
Welcome to the DCG 201 Guides for Hacker Summer Camp 2023! This is part of a series where we are going to cover all the various hacker conventions and shenanigans both In-Person & Digital! This year in 2023 somehow bigger than it was in 2022 and thus we will have a total of 15 guides spanning 3 Months of Hacker Insanity!
As more blog posts are uploaded, you will be able to jump through the guide via these links:
HACKER SUMMER CAMP 2023 — Part One: Surviving Las Vegas & Virtually Anywhere
HACKER SUMMER CAMP 2023 — Part Two: Capture The Flags & Hackathons
HACKER SUMMER CAMP 2023 — Part Three: SummerC0n
HACKER SUMMER CAMP 2023 — Part Four: Zero Gravity by RingZero
HACKER SUMMER CAMP 2023 — Part Five: The Diana Initiative
HACKER SUMMER CAMP 2023 — Part Six: BSides Las Vegas
HACKER SUMMER CAMP 2023 — Part Seven: Black Hat USA
HACKER SUMMER CAMP 2023 — Part Eight: SquadCon by Black Girls Hack
HACKER SUMMER CAMP 2023 — Part Nine: DEFCON 31
HACKER SUMMER CAMP 2023 — Part Ten: USENIX + SOUPS
HACKER SUMMER CAMP 2023 — Part Eleven: Chaos Computer Camp
HACKER SUMMER CAMP 2023 — Part Twelve: Wikimania 2023
HACKER SUMMER CAMP 2023 — Part Thirteen: HackCon XI
HACKER SUMMER CAMP 2023 — Part Fourteen: Blue Team Con
HACKER SUMMER CAMP 2023 — Part Fifteen: Hack Red Con
HACKER SUMMER CAMP 2023 — Part Sixteen: SIGS, EVENTS & PARTIES

Blue Team Con 2023
Date & Time: Friday, August 25th (6:00PM) — Sunday, August 27th (4:30 PM)
Location: Fairmount Chichago (200 N Columbus Dr, Chicago, IL 60601)
Website: https://blueteamcon.com/
Tickets: https://blueteamcon.eventbrite.com/
Virtual Platform(s): NONE (In-Person Only)
Schedule: https://blueteamcon.com/2023/schedule/
Live Streams:
N/A
Virtual Chat: N/A
Affordability: Blue Team Village is In-Person only with $200 tickets for normal hackers. There is a $60 discount option for Students but MUST USE .EDU ADDRESS OR WILL BE REFUNDED. Children under 18 can get in for FREE with an acompyoning adult and there is a $5 charges for the Child Care area and Hak4Kidz area. (DETAILS BELOW)
Code Of Conduct: https://blueteamcon.com/about/code-of-conduct/

While traveling around the country to various conferences, through a mix of observation, participation, and attendance of many talks it became quite clear a gap within the information security industry currently exists. When it comes to these industry standard conferences and gatherings, the information sharing network for red team and offense research and activities was very mature while those for blue team and defense are lacking.
There are a multitude of industry standard offerings ranging from small regional meetups to the much larger well-known conferences held at summer camp in Las Vegas. These information-sharing networks benefit all teams encompassed within information security but are limited in how much they can benefit defenders of the enterprise. This realization made evident a strong need for a conference specific to blue teams and defense to kickstart the maturation process of information-sharing on this side of the house. Enter Blue Team Con.
The goal of Blue Team Con is to have talks that are almost exclusively focused on sharing information amongst defenders and protectors of organizations. This can span from SOC Analysts through CISOs and across the aisle to auditors and compliance personnel and application developers focusing on security. There are many professionals hard at work struggling to keep up with the vast amount of information in the cybersecurity space. Our goal is to help organize that information in a fun and collaborative way while offering a platform for those that have figured it out to share their knowledge.
The conference audience will include students, professionals, executives, and sales personnel from all over the United States and potentially beyond. We limit the amount of each of these categories of attendees to ensure this conference contains actual information security practitioners that need to benefit from the knowledge-transfer contained within.
We look forward to seeing you at Blue Team Con!
Blue Team Con is an annual cybersecurity conference for individuals interested in cyber security defense. A SIG (Special Interest Groups) focused convention that is reminiscences of single topic gatherings such as Fuzzcon (canceled this year) and PasswordCon (before it was absorbed into BSidesLV), if you love the Blue Team Village at DEF CON 31 you will love this one! We also wanted to highlight this convention as we feel that defense is something that is overlooked in modern digital security which is creating an entire generation of glass canons.
I’M IN CHICAGO AND IT’S NOT THOTCON, HALP!

https://www.transitchicago.com/assets/1/6/ctamap_System_textdesc.txt

Blue Team ReCon
Address: 200 N Columbus Dr, Chicago, IL 60601
Website: https://www.fairmont.com/chicago/
Room Block: https://btcon.link/roomblock
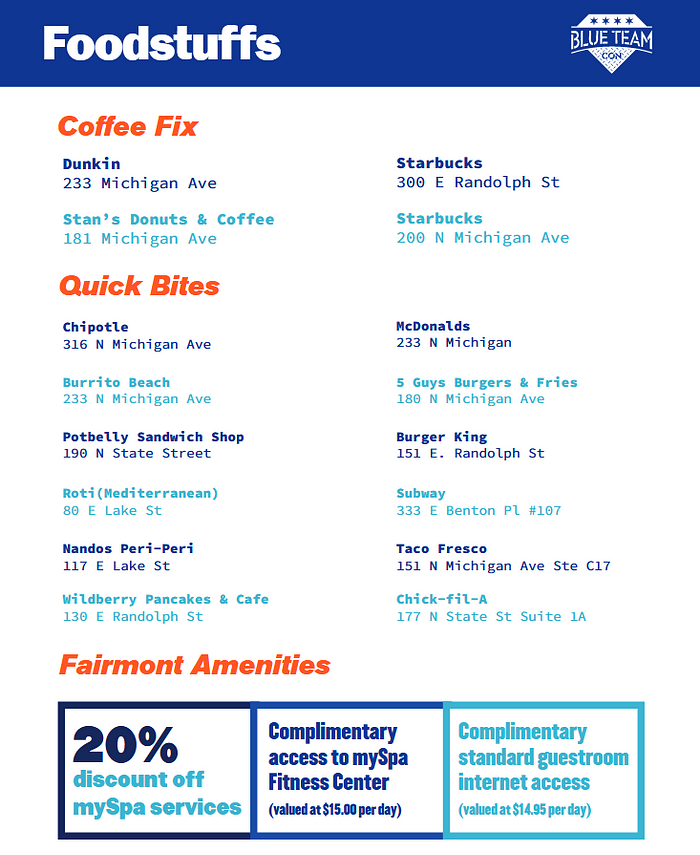
Transit: This venue is most accessible through train lines, both the Metra and CTA. Parking has a per day cost of over $60 a day. It is recommended to utilize the SpotHero mobile app for better parking rates in the area.

Last Minute CTF

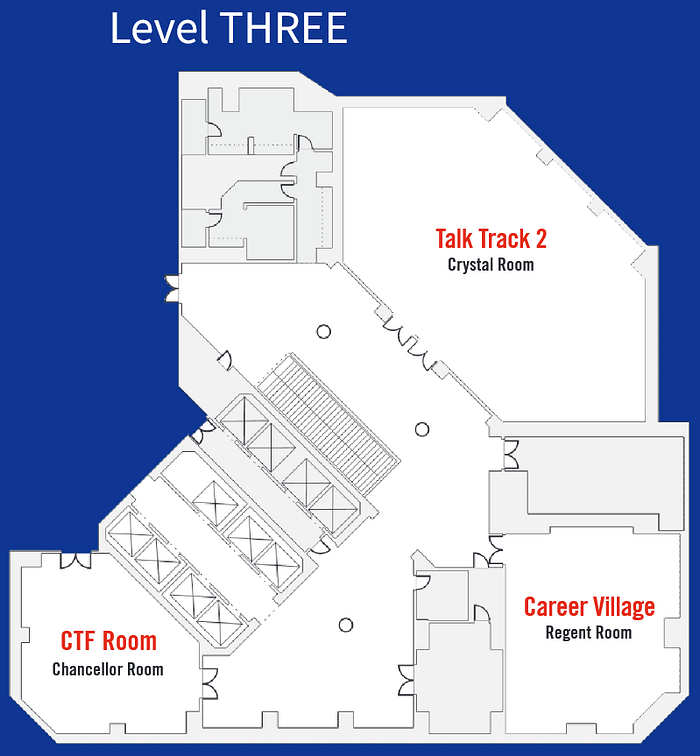
The Last Minute Capture the Flag [CTF] event is back for another year during Blue Team Con. This is a beginner-friendly CTF competition. Originally, this was a very last minute thing. This time, not quite so late, and with much better planning, but “Not Last Minute CTF” isn’t as fun. However, we continue to provide a fun game via a unique learning experience. As this is being run at Blue Team Con, all of the puzzles and challenges will be related as best we can to defensive cybersecurity topics. Remember, we want you to learn, we just might not make everything too easy…
However, a big difference that we can impart on this competition compared to other competitions, is that the Last Minute CTF wants to see you document your work and provide write-ups for each of the challenges. Half of the available points will come directly from these write-ups. While documentation is not something for everyone, it is a highly desirable skill to have and use in any day-to-day operation and who knows, we may even feature your write-up and tell everyone how awesome you did the thing!
Whether you have never played a CTF before, or have been completing challenges for years, we want you to play.

More information, as well as competition updates, will be provided directly via this page and Discord. And no, this is not a flag.
To compete in the CTF, find the link here on August 25th.
CTF winners will be announced at the closing ceremonies!
CTF Win Categories
We will have numerous categories that one can win in our Last Minute CTF. Some examples are:
- 1st Place
- 2nd Place
- 3rd Place
- Kickstarter (First Score)
- Down to the Wire (Last Score)
- Best Write-Up
CTF Prizes
Coveted Blue Badge (Offers free admission to Blue Team Con indefinitely), CompTIA Certification Vouchers (Provided by CompTIA Sponsorship), Books, and more to be announced!
CTF Hours
The competition homepage will go live for player signups (and to allow people early access to complete the introduction) when registration opens on Friday, August 25th, at 6:00pm CDT.
The rest of the challenges and the competition will begin Saturday, August 26th, at 10:30am CDT until Sunday, August 27th, at 1:00pm CDT.
Help and Assistance
- Join the Blue Team Con Discord and then the #ctf channel
- Stop by the CTF Room during Admin Availability Hours* for Assistance
- Saturday, August 27th: 10:30am to 5:00pm
- Sunday, August 28th: 10:00am to 1:00pm
- These hours are subject to change.
CONTESTS



BLUE TEAM CON VILLAGES
Villages are individual rooms throughout the conference that provide unique experiences. The villages will run through the entire conference, and most are free to walk in and out of as you like. Ones that are restricted will be listed as such.
Career Village
Saturday TBD Hours.
Sunday TBD Hours.
A Career Village that involves hiring managers and business professionals.
Are you starting a new career in cybersecurity? Or maybe you’re looking for a change in scenery or direction? This village is your opportunity to schedule one-on-one insider advice and tips from real recruiters and hiring managers. Seek guidance about what could be your (next) career in cybersecurity. Learn how to effectively highlight your knowledge, experiences, and abilities on your resume. Learn how to prepare for interview settings that employers are utilizing today. Practice your interview skills and get direct feedback so you can feel more confident in your job search.
The signup sheet will be announced at a later date.

Hands-On Village
Saturday from 10:30am to 6:00pm CDT.
Sunday from 10:00am to 3:00pm CDT..
The Hands-On Village is a location where labs and interactive activities will take place. The goal of this village is to allow attendees to get hands-on experience with numerous technologies, processes, or useful activities.
Vulcan Cyber
Gain hands-on experience prioritizing vulnerability risk by interacting with Vulcan Cyber researchers from the Voyager18 team. Learn best practices for contextualizing and mitigating vulnerability risk. Get hands-on to community tools developed by Vulcan Cyber, including VulnRX, the largest, curated library of vulnerability risk and threat intelligence, and MITRE Mapper, a service that maps prioritized CVEs to relevant remediation tactics and techniques from MITRE ATT&CK.
Trimarc
Trimarc is hosting Identity Security Village. This hands-on experience for all attendees consists of 2 domains with various common misconfigurations. Conference attendees have the opportunity to learn how to defend their networks by emulating an attacker: attempting to hack their way into a Domain Controller as either a Malicious Insider (using compromised window creds on a window 10 machine), or as a red teamer/penetration tester with a Kali machine on the same network. There are several layers of complexity in this environment extending its attack surface in ways that are very common and realistic including, certificate services, VMware environments, Azure Active Directory Sync, etc.
Escape Room
An Escape Room with a twist. Come see to find out!
Book-Swap
This year, we’re introducing the First Annual Blue Team Con Book Swap-O-Rama!
Here’s how it works:
- We’ll be accepting books published within the past 7 years as long as they’re still relevant to the security industry.
- We’ll also accept security-adjacent books, coding books, and textbooks as long as they’re applicable to modern cloud environments. (We know you love your Perl and COBOL books, so we encourage you to hang on to those!)
- Drop off a book or two to swap or donate at the Book Swap table in the Hands-On-Village on Saturday between 10am and 2pm and receive a Blue Star ticket. Swing by the booth between 2pm on Saturday and noon on Sunday to “shop” for another book with your ticket.
- If you are not a student, we ask that you hold off your shopping excursion until after 3pm Saturday so that students will have first crack to swap their books, then the booth will open for all.
- After noon on Sunday, we will not take any new donations and all ‘shopping’ will be free — no ticket required.
We’re really excited about the opportunity to share some knowledge, swap some books, and save the environment a little bit, too. Any books not claimed or swapped by Sunday at before closing ceremonies will be distributed or donated by Blue Team Con.
We’re looking forward to seeing you in a few weeks, so check your bookshelves and toss a book in your backpack to swap!
Thanks to Bat recommending we bring this event to Blue Team Con!
Hak4Kidz Village
Hak4Kidz operates as a public charity registered with the IRS under 501(c)(3) regulations.
Ethical hackers, information security professionals, and educators will bring the benefits of white hat hacking to the children and young adults at the conference. Hak4Kidz plans to accomplish this mission by putting their collective expertise and passion on display for the attendees to interact with at their will. An open area of stations will enable the attendees to expand and enlighten their technical interests. For innovation to perpetuate, it’s imperative that today’s young users are exposed to the bigger picture of how we got here and to help realize their potential.
Activities for kids will include SpyMath, SnapCircuits, Heal’s Ask Me Anything, and more. If participating, please have kids bring a laptop with Wireshark installed and tested.

Unconference
Open during the entire time (even through the night) of the conference.
No talks are selected or scheduled before the start of the conference. Once the conference opens, you can sign up for a slot to present. If your amazing talk didn’t get selected by the Blue Team Con CFP committee, this is your chance to present on your topic in a creative way. If you didn’t submit but wished you would have — here you go! If you want to do a fish bowl about knitting — have at it! It’s an Unconference!

Wellness Village
Saturday from 10:30am to 6:00pm CDT.
Sunday from 10:00am to 3:00pm CDT.
The Wellness Village will be ran by Mental Health Hackers, a 501(c)(3) organization.
The Mental Health Hacker’s (MHH) mission is to educate tech professionals about the unique mental health risks faced by those in our field — and often by the people who we share our lives with — and provide guidance on reducing their effects and better manage the triggering causes. This will be done through numerous talks and speakers conducted within the village during the conference. There will also be fun activities, crafts, coloring, and more to help you reduce stress and take a mental break from the conference activities and attendees.
MHH also aims at providing support services to those who may be susceptible to related mental health issues such as anxiety, depression, social isolation, eating disorders, etc.
Please understand that MHH does not provide counseling or therapy services.
YOGA: Saturday & Sunday ~ 9:00am CDT
Mental Health Hackers Lightning Talks
Saturday from 12pm to 2pm CDT
Sign up on site!
Come share your thoughts in presentation or discussion group format. We’re looking for topics related to your experience in anything related to
mental health and wellness.

BLUE TEAM CON LOUNGE
The Lounge will be setup to promote networking, allow for speakers to continue questions and answers after their talks, and to provide a relaxing atmosphere for attendees. Comfortable furniture will be provided to ensure attendees can take a break from the remainder of the conference to plug in and recharge if needed.
BLUE TEAM CON TRAININGS
Training is on 25 August 2023 and each one is a full in-person 8-hour class.
Seats are limited, so grab a ticket as soon as possible! See the full list of all trainers here.
Training can be attended by anyone, even if you do not attend the 2-day General Conference.
NOTE: Training tickets (besides board training) do not include a Practitioner ticket for the general Blue Team Con 2-day conference.

PDA Cybersecurity Board Training
Robert Barr, Rochelle Campbell, Matt DeChant, Julie Liu, Troy Mattern, Alyssa Miller, Jeff Olejnik, David Olivencia, Anthony Petitte, Michael Phillips, Ralston Simmons, and Stel Valavanis.
Overview
The Private Director’s Association is proud to present the PDA Cybersecurity Board Training, designed in collaboration with Blue Team Con. This all-day training targets directors of company boards and also those who aspire to become one and prepares them for participation in the board of the future with greater understanding, support, and governance of cybersecurity practices in companies. While not a certification, the training will provide a certificate of completion and an opportunity to empower the participant with a firm grounding in cybersecurity at the board level, and a cohort of experts and peers with which to network. The instructors have been curated from leading organizations and range from enterprise CISOs to top consultants in the industry to seasoned board members who have helped define the board cybersecurity role.
Forthcoming SEC regulations will require that a qualified cybersecurity expert is present on public boards, similar to the qualified financial expert currently required. While this does not legally affect private boards, PDA considers the requirement to be good practice and, furthermore, recommends that all board members receive basic cybersecurity training. Leading organizations do not wait for regulation to lead them and neither should their boards!
The PDA Cybersecurity Board Training provides a full day of panels, workshops, and tabletop exercises. Coffee, lunch, and an evening networking dinner with instructors and PDA committee members are included. This training also includes a full pass for the 2-day Blue Team Con conference on August 26th-27th.
To register, please follow these steps:
- PDA members receive a $200 discount. If you are a member or would like to become one, please email admin@privatedirectorsassociation.org for the discount code.
- Click here to register.
- Click on “Get tickets”. If you received a promo code from PDA, enter it at the top of the window. The PDA Cybersecurity Board Training item (3rd down) will show the discounted price.
- Choose ticket quantity, click “Check out” and complete the transaction.
- You will receive email confirmation and further instructions.
Agenda
Breakfast Networking
Opening Remarks
The Board of the Future and Cybersecurity — Rochelle Campbell will lead a panel of Directors in a discussion of how boards have changed and must continue to change to adapt to the new normal. Panelists: Anthony Petitte, David Olivencia.
Cybersecurity Responsibilities for Today’s Board — Matt DeChant will lead a workshop to guide you through the Cybersecurity knowledge needed and expectations of you as a Director.
Why Compliance Matters to You — The compliance landscape includes government, insurance, vendor management and industry pressure. Julie Liu walks you through the alphabet soup and helps you understand where and when it applies to a given organization.
Lunch
A CISO Presents to the Board — Alyssa Miller runs you through a mock CISO presentation to you, as the board.
Reports, Attestations, and Oversight — Jeff Olejnik presents many example reports and attestations that you may be confronted with and runs you through how to read and respond to them and provide oversight to your CEO and CISO.
Incident Response at the Board Level — Matt DeChant runs you through a mock cybersecurity incident with a board’s-eye view of Public Relations, legal, insurance, planning, and oversight.
The CISO Perspective — Michael Phillips leads a panel of CISOs to give you a taste of their strategic thinking such as baking in security by design, enabling digital transformation with security, and overall keeping your organization safe. Panelists: Alyssa Miller, Ralston Simmons, and Troy Mattern.
Closing Remarks
Networking Dinner
Advanced Memory Forensics
Memory Forensics is a required skill for digital analysts these days; it is also a needed in order to keep up with advanced attackers. In addition to attackers avoiding disk, thousands of nodes and BYOD are increasing the complexity of investigations. Gone are the days when an analyst could examine one machine at a time- results must be quick and precise. Oftentimes if you are not proactive, you’ve already lost the war before you even knew it was raging.
This workshop demonstrates the importance of including Volatile memory in your investigations by covering several attack methodologies that we’ve seen in the field. It also includes an overview of the most widely used memory forensics tool, Volatility, by one of its developers.
Student Prerequisites:
- Laptop with the following minimum specifications:
- 2.0 GHz, multi-core CPU
- 4 GB of RAM
- 20 GB of disk space
- USB 2.0/3.0 ports
- Wireless Network Interface Card
- VMWare workstation, VMWare player, or VMWare Fusion must be installed. VMWare player can be downloaded and used for free for purposes of this course. A PDF reader is also required. If students wish to examine evidence from their own native laptop, they must have a decompression tool that can handle a wide variety of formats (tar, gzip, bzip, RAR, etc) installed. 7zip and Winrar meet this criteria and are free.
- A USB thumbdrive with evidence and tools will be provided.
Defending your Enterprise using Security Onion
This one-day class will equip students with the necessary skills to properly place network sensors and investigate malicious activity using network and host data in enterprise environments. Students will learn core analyst techniques needed to investigate alerts, determine the scope of an incident, and manage a case using the Security Onion 2 platform.
Student Prerequisites:
- Students should attend the free 2-hour Security Onion Essentials course before the first day of class using the following link: https://securityonionsolutions.com/training. One topic covered by the Essentials course is building a Security Onion VM.
- Students will need a laptop with a modern browser.
- Students will need to connect to the provided WiFi and access cloud resources in order to do the labs.
- Students do not need to build a Security Onion VM for this class. We will be using a pre-installed lab.
- Students should have a basic understanding of networks, TCP/IP, and standard protocols such as DNS, HTTP, etc.
- Some Linux knowledge/experience is recommended but not required.
Ransomware Attack Simulation and Investigation for Blue Teamers
As a cyber security defender and investigator, we mostly only get to see a backwards perspective on how attacks unfolded, typically from impact and ransomware execution we are trying to make our way back in time to understand the scope and initial infection vectors of a breach. This is why it can help tremendously to be familiar with the typical TTPs that often employed by ransomware threat actors. This workshop will provide hands-on training on performing a typical ransomware attack in a Windows lab environment, using PowerShell Empire. Participants will gain an understanding of the techniques and tactics used by ransomware attackers, from initial access and reconnaissance to privilege escalation, credential dumping, lateral movement, defense evasion, data exfiltration, and encryption. Individual online lab access will be provided via RDP to follow along with the instructor throughout the workshop. By the end of the workshop, attendees will have a better understanding of the ransomware attack lifecycle, the tactics used by ransomware attackers and how to detect, respond and ultimately prevent them.
Student Prerequisites:
- Students will need a laptop with a modern browser.
- Students will need to connect to the provided WiFi and access cloud resources in order to do the labs.
- This course is designed for beginner and intermediate level professionals in blue teaming roles and may also be valuable to seasoned professionals who have not had an opportunity to work with attack tools.
- The workshop assumes basic knowledge of Windows systems, fundamental knowledge of networking, and an understanding of how Command and Control infrastructure works.
- Students should also be familiar with the forensic process, basic forensic artifacts, and basic knowledge of using SIEMs for log analysis.

DCG 201 TALK & WORKSHOP HIGHLIGHTS FOR BLUE TEAM CON 2023 (CDT)
This is the section where we have comb through the entire list of talks on both days and list our highlights for the talks that stand out to us. Note that this does not invalidate any talks we didn’t list, in fact, we highly recommend you take a look at the full convention schedule beforehand and make up your own talk highlight lists. These are just the talks that for us had something stand out, either by being informative, unique or bizarre. (Sometimes, all three!)
Thursday, August 24th
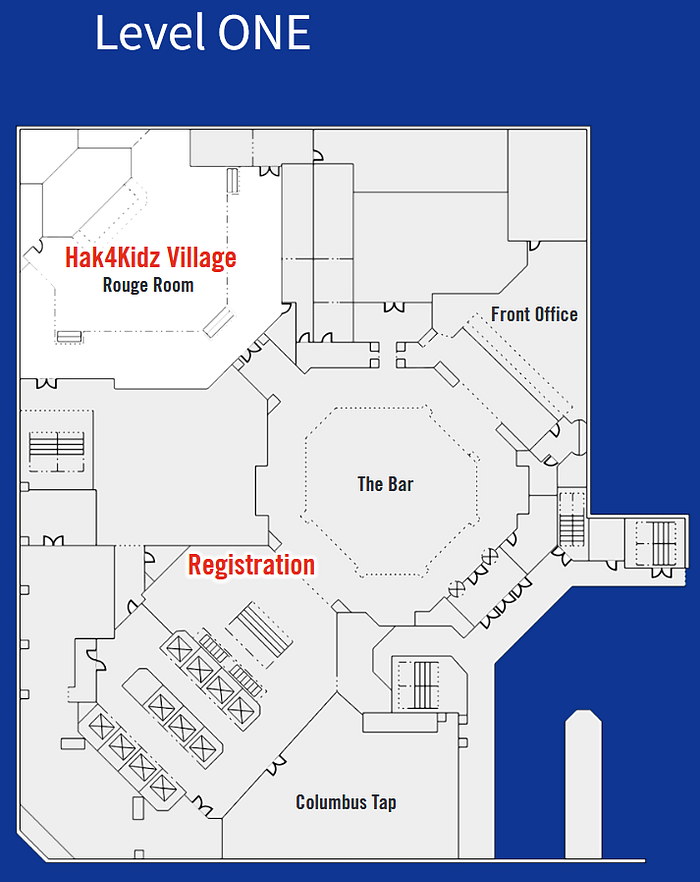
Registration: (Lobby) 6:00pm to 9:00pm
Friday, August 25th
Registration: (Lobby) 7:00am to 10:00am and 6:00pm to 9:00pm
Training Breakfast: 8:15am to 8:45am
Training: 8:45am to 5:00pm
Training Lunch: 12:00pm to 1:00pm
Saturday, August 26th
Registration: (Lobby) 7:00am to 5:00pm
Swag: 11:00am to 4:00pm
9:00am

We’re All Scared, Too: 10 Years of Lessons from Cybersecurity Mentorship
KENOTE
For the past decade, Lesley has been running career clinics for job seekers and changers in cybersecurity. For the past year, they have added on 1:1 mentorship office hours. Helping people choose career trajectories and overcome hurdles in employment has been a fascinating window into the fears, insecurities, concerns, problems, and victories of a wide range of people who work (or want to work) in cybersecurity. Many of their challenges are more universal than people are brave enough to admit, and everyone can learn from them to have a happier career.
Lesley Carhart is a Chicago-based Digital Forensics and Incident response professional specializing in investigations of industrial control system networks. They currently work for the industrial control cybersecurity company, Dragos, Inc — investigating intrusions into utilities, manufacturing, and transportation systems. Lesley speaks, teaches, and blogs about the topic around the world. In their free time, Lesley runs a virtual conference, as well as resume and career clinics for cybersecurity job-seekers, as well as teaching small kids to kick things. They are honored to have received awards like DEF CON Hacker of the Year and SANS Difference Maker Lifetime Achievement.
10:00am
An Enterprise on Fire: Successful Strategies in Triage
K “Turb0Yoda” Singh, Bluescreenofwin
0900 PST. You grab your cup of coffee and get into your chair. You begin the day with some small cheese factory in Wisconsin claiming that they’ve been hacked. As you log in, you behold default creds, no MFA, and a small Cisco firewall set to ALLOW ANY:ANY because hey, having a rule means passing compliance checks. In the corner of your eye, you suddenly start to see alerts appear. Mimikatz, Metasploit, some Cobalt Strike Beacons, LSASS dumps, the lot quickly piles on and on in your environment. No amount of caffeinated adrenaline will help as you watch your environment go up in flames.
Even the most seasoned veterans can be stricken by keyboard fright when facing the unknown state of a compromised system. Maybe your playbooks are woefully inadequate, out of date, or simply don’t exist. Perhaps you’ve assumed that your tooling will feed you information, but the right information may not always be available or easily consumable. It can be daunting when faced with the prospect of manual box-by-box triage.
If you’ve ever been in any of the aforementioned situations and have stared in incredulity at your terminal then this talk is for you.
We will examine the compromised environment from the 2023 WRCCDC security competition and discuss the foundation of the competition and the infrastructure from where all the data was pulled. Next, we will explore the strategies of the teams based on data from images taken at specific and timed intervals. Lastly, we will attempt to rank the strategies undertaken by the top eight collegiate cybersecurity teams in the competition and focus on what steps led to the most success in remediating the threat, which were not successful, and what kept threat actors out of systems the longest.
11:00am
Myths and Lies in InfoSec
In InfoSec, many closely held beliefs, commonly accepted best practices, and accepted “facts” are just wrong. These myths and lies spread quickly. Collectively, they can point security teams in the wrong direction. They can give rise to ineffective products. They often make their way into legitimate research, clouding results.
“Sixty percent of small businesses close within 6 months of being hacked.”
There’s a good chance you’ve seen this stat before. It has no basis in reality. The available evidence suggests quite the opposite.
“Attackers only need to get it right once, defenders have to get it right every single time.”
This idea has been repeated so often in InfoSec that it has become generally accepted as a true statement. It isn’t just wrong, it’s demotivating and encourages defeatist thinking that can sink the morale of a security team.
Most of the myths and lies in InfoSec take hold because they *seem* correct, or *sound* logical. Similar cognitive biases make it possible for even the most preposterous conspiracy theories to become commonly accepted in some groups.
This is a talk about the importance of critical thinking and checking sources in InfoSec. Our industry is relatively new and constantly changing. Too often, we operate more off faith and hope than fact or results. Exhausted and overworked defenders often don’t have the time to seek direct evidence for claims, question sources, or test theories for themselves.
This talk compiles some of the most interesting research I’ve done over the past decade. My goal is to convince you to treat vendor claims, commonly accepted industry statistics, and best practices with healthy skepticism. You don’t need to be a data scientist or OSINT expert to test theories and discover the truth — you just need to sacrifice a bit of your time now and then. I’ll show you how.
Vulnerability Prioritization: Addressing The Great Debate
In recent years, there has been a push in the Vulnerability Management space to focus on risk reduction, rather than pure remediation. Part of this push has been recognizing the need to prioritize which vulnerabilities should be remediated, and in what order. This has given rise to a great debate on how to best handle prioritization. At the core of the debate is how we calculate and address the risk that vulnerabilities present.
Here, we will dive into the debate, understand the underlying motivations, discuss different prioritization methods, identify the pitfalls that should be avoided, and identify effective reporting strategies throughout the organization.
12:00pm
PCI DSS v4.0 Is Here — Now What?
The Payment Card Industry Security Standards Council (PCI SSC) released v4.0 of the PCI Data Security Standard (DSS) in 2022 and the countdown is on. Organizations that need to comply with PCI DSS only have until April 2025 to implement all the new requirements. Are you ready and, more importantly, do you even know what it will take to be ready?
Many organizations need to comply with the PCI DSS and a major version change can be daunting. To make things worse, most of the information provided by the PCI SSC and other organizations can be vague and/or marketing focused. This leaves individuals confused as to what they really need to be doing to prepare themselves and their organizations. My goal is to break it down Barney-style so that no one gets stuck behind the eight ball when they run their first v4.0 assessment.
This presentation will:
-Provide brief definitions of the PCI SSC and PCI DSS
-Explain the history of the PCI DSS (how we got to where we are)
-Provide an overview of the changes in v4.0, specifically avoiding any vague marketing talk and focusing on actionable items to help prepare organizations for v4.0
-Provide a summary of the big-ticket items that organizations should be working on to ease into v4.0
2:00pm
Can’t Trust These Logs
Logs are usually the foundation of a blue teamer’s handbook, helping form the basis for audits and reconstructing events if an incident occurs.
But what if the information within your logs cannot be trusted, or their very existence is subverted, becoming an asset for an attacker instead of for your team? In this talk we will go over the approaches an attacker might take to bypass authentication, impersonate users, and use poorly secured logs to try and take over your application instead.
“Secure” GUIs with a poor API implementation, insecure cookie configurations, non authenticated endpoints with juicy data. These case studies will be briefly touched on, and inform how logs that just cannot be trusted (without further analysis) can come to be.
3:00pm
Defending Beyond Defense
Assumptions burn defenders every day. Perhaps the most pernicious one is that systems and their controls will always work as designed. Best practices in security may be good guidelines, but unfortunately also suffer from these same blind spots. For example, best practice recommends the use of LAPS for local administrator account passwords of domain-joined computers, yet misconfiguration of active directory can turn it from a protective control into a vulnerability. But what if there was a way to challenge these assumptions up front? The best way to dismantle these types of assumptions is to experience how deeply flawed they are. There is no better way to gain first hand experience into this perspective than immersion in the offensive security space. In this talk we’ll explore how to immerse yourself in the offensive security world to obtain this knowledge without needing to change careers or obtain additional certifications. By being more informed about offensive security, defenders are better able to recognize relevant intel, understand existing threats, and more readily discover attacker behavior. Join me as I discuss how there’s more to defending than just defense, and how you can find and engage with the amazing resources that are out there waiting to be explored.
3:30pm
You have a SIEM, Now What?
This talk will cover what to do once you have a SIEM approved by management. How do you configure it? How do you tune from it? During the talk we will touch on what is needed to deploy the SIEM, along with where the logs should come from. We will also touch on if there are compliance and regulatory requirements for retention. We will talk about how to ingest and tune the logs for your specific use case because there is no cookie cutter way to deploy a SIEM. We will touch on where the logs should come from what devices that you should obtain information from. We will also touch on what Open source tools that you can use and how they can integrate with cloud environments which organizations are moving. We will also touch on the topic of NIDS, HIDS and Threat Intel in the context of using them with a SIEM.
5:00pm
Transforming Vulnerability Management — How CSAF, VEX, SBOMs and SSVC Work Together
There is no such thing as a “vulnerability-free” product. As we get more insights into our supply chains, we can easily be overwhelmed by the number of potential vulnerabilities. All of our manual processes are failing. Instead of burning people out with boring tasks, we need to change the way we handle vulnerability management. The presentation will show the interconnection and relationship of different standards, like the Common Security Advisory Framework (CSAF), the Vulnerability Exploitability eXchange (VEX), the Known Exploited Vulnerability (KEV) catalog, Stakeholder Specific Vulnerability Categorization (SSVC) and Software Bill of Materials (SBOM). It will cover what needs to change to keep up with the vulnerabilities and threats discovered today. Taking the November 2022 blog post Transforming the Vulnerability Management Landscape by Eric Goldstein, CISA’s Executive Assistant Director for Cybersecurity, as a starting point, the presentation will shed light on how the US government believes the situation can be improved. It will also cover the actions necessary to support the ecosystem to transform its vulnerability management. That includes the support of tools, use of procurement regulation, education and much more.
Sunday, August 27th
10:00am
Keep the F in DFIR: The Importance of Digital Forensics in Incident Response
In recent years, blue teamers have greatly benefited from advanced security tools such as EDRs and XDRs. While these tools provide valuable visibility and containment mechanisms during DFIR investigations, over-reliance of these tools in DFIR investigations may lead to an incomplete picture of the incident. In this presentation, we will discuss how traditional forensic analysis methods can provide a more holistic look at an incident and reduce gaps in visibility.
Our presentation will provide an overview of challenges encountered when using EDR tools such as telemetry retention, OS compatibility, deployment scope and the lack of forensic artifacts that track interactive activity by an attacker. Next, we will introduce several forensic artifacts such as Amcache, Shellbags, Windows UAL etc. that provide deeper, historical visibility into attacker activity. Using forensic artifacts introduced in this presentation, blue teamers will be able to piece together and timeline crucial pieces of evidence on systems that provide insight into historical process executions, file/folder access, lateral movement, etc. Finally, we will introduce real-life case studies where forensic methods have proved vital in incident response investigations.
Attendees of this presentation will gain a better understanding of forensic artifacts and how they can be utilized in incident response investigations. They will also learn about free and open-source tools available to parse these artifacts at scale.
11:00am
Dude, Where’s My Domain Admins?
*Attacker pops a workstation on your domain*
*Attacker establishes her foothold and local persistence*
*Attacker begins recon of AD, starting with Domain Admins*
ERROR: The group name could not be found.
Attacker, with a disconcerted look on her face: “Dude, where’s my Domain Admins?”
Killchains that involve AD usually involve enumeration of highly-privileged accounts: members of Domain/Enterprise/Builtin Admins, Server Operators, etc. Those groups and their members can be enumerated in AD by default, exposing members as targets of exploitation to obtain those privileges. However, there’s a way to use in-the-box AD capabilities to thwart these attempts. Using List Object mode, implicit deny, and AdminSDHolder/SDProp, AD defenders can hide these principals from unprivileged users. In this talk, I’ll walk you through the principles, process, and pitfalls, so you can raise the bar on your AD defenses without blowing things up.
11:30am
Scraping new territory: Defending privacy in the new world
Data scraping is a unique threat, as adversaries apply offensive security techniques to obtain private user data at scale. Detecting and preventing scraping threats also entails a unique set of technical challenges, as it involves a variety of adversary profiles with limited incident signals for defenders. In recent years — in addition to the technical battle online — the battle against scrapers has transformed into a legal battle in the courts, with notable precedents impacting the overall scraping landscape.
In this talk, you will learn about the scraping threat landscape, and the lessons learned through defending and preventing scraping threats in the world’s largest social networks, Facebook and Instagram. We will cover attack scenarios, unique threat requirements, adversary profiles, and share our best practices for reducing scraping risks by adjusting common practices, such as Static Analysis and Red Teaming. In addition, we will provide context on the latest legal precedent in the scraping field, and how it can shape defense practices and user behavior. We will end with a call for action for security professionals, and how you can and should be more involved when setting industry standards for users’ privacy.
1:00pm
HOW TO MAKE AI COMPLY
Raul Rojas (AKA El Jefe De Security)
How are you adopting AI/ML into your enterprise? How hard can building an AI really be? What should you consider when introducing an AI model? Are you prepared for the consequences? How to do set guard rails so that your developers don’t break you into jail?
This talk is a Treatise on AI/ML challenges for governance and strategic guidance for securing AI/ML scenarios within an enterprise for product research and development. Developed from years of experience learning how to approach AI/ML projects in Microsoft Research, I will attempt to shed light on some of the current thinking and best practices for AI models for internal and public use.
You can expect to learn about the explosion of technologies becoming available to industry and the challenges facing platform builders and enterprises now that these features are present.
We’ll take a journey through the current regulatory landscape and share some considerations that Security governance programs should think about for their own AI/ML compliance.
Learn about how security fundamentals have not really changed but must be enhanced to deal with these new realities, including new perspectives on protecting the supply chain, approaching AI scenarios in threat modeling, building controls for resilience and the new demands of logging and auditing in real time for intentional behavior vs malicious behavior.
Then we wrap up with how to approach educating compliance organizations, your leaders, and your developers to be prepared to understand AI/ML risks and adopt AI with due diligence.
Smoke and Mirrors: Wasting a hacker’s time with misdirection & obscurity
In the world of DevSecOps, it’s not enough to simply secure your applications and systems against known vulnerabilities. As cybercriminals become more sophisticated, taking additional steps is important to make it more difficult and expensive for them to breach your defenses. Obfuscation techniques can be a powerful tool in this fight, costing hackers valuable time, resources, and money.
In this talk, we’ll explore some simple obfuscation techniques that can be used to make life harder for hackers. We’ll cover simple to advanced techniques like hiding the login page, redirecting hackers to honeypots, using fake data that triggers canaries, preventing email scraping, feeding fake emails to scanning tools, using dummy DNS entries, and using fake comments in code to mislead attackers about vulnerabilities that do not exist. We’ll also discuss strategies for obscuring code and purposely leaking API keys to create distractions and dead ends for attackers.
Whether you’re a developer, security professional, or DevOps practitioner, this introduction will provide valuable insights into how you can use obfuscation to make your applications more secure and resilient against cyber attacks. Join me and learn how to make life harder for hackers in DevSecOps!
2:00pm
Authentication Proxy Attacks: Detection, Response and Hunting
Over five years ago, Evilnginx was released, demonstrating the ease of stealing authentication session tokens from MFA-enabled logon processes with a simple reverse proxy. Despite being a well-known technique, few of these attacks were seen in widespread use among cybercrime threat actors, until recently.
The advent of the EvilProxy and similar platforms has now given attackers the ability to compromise targets with strong authentication without resorting to burdensome SIM swapping or noisy push fatigue attacks. With rapid adoption of phish-resistant MFA outside government-aligned sectors, organizations need to know how to detect and respond to these attacks.
In this talk, we will provide an in-depth look at the tactics, tools and procedures (TTPs) used by threat actors to effect account-takeover of MFA-enabled accounts. We’ll demonstrate how the ingenuity of this attack has a fatal flaw at its core, allowing us to hunt, detect, mitigate and block this type of attack.

CONTINUE TO: HACKER SUMMER CAMP 2023 — Part Fifteen: Hack Red Con
