support and/or volunteer your time and tools to provide protection to vulnerable organizations that have high risks, face advanced and persistent adversaries, but have modest resources.
Video-Based Cryptanalysis: Recovering Cryptographic Keys from Non-compromised Devices Using Video Footage of a Device’s Power LED
Ben Nassi | Postdoctoral Researcher, Cornell Tech
Etay Iluz | Security Researcher, Ben-Gurion University of the Negev
Date: Wednesday, August 9 | 10:20am-11:00am ( South Pacific F, Level 0 )
Format: 40-Minute Briefings
Tracks: Hardware / Embedded, Cryptography
In this talk, we present video-based cryptanalysis, a new method to recover secret keys from a non-compromised device by analyzing video footage obtained from a device’s power LED. We show that cryptographic computations performed by the device’s CPU change the power consumption, affecting the brightness/color of the device’s power LED. Based on this observation, we show how attackers can exploit commercial video cameras (e.g., of an iPhone 13 Pro Max or an Internet-connected security camera) to recover secret keys from devices. This is done by obtaining video footage from a device’s power LED (by filling the frame with the LED) and exploiting the video camera’s rolling shutter to increase the sampling rate by three orders of magnitude from the FPS rate (60–120 measurements per second) to the rolling shutter speed (60K measurements per second in iPhone 13 Pro Max). The frames of the video footage of the device’s power LED are analyzed in the RGB space, and the associated RGB values are used to recover the secret key by inducing the power consumption of the device from the RGB values.
We will show video demonstrations of the application of two side-channel cryptanalytic timing attacks used to recover: (1) a 256-bit ECDSA key from a smartcard by analyzing video footage obtained from the power LED of the smartcard reader via a hijacked Internet-connected security camera located 16 meters away from the smartcard reader, and (2) a 378-bit SIKE key from a Samsung Galaxy S8 by analyzing video footage obtained from the power LED of Logitech Z120 USB speakers that were connected to the same USB Hub (that was used to charge the Galaxy S8) via iPhone 13 Pro Max.
Finally, we discuss countermeasures, limitations, and the future of video-based cryptanalysis in light of the expected improvements in video cameras’ specifications.
Apple PAC, Four Years Later: Reverse Engineering the Customized Pointer Authentication Hardware Implementation on Apple M1
Zec Cai | Student, Zhejiang University
Jiaxun Zhu | Student, Zhejiang University
Yutian Yang | Student, Zhejiang University
Wenbo Shen | Professor, Zhejiang University
Yu Wang | Founder, CyberServal
Date: Wednesday, August 9 | 11:20am-12:00pm ( Islander FG, Level 0 )
Format: 40-Minute Briefings
Tracks: Reverse Engineering, Hardware / Embedded
Since 2018, Apple has deployed PA on all Apple-silicon-based products to improve the security of the system. There have been many incredible security researchers who have conducted in-depth analyses of the PA protection deployed by Apple. Notably, in the 2019 analysis blog “Examining Pointer Authentication on the iPhone XS” by Brandon Azad from Project Zero, he discovered that Apple uses some unknown “dark magic” on the PA hardware. So the customized PA on Apple Silicon can defend against cross-EL/Key attacks without software support. However, four years have passed and there is still no research to reveal the causes of these cross attack mitigations.
We found that this customized PA (Apple PA) was also deployed on Apple M1, and in addition, we found that Apple deployed hardware read/write protection for PA key registers. This hardware protection makes Apple PA difficult to reverse engineer since we can not control the value of PA key registers after Apple PA is enabled. To bypass this protection, we propose new techniques based on another hardware feature on Apple M1: Virtualization Host Extension (VHE).
Based on these new techniques, we successfully revealed the new PA hardware (registers and instruction behaviors) introduced by Apple. More specifically, we found that Apple introduces three new diversifiers and a per-key-type key transformation to implement four types of cross attack (Cross-VM/Key/Boot/EL) mitigations on the hardware level.
Badge of Shame: Breaking into Secure Facilities with OSDP
Dan Petro | Senior Security Engineer, Bishop Fox
David Vargas | Senior Security Consultant, Bishop Fox
Date: Wednesday, August 9 | 11:20am-12:00pm ( South Seas CD, Level 3 )
Format: 40-Minute Briefings
Tracks: Cyber-Physical Systems & IoT, Cryptography
Breaking into secure facilities used to be possible by inserting a listening device (such as an ESPKey) behind an RFID card reader and sniffing the unencrypted Wiegand badge numbers over the wire as they go to the backend controller. The physical security industry has taken notice and there’s a new sheriff in town: The encrypted protocol OSDP which is starting to be rolled into production. Surely encryption will solve our problems and prevent MitM attacks right? … right?
In this presentation, we’ll demonstrate over a dozen vulnerabilities, concerning problems, and general “WTF”s in the OSDP protocol that let it be subverted, coerced, and totally bypassed. This ranges from deeply in-the-weeds clever cryptographic attacks to boneheaded mistakes that undermine the whole thing. We will also demonstrate a practical pentesting tool that can be inserted behind an RFID badge reader to exploit these vulnerabilities.
Get your orange vest and carry a ladder, because we’re going onsite!
Jailbreaking an Electric Vehicle in 2023 or What It Means to Hotwire Tesla’s x86-Based Seat Heater
Christian Werling | PhD Student, TU Berlin
Niclas Kühnapfel | PhD Student, TU Berlin
Hans Niklas Jacob | PhD Student, TU Berlin
Oleg Drokin | Security Researcher,
Date: Wednesday, August 9 | 11:20am-12:00pm ( South Pacific F, Level 0 )
Format: 40-Minute Briefings
Tracks: Platform Security, Hardware / Embedded
Tesla has been known for their advanced and well-integrated car computers, from serving mundane entertainment purposes to fully autonomous driving capabilities. More recently, Tesla has started using this well-established platform to enable in-car purchases, not only for additional connectivity features but even for analog features like faster acceleration or rear heated seats. As a result, hacking the embedded car computer could allow users to unlock these features without paying.
In this talk, we will present an attack against newer AMD-based infotainment systems (MCU-Z) used on all recent models. It gives us two distinct capabilities: First, it enables the first unpatchable AMD-based “Tesla Jailbreak”, allowing us to run arbitrary software on the infotainment. Second, it will enable us to extract an otherwise vehicle-unique hardware-bound RSA key used to authenticate and authorize a car in Tesla’s internal service network.
For this, we are using a known voltage fault injection attack against the AMD Secure Processor (ASP), serving as the root of trust for the system. First, we present how we used low-cost, off-the-self hardware to mount the glitching attack to subvert the ASP’s early boot code. We then show how we reverse-engineered the boot flow to gain a root shell on their recovery and production Linux distribution.
Our gained root permissions enable arbitrary changes to Linux that survive reboots and updates. They allow an attacker to decrypt the encrypted NVMe storage and access private user data such as the phonebook, calendar entries, etc. On the other hand, it can also benefit car usage in unsupported regions. Furthermore, the ASP attack opens up the possibility of extracting a TPM-protected attestation key Tesla uses to authenticate the car. This enables migrating a car’s identity to another car computer without Tesla’s help whatsoever, easing certain repairing efforts.
Redacted Telecom Talk
Carlo Meijer | Founding Partner and Security Researcher, Midnight Blue
Wouter Bokslag | Founding Partner and Security Researcher, Midnight Blue
Jos Wetzels | Founding Partner and Security Researcher, Midnight Blue
Date: Wednesday, August 9 | 11:20am-12:00pm ( Mandalay Bay H, Level 2 )
Format: 40-Minute Briefings
Tracks: Cryptography, Hardware / Embedded
This talk will present an in-depth security analysis of a prominent telecommunications standard used globally by law enforcement, military, and critical infrastructure in the power, oil & gas, water, and transport sectors and beyond.
In this talk, we will discuss several severe flaws we uncovered allowing for practical interception and manipulation attacks by both passive and active adversaries. In addition, we will discuss the journey that enabled us to uncover these flaws which involved exploiting multiple zero-day vulnerabilities in a popular communications device and its trusted execution environment (TEE).
This talk will include a demonstration of interception capabilities as well as the publication of research materials in order to enable asset owners and the cyber-security industry at large to conduct further research on this important standard.
BingBang: Hacking Bing.com (and much more) with Azure Active Directory
Hillai Ben-Sasson | Security Researcher, Wiz
Date: Wednesday, August 9 | 11:20am-12:00pm ( Oceanside C, Level 2 )
Format: 40-Minute Briefings
Tracks: Cloud Security, Enterprise Security
In cloud-managed environments, exposing one of your most sensitive assets to external attackers can be as simple as clicking a checkbox. This was the case for Bing.com with their Azure Active Directory (AAD) integration, where a single misconfiguration enabled us to bypass authentication, alter search results, and launch XSS attacks on its users stealing their Office 365 tokens. However, Bing was not an isolated case. By inventing a new scanning technique to remotely map AAD misconfigurations, we identified thousands of exposed applications across the internet.
In this talk, we will present our novel technique for hunting misconfigurations on Azure AD, one of the most common Identity Providers on the internet. We will detail several pitfalls that we found in AAD integrations, from misconfigurations to design flaws, each of them resulting in complete authentication bypass on affected applications — essentially rendering the identity provider useless.
We will then detail our approach for mapping exposed cloud resources, scanning the web to find vulnerable applications, and narrowing down the results to high-profile targets. As a case study, we will demonstrate how we utilized this technique to bypass authentication on several highly sensitive Microsoft enterprise applications, including an internal CMS that allowed us to take over Bing.com.
Join us to learn how to identify and map exposed Azure AD applications, as well as how to protect them in your environment.
dr1v3by! Broken 802.11 Wifi Driver Leads to Millions of Vulnerable Cars
Omri Ben Bassat | Security Researcher, Microsoft
Date: Wednesday, August 9 | 1:30pm-2:10pm ( Mandalay Bay H, Level 2 )
Format: 40-Minute Briefings
Tracks: Cyber-Physical Systems & IoT, Exploit Development
Nowadays it’s almost mandatory for every automaker to have its own slick, modern, smart, and connected infotainment system. Despite the very modern look and feel of these systems, some of them are based on traditional RTOS (such as those used in PLCs/IoT/Embedded devices) and are often built using 3rd party legacy hardware components which eventually expose the vehicle to different supply chain attack vectors.
In our research we successfully implemented a full remote exploit chain, from within the Wifi range of the car, against a brand new unaltered, and fully patched vehicle of a major US based vendor, affecting millions of cars that have been shipped as early as 2015.
In this talk, we’ll discuss in technical depth a 0-day RCE vulnerability we found in legacy proprietary SoftMAC Wifi driver, which is integrated into a popular infotainment system. We’ll explain the details of how we were able to remotely exploit this 3rd party modem via maliciously crafted 802.11 Wifi packets to achieve code execution and gain persistent remote shell access into the car.
We’ll also demonstrate how we were able to fingerprint the specific firmware version installed on almost every infotainment only by knowing the vehicle’s license plate number. Then showcase several relevant post-exploitation attack scenarios such as car ransomware, gathering GPS locations, eavesdropping on passengers, CAN bus message injection, and user mobile application account takeover which enables remote door unlocking and engine start. To conclude we’ll show a demo of a working POC exploit against a brand new car and finally tell about the disclosure process and vendor mitigations.
Physical Attacks Against Smartphones
Christopher Wade | Security Researcher,
Date: Wednesday, August 9 | 1:30pm-2:10pm ( South Seas AB, Level 3 )
Format: 40-Minute Briefings
Tracks: Mobile, Hardware / Embedded
Android devices are constantly improving their security to protect against attackers with physical access, with new protection techniques being added year-by-year. This talk aims to demonstrate vulnerabilities in modern Android smartphones that are still viable, despite the mitigations in place.
In the first phase of this talk, we will discuss the analysis and exploitation of vendor-customized versions of Android’s Recovery mode, demonstrating weaknesses that allow for privilege escalation to root, and traversal from Recovery to Android, without Bootloader access.
In the second phase, we will discuss weaknesses in the Secondary Bootloader of devices produced by a popular smartphone manufacturer. We will demonstrate how, using a vulnerability in the core USB stack, code execution can be achieved, and a modified Android image can be booted, without compromising the functionality of the device.
Small Leaks, Billions Of Dollars: Practical Cryptographic Exploits That Undermine Leading Crypto Wallets
Nikolaos Makriyannis | Cryptography Research Lead, Fireblocks
Oren Yomtov | Blockchain Research Lead, Fireblocks
Arik Galansky | VP of Technology, Fireblocks
Date: Wednesday, August 9 | 1:30pm-2:10pm ( Jasmine AE, Level 3 )
Format: 40-Minute Briefings
Tracks: Cryptography, Exploit Development
Multi-Party Computation (MPC) has become a common cryptographic technique for protecting hundreds of billions of dollars in cryptocurrency wallets. MPC algorithms are currently powering the wallets of Coinbase, Binance, Zengo, BitGo, Fireblocks and many other fintechs/banks servicing hundreds of millions of consumers and thousands of financial institutions.
This presentation examines the most common MPC protocols and implementations and shows that securing MPC remains a challenge for most companies.
We show practical key-exfiltration attacks requiring no more than a couple of hundred signatures (the severity of the exploit is evaluated by counting the number of signature-generation ceremonies the attacker participates in). Namely, we show three different attacks on different protocols/implementations requiring 256, 16, and *one* signature, respectively.
The Most Dangerous Codec in the World: Finding and Exploiting Vulnerabilities in H.264 Decoders
Willy Vasquez | PhD Student, The University of Texas at Austin
Stephen Checkoway | Associate Professor, Oberlin College
Hovav Shacham | Professor, The University of Texas at Austin
Date: Wednesday, August 9 | 2:30pm-3:00pm ( Mandalay Bay H, Level 2 )
Format: 30-Minute Briefings
Tracks: Platform Security, Exploit Development
Modern video encoding standards such as H.264 are a marvel of hidden complexity. But with hidden complexity comes hidden security risk. Decoding video today involves interacting with dedicated hardware accelerators and the proprietary, privileged software components used to drive them. The video decoder ecosystem is obscure, opaque, diverse, highly privileged, largely untested, and highly exposed — a dangerous combination.
We introduce H26Forge, a framework that carefully crafts video files to expose edge cases in H.264 decoders. H26Forge’s key insight is operating on the syntax elements rather than on the encoded bitstring to build syntactically correct but semantically spec-non-compliant video files. These videos cause H.264 decoders to find themselves in undefined states or unhandled errors when decoded.
We used H26Forge to uncover numerous vulnerabilities across the video decoder ecosystem, including kernel memory corruption bugs in iOS, memory corruption bugs in Firefox and VLC for Windows, and video accelerator and application processor kernel memory bugs in multiple Android devices. These bugs have been acknowledged by multiple vendors including Apple, Mozilla, and FFmpeg.
In this talk, we will share our experiences developing and using H26Forge to find vulnerabilities. H26Forge and its related tools are fully open source and available to participants. We will also explore how participants can use H26Forge to test the security of H.264 decoders on the platforms they use.
Bad io_uring: A New Era of Rooting for Android
Zhenpeng Lin | PhD Candidate, Northwestern University
Xinyu Xing | Associate Professor, Northwestern University
Zhaofeng Chen | Principle Security Researcher, CertiK
Kang Li | Chief Security Officer, CertiK
Date: Wednesday, August 9 | 3:20pm-4:00pm ( Jasmine AE, Level 3 )
Format: 40-Minute Briefings
Tracks: Exploit Development, Mobile
io_uring is a high-performance asynchronous I/O framework that was introduced in version 5.1 of the Linux kernel. Since its introduction, more than 100 vulnerabilities have been discovered in this subsystem. While there is extensive public exploitation against io_uring bugs in desktop Linux, no public research has targeted it in the Android kernel due to its strict restrictions on memory layout manipulation.
During this talk, we will detail our approach to achieving privilege escalation on Google Pixel 6 and Samsung S22 via CVE-2022–20409, a UAF io_uring bug. Firstly, we will briefly introduce io_uring, the vulnerability, and its memory corruption capabilities. We will then delve into the challenges of exploiting the Android kernel and present our novel exploitation techniques with a detailed step-by-step explanation. We will highlight the effectiveness, generality, and stability of our approach and provide insights into how these techniques work, as well as how to generalize them to exploit other use-after-free (UAF) bugs in both Android and desktop Linux.
Furthermore, we will discuss Samsung’s KNOX RKP and showcase a new approach to bypassing its security protection. Through this talk, we hope to provide valuable insights into io_uring exploitation and the challenges associated with exploiting the Android kernel.
Nothing but Net: Leveraging macOS’s Networking Frameworks to Heuristically Detect Malware
Patrick Wardle | Founder, Objective-See Foundation
Date: Wednesday, August 9 | 3:20pm-4:00pm ( Oceanside A, Level 2 )
Format: 40-Minute Briefings
Tracks: Network Security, Malware
As the majority of malware contains networking capabilities, it is well understood that detecting unauthorized network access is a powerful detection heuristic. However, while the concepts of network traffic analysis and monitoring to detect malicious code are well established and widely implemented on platforms such as Windows, there remains a dearth of such capabilities on macOS.
This talk aims to remedy this situation by delving deeply into a myriad of programmatic approaches capable of enumerating network state, statistics, and traffic, directly on a macOS host. We will showcase open-source implementations of relatively overlooked low-level APIs, private frameworks, and user-mode extensions that provide insight into all networking activity. And, by leveraging these techniques, you will learn how to efficiently and generically detect both known and unknown threats targeting macOS!
Over the Air, Under the Radar: Attacking and Securing the Pixel Modem
Farzan Karimi | Manager, Android Offensive Security, Google
Xuan Xing | Software Engineer, Google
Xiling Gong | Information Security Engineer, Google
Eugene Rodionov | Security Engineer, Google
Date: Wednesday, August 9 | 3:20pm-4:00pm ( Oceanside C, Level 2 )
Format: 40-Minute Briefings
Tracks: Mobile, Hardware / Embedded
To ensure Google Pixel devices are always at their most secure, the Android Red Team continuously attacks the riskiest areas of the phone. This allows us to proactively get ahead of bugs and protect the phone, before it’s even shipped to users.
The modem — or baseband — is a high risk, fundamental smartphone component because it accepts data from untrusted remote sources (over the air radio, cell tower, etc.). A vulnerability in the modem can lead to many kinds of remote compromises on a phone.
Modem security is currently a hot topic of research, attracting growing interest from security researchers, both in the industry and in academia. This wasn’t the case up until recently for a couple of reasons: most modem code is closed source, and testing it requires expensive hardware equipment. With some of these barriers being removed in recent years, due to the invention of software-defined radio (SDR) devices and public toolkits, the entry level into baseband security analysis has become more affordable.
This talk will cover multiple baseband remote code execution vulnerabilities in Pixel modems that could be launched with a software radio from as far as 3 miles away.
The talk will also demonstrate an over-the-air (OTA) remote code execution (RCE) targeting smartphones running the affected modem stack, allowing remote compromise of all impacted devices that fall into the range of a malicious cell tower. The team will showcase a proof of concept that demonstrates the ability to compromise devices via an SMS message or phone call with no user interaction required.
The Android Red Team worked closely with both internal and external partners to secure the modem implementation for millions of devices by implementing additional hardening and security mitigations in the modem code, and also evangelized the development of a fuzzing program within the manufacturer’s organization.
Shuffle Up and Deal: Analyzing the Security of Automated Card Shufflers
Joseph Tartaro | Principal Security Consultant, IOActive
Enrique Nissim | Principal Security Consultant, IOActive
Ethan Shackelford | Associate Principal Security Consultant, IOActive
Date: Wednesday, August 9 | 3:20pm-4:00pm ( Islander HI, Level 0 )
Format: 40-Minute Briefings
Tracks: Hardware / Embedded, Reverse Engineering
There’s a long history of cheating in the world of gambling, from hiding aces up your sleeve to developing modern hacks. So it’s no surprise that modern casinos are designed with security in mind; thousands of cameras watch every square inch of the floor, closely monitoring each table and machine. Nevertheless, cheating still occurs and can lead to millions of dollars in losses, not only to casinos but, in some games, to players as well.
This presentation will start by providing an overview of the standards defined by the International Gaming Standards Association (IGSA), which are used for communication and authentication in Electronic Gaming Machines (EGMs) and peripherals. We have found these standards to be concerning in terms of device security as they are not aligned with modern best practices for safeguarding embedded devices. On this line, we identified automated shuffler peripherals as an interesting and high-reward target.
Shufflers vary widely in terms of their features and capabilities, but one of the most popular is Shuffler Master’s Deck Mate. We will dig into the internals of both Deck Mate models to understand their inner workings and investigate the possibility of exploiting these devices to cheat.
Ultimately, we will show how these devices can be compromised, allowing us to cheat in a live poker game.
Keynote: A Fireside Chat with Jen Easterly and Viktor Zhora
Jen Easterly | Director, Cybersecurity and Infrastructure Security Agency
Viktor Zhora | Deputy Chairman , State Service of Special Communication and Information Protection
Date: Wednesday, August 9 | 4:20pm-5:00pm ( Shoreline Ballroom, Level 2 )
Format: 40-Minute Keynote
Track: Keynote
Jen Easterly
Jen Easterly is the Director of the Cybersecurity and Infrastructure Security Agency (CISA). She was nominated by President Biden in April 2021 and unanimously confirmed by the Senate on July 12, 2021. As Director, Jen leads CISA’s efforts to understand, manage, and reduce risk to the cyber and physical infrastructure Americans rely on every day. She is a proud Mom, a mental health advocate, a Rubik’s Cube enthusiast, and an aspiring electric guitarist.
Before serving in her current role, Jen was the head of Firm Resilience at Morgan Stanley, responsible for ensuring preparedness and response to business-disrupting operational incidents and risks to the Firm. She also helped build and served as the first Global Head of Morgan Stanley’s Cybersecurity Fusion Center, the Firm’s center of gravity for cyber defense operations.
Jen has a long tradition of public service, to include two tours at the White House, most recently as Special Assistant to President Obama and Senior Director for Counterterrorism and earlier as Executive Assistant to National Security Advisor Condoleezza Rice. She also served as the Deputy for Counterterrorism at the National Security Agency.
A two-time recipient of the Bronze Star, Jen retired from the U.S. Army after more than twenty years of service in intelligence and cyber operations, including tours of duty in Haiti, the Balkans, Iraq, and Afghanistan. Responsible for standing up the Army’s first cyber battalion, she was also instrumental in the design and creation of United States Cyber Command.
A distinguished graduate of the United States Military Academy at West Point, Jen holds a master’s degree in Philosophy, Politics, and Economics from the University of Oxford, where she studied as a Rhodes Scholar. She is the recipient of numerous honors and awards, including the 2023 Sisterhood Award from Girls Who Code; the 2022 National Defense University Admiral Grace Hopper Award; the 2021 Cybersecurity Ventures Cybersecurity Person of the Year Award; the 2020 Bradley W. Snyder Changing the Narrative Award, and the 2018 James W. Foley Legacy Foundation American Hostage Freedom Award.
A member of the Council on Foreign Relations and a French American Foundation Young Leader, Jen is the past recipient of the Aspen Finance Leaders Fellowship, the National Security Institute Visiting Fellowship, the New America Foundation Senior International Security Fellowship, the Council on Foreign Relations International Affairs Fellowship, and the Director, National Security Agency Fellowship.
Viktor Zhora
Deputy Chairman of the State Service of Special Communication and Information Protection of Ukraine on Digital Development, Digital Transformations and Digitalization (CDTO) since January 2021.
At the SSSCIP Mr. Zhora is responsible for cybersecurity in the Ukrainian digital infrastructure, supervises digital transformation and cybersecurity projects, CERT-UA and the State Cyberprotection Center.
He is a graduate of the Institute of Physics and Technology of the National Technical University of Ukraine and the Institute of Software Systems of the National Academy of Science of Ukraine. He is the author of numerous scientific publications on information security and actively supports cybersecurity education programs.
THURSDAY, AUGUST 10TH
Keynote: Acting National Cyber Director Kemba Walden Discusses the National Cybersecurity Strategy and Workforce Efforts
Kemba Walden | Acting National Cyber Director , Executive Office of the President
Date: Thursday, August 10 | 9:00am-10:00am ( Shoreline Ballroom, Level 2 )
Format: 60-Minute Keynote
Track: Keynote
Acting National Cyber Director Kemba Walden will discuss the finer details in the National Cybersecurity Strategy Implementation Plan and the National Cyber Workforce and Education Strategy.
All You Need is Guest
Michael Bargury | CTO, Zenity
Date: Thursday, August 10 | 10:20am-11:00am ( Oceanside C, Level 2 )
Format: 40-Minute Briefings
Tracks: Cloud Security, Enterprise Security
Azure AD guest accounts are widely used to grant external parties limited access to enterprise resources, with the assumption that these accounts pose little security risk. As you’re about to see, this assumption is dangerously wrong.
In this talk, we will show how guests can leverage undocumented APIs to bypass limitations and gain unauthorized access to sensitive business data and capabilities including corporate SQL servers, SharePoint sites, and KeyVault secrets. Furthermore, we will reveal how guests can create and control internal business applications to move laterally within the organization. All capabilities presented in the talk will be demonstrated with the default Office 365 and Azure AD configuration.
Next, we will drop PowerGuest, a powerful tool designed to uncover the true scope of guest access in your tenant. PowerGuest can automate limitation bypass, enumerate and dump all accessible data, and allow for interactive non-read actions by the researcher.
Finally, we will make up for shattering the illusion of guests having limited access by sharing concrete steps to harden your Azure AD and Office 365 configurations to prevent such attacks and suggest detection logic to catch them if a change in configuration is not possible.
Making and Breaking NSA’s Codebreaker Challenge
Rita Doerr | Academic Outreach Lead, NSA
Date: Thursday, August 10 | 10:20am-11:00am ( South Seas CD, Level 3 )
Format: 40-Minute Briefings
Track: Community & Career
For the past 10 years, the National Security Agency (NSA) has hosted the Codebreaker Challenge. This competition, written and run by NSA’s technical experts, includes a new theme and challenge each year. The challenges are custom designed by NSA to mimic a real-world problem NSA faces in its mission and include up to 10 rounds of increasing difficulty including code analysis and reverse engineering. Starting with only 5 schools in 2013, the program has grown exponentially. In 2022, more than 4,800 participants from 449 schools across the United States competed for bragging rights. Only 104 people (about 2%) successfully completed all 9 rounds of the challenge this past year.
For the very first time at Black Hat, the NSA will publicly share insights and lessons from running the Codebreaker Challenge. We will present details about the design of the 2022 challenge that focused on the NSA assisting FBI agents in responding to a US company that had been crippled by a ransomware attack.
Oven Repair (The Hardware Hacking Way)
Colin O’Flynn | CTO, NewAE Technology Inc.
Date: Thursday, August 10 | 10:20am-11:00am ( Oceanside A, Level 2 )
Format: 40-Minute Briefings
Tracks: Hardware / Embedded, Cyber-Physical Systems & IoT
Cooking a turkey one (Canadian) Thanksgiving, Colin’s oven displayed a 325F temperature, but the turkey took hours longer than expected! Thus began the realization his oven lies to him — and the temperature is often much cooler than claimed.
The Samsung oven in question has this as a common complaint online, but without a solution. The solution it turns out involves a little more than is covered in the oven service manual: low-level hardware attacks in the form of side-channel power analysis and fault injection, building tools to work with the TMP91 microcontroller bootloader, and finally reverse engineering and patching the firmware in the oven. The result saved Colin’s oven from becoming e-waste, and can help others repair a variety of older electronics using these (obsolete but still widely deployed) TMP91 (TLCS-900/L1) microcontrollers.
Specific to the oven in question, a demonstration of patching the firmware to add a temperature logger, along with fixing two of the common complaints is demonstrated: the oven is made to always display the true temperature, and the oven control logic is patched to recover from heat loss more quickly. This demonstrates that many of the issues with these ovens may be related to firmware and not a physical fault. A souffle is finally cooked to validate the firmware patch (the souffle is not cooked live, unfortunately).
Apple’s Predicament: NSPredicate Exploits on iOS and macOS
Austin Emmitt | Vulnerability Researcher, Trellix Advanced Research Center
Date: Thursday, August 10 | 11:20am-12:00pm ( Oceanside C, Level 2 )
Format: 40-Minute Briefings
Tracks: Exploit Development, Application Security: Offense
In 2021 the FORCEDENTRY sandbox escape introduced the usage of NSPredicate in an iOS exploit. This new technique allowed attackers to sidestep codesigning, ASLR, and all other mitigations to execute arbitrary code on Apple devices. As a result, Apple put in place new restrictions to make NSPredicate less powerful and less useful for exploits. This presentation will cover new research showing that these added restrictions could be completely circumvented in iOS 16, and how NSPredicates could be exploited to gain code execution in many privileged iOS processes. This technical deep dive will be a rare instance of iOS security that anyone can comprehend without years of experience.
After an overview of the classes involved, we will explore the full syntax of NSPredicate and cover how it can be used to script the Objective-C runtime and even call any C function. It will be shown that PAC can still be bypassed 100% reliably with NSPredicates in order to execute any function with arbitrary arguments. A new tool will be unveiled to help iOS developers understand how dangerous NSPredicates can be created and therefore enforce the need for thorough testing of their usage. Additionally, a demonstration will be given which executes arbitrary code in the highly privileged Preferences app.
Finally, the talk will cover a bypass of NSPredicateVisitor implementations which allows a malicious process to evaluate any NSPredicate within several system processes including coreduetd, appstored, OSLogService, and SpringBoard. Next, there will be a live demo of exploiting SpringBoard to steal a user’s notifications and location data. The presentation will end with some discussion about what can still be done with NSPredicates now that these issues have been fixed, including bypassing App Store Review, and what app developers should know to keep their own apps safe.
First Party Problems in a Zero Trust World: The Accidental Discovery of a New Vulnerability in Google’s OAuth Implementation
Brian Smith-Sweeney | Vice President, Head of Security Risk Management, Two Sigma
Date: Thursday, August 10 | 11:20am-12:00pm ( South Pacific F, Level 0 )
Format: 40-Minute Briefings
Tracks: Enterprise Security, Cloud Security
Beware, dear friends, the cautionary tale of the cloud provider that broke its own security model. Ignoring RFCs! Putting plaintext passwords in scripts — and printing them in books! It’s a crazy story, but one that may nonetheless resonate with enterprise security practitioners everywhere.
In early 2021, I identified a client impersonation vulnerability in a series of Google “first-party” applications. This vulnerability allows an attacker to present themselves both to a user and to Google as one of these applications, and enjoy all the privileges therein. These privileges include subverting Google’s app verification process to access sensitive scopes, bypassing enterprise app controls, leveraging Google’s infrastructure to execute OAuth phishing attacks, and obfuscating attacker activities to maintain account access. For all intents and purposes, the attacker’s application becomes a Google application.
While the vulnerability itself is interesting, the story of how it came to be is even more so. I will take you on a 40-minute walk through a year’s worth of work — from identifying inexplicable behavior, to trawling RFCs and SDKs, to standing up a functional demo — to tell that story. You will see how decisions made across disparate teams, in different decades, can end up breaking core tenets of a security model.
This will be the first public disclosure of this vulnerability.
How NOT to Train Your Hack Bot: Dos and Don’ts of Building Offensive GPTs
Ariel Herbert-Voss | CEO and Founder, RunSybil
Shane Caldwell | Lead Research Engineer, RunSybil
Date: Thursday, August 10 | 11:20am-12:00pm ( Islander HI, Level 0 )
Format: 40-Minute Briefings
Tracks: AI, ML, & Data Science, Application Security: Offense
No doubt everybody is curious if you can use large language models (LLMs) for offensive security operations.
In this talk, we will demonstrate how you can and can’t use LLMs like GPT4 to find security vulnerabilities in applications, and discuss in detail the promise and limitations of using LLMs this way.
We will go deep on how LLMs work and share state-of-the-art techniques for using them in offensive contexts.
Three New Attacks Against JSON Web Tokens
Tom Tervoort | Principal Security Specialist, Secura
Date: Thursday, August 10 | 11:20am-12:00pm ( South Seas AB, Level 3 )
Format: 40-Minute Briefings
Tracks: Cryptography, Application Security: Offense
JSON Web Tokens (JWTs) have become omnipresent tools for web authentication, session management and identity federation. However, some have criticized JWT and associated Javascript Object Signing and Encryption (JOSE) standards for cryptographic design flaws and dangerous levels of unnecessary complexity. These have arguably led to severe vulnerabilities such as the well-known “alg”:”none” attack.
When examining JOSE standards myself I also noticed a few potential “foot guns” that might result in JWT library implementers introducing vulnerabilities if they were to interpret the RFC in certain ways. This prompted me to investigate various JWT libraries for vulnerabilities. As a result, I managed to identify three new classes of JWT attacks affecting at least five different implementations. Two of these attacks (“sign/encrypt confusion” and “polyglot token”) can allow complete token forgery, allowing authentication bypasses or privilege escalation in applications using an affected library and configuration. The third (“billion hashes”) attack can be leveraged for a denial-of-service attack against token-processing servers.
In this talk, I will outline these new vulnerability classes and show how to attack applications using a vulnerable JWT library. While each type of vulnerability could be considered to be just an implementation bug, I argue that they are also the result of understandable RFC interpretations and that these problems are indicative of broader issues with the JOSE standards.
Evasive Maneuvers: Trends in Phishing Evasion & Anti-Evasion
Din Serussi | Incident Response Group Manager, Perception Point
Date: Thursday, August 10 | 1:30pm-2:10pm ( Islander HI, Level 0 )
Format: 40-Minute Briefings
Tracks: Enterprise Security, Data Forensics & Incident Response
Phishing is still one of the most concerning widespread cyber threats that organizations face today. In spite of the ongoing global investment in anti-phishing solutions, attacks still manage to bypass security systems and have a huge impact on individuals, SMBs and large enterprises alike. Furthermore, phishing is no longer limited to email, but is now being delivered via a variety of additional channels, including instant messaging and all kinds of SaaS apps, which are continuing to be widely adopted amidst the rise of hybrid work.
This presentation will unveil some of the latest creative tactics and evasion techniques used by threat actors to set up phishing websites that fly under the radar of most conventional anti-phishing security solutions. We will present concrete examples that our incident response team has caught in the wild and try to generalize them into practical tips and lessons that can help security practitioners.
Some examples include novel abuse of Microsoft, Google, and modern SaaS services to masquerade phishing content, new Javascript obfuscation and encryption techniques, requiring users to prove their identity before delivery, etc.
We’ll show how these methods easily bypass well-known defenses applied by enterprises to protect against phishing. We’ll also cover new anti-evasion methodologies and approaches that put security in the browser and are able to detect cutting-edge phishing campaigns.
By providing a comprehensive overview of modern evasion and anti-evasion tactics, attendees will gain a deeper understanding of how phishing attacks are evolving and how to stay ahead of attackers, which is especially relevant for security professionals, penetration testers, and anyone else responsible for detecting and preventing phishing attacks.
Houston, We Have a Problem: Analyzing the Security of Low Earth Orbit Satellites
Johannes Willbold | Doctoral Student, Ruhr University Bochum
Date: Thursday, August 10 | 1:30pm-2:10pm ( South Seas AB, Level 3 )
Format: 40-Minute Briefings
Tracks: Cyber-Physical Systems & IoT, Hardware / Embedded
Satellites have become a fundamental part of modern society, providing crucial services such as communication, global navigation, earth observation and weather monitoring. The number of satellites, especially in the Low Earth Orbit (LEO), has recently seen a dramatic increase in the wake of the “New Space” era. With their number continuously increasing, there is a growing need to ensure their security. Despite this, little to no research has been done on the security of LEO satellites.
This talk will present the first public security analysis and exploitation of real-world satellites, specifically focusing on LEO satellites. We will walk you through several satellite designs and point out their security-relevant highlights. Next, we will discuss different vulnerabilities found in each of the satellites, how they can be exploited in general, and how satellite-specific design decisions lead to specific vulnerabilities. To showcase the real-world exploitability, we will present an emulation of an active ESA satellite developed by us from scratch to serve as a test field for our exploitation. We will then utilize the emulation to demonstrate the exploitation of the satellite live and show how to obtain full, persistent control of the satellite.
After focusing on individual satellites and showing their vulnerabilities, we will discuss the larger picture: We surveyed 19 professional satellite developers to understand how widespread these issues are in the satellite ecosystem. Evidently, security by obscurity is still the dominating security concept, even to the point that many satellites are missing basic command-and-control traffic protection, allowing *anyone* with a strong enough radio to control the satellites.
We will conclude our talk with the lessons learned during this talk and our line of research. Specifically, we will reiterate the relevance of satellite-specific security solutions, the prevalence of security by obscurity, and the need for collaboration between space engineering and security communities.
npm and Sigstore: Provenance Comes to the World’s Largest OSS Ecosystem
Trevor Rosen | Staff Engineering Manager, GitHub
Zach Steindler | Principal Security Engineer, GitHub
Date: Thursday, August 10 | 1:30pm-2:10pm ( South Pacific F, Level 0 )
Format: 40-Minute Briefings
Tracks: Defense, Application Security: Defense
At GitHub, we’ve been hard at work over the last year on a project to secure the Javascript ecosystem by building provenance directly into first-party tooling and partnering with Sigstore to make software signing easy and ubiquitous.
GitHub-owned npm is the de facto standard package system for Javascript, which is the world’s largest language ecosystem by lines of code. Serving over 70 billion requests per month and accepting around 40k publish events in the average day, npm is popular enough that it’s seen more than its fair share of malware attacks and supply chain trojans in the recent past.
Mitigating these attacks not only means making technology available to OSS maintainers, but it also means a cultural shift away from the implicit tradition of unwary trust in components and toward a world where we can prove that every ingredient going into our software masterpieces deserves to be there. We will take you inside the effort to make this vision a reality and tackle some of the controversial questions that have come up along the way, making the case that this approach deserves to be copied throughout the world of open source.
One Drive, Double Agent: Clouded OneDrive Turns Sides
Or Yair | Security Researcher, SafeBreach
Date: Thursday, August 10 | 1:30pm-2:10pm ( Mandalay Bay H, Level 2 )
Format: 40-Minute Briefings
Tracks: Malware, Cloud Security
Over the last 10 years, ransomware attacks have become the main cybersecurity risk. More than 200 different ransomware families have been used in the wild. Most of them are fairly similar. EDRs can prevent most of them generically with decoy file traps, monitoring for processes that modify many files, or by monitoring common pre-encryption actions such as shadow copy deletion.
But what if we tell you there’s a way to encrypt all of your sensitive data without encrypting a single file on your endpoints? What if adversaries can encrypt files, while they are not even executing code on endpoints? What if not a single malicious executable from the adversary needs to be present on endpoints while files are encrypted?
We proved that all of this is possible. For the last decade, a built-in double-agent named OneDrive has been on all of our computers. Microsoft’s shelter-from-ransomware can be operated as ransomware. This double-agent has managed to gain so much trust that it can encrypt all of your local files in almost any directory without any of the tested EDRs detecting or stopping it. Not even the ones that implement AI / ML approaches. Some EDRs even trust it to execute malicious code.
In this talk, we will present DoubleDrive, a fully undetectable cloud-based ransomware, different from all other public ransomwares seen so far. It uses OneDrive to encrypt local files outside of OneDrive’s directory. It bypasses decoy file detection, Microsoft’s Controlled Folder Access and OneDrive’s ransomware detection. While monitored by some EDRs, it can execute common malicious actions including shadow copy deletion. It successfully wipes OneDrive files’ 500 previous versions and empties OneDrive’s recycle bin, making file recovery impossible. It can run with any privileges, no encryption is done on the computer itself, and all by operating our double-agent OneDrive.
TSSHOCK: Breaking MPC Wallets and Digital Custodians for $BILLION$ Profit
Duy Hieu Nguyen | Lead Security Engineer, Verichains
Anh Khoa Nguyen | Security Engineer, Verichains
Huu Giap Nguyen | Head of Technology, Verichains
Thanh Nguyen | Co-Founder, VNSecurity & Verichains
Anh Quynh Nguyen | Doctor, Nanyang Technological University
Date: Thursday, August 10 | 1:30pm-2:10pm ( Islander FG, Level 0 )
Format: 40-Minute Briefings
Tracks: Cryptography, Application Security: Offense
Would you like to hear how an attacker can steal BILLIONS of dollars worth of cryptocurrency from MPC digital custodian vaults and wallets by exploiting our new 0-day attacks?
At the core of modern Multi-Party Computation (MPC) wallets and digital asset custody solutions of major blockchains is a cryptographic protocol named Threshold Signature Scheme (TSS). Today, many institutions, including banks, exchanges, and wallets, rely on TSS to enable a group of parties to authorize transactions by generating signatures without having to reveal their individual secret keys. Consequently, the security of TSS is of utmost importance to many digital asset financial ecosystems.
Most TSS implementations rely on Gennaro & Goldfeder’s papers, which use homomorphic encryption and zero-knowledge proofs to secure digital assets worth billions of USD. Unfortunately, despite having undergone multiple security audits, these implementations — including the de-facto open-source TSS frameworks in Golang and Rust — are still vulnerable to three new key extraction attacks that our team at Verichains has discovered, which we have named TSSHOCK.
TSSHOCK completely breaks the security of TSS, with proof of concept exploitation demonstrating a full private key extraction by a single malicious party in 1–2 signing ceremonies on various popular wallets, non-custodial key infrastructure, and cross-chain asset management protocols. The attack leaves no trace and appears innocent to the other parties. Attackers can exploit these flaws to steal billions of dollars worth of cryptocurrency from both individual users and institutions.
In this talk, we will share our new key extraction attacks and demonstrate TSSHOCK on a blockchain testnet so the audience can witness how the attacker could steal asset vaults in seconds.
Dive into Apple UserFS (Userspace Filesystem)
Zuozhi Fan | Security Researcher, Ant Group
Date: Thursday, August 10 | 2:30pm-3:00pm ( South Seas CD, Level 3 )
Format: 30-Minute Briefings
Tracks: Mobile, Platform Security
Typically, filesystem code is implemented in kernel, and any flaws in it may cause serious impacts. My previous talk proved that filesystem vulnerabilities (CVE-2020–27904, CVE-2019–8852) make it possible for attackers to gain root privileges on macOS.
The “Files” file manager app was introduced in iOS 11, allowing users to browse and manage files stored on USB flash drives on iOS. Maybe to mitigate the above-mentioned filesystem attack surface, Apple introduced a new mechanism, UserFS. UserFS (Userspace Filesystem), which has most of its code running in userspace, consists of a kernel extension and a few userspace daemons. When handling files on USB drives on iOS, UserFS serves as the actual filesystem backend, rather than the kernel. This subsystem ensures that even if filesystem bugs exist, the impact is limited to userspace, preventing more serious risks.
In this talk, I will provide a brief overview of the Apple UserFS architecture and its functioning. Then, I will compare the changes in filesystem security after the introduction of UserFS. We will see that although UserFS reduces the kernel attack surface, it introduces some new attack surfaces. Following that, I will detail some vulnerabilities I found while reverse-engineering and analyzing UserFS, including both kernel and userspace vulnerabilities. The findings show that although UserFS hardens the filesystem, there is still a chance to break iOS via UserFS.
I Was Tasked With Enrolling Millions of Developers in 2FA — Here’s What Happened
John Swanson | Director, Security Strategy, GitHub
Date: Thursday, August 10 | 3:20pm-4:00pm ( Islander HI, Level 0 )
Format: 40-Minute Briefings
Tracks: Human Factors, Enterprise Security
Well before the U.S. government published its cybersecurity strategy that asks Big Tech to take more responsibility for securing their systems, I was tasked with enrolling millions of developers in two-factor authentication (2FA) and enforcing it, without users getting locked out of their accounts or increasing the workload for our support teams.
GitHub is the home of open source software and open source developers, and as such, we want to embrace our role in making the software supply chain more secure. In order to reduce the chances of both open source and private software projects being compromised through social engineering or other methods of account takeover, broad use of 2FA remains the best option to harden our ecosystem’s defenses.
In this presentation, I’ll take you behind the scenes of the GitHub 2FA initiative, and what we’ve learned six months into this multi-year program.
I’ll take you through the key strategic considerations that needed to be addressed prior to rolling out the initiative, including our operating principles, the challenges of scaling the program, and the ways in which we address them.
Next, I’ll share my experience leading and empowering a cross-functional team to collaborate, plan, execute, and promote the initiative.
Finally, we’ll take a look at the progress we’ve made six months into the initiative, the impact on users and internal teams, and what we expect for the next six months.
You’ll come away from this talk with a better understanding of 2FA and what it takes to implement similar strategies in your own organization.
Seeing Through the Invisible: Radiation Spikes Detected in Chernobyl During the Russian Invasion Show Possible Evidence of Fabrication
Ruben Santamarta | Independent Security Researcher,
Date: Thursday, August 10 | 3:20pm-4:00pm ( Oceanside C, Level 2 )
Format: 40-Minute Briefings
Tracks: Data Forensics & Incident Response, Cyber-Physical Systems & IoT
Chernobyl, an iconic symbol in our social imaginary that represents everything that may go wrong with radioactivity, was taken by the Russian occupation forces, as part of a full-scale invasion of Ukraine. During the first 48 hours of this situation, it was officially reported that the Automatic Radiation Monitoring System (ASKRS) of the Chernobyl Exclusion Zone had detected abnormally high radiation values. The intense traffic of heavy military vehicles, which would be stirring up radioactive dust, was initially pointed out as the root cause for the reported radiation spikes.
This talk will comprehensively describe the research that has been performed around this incident. Among other things, I have reconstructed the events through OSINT, talked to nuclear experts and visited radiological laboratories to analyze equipment and software. Eventually, I gained access to the data transmitted during those days by the wireless radiation monitoring devices in Chernobyl, thus being able to demonstrate that the patterns identified in the radiation spikes detected during the 24th and 25th of February 2022 show the possibility that data may have been fabricated.
Evidence confirms that the radiation levels depicted by a very specific set of real-time radiation maps, which during those days were consulted by millions of people and also consumed as a single source of information by media outlets and official entities, did not correspond to the actual physical conditions of the Chernobyl Exclusion Zone.
This research elaborates the software-based data manipulation as a plausible explanation.
The Living Dead: Hacking Mobile Face Recognition SDKs with Non-Deepfake Attacks
Xianbo Wang | PhD Candidate, The Chinese University of Hong Kong
Kaixuan Luo | PhD Student, The Chinese University of Hong Kong
Wing Cheong Lau | Professor, The Chinese University of Hong Kong
Date: Thursday, August 10 | 3:20pm-4:00pm ( South Seas CD, Level 3 )
Format: 40-Minute Briefings
Tracks: Application Security: Offense, Mobile
Face recognition is increasingly popular in mobile apps, especially for critical tasks like opening a bank account. To prevent identity spoof using injected images, liveness detection is crucial. This is particularly important due to the widespread availability of stolen identity documents and selfies on the black market.
While many researchers have studied deepfake or presentation attacks that target machine learning models, few have addressed the protocol design or implementation issues in face recognition systems that can enable low-cost and easy-to-scale attacks. Starting from several real-world incidents of non-deepfake attacks, we will delve into the technical aspect of mobile face recognition spoofing. Our analysis of 18 mobile face recognition libraries, including those from industry leaders, reveals their security flaws that can result in liveness detection bypasses.
After scanning more than 18,000 apps, we discovered approximately 1,000 apps that had face recognition libraries and a total of 100 million downloads. We conducted proof-of-concept identity forgery attacks against several popular apps. Without presenting in camera, we were able to complete identity verification by using only static photos of the “victim”. Finally, we will provide reference protocol for secure face recognition systems in mobile apps, along with security caveats for implementation.
With this talk, we hope to draw the community’s attention back on to the system security in the era of AI.
Kids in the Ad Fraud Crosshair: Why International Threat Actors are Targeting Children to Steal Money from Banks and Major Corporations
Zach Edwards | Senior Manager, Threat Insights, HUMAN Security
Date: Thursday, August 10 | 4:20pm-5:00pm ( South Seas AB, Level 3 )
Format: 40-Minute Briefings
Track: Human Factors
Cyber threat actors are scaling “Malicious Marketing as a Service” organizations with affiliates who hijack legitimate .gov, .edu and .org infrastructure in order to host scams that are crafted to show up on the first page of search results for specific phrases.
These threat actors are explicitly targeting children and gamers, likely due to some lack of sophistication in that audience or a general “lack of criminal reporting” that occurs when a child is tricked into downloading malware or committing financial fraud.
To make matters worse, this group is scaling up through affiliate software which claims publicly to have paid out more than $40 million to partners. This same software is now not only being used to target gamers, but someone is paying this network to prop up honeypots for people searching for recent anti-China / anti-CCP news articles.
It’s crucial for defenders and the public to understand not only the technical nuance of new exploits, but the psychological tactics used to get malware deployed at scale. For some threat groups, scale is acquired through sophistication and speed. For other threat groups, scale is acquired through persistence and psychological tricks that rely on people misunderstanding risks. This presentation will help folks understand a network that relies on both persistent psychological tricks as well as cutting edge malware and carefully crafted malicious data supply chains.
The Yandex Leak: How a Russian Search Giant Uses Consumer Data
ALSO AT THE DIANA INITIATIVE & BSIDES LAS VEGAS
Kaileigh McCrea | Privacy Engineer, Confiant
Date: Thursday, August 10 | 4:20pm-5:00pm ( Islander HI, Level 0 )
Format: 40-Minute Briefings
Track: Privacy
In late January 2023, almost 45 GB of source code from the Russian search giant Yandex was leaked on BreachForums by a former Yandex employee. While the leak itself did not contain user data, it reportedly contained the source code for all major Yandex services, including Metrika, which collects user analytics through a widely used SDK, and Crypta, Yandex’s behavioral analytics technology.
While there has been lots of speculation about what Yandex could do with the massive amounts of data it collects, this is the first time outsiders have been able to peek behind the curtain to confirm it, and what we’ve found is both fascinating and deeply unsettling.
Zero-Touch-Pwn: Abusing Zoom’s Zero Touch Provisioning for Remote Attacks on Desk Phones
Moritz Abrell | Senior IT Security Consultant, SySS GmbH
Date: Thursday, August 10 | 4:20pm-5:00pm ( South Pacific F, Level 0 )
Format: 40-Minute Briefings
Tracks: Reverse Engineering, Exploit Development
Cloud communication platforms like Zoom have become a fundamental aspect of modern communication and are widely used in daily work. However, in certain scenarios, traditional endpoints such as desk phones or analog gateways are still required.
Today, these devices can be integrated with most major cloud communication providers through the use of their provisioning services, which centralize configurations and firmware.
This session is about a security analysis of the Zoom “Zero Touch Provisioning” method in conjunction with certified hardware. It will reveal several vulnerabilities that, when combined, allow an attacker to remotely compromise arbitrary devices, such as massive eavesdropping on conversations or rooms, remote control of devices, or using them as a pivot point to attack the adjacent corporate network.
Be curious about the details of hard-coded cryptographic material, improper authentication, lack of immutable root of trust, exposure of sensitive information and unverified ownership.

