
Welcome to the DCG 201 Guides for Hacker Summer Camp 2023! This is part of a series where we are going to cover all the various hacker conventions and shenanigans both In-Person & Digital! This year in 2023 somehow bigger than it was in 2022 and thus we will have a total of 15 guides spanning 3 Months of Hacker Insanity!
As more blog posts are uploaded, you will be able to jump through the guide via these links:
HACKER SUMMER CAMP 2023 — Part One: Surviving Las Vegas & Virtually Anywhere
HACKER SUMMER CAMP 2023 — Part Two: Capture The Flags & Hackathons
HACKER SUMMER CAMP 2023 — Part Three: SummerC0n
HACKER SUMMER CAMP 2023 — Part Four: Zero Gravity by RingZero
HACKER SUMMER CAMP 2023 — Part Five: The Diana Initiative
HACKER SUMMER CAMP 2023 — Part Six: BSides Las Vegas
HACKER SUMMER CAMP 2023 — Part Seven: Black Hat USA
HACKER SUMMER CAMP 2023 — Part Eight: SquadCon by Black Girls Hack
HACKER SUMMER CAMP 2023 — Part Nine: DEFCON 31
HACKER SUMMER CAMP 2023 — Part Ten: USENIX + SOUPS
HACKER SUMMER CAMP 2023 — Part Eleven: Chaos Computer Camp
HACKER SUMMER CAMP 2023 — Part Twelve: Wikimania 2023
HACKER SUMMER CAMP 2023 — Part Thirteen: HackCon XI
HACKER SUMMER CAMP 2023 — Part Fourteen: Blue Team Con
HACKER SUMMER CAMP 2023 — Part Fifteen: Hack Red Con
HACKER SUMMER CAMP 2023 — Part Sixteen: SIGS, EVENTS & PARTIES

DEF CON 31
Date: Thursday August 10th (12:30 PM EST) — Sunday, August 13th (8:00 PM EST)
Website: https://defcon.org/html/defcon-31/dc-31-index.html
Badge Firmware & Updates: TBA (Last Years: https://defcon.org/signal/index.html)
On-Site WiFi Registration: TBA (Last Years: https://wifireg.defcon.org/)
Locations:
Caesars Forum (3911 S Koval Ln, Las Vegas, NV 89109)
Flamingo (3555 S Las Vegas Blvd, Las Vegas, NV 89109)
Harrah’s Las Vegas (3475 S Las Vegas Blvd, Las Vegas, NV 89109)
The LINQ Hotel (3535 S Las Vegas Blvd, Las Vegas, NV 89109)
Platform(s): Discord via Twitch TV, YouTube using Restream.io in addition to DEF CON FORUMS
Android App: https://play.google.com/store/apps/details?id=com.shortstack.hackertracker&hl=en
iOS App: https://itunes.apple.com/us/app/hackertracker/id1021141595
Schedule: https://defcon.org/html/defcon-30/dc-30-schedule.html
Live Streams:
YouTube: https://www.youtube.com/user/BlackHatOfficialYT
Twitch: https://www.twitch.tv/defconorg
Chat:
Discord: http://discord.gg/defcon
Accessibility: The price to attend DEF CON in-person will be $440 USD. You may not attend in-person without purchasing a badge. Attending virtual on our Discord will be free.
Tickets (In Person): https://shop.defcon.org/products/def-con-31-pre-registration-ticket
Code Of Conduct: https://defcon.org/html/links/dc-code-of-conduct.html
Alternative Text Guide: https://defcon.outel.org/dcwp/dc31/
Reddit Guide: https://www.reddit.com/r/Defcon/comments/tx7tg2/mega_def_con_info_for_your_planning_enjoyment/
DEFCON was started in 1993 by Dark Tangent (Jeff Moss) as a going away party for a friend who never showed. It has since grown to one of the biggest hacker security conventions around the world with over 20,000 attendees yearly.
‘We are living through a revolt against the future. The future will prevail.’
This years DEF CON is about the future we want to bring into being, together. DEF CON’s hacker community has a powerful role to play in whatever comes next, From hardware to policy, from biohacking to satellites.
The skill set of hackers — reckless curiosity, the drive to know how systems work and a vision that sees beyond what a thing is and into what it could be after its pesky warranty is voided — is more important now than its ever been.
As you work on your various projects, keep in mind that the future is undefeated, and it belongs to the resourceful, the brave and most of all to those who can see around the corner of what is and what might be.
DEF CON 31 will be a hybrid event this year, though the majority will be attendee in-person. They’ll host both an in-person experience in Las Vegas and some activities and villages on the official Discord just as they did for DEF CON Safe Mode and DEFCON 31 H0M3COMING.
Either Virtual or In-Person, DEF CON 30 is still what DCG 201 classifies it as a “Mega Convention” aka a convention with smaller mid-sized conventions nested in it. You will be covering a wide area with a diverse mob of people with ten million activities going on all at once. It’s important to plan out your day, take your time and remember that it’s physically impossible to see and do everything in one con year never mind in one day. For those attending Virtually be thankful that unlike the previous this year you can see most of DEF CON 30 at mostly your leisure since most of the content will be pre-recorded and archived.
The convention this year is so massive we plan on listing all the important things to note, not exactly everything that is there. We highly suggest looking at their website and clicking around to give you a sense on what you would like to see.
DEFCON LOCATION RECON
Caesars Floor Plan
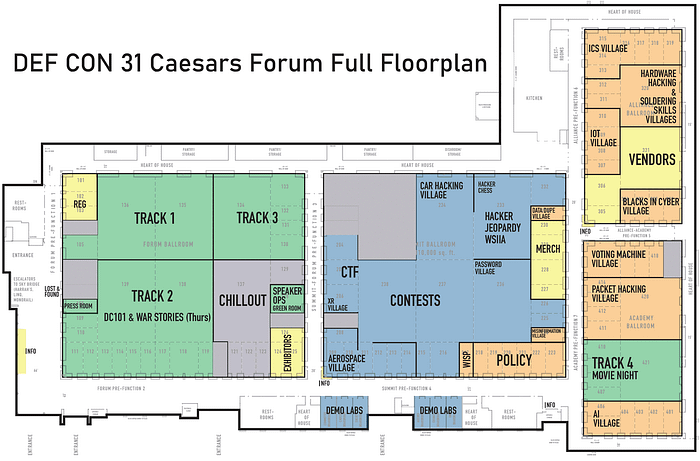
3D CAESARS WALK AROUND:
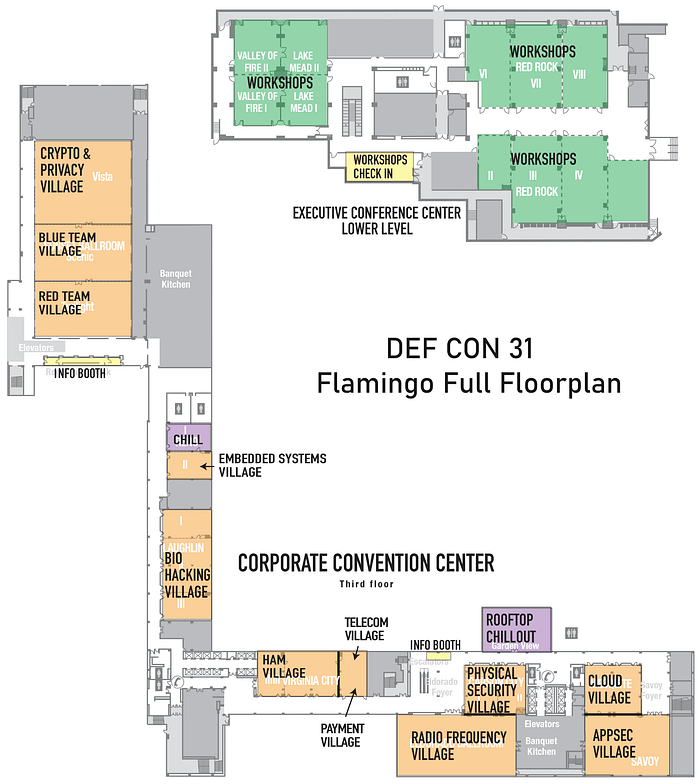
Flamingo Floor Plan
Harrah’s Floor Plan

LINQ Floor Plan

HACKERS WITH DISABILITIES GUIDE @ DEF CON 31

Thanks to @A_P_Delchi and Hackers with Disabilities for creating this helpful accessibility guide to DEF CON 30!
WELCOME TO DEFCON, HDA IS HERE TO HELP!
Hackers with disabilities (HDA) was assembled to provide resources, maps, guides and assistance to people attending DEFCON who need assistance due to disabilities. We acknowledge that not all disabilities are visible and that we are providing this information for all attendees & stand ready to assist anyone with ADA needs to the best of our ability and within the operational scope of DEFCON. If at any time you have questions or would like to suggest things that we should be doing please see the DEFCON forums page dedicated to HDA: https://forum.defcon.org/node/246536
While our goal is to make DEFCON more accessible to people with disabilities, we are limited in what we can do and provide this information and any assistance we can on a best effort basis.
Due to the complications involved in working with multiple hotels, federal, state, and local regulations, the requirements of operating a public gathering during a global pandemic we cannot promise nor provide accommodations for all people in all situations. Please understand that under no circumstances are we singling out, mocking, or intending to make anyone feel out of place. We want individuals with disabilities to be an active and contributing part of the DEFCON culture. If we must set a blanket rule or cannot provide specific items or services at scale, please understand the limitation is based on resources, legal implications, and restrictions put upon a large-scale social gathering and not from a place of discrimination.
Despite what our badges say at the end of the day we are all HUMAN. We strive to improve with your input and active involvement with the community to bring you the best conference that we can.
FULL GUIDE: https://forum.defcon.org/filedata/fetch?id=242955
PRINT FRIENDLY: https://forum.defcon.org/filedata/fetch?id=242954
PREPARE (VIRTUAL)
What you need to access DEF CON 30:
DISCORD Account
You will need a Discord account to participate in the social aspects of DEF CON 30. You can find detailed instructions on getting on the DEF CON Discord server here. There is a FAQ for Humans on Discord as well.
Join with the DEF CON Discord Server signup link: https://discord.gg/defcon
Twitch
You will need to get on the DEF CON Twitch for live streamed talk Q&A sessions, evening fireside talks and evening contests. Not to mention the live entertainment!
YouTube/DEF CON Media Server
The Talks for DEF CON will be released daily on the DEF CON YouTube channel so you might want to susbscribe! They will also be released in torrents on https://media.defcon.org
Accessing Talks
How to Access DEF CON 30Mode Talks and Q&A Sessions
DEF CON official presentations have been pre-recorded, and pre-released online individually and as a torrent on media.defcon.org and on our official YouTube channel.
The dates and times on the Speaker Page and Schedule Page are special live streamed Q&A sessions for each talk, as well as additional fireside lounges and panels. These sessions will be streamed on Twitch at https://www.twitch.tv/defconorg.
All discussions and attendee to speaker participation will be on the DEF CON Discord Server at: https://discord.com/channels/708208267699945503/733079621402099732
Main Tracks
DEF CON official presentations will be a mix of LIVE In-Person & pre-recorded. We will try to make note to the best of our ability which talks will be In-Person & Virtual.
Also watch the talks released later in the month on YouTube: https://www.youtube.com/user/DEFCONConference
Track 1 Talks Chat
https://discord.com/channels/708208267699945503/733079621402099732
Virtual Sessions will be streamed here
https://www.twitch.tv/defconorg
Speaker Q&A Live Chat — Ask a question
https://discord.com/channels/708208267699945503/733079691145117848
Fireside Lounge Panels
https://discord.com/channels/708208267699945503/733562098315034735
War Story Bunker & No Tech Talks
https://discord.com/channels/708208267699945503/733562098315034735
ALL TWITCH STREAMS
DCG TV (All Main Twitch Streams + Hotel CCTV Rebroadcast Channels):
Master Channel (All Channels In One):
DEF CON Streams Individual
DEF CON org Twitch Stream // Schedule
Hacker Jeopardy Twitch Stream
DEF CON Music Twitch Stream
DEF CON Youtube Streams
DEF CON Chill Twitch Stream
DEF CON Village Streams
Blue Team Village Twitch Stream // Youtube Stream
Red Team Village Twitch Stream // Youtube Stream
Aerospace Village Twitch Stream // Youtube Stream
BiohackingVillage Twitch Stream // Youtube Stream
Career Hacking Village Twitch Stream // Youtube Stream
Hack The Sea Twitch Stream // Youtube Stream
Car Hacking Village (Track1) Twitch Stream // Youtube Stream
Car Hacking Village (Track2) Twitch Stream // Youtube Stream
Car Hacking Village (CHV 101) Twitch Stream // Youtube Stream
CryptoVillage Twitch Stream // Youtube Stream
Ethics Village Twitch Stream // Youtube Stream
Wall of Sheep/Packet Hacking Village Twitch Steam // Youtube Stream
Recon Village Twitch Stream // Youtube Stream
Cloud Hacking Village Youtube Stream
Ham Radio Village Twitch Stream
ICS Village Twitch Stream
IoT Village Twitch Stream
ByPass Village Twitch Stream
Toool US/Lockpick Village Twitch Stream
Monero Village Twitch Stream
Payments Village Twitch Stream
Password Village Twitch Stream
AppSec Village Youtube Stream
cpxSatAmericas Twitch Stream
Voting Village Twitch Stream
Hardware Hacking Village Twitch Stream
Rogues Village Twitch Stream
AI Village Twitch Stream
- Adversary Village
- Aerospace Village: Videos are linked at their schedule
- AI Village
- Appsec Village: Videos are linked at their schedule
- B.I.C. (Blacks In Cybersecurity) Village
- Bio Hacking Village
- Blue Team Village
- Car Hacking Village
- Career Hacking
- Cloud Village
- Crypto & Privacy Village
- Hack the Sea Village
- Ham Radio Village
- ICS Village
- IoT Village
- Lock Bypass Village
- Packet Hacking Village
- Payment Village
- Recon Village
- Rogues Village
- Social Engineering Village
- Voting Village
Other Streams Related
Second Order Chaos Twitch Stream
Hacker Gameshow Twitch Stream
The Many Hats Club Twitch Stream
ZephrPhish Twitch Stream
(Thanks To AngusRed!)
DEFCON VILLAGES
The core and heart of the convention are the “Villages”. These are spaces inside of DEFCON that act as their own miniature convention, including talks, contests, badges and swag. Many of them focus around a particular special interest. Here is a master list of almost every village at the convention plus a special highlight of one talk or activity they will have there.
NEW VILLAGES IN 2023
EMBEDDED SYSTEMS VILLAGE
Friday: 9:00am–6:00pm
Saturday: 9:00am–6:00pm
Sunday: 9:00am–2:00pm
CTF ONLY in-person. Some labs will be made available virtually.
Where: Reno 2 Flamingo
Embedded systems exist at the intersection of hardware and software, built to accomplish a specific task. Often these disciplines are dealt with individually, but understanding the custom relationships between hardware and software is key to performing security research on these devices.
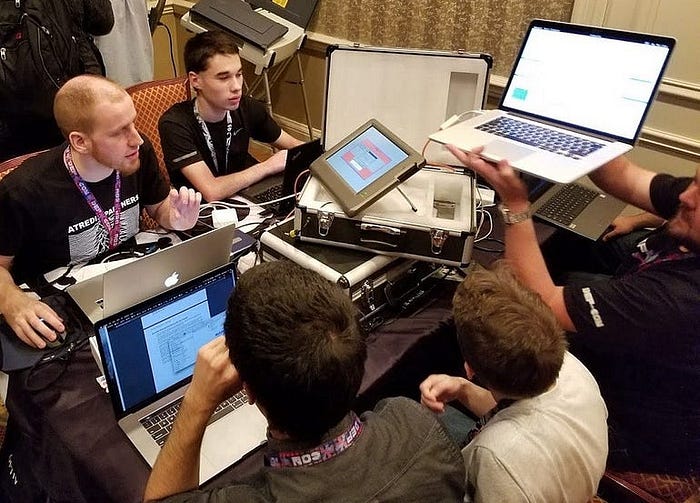
Embedded Systems Village advances the security of embedded systems by hosting hands-on hacking workshops, showcasing new security research demos, and organizing exciting hacking contests to educate attendees and manufacturers on the approach hackers use to attack these devices. Attendees will leave the village with an understanding of how to reduce complex, exotic devices to their underlying embedded components and to extract the information required to use the tools and techniques taught at other villages where embedded systems are on display.
What we will bring:
Labs: We have a lab platform that brings everyone from every skill level to the same playing field with step by step instructions that aim to teach individuals specific techniques and skills in a hands-on manner.
Interactive Hacking Content: We want to showcase the weird and cool in the embedded device world, and provide an opportunity for hackers to get hands-on experience hacking them.
Contests: We are working on a brand new CTF contest that will support everyone from the casual player (i.e. someone that only wants to drop in for a few minutes) all the way to the hardcore teams that are willing to spend their full DEF CON engaged in our challenges.
Expect unique devices, new challenge formats and full DEF CON worth of fun.
Expect unique devices, new challenge formats and that WOW factor that our CTFs have had in the past. Building on our lessons learned and experience over the years, we are confident that this track will not disappoint!
Twitter: https://twitter.com/EmbeddedVillage

PASSWORD VILLAGE
Friday: 10:00am–8:00pm
Saturday: 10:00am–8:00pm
Sunday: 10:00am–2:00pm
Where: Contest Area, Forums
The Password Village provides training, discussion, and hands-on
access to hardware and techniques utilized in modern password cracking,
with an emphasis on how password cracking relates to your job function
and the real world . No laptop? No problem! Feel free to use one of our
terminals to access a pre-configured GPGPU environment to run password
attacks against simulated real-world passwords. Village staff and
expert volunteers will be standing by to assist you with on-the-spot
training and introductions to Hashcat, as well as other FOSS cracking
applications. Already a password cracking aficionado? Feel free to
give a lightning talk, show off your skills, help a n00b learn the
basics, or engage in riveting conversation with other password crackers.
Website: https://passwordvillage.org
Twitter: @passwordvillage

TELECOM VILLAGE
Friday: 10:00am–8:00pm
Saturday: 10:00am–8:00pm
Sunday: 10:00am–1:00pm
Where: Virginia City, Flamingo
The Telecom Village’s primary focus would be around Telecom Security. We plan to host multiple hands on events as part of the village so as to give participants an overview security specific challenges in a Telcom Network. This includes: CTFs in telecom signaling security and another one in Private 5G and select set of talks (5), spread across two days.
We are planning a workshop over a day where we will be giving an overview of the 4G/5G network and its security. There will be a small CTF for SS7, Diameter attack on the 3G/4G network and 5G network. The workshop and CTF will focus on use of open-source tools so as to ensure that this Niche within the Security Industry is taken to wider audience.
In the village, we will also be hosting a 4G/5G live network which will have Live Radio and 4G/5G Core. Attendees will be able to understand the call flow of Telecom and the Weaknesses in the call flows.
Website: https://telecomvillage.com/
Twitter: https://twitter.com/TelecomVillage

XRVillage
Friday: 10:00am–8:00pm
Saturday: 10:00am–8:00pm
Sunday: 10:00am–2:00pm
Where: Contest Area, Forums
Augmented reality (AR), virtual reality (VR), collectively referred to extended reality (XR) technologies have the potential to revolutionize the way we interact with the world around us. However, as with any new technology, there are security and privacy concerns that must be addressed.
These concerns include data privacy, hacking of haptic hardware, software, and XR Infrastructure and public safety. In XR systems, personal information, such as location data and biometric information, can be collected and shared without the user’s knowledge or consent.
Current XR development platforms for these technologies do not allow for built in security, safety, and privacy.
The XRVillage was created to:
The Vision
To promote Security, Privacy, and Safety for XR software, hardware, and environments including the Metaverse, through awareness, education, policy and legal coordination, and exploitation and remediation of known and unknown vulnerabilities.
The Mission
Provide access to XR devices and applications for the security community for vulnerability testing; provide guidance & collaborative recommendations back to Policy makers, legislators, law enforcement, vendors, users, and the world on best Security, Privacy, and Safety practices in XR
At the Defcon31 XRVillage hackers can expect expert XR security talks, policy and legal discussions, and a Hands-on Haptics Hackathon. XR devices will be on hand to demonstrate applications and environments such as BadVR w/Microsoft HoloLens (Example) showing virtual visibility to all surrounding WIFI networks via AR. They and others will show what is already being built in XR environments that may, or may not cross a line for privacy, safety, and security in the space. Specific breakout sessions will be available for hackers to discuss current efforts by XR Vendors to address security concerns.
Expert XR Security Talks will focus on exploitation of XR in the wild: What’s been done and what’s coming.
A Policy & Legislation panel of Global Governments and Law Enforcement Agencies will discuss challenges with current policies, and their limitations in enforcing privacy, safety, and security in XR. The panel will include a lengthy Q&A for hackers to present their thoughts.
Hackers will get their hands dirty with the Hands-On Haptics Hackathon. They will be given XR headsets within a test environment to identify specific vulnerabilities; with extra credit to anyone who finds new ones.
Hackers will have many different elements of XR to immerse themselves in, challenge their preconceptions of XR, and inspire them to learn more.
Website: https://xrvillage.org/
Twitter: https://twitter.com/XRVillage

DEFCON GROUPS VR (DCGVR)
Friday & Saturday, 10:00am–5:00pm (talks/panels), 15:00 — late night (socializing)
Where? This year our event will be hosted in Frame VR
Twitch: https://www.twitch.tv/defcon_groups
YouTube:
DEF CON Groups VR was created with strong support from Jayson E. Street, who is the DEF CON Groups Ambassador and close friend. Not all DEF CON Groups members can attend DEF CON conference in person due to variety of factors — financial hardship, disability, or political (getting a visa is problematic if you live in certain countries)
DEF CON Groups VR brings hackers / DEF CON Groups together in Virtual Reality setting. We provide closest experience to being at DEF CON in person and have been doing it since DEF CON 28. DEF CON Groups VR events combine ability to socialize with like-minded individuals, give/watch presentations, as well as participate in panels
We will have talks and panels during the day, socializing events in the evenings!
DEF CON Groups VR has a good track record for hosting events. We have a solid team of volunteers dedicated to the success and high quality of each event we host. Please review our YouTube channel for glimpse into previous events.
Website: https://www.dcgvr.org/

Aerospace Village
DEF CON 30 Aerospace Village is a researcher led, non-profit whose mission is to build a diverse community focused on the security of everything from airports, air traffic management, aircraft and space.
Discussion Forum: https://forum.defcon.org/node/244860
Village Schedule: https://aerospacevillage.org/events/upcoming-events/def-con-30/def-con-30-schedule/
More Info:
https://twitter.com/secureaerospace
https://aerospacevillage.org
https://www.linkedin.com/company/aerospace-village
AI Village
Artificial Learning techniques are becoming more prevalent in core security technologies like malware detection and network traffic analysis. Its use has opened up new vectors for attacks against non-traditional targets, such as deep learning based image recognition systems used in self driving cars. There are unique challenges in defending and attacking these machine learning systems that the security community needs to be made aware of. This AI Village will introduce DEF CON attendees to these systems and the state of the art in defending and attacking them. We will provide a setting to educate DEF CON at large through workshops and a platform for researchers in this area to share the latest research.
Discussion Forum: https://forum.defcon.org/node/244879
More Info:
https://discord.com/invite/GX5fhfT
https://twitter.com/aivillage_dc
AppSec Village
The AppSec Village welcomes all travelers to choose from talks by expert community members, an awesome AppSec-focused (CTF)2, online workshops, and more. Bring your thirst for knowledge and passion for breaking things, and your visit to AppSec Village will be a thrill!
Discussion Forum: https://forum.defcon.org/node/244879
More Info:
https://twitter.com/appsec_village
https://www.youtube.com/channel/UCpT8Ll0b9ZLj1DeEQQz7f0A
https://www.appsecvillage.com/
Bio-Hacking Village
Borne in 2014, the Biohacking Village started with a small space and a big idea: Bring the forefront of citizen science and biomedical security to the world’s biggest hacker conference. With partners such as the FDA and Mayo Clinic, the Biohacking Village has become a primary conduit for the healthcare community to engage positively and proactively with security researchers.
Device Lab:
A high-collaboration environment to build trust and trustworthiness in healthcare, connecting security researchers, manufacturers, hospitals, and regulators, to learn from each other and develop their skills. Device Lab research benefits patients by providing manufacturers valuable feedback on cyber safety of their devices with high fidelity.
Speaker Lab:
Our speakers hail from varying fields in the biomedical ecosystem to engage security researchers and healthcare stakeholders. We welcome self made entrepreneurs, security researchers, inventors, government regulators makers, innovators to discuss real world solutions to some of humanity’s most pressing challenges and opportunities in the areas of health, security, and technology.
Catalyst Lab:
The Catalyst Lab provides the opportunity to interact with outstanding faculty, thought leaders and cutting edge experts in the biomedical industry who provide up-to-date advice and training in the developing field of translational medicine by fostering leadership, entrepreneurship, and commercialization activities.
Discussion Forum: https://forum.defcon.org/node/244865
More Info:
https://twitter.com/DC_BHV
https://m.twitch.tv/biohackingvillage/profile
https://www.youtube.com/channel/UCm1Kas76P64rs2s1LUA6s2Q/about?view_as=subscriber
Blacks In Cybersecurty Village
This village seeks to highlight Black experiences, innovations in the field, Black culture, Black history as well as provide a platform for the discussion of social justice and its impact on the progression and development of Technology.
https://www.blacksincyberconf.com/bic-village
Discussion Forum: https://forum.defcon.org/node/244885
Blue Team Village
Blue Team Village is returning for our third DEF CON! Focusing on the defensive side of hacking, we aim to offer our hybrid community the same kind of talks and workshops that you would experience in person, adapted for this year’s remote circumstances. Likewise, we’ll be seeing the return of our popular OpenSOC CTF — the schedule can be found on our website at blueteamvillage.org. Come join us to learn about defensive-side hacking, and join our community of like-minded hackers for fun, learning, and mentorship.
Discussion Forum: https://forum.defcon.org/node/244855
More Info:
https://twitter.com/BlueTeamVillage
https://twitch.tv/BlueTeamVillage
Car Hacking Village
Learn, hack, play. The Car Hacking Village is an open, collaborative space to hack actual vehicles (this year virtually) that you don’t have to worry about breaking! Don’t have tools? No worries, since our challenges are virtual this year, you will only need a web browser and terminal access to access our challenges. Never connected to a car?
We also have great Car Hacking Village swag!! Head on over to our store and order today!! https://stores.customink.com/carhackingvillage
Discussion Forum: https://forum.defcon.org/node/244891
More Info:
https://www.carhackingvillage.com/
https://twitter.com/CarHackVillage
https://stores.customink.com/carhackingvillage
Cloud Village
Cloud village is an open platform for researchers interested in area of cloud security. We plan to organize talks, tool demos, CTF and workshops around Cloud Security and advancements.
Discussion Forum: https://forum.defcon.org/node/244897
More Info:
https://cloud-village.org
https://twitter.com/cloudvillage_dc
https://www.youtube.com/channel/UCupKln6fqF9tBTweRE6xNDQ
Crypto & Privacy Village
A place for puzzles, privacy, and pseudorandom permutations. We will be streaming talks on a variety of cryptography and privacy topics, as well as hosting our annual Goldbug puzzle. The Gold Bug starts Friday at 10am PT until Sunday 12pm PT
Discussion Forum: https://forum.defcon.org/node/244871
More Info:
https://twitter.com/cryptovillage
https://twitch.tv/cryptovillage/
https://cryptovillage.slack.com
https://www.youtube.com/channel/UCGWMS6k9rg9uOf3FmYdjwwQ
Data Duplication Village
The Data Duplication Village is ready for DC 31! We have all the updated bits and bytes available from infocon.org packed up into nice, neat packages. If you’re looking for something to fill up all your unused storage, we have a few nice hash tables and all of the DefCon talks. Add to that just about every other security con talk known to human-kind! We provide a “free-to-you” service where of direct access to terabytes of useful data to help build those hacking skills.
Check the schedule and/or dcddv.org for the most up-to-date information.
HOW IT WORKS
The DDV provides a core set of drive duplicators and data content options. We accept 6TB and larger drives on a first come, first served basis and duplicate ’till we can no longer see straight. Bring in your blank SATA3 drives — check them in early — to get the data you want. Come back in about 24 hours to pick up your data-packed drive. Space allowing, we’ll accept drives all the way through until Saturday morning — but remember, it’s FIFO — get those drives in early!
WHAT YOU GET
We’re working on more content right up until the last minute but for dc29, we provided:
– 6TB drive 1–3: All past hacking convention videos that DT could find, built on last years collection and always adding more for your data consuming appetite.
– 6TB drive 2–3: freerainbowtables.com hash tables (1–2)
– 6TB drive 3–3: GSM A5/1 hash tables plus remaining freerainbowtables.com data (2–2)
The DC 30 content will be posted at dcddv.org once finalized
Discussion Forum: https://forum.defcon.org/node/244903
Website: https://dcddv.org/
Twitter: https://twitter.com/DDV_DC
Ham Radio Village
Ham Radio is all about overcoming obstacles and communicating over long distances without physical contact. That’s why Ham Radio Village is excited to return for a second year as part of DEFCON 29. Join us on the DEF CON discord where we will be giving everyone the opportunity to learn more about ham radio than they do today.
Discussion Forum: https://forum.defcon.org/node/244915
More Info:
https://twitter.com/HamRadioVillage
https://www.twitch.tv/HamRadioVillage
https://www.hamvillage.org/dc28.html
HHV/SSV
A basic bar to working with embedded electronics is learning to properly meld metal, creating both a electrical and physical bond. You can only get so far with a breadboard and wires hanging out everywhere. At some point you will need to take the device out of the lab and introduce it to the rigors of the world. We supply the irons and the skills to help you, whether that is your first time fusing metal or getting those lead wires on a UART breakout. Details @ dcssv.org
Discussion Forum: https://forum.defcon.org/node/244921
Website: https://dchhv.org/
ICS Village
Connecting public, industry, media, policymakers, and others directly with ICS systems and experts.
Hack the Plan[e]t Capture the Flag (CTF) contest will feature Howdy Neighbor and the Industrial Control System (ICS) Range. Building off of last year’s, the CTF will integrate both Internet of Things (IoT) and ICS environments with interactive components for competitors to test their skills and knowledge.
Discussion Forum: https://forum.defcon.org/node/244927
More Info:
https://twitter.com/ICS_Village
https://www.linkedin.com/company/icsvillage
https://www.youtube.com/channel/UCI_GT2-OMrsqqglv0JijHhw
https://www.twitch.tv/ics_village
IOT Village
IoT Village advocates for advancing security in the Internet of Things (IoT) industry through bringing researchers and industry together. IoT Village hosts talks by expert security researchers, interactive hacking labs, live bug hunting in the lastest IoT tech, and competitive IoT hacking contests. Over the years IoT Village has served as a platform to showcase and uncover hundreds of new vulnerabilities, giving attendees the opportunity to learn about the most innovative techniques to both hack and secure IoT. IoT Village is organized by security consulting and research firm, Independent Security Evaluators (ISE), and the non-profit organization, Village Idiot Labs (VIL).
Discussion Forum: https://forum.defcon.org/node/244939
More Info:
https://twitter.com/IoTvillage
https://www.twitch.tv/iotvillage
https://www.iotvillage.org
Physical Security Village
Formerly known as the Lock Bypass Village, the Physical Security Village (PSV) is a security awareness initiative that makes appearances at security conferences and other educational functions. You can find some of the content we’ve created below.
Discussion Forum: https://forum.defcon.org/node/244958
More Info:
https://bypassvillage.org/
https://twitter.com/bypassvillage/
https://twitch.tv/bypassvillage/
Lock Picking Village
Want to tinker with locks and tools the likes of which you’ve only seen in movies featuring secret agents, daring heists, or covert entry teams? Then come on by the Lockpick Village, run by The Open Organisation Of Lockpickers, where you will have the opportunity to learn the hands-on how the fundamental hardware of physical security operates and how it can be compromised.
The Lockpick Village is a physical security demonstration and participation area. Visitors can learn about the vulnerabilities of various locking devices, techniques used to exploit these vulnerabilities.
Experts will be on hand to demonstrate and discuss pick tools, and other devices that are generally available. By exploring the faults and flaws in many popular lock designs, you can not only learn about the fun hobby of sportpicking, but also gain a much stronger knowledge about the best methods and practices for protecting your own property.
Discussion Forum: https://forum.defcon.org/node/244933
More Info:
https://toool.us/
https://twitter.com/toool
https://www.twitch.tv/toool_us
MisInformation Village
Misinformation is a snowballing, mutating information problem that is affecting human communications, social relationships and has real-world consequences. Misinformation, disinformation and malinformation campaigns undermine democratic institutions, legitimate elections results, public health and public health responses and has created a space for the rise of autocratic regimes and warfare.
We will apply our organizational skills and subject matter expertise to bring together experts from different professions, governments, civil society and private enterprise to come together and create a platform to define and combat misinformation, explore and align missions and tactics to achieve this goal.
Discussion Forum: https://forum.defcon.org/node/245077
Official website is https://misinfovillage.org. Twitter: @misinformationvillage
Payment Village
Payment technologies are an integral part of our lives, yet few of us know much about them. Have you ever wanted to learn how payments work? Do you know how criminals bypass security mechanisms on Point of Sales terminals, ATM’s and digital wallets? Come to the Payment Village and learn about the history of payments. We’ll teach you how hackers gain access to banking endpoints, bypass fraud detection mechanisms, and ultimately, grab the money!
Discussion Forum: https://forum.defcon.org/node/244951
More Info:
https://www.paymentvillage.org/
https://www.twitch.tv/paymentvillage
https://www.youtube.com/channel/UCivO-5rpPcv89Wt8okBW21Q
https://twitter.com/paymentvillage
Packet Hacking Village
The Packet Hacking Village welcomes all DEFCON 29 attendees and we have something for every level of security enthusiast, from beginners to those seeking a black badge. PHV Speakers, Workshops, and Walkthrough Workshops delivers high quality content for all skill levels. Packet Detective and Packet Inspector offers hands-on exercises to help anyone develop or improve their Packet-Fu. WoSDJCo has some of the hottest DJs at con spinning virtual for your enjoyment. And finally… Capture The Packet, the ultimate cyber defense competition that has been honored by DEF CON as a black badge event for nearly a decade.
Discussion Forum: https://forum.defcon.org/node/244945
Website: https://forum.defcon.org/node/244945
Policy Village
Hackers are early users and abusers of technology, and that technology is now critical to modern life. As governments make policy decisions about technology Hackers, researchers and academics need to be part of that conversation before decisions are made, not after policies are implemented. To do that DEF CON is a place for everyone on the policy and technology spectrum to interact, learn from each other, and improve technology.
Policy will build connections across and between technical and policy experts and provide opportunities for attendees interested in learning more about how policy and technology intersect and to examine the challenges at this intersection.
Our Policy program will consist of Main stage presentation and panels, daytime sessions in our policy track, and some evening lounges that will provide an off the record and more intimate setting to have policy-focused conversation
Where: Ceasars Forum — Rooms 213–223
Discussion Forum: https://forum.defcon.org/node/244979
Website: https://www.defcon.org/html/links/dc-policy.html
Quantum Village
This is the safe space for anyone to discover, learn, create and break all things around Quantum Technologies. We are committed to helping raise awareness and involvement in the quantum industry and with quantum technologies. We know that in order to avoid the mistakes of past technological surges, we have to engage as many people with as wide a variety of interests and backgrounds as possible.
To date, very few (if any) people have actually hacked a quantum computer, and we want to change that! Something we demonstrated last year was that quantum computers are only a small part ‘magic’ — the rest are familiar API and tech stack technologies we see everywhere. These devices are set to become more and more commonplace as more time, money, and intelligence is spent on improving them — so let’s get quantum hacking!
Our ethos is to encourage participants to engage, explore, and discuss topics surrounding this new and burgeoning technology ecosphere that is in many ways very different from what has gone before in technical revolutions — but there are many hallmarks that are the same, and which we can use to shape this new paradigm of computing. That conversation is essential to bring before some of the most talented and brilliant technologists going; the hackers at DEF CON.
Twitter: @quantum_village
Website: https://quantumvillage.org/
Discussion Forum: https://forum.defcon.org/node/244973
Recon Village
Recon Village is an Open Space with Talks, Live Demos, Workshops, Discussions, Beginner Sessions, CTFs with a common focus on Reconnaissance. The village is meant for professionals interested in areas of Open Source Intelligence (OSINT), Threat Intelligence, Reconnaissance, and Cyber Situational Awareness, etc. with a common goal of encouraging and spreading awareness around these subjects.
For DEFCON 29 we will be running a bunch of OSINT / RECON talks as well as our RECON CTF.
Website: https://reconvillage.org
Twitter: https://twitter.com/reconvillage
Discussion Forum: https://forum.defcon.org/node/245016
Red Team Village
The DEF CON Red Team Village is a community-driven effort for and by the offensive security community members (red teams and ethical hackers). The goal of the village is to expand the spectrum of red team and offensive security training, as well as to create opportunities for individuals to both, present and learn. The DEF CON Red Team Village community creates different activities including many technical presentations, hands-on workshops, trainings, demos, capture the flag (CTF), games, and other activities from participants.
Discussion Forum: https://forum.defcon.org/node/245022
Village Schedule: https://redteamvillage.io/schedule.html
More Info:
https://twitter.com/VillageRedTeam
https://RedTeamVillage.io/YouTube
https://www.twitch.tv/redteamvillage
Radio Frequency Village
The RF Village (Formally the Wireless Village) is run by the RF Hackers Sanctuary as an environment where people come to learn about the security of radio frequency (RF) transmissions which includes wireless technology, applications of software defined radio (SDR), Bluetooth (BT), Zigbee, WiFi, Z-wave, RFID, and all other protocols within the useable RF spectrum. RF Hackers Sanctuary is supported by a group of experts in the areas of information security as it relates to RF technologies. RF Hackers Sanctuary’s common purpose is to provide an environment in which participants may explore these technologies with a focus on improving their skills through offense and defense. These learning environments are provided in the form of guest speakers, panels, and Wireless Capture the Flag games.
Discussion Forum: https://forum.defcon.org/node/244984
Website: https://rfhackers.com/
Social Engineering Community Village
Welcome to the Social Engineering Community! The SEC village focuses purely on the human aspect of security, Social Engineering, with the goal of enabling people of all ages and backgrounds interested in the subject matter with a venue to learn, discuss, and practice this craft.
This year, over the course of three days at DEF CON, you can expect the following events to take place in the village:
– Vishing Competition (#SECVC) — This competition is where prior selected teams (who have already put WEEKS of work into the competition) place live phone calls inside a soundproof booth in front of SEC audience members with the goal of eliciting as many objectives as possible. Highest score, wins! This competition takes place only on Friday.
– Youth Challenge — Anyone 18 and under is invited to play, where they can compete and learn about more than just social engineering; our challenges include areas in cryptography, network security, … and don’t worry, you won’t be alone. We’ve worked with other villages so you can get help you need and learn on the way!
– Cold Calls — This event lets DEF CON attendees sign up in the village (first come, first serve style) to place live phone calls inside of the soundproof booth. We provide the target and phone number, then give a few objectives (easy, medium, and hard), and start a countdown timer to see if they have the skills to get information from a stranger, with no preparation. There is nothing to prepare for, just bring yourself!
– SE Improv — Struggling to think on your feet? Discover the art of improvisation and transform every conversation into an opportunity! On Saturday, the improv team will start by presenting the benefits of utilizing Improv with Social Engineering and then have the opportunity for audience participation.
– Presentations — Come listen from folks in the field and get a glimpse of the newest techniques and perspectives in our presentations and panels hosted various times between Friday and Saturday in the village.
– SEC Reception — Want to hang out without the loud music, so that you can have a conversation? Join us on Saturday evening to schmooze with the SEC crew, competitors, speakers, meet new people, and chill with old friends! There will be a cash bar with alcoholic and non-alcoholic options.
Please check out our website and Twitter account to learn more and view the detailed schedule.
Website: https://www.se.community/
Twitter: @sec_defcon
Discussion Fourm: https://forum.defcon.org/node/245028
Tamper Evidence Village
Bypassing packages and tamper proof seals and leave no trace, formed by The Dark Tangent himself!
Discussion Forum: https://forum.defcon.org/node/245000
Voting Village
The Voting Machine Hacking Village (“Voting Village”) returns for its fourth year at DEF CON! As the only public third-party assessment of voting infrastructure in the world, the Voting Village attracts thousands of white hat hackers, government leaders, and members of the media to partake in the mission of rigorously researching voting systems and raising awareness of voting vulnerabilities.
The Voting Village gives hackers a unique opportunity to directly audit voting machines and other election equipment. With the 2020 elections looming and efforts to combat election vulnerabilities ongoing at the state and federal levels, the educational mission of the Voting Village remains as critical as ever.
Discussion Forum: https://forum.defcon.org/node/245034

DEFCON 31 WORKSHOPS
DEF CON WORKSHOPS IS BACK LIVE AND IN-PERSON!
Master List: https://forum.defcon.org/node/244772
Workshops are a great way for instructors from the community to share information with others on a variety of subjects. We will be using EventBrite again to handle pre-registration and are anticipating the same level of response that we have seen in previous years.
To keep everyone safe while participating in workshops, we are making the following changes:
- Max capacities listed, below, take into account keeping rooms at 80% capacity of the room.
- More space between attendees while still ensuring there are power strips available.
- Staggered check-in times in the morning in evening and an hour in-between sessions to reduce the number of people in the hallways at any given time.
Please note that all workshops are going to be in-person only with no parts of it streamed. Out of consideration for others, we ask that you do not pre-register unless you are certain you are able to attend.
DCG 201 DEFCON 31 WORKSHOP HIGHLIGHTS
Flipping the Coin: Red and Blue Teaming in Windows Environments
Thursday, August 10, 2023, at 2:00–6:00pm
EventBrite Link: https://www.eventbrite.com/e/angus-s...=oddtdtcreator
Max Class Size: 40
Red and blue are two sides of the same coin. Offensive and defensive teams deliver the best results when working together; sharing knowledge, ideas, and understanding with each other. And a core part of this information exchange is understanding each respective perspective. This is the overarching theme of the workshop; attackers thinking like defenders, and defenders thinking like attackers.
By the end of the workshop, attendees will:
1. Understand and perform common offensive attacks (supported by the Metasploit Framework) against Windows Domains, including:
- Pass the Hash attacks;
- ADCS abuse;
- PrintSpoofer exploits;
- LSASS exploitation (using Mimikatz);
- AD enumeration (using BloodHound);
- DACL abuse;
- Kerberos golden tickets; and
- DLL hijacking.
2. Understand the process of detecting attacks against Windows infrastructure, including how to design and implement their own detection rules based on attendees’ previous attacks, using:
- Sigma/Yara rules.
- Log ingestion/normalization platforms, and query engines (e.g. ELK).
3. Understand and appreciate how the actions and processes of red and blue teams are interlinked, for the greater collective good. Recommended (but not required) prior reading:
- https://nooblinux.com/metasploit-tut...e-39cfd8d6eb7c
- https://learn.microsoft.com/en-us/wi...vices-overview
- https://socprime.com/blog/sigma-rule...ginners-guide/
- https://github.com/socprime/SigmaUI
- https://blog.netwrix.com/2021/11/30/...-hash-attacks/
- https://posts.specterops.io/certifie...d-d95910965cd2
- https://www.elastic.co/guide/en/secu...print-dll.html
Skill Level: Beginner to Intermediate
Prerequisites for students:
Basic understanding of the Linux and Windows command line, and some basic knowledge of IP networking and routing. A basic understanding of Active Directory and exposure to the Metasploit Framework/Meterpreter are beneficial, but not required.
Materials or Equipment students will need to bring to participate:
Laptop, 8GB RAM, OpenVPN Client, Remote Desktop Protocol (RDP) client. It is strongly recommended that attendees have local administrative rights to their device.
An Internet connection is also required; DEF CON’s (authenticated) WiFi network will suffice, however attendees should consider alternative options in favour of resiliency (e.g. tethering/hotspotting cell phones).
Bios:
Angus (0x10f2c_) is currently a Senior Security Engineer working at a tech company. He obtained a love for all things computers by scavenging computer parts from local garbage pickups as a kid, and then trying to make them work together without blowing up. Angus eventually realised that a career could be made out of his skills hacking together poorly written LUA code in Garry’s mod, and finished a Bachelors in Network Security. In his professional career Angus has 5+ years working in Security Consulting, working across many industries and gaining many shells. More recently Angus has made the move to a security engineer focused role. When not hacking he loves to ski on the little snow that Australia has, and loves to paint small miniatures while listening to Drone Metal.
Having worked in the UK and Australian InfoSec industries for just over a decade, and following 8 and a half years of red teaming, Troy jumped the proverbial fence from red to blue, and is currently a Security Engineering Manager at a tech company. His interest and experience is in detection engineering, red teaming, threat modelling, hardware, and assessing ICS environments. Other interests include music, electronics, the outdoors, travel, rugby, CTF, and being bad at golf.
Snakes on a Screen: Taming Offensive IronPython Techniques
Friday, August 11, 2023, at 9:00am
EventBrite Link: https://www.eventbrite.com/e/anthony...=oddtdtcreator
Max Class Size: 80
IronPython is a powerful and flexible programming language that has been increasingly used by attackers due to its ability to bypass security controls. This practical workshop will explore the inner workings of IronPython and its unique features that enable sophisticated offensive techniques. Participants will gain hands-on experience in developing IronPython payloads that can evade modern security controls and execute malicious code on target systems.
The workshop will cover the following topics:
1. Introduction to IronPython: Basic syntax and usage of IronPython, and how it can be used in offensive scenarios.
2. BYOI and DLR: Bring Your Own Interpreter (BYOI) and Dynamic Language Runtime (DLR) concepts and their role in developing offensive payloads.
3. Malware Development with IronPython: Develop sophisticated payloads that can bypass modern security controls and execute malicious code on target systems.
4. Anti-Forensics and Evasion Techniques: Techniques to make the payloads more resilient to forensic analysis and detection.
5. Advanced Techniques: Advanced techniques like using IronPython with C# and PowerShell and integrating the payloads with other offensive tools.
This workshop is designed for offensive security professionals, red teamers, penetration testers, and anyone interested in exploring the capabilities of IronPython for offensive purposes.
Participants should have a basic understanding of Python and programming concepts. By the end of the workshop, participants will have a deeper understanding of IronPython and its capabilities for developing offensive payloads.
Skill Level: Intermediate
Prerequisites for students: A familiarity with python is preferred, but not required.
Materials or Equipment students will need to bring to participate: Laptop with Windows or other Windows VM
Bios:
Anthony “Coin” Rose, CISSP, is the Director of Security Researcher at BC Security, where he specializes in adversary tactic emulation planning, Red and Blue Team operations, and embedded systems security. He has presented at numerous security conferences, including Black Hat, DEF CON, HackSpaceCon, HackMiami, and RSA conferences. Anthony is the author of various offensive security tools, including Empire and Starkiller, which he actively develops and maintains. He is recognized for his work, revealing wide-spread vulnerabilities in Bluetooth devices and is the co-author of a cybersecurity blog at https://www.bc-security.org/blog/.
Gannon “Dorf” Gebauer is a Security Consultant at BC Security and specializes in threat intelligence and embedded system testing. He has led teams through the Cyber Patriot, a USAF CTF that tests both defense and offensive capabilities. Currently, his expertise is focused on building automation tools for range deployments. Dorf has taught courses at both, Blackhat and DEF CON.
Vincent “Vinnybod” Rose is the Lead Developer for Empire and Starkiller. He is a software engineer with a decade of expertise in building highly scalable cloud services, improving developer operations, and building automation. Recently, his focus has been on the reliability and stability of the Empire C2 server in the most recent major update (Empire 5). Vinnybod has presented at Black Hat and has taught courses at DEF CON on Red Teaming and Offensive PowerShell. He currently maintains a cybersecurity blog focused on offensive security at https://www.bc-security.org/blog/.
How hackers can send feedback directly to policymakers like the pros
Scheduled Date and Time: Friday, August 11, 2023, at 2:00pm
EventBrite Link: https://www.eventbrite.com/e/harley-...=oddtdtcreator
Max Class Size: 70
The first official comments on security policy live from DEF CON. The workshop will show hackers how to go through the process of submitting official comments to regulations and legislation.
Meeting with policymakers is only one way to make your voice heard. There are also formal channels for submitting written feedback on policy proposals that become a critical part of the record for regulations. These channels are open to the public, but non-policy professionals don’t always know how to access or make the most effective use of them.
This workshop will walk security researchers through the process of using regulations.gov and congress.gov to find open opportunities to influence regulations, and actually submit official comments via those channels from the workshop. The workshop will also talk through how to form an advocacy strategy to amplify the impact of the comments — for example, how to find the right policymakers and staff to follow up with.
The workshop will be led by policy professionals with deep ties to the security community.
Skill Level: All Levels
Prerequisites for students: None
Materials or Equipment students will need to bring to participate: To walk through the process and/or submit comments, bring a laptop, iPad, or other connected device you can type on.
Bios:
Harley Geiger is Counsel and Senior Director at Venable, LLP, where he leads the Security Research Legal Defense Fund and the Hacking Policy Council and counsels clients on a variety of cybersecurity issues. Prior to this, Geiger was Senior Director for Public Policy at Rapid7, where he worked to expand adoption of vulnerability disclosure and legal protections for security research. Geiger also worked as Senior Legislative Counsel in the U.S. House of Representatives, where he drafted Aaron’s Law, and served as Advocacy Director at the Center for Democracy & Technology.
Dr. Amit Elazari is Co-Founder and CEO of OpenPolicy, the world first tech-enabled policy and advocacy company, aiming to democratize access to information concerning future regulation action, policy and lobbying to entities of all sizes by leveraging scale and technology. Prior to OpenPolicy, she served as Head of Cybersecurity Policy for Intel Corp and chaired the Cybersecurity Committee for the Information Technology Industry Council (ITI) among others. She holds a Doctoral Degree in the Law (JSD) from Berkeley Law, and graduated summa cum laude with three prior degrees in law and business. Her research appeared in leading academic journals, key conferences such as RSAC, Black Hat, DEFCON, Bsides, and USENIX, and was featured at the WSJ and NYT. She co-founded Disclose.io, a non-profit that foster adoptions of legal protections for good-faith security research. Amit has a diverse background in technical, policy, and legal roles, and practiced Hi-tech, Venture Capital, and M&A law at Israel’s largest law firm, Goldfarb Gross Seligman & Co.
Android App Hacking — Hacking for Good!
Scheduled Date and Time: Friday, August 11, 2023, at 9:00am–1:00pm
EventBrite Link: https://www.eventbrite.com/e/maria-u...=oddtdtcreator
Max Class Size: 50
Welcome to the world of Android Hacking! This is a hands-on workshop designed to introduce you to the knowledge, tools and techniques for analyzing and exploiting vulnerabilities in Android applications.
The workshop will start by presenting hacking for good, insights on the Android bug bounty, then it will cover the basic concepts of Android applications, walk you through industry standard tools and techniques and then let you experiment on your own with our Android reverse engineering CTF!
Come and hack with us!
The workshop requires no prior knowledge of Android or reverse engineering.
Skill Level: Beginner to Intermediate
Prerequisites for students: Before the workshop, students should follow the setup instructions to ensure they can start working on the CTFs in the workshop.
https://tinyurl.com/aah-setup
There is no pre-required knowledge.
Materials or Equipment students will need to bring to participate: Laptop with 20+ GB free hard disk space 4+ GB RAM
Mac. Windows 7/8 , Ubuntu 12.x + (64 bit Operating System),
ADB, apktool, Python & pip, JDK, jadx, Burp Suite, Wireshark, Frida, Ghidra
Administrative access on your laptop
Bio:
Maria Uretsky is leading the Android Vulnerability Rewards program at Google. Her passion is to break all the things before the bad actors do, to ensure they are kept out. During her 10+ years of software engineering and security work, she has been part of Google Cloud Security, Azure Sentinel, Windows Defender and AVG.
Kavia Venkatesh is a Technical Program Manager on the Android Security Team at Google where she leads the execution of the Android Security Release Program aka Android Security Bulletin. Over the last 7+ years has led numerous security initiatives. Now, she’s passionate about sharing her knowledge with the world.
JJ is a Senior Security SWE at Google’s Android Security & Privacy team where he is developing tools to fight abuse in Android with focus on JavaScript-based frameworks. He has also designed CTF challenges and helped organize GoogleCTF in the past few years. Before Google, he was a Cybersecurity researcher at iSecLab and earned his PhD in Cybersecurity from Northeastern University, Boston, MA. Some domains he is active in are large-scale web security & privacy measurement, program analysis, and Malware detection.
Olivier Tuchon is a Security Engineer on the Android Vulnerability Research team. Olivier has been working at Google for almost 5 years, he started by chasing malware/PHA in the Play Store and into the wild (OffMarket) with a speciality in Stalkerware. Now, Olivier looks for vulnerabilities in 3P Android applications. Before Google, Olivier had been a Security Engineer in the French Army for 12 years.
Learning to Hack Bluetooth Low Energy with BLE CTF
Scheduled Date and Time: Friday, August 11, 2023, at 2:00pm
EventBrite Link: https://www.eventbrite.com/e/ryan-ho...=oddtdtcreator
Max Class Size: 90
BLE CTF is a series of Bluetooth Low Energy challenges in a capture-the-flag format. It was created to teach the fundamentals of interacting with and hacking Bluetooth Low Energy services. Each exercise, or flag, aims to interactively introduce a new concept to the user.
Over the past few years, BLE CTF has expanded to support multiple platforms and skill levels. Various books, workshops, training, and conferences have utilized it as an educational platform and CTF. As an open source, low-cost of entry, and expandable education solution, BLE CTF has helped progress Bluetooth security research.
This workshop will teach the fundamentals of interacting with and hacking Bluetooth Low Energy services. Each exercise, or flag, aims to interactively introduce a new concept to the user. For this workshop, we will undergo a series of exercises to teach beginner students new concepts and allow more seasoned users to try new tools and techniques. After completing this workshop, you should have a good solid understanding of how to interact with and hack on BLE devices in the wild.
If you have done BLE CTF in the past, this class is still valuable. For advanced users, we offer BLE CTF Infinity, a sequel to BLE CTF. The workshop will also showcase new hardware platforms and client tools for interacting with and completing the exercises.
To prepare for the workshop, please follow the setup documentation located at https://github.com/hackgnar/ble_ctf/...kshop_setup.md
Skill Level: Beginner to Intermediate
Prerequisites for students: To prepare for the workshop, please follow the setup documentation located at https://github.com/hackgnar/ble_ctf/...kshop_setup.md
Materials or Equipment students will need to bring to participate:Preferably a Linux box with a Bluetooth controller or a Bluetooth USB dongle. An OSX or Windows machine with a Linux VM and USB passthough works as well but should be setup and tested before the workshop.
Bio:
Ryan Holeman resides in Austin, Texas, where he works as the CISO for the peer-to-peer payment platform Strike. He is currently pursuing a Ph.D. in cyber defense from Dakota State University. He has spoken at respected venues such as Black Hat, DEF CON, Lockdown, BSides, Ruxcon, Notacon, and Shmoocon. You can keep up with his current activity, open source contributions, and general news on his blog. His spare time is mostly spent digging into various network protocols, random hacking, creating art, and shredding local skateparks.
Machine Learning for N00bs
Scheduled Date and Time: Friday, August 11, 2023, at 2:00pm
EventBrite Link: https://www.eventbrite.com/e/sam-bow...=oddtdtcreator
Max Class Size: 80
Every technical product is now incorporating machine learning at an explosive rate. But most people, even those with strong technical skills, don’t understand how it works, what its capabilities are, and what security risks come with it. In this workshop, we’ll make machine learning models using simple Python scripts, train them, and evaluate their value. Projects include computer vision, breaking a CAPTCHA, deblurring images, regression, and classification tasks. We
will perform poisoning and evasion attacks on machine learning systems, and implement deep neural rejection to block such attacks.
No experience with programming or machine learning is required, and the only software required is a Web browser. We will use TensorFlow on free Google Colab cloud systems.
All materials and challenges are freely available at samsclass.info, and will remain available after the workshop ends.
Skill Level: Beginner
Prerequisites for students: None
Materials or Equipment students will need to bring to participate: A computer with a Web browser
Bios:
Sam Bowne has been teaching computer networking and security classes at City College San Francisco since 2000, and is the founder of Infosec Decoded, Inc. He has given talks and hands-on trainings at Black Hat USA, RSA, DEF CON, DEF CON China, HOPE, and many other conferences.
Credentials: PhD, CISSP, DEF CON Black Badge Co-Winner
Elizabeth Biddlecome is a consultant and instructor, delivering technical training and mentorship to students and professionals. She leverages her enthusiasm for architecture, security, and code to design and implement comprehensive information security solutions for business needs. Elizabeth enjoys wielding everything from soldering irons to scripting languages in cybersecurity competitions, hackathons, and CTFs.
Kaitlyn Handelman is an offensive security engineer at Amazon. Her focus is cybersecurity in space. In addition to traditional penetration testing, Kaitlyn works on physical devices and RF signals. In her free time, she enjoys ham radio, astronomy, and her cat, Astrocat.
Irvin Lemus, CISSP is a Cyber Range Engineer at By Light IT Professional Services, training military personnel through international cyber security exercises. Irvin has been in the field
since 2006, involved with cybersecurity competitions since 2015 as a trainer, coach, and mentor. He also has taught IT and Cybersecurity courses at Coastline and Cabrillo
Colleges. He is the BACCC Cyber Competitions Regional Coordinator, Board member at Pacific Hackers and is a speaker at DEFCON. He describes himself as, “A professional troublemaker who loves hacking all the things.”
Protecting the AWS ecosystem — Misconfigurations, IAM, and Monitoring
Scheduled Date and Time: Thursday, August 10, 2023, at 9:00pm
EventBrite Link: https://www.eventbrite.com/e/rodrigo...s-668351787187
Max Class Size: 60
Cloud providers’ ecosystems have brought a lot of new challenges to companies and Security teams. Many new attack vectors create known and unknown attack vectors, generating a considerable need for further research and detection in this field.
In the current cloud security world, access keys are the new perimeter, and permissions associated with those keys are the limits. In many real-world scenarios, leaked access keys are the initial vectors to get into an organization’s cloud environments. Therefore, the least privilege and detection in real-time becomes critical.
Specifically, in AWS, we are talking about more than three hundred (300+) services that an attacker could create their specific attack path to achieve their goal. Considering this chaotic scenario, we developed this workshop to teach how to mitigate those new vectors and improve the company’s overall cloud security posture. The workshop will cover misconfigurations, AWS IAM (Identity and Access Management) least privilege, and control plane (Cloudtrail) monitoring.
This workshop will help organizations improve their cloud security posture in these three fields — misconfigurations, IAM permissions management, and control plane monitoring. There will be practical demonstrations, hands-on labs, and some Capture The Flag (CTF) to practice incident response.
Skill Level: Intermediate
Prerequisites for students: AWS basic to intermediate knowledge
Materials or Equipment students will need to bring to participate: Just bring a laptop. Demonstrations and Capture The Flag (CTF) exercises will be executed in my AWS account and using CTFd.
Bio:
Rodrigo Montoro has over 23 years of experience in Information Technology and Computer Security. For most of his career, he has worked with open-source security software (firewalls, IDS, IPS, HIDS, log management, endpoint monitoring), incident detection & response, and Cloud Security. Currently is Head of Threat & Detection Research at Clavis Security. Before that, he worked as Cloud Researcher at Tenchi Security, Head of Research and Development at Apura Cyber Intelligence, SOC/Researcher at Tempest Security, Senior Security Administrator at Sucuri, and Researcher at Spiderlabs. Author of 2 patented technologies involving innovation in the detection field. One is related to discovering malicious digital documents. The second one is in how to analyze malicious HTTP traffic. Rodrigo has spoken at several open source and security conferences (Defcon Cloud Village, OWASP AppSec, SANS (DFIR, SIEM Summit & CloudSecNext), Toorcon (USA), H2HC (São Paulo and Mexico), SecTor (Canada), CNASI, SOURCE, ZonCon (Amazon Internal Conference), Blackhat Brazil, BSides (Las Vegas e SP)).
The Joy of Reverse Engineering: Learning With Ghidra and WinDbg
Scheduled Date and Time: Saturday, August 12, 2023, at 2:00pm
EventBrite Link: https://www.eventbrite.com/e/wes-mcg...s-668400352447
Max Class Size: 80
While it can be intimidating to “get into” software reverse engineering (RE), it can be very rewarding. Reverse engineering skills will serve you well in malicious software analysis, vulnerability discovery, exploit development, bypassing host-based protection, and in approaching many other interesting and useful problems in hacking. Being able to study how software works, without source code or documentation, will give you the confidence that there is nothing about a computer system you can’t understand, if you simply apply enough time and effort. Beyond all of this: it’s fun. Every malicious program becomes a new and interesting puzzle to “solve”.
The purpose of this workshop is to introduce software reverse engineering to the attendees, using static and dynamic techniques with the Ghidra disassembler and WinDbg debugger. No prior experience in reverse engineering is necessary. There will be few slides — concepts and techniques will be illustrated within the Ghidra and WinDbg environments, and attendees can follow along with their own laptops and virtual environments. We will cover the following topics:
- Software Reverse Engineering concepts and terminology
- Setting up WinDbg and Ghidra
- The execution environment (CPU, Virtual Memory, Linking and Loading)
- C constructs, as seen in disassembled code
- Combining static and dynamic analysis to understand and document compiled binary code
- Methodology and approaches for reverse engineering large programs
- Hands-on malware analysis
- How to approach a “new-to-you” architecture
Skill Level: Beginner
Prerequisites for students: No previous reverse engineering experience required. Basic familiarity with programming in a high-level language is necessary (C preferred, Scripting languages like Python would be okay).
Materials or Equipment students will need to bring to participate: A laptop with a fresh Windows 10 Virtual Machine.
- Being able to dedicate 8GB RAM to the VM (meaning, you probably have 16GB in your laptop) will make the experience smoother, but you can get by with 4GB
- 10 GB storage free in the VM (after installing Windows)
- Administrative privileges
- Ability to copy exercise files from USB
We will be working with live malware samples. Depending on your comfort level with this, bring a “burner” laptop, use a clean drive, or plan on doing a clean install before and after the workshop.
Bio:
Dr. Wesley McGrew directs research, development, and offensive cyber operations as Senior Cybersecurity Fellow for MartinFed. He has presented on topics of penetration testing and and malware analysis at DEF CON and Black Hat USA and taught a self-designed course on reverse engineering to students at Mississippi State University, using real-world, high-profile malware samples. Wesley has a Ph.D. in Computer Science from Mississippi State University for his research in vulnerability analysis of SCADA HMI systems.

DEFCON COMMUNITIES
DEF CON started as talks and parties that evolved into a community of those who with a hacker’s mindset and an insatiable curiosity of how things work. We are committed to creating a place for all hackers to share, interact and learn from each other. Sometimes, though, we have to reassess whether the structure of DEF CON is helping or hindering this vision.
One example of this is how we categorize creators. There are a lot of content departments at DEF CON. If you’re a Vendor, you go here. If you’re a Village, you go over there. If something doesn’t quite fit our categories we force them to fit: The EFF or a University in our vendor room for example.
With “Communities” we intend to work with some of the content creators that don’t fit perfectly into categories like “Village” or “Contest”. We want to help them define the best way to showcase what they came to share without a prior template limiting their options. What would the EFF’s space look like if they didn’t have to try to fit in with Vendors? This is a good time to get together and figure it out.
This year at DEF CON you’ll see this new DEF CON Community format in action with DEF CON Groups (DCG), Women in Information Security Professionals (WISP), DEF CON Hackers with Disabilities (HDA), and some more as groups learn of this new option. Please make some time to visit them and check out their new offerings. As always, thank you for helping us grow and test out new things. See you soon!
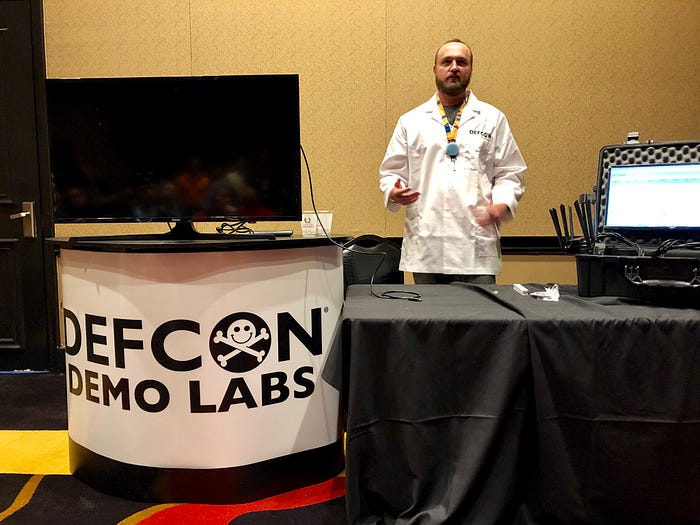
DEF CON 31 DEMO LABS
Explore the exploit the new haxor tools this year!
Full List: https://forum.defcon.org/node/244767
DCG 201 DEFCON 31 DEMO LAB HIGHLIGHTS
Veilid
Saturday August 12, 10:00–11:55, Committee Boardroom, Forum
TC Johnson & Deth Veggie
Veilid is a new, distributed communication protocol developed by Cult of the Dead Cow’s Dildog (of BO2K fame). This p2p, E2EE, distributed protocol is being released at Defcon 31, fully open source, and with an example app called Veilid Chat. These demos will cover setting up an identity, connecting to others, deploying heavy nodes to support the network, and contributing to the project.
TC: Rubber Duck to the actual developer of Veilid. Here to get you started on the future we were promised — communication free of a profit motive, free of corporate overlords, and free of other intrusive eyeballs.
The Deth Vegetable: cDc member since December 1990. Minister of Propaganda If everything is to be believed, he has alternately been a Special Forces Commando, Mexican wrestler, comicbook villain, bodyguard to Mr. T, designer drug manufacturer, electronics wizard, and used tire recycler.
Audience: Everyone, we’re changing the world, cDc style
https://forum.defcon.org/node/246329
Am I Exploitable? (MI-X)
Saturday August 12, 12:00pm–1:55pm, Council Boardroom, Forum
Addressing security vulnerabilities begins with verifying the impact on an environment. Merely having a vulnerable package installed does not guarantee exploitability, as several conditions must align for the vulnerability to be applicable and exploitable. For example: is the operating system in question susceptible to the vulnerability? is the vulnerable component loaded to memory? is the required configuration in place? is there a patch installed? And more… Standard vulnerability scanners simply do not take these factors into account and thus require manual triage in order to answer “Can a vulnerability be exploited in a given environment?”. ‘Am I Exploitable?’ (MI-X), is an open-source tool aimed at effectively determining whether a local host or running container is truly affected by a specific vulnerability by accounting for all factors which affect *actual* exploitability. MI-X also prints out the logical steps it takes in order to reach a decision and can also provide a graphical representation of the validation flow. The tool can therefore help practitioners understand what are the factors that affect exploitability for each of the supported vulnerabilities.
Ofri Ouzan is an experienced Security Researcher who has been working in the cybersecurity field for over four years. She specializes in conducting security research on Windows, Linux, Cloud Platforms, and containerized applications with an emphasis on vulnerabilities. Her expertise lies in finding and solving complex problems in the cyber field, developing automation and open-source tools.
Yotam leads the vulnerability research team at Rezilion, focusing on research around vulnerability validation, mitigation, and remediation. Prior to Rezilion, Yotam filled several roles at PayPal Security organization, dealing with vulnerability management, threat intelligence, and Insider threat. Additionally, Yotam takes part in several OpenSSF working groups around open-source security as well as several CISA work streams around SBOM and VEX and is also a member of the PyCon Israel organization committee. He is passionate about Cyber Security and Machine Learning and is especially intrigued by the intersection between the domains, whether it be using ML in order to help solve Cyber Security challenges or exploring the challenges in securing ML applications.
Audience — Defense and Offense
https://forum.defcon.org/node/246341
BBOT (Bighuge BLS OSINT Tool)
Saturday August 12, 12:00pm–1:55pm, Accord Boardroom, Forum
BBOT (Bighuge BLS OSINT Tool) is a new recursive OSINT scanner inspired by Spiderfoot, but designed and optimized for bigger targets and faster scan times. BBOT is open-source and written in Python. Its 80+ modules range in function from subdomain enumeration to cryptographic exploitation. BBOT can map the attack surface of an organization (and sometimes get you RCE) in a single command.
Features include:
- multiple targets
- automatic dependencies w/ ansible
- python API
- subdomain enumeration
- email enumeration
- cloud bucket enumeration
- port scanning
- web service enumeration
- web screenshots
- web spidering
- vulnerability scanning (with nuclei and more)
TheTechromancer is a hacker at Black Lantern Security (BLS). He loves coding in Python, and is the creator of several security tools including ManSpider, TrevorSpray, and BBOT (Bighuge BLS OSINT Tool). He has also made contributions to other open-source projects such as Spiderfoot.
Paul Mueller is a Principal Operator at Black Lantern Security (BLS). He specializes in web application testing and application security. He loves finding complex hard-to-find web bugs, especially when they involve cryptography. He is also one of the developers for the BLS tools Writehat and BBOT (Bighuge BLS OSINT Tool). Prior to working with BLS, he spent over a decade as a DoD contractor providing both penetration testing and security analysis/incident handling. He got his start in the field as a systems administrator and later as a Signals Intelligence Analyst with the US Marine Corps.
Audience — BBOT is useful to both Offensive (for automating recon / bug bounties) and Defensive (for attack surface mapping).
https://forum.defcon.org/node/246339
BLE CTF
Saturday August 12, 2:00pm–3:55pm, Unity Boardroom, Forum
BLE CTF is a series of Bluetooth Low Energy challenges in a capture the flag format. It was created to teach the fundamentals of interacting with and hacking Bluetooth Low Energy services. Each exercise, or flag, aims to interactively introduce a new concept to the user. Over the past few years, BLE CTF has expanded to support multiple platforms and skill levels. Various books, workshops, trainings, and conferences have utilized it as an educational platform and CTF. As an open source, low cost of entry, and expandable education solution, BLE CTF has helped progress Bluetooth security research.
Ryan Holeman resides in Austin, Texas, where he works as the CISO for the peer-to-peer payment platform Strike. He is currently pursuing a Ph.D. in cyber defense from Dakota State University. He has spoken at respected venues such as Black Hat, DEF CON, Lockdown, BSides, Ruxcon, Notacon, and Shmoocon. You can keep up with his current activity, open source contributions, and general news on his blog. His spare time is mostly spent digging into various network protocols, random hacking, creating art, and shredding local skateparks.
Alek Amrani — bad at expense reports
Audience — Offensive & Hardware
https://forum.defcon.org/node/246345
Dracon
Friday August 11, 12:00pm–1:55pm, Council Boardroom, Forum
Dracon is an open-source Application and Cloud security automation framework that helps organizations create security workflows and improve their security posture. Dracon can run a wide range of security tools against any target, and it can deduplicate and enrich the results of those tools with contextual or regulatory information. Dracon can then send the enriched results to any visualization or data processing tool. Here are some of its key features: Automated security workflows: Dracon can automate the execution of security tools and the aggregation of results, which saves both time and effort. Scalable and flexible: Dracon is both scalable and flexible with a wide array of existing integrations and more on the way, Dracon integrates seamlessly with any exisitng toolset. Open source: Dracon is open-source platform, which means that it is free to use and modify.
Spyros is a Security Engineer with over a decade of experience in various organisations. Currently, he is helping Fintechs mature their AppSec programmes through automation. He maintains several Open Source projects including Dracon, opencre.org and others. Also, he is heavily involved with the OWASP foundation helping with outreach and diversity efforts.
Audience — Offense, Defense, AppSec, CloudSec
https://forum.defcon.org/node/246223
Ek47 — Payload Encryption with Environmental Keys
Friday August 11, 12:00pm–1:55pm, Committee Boardroom, Forum
Ek47 is a payload encryptor that leverages user-selected environmental keys associated with a target execution context. In the absence of these environmental keys, Ek47 payloads will not decrypt and execute. This creates a strong resistance to automated/manual analysis and reverse engineering of payloads. Ek47 supports many different environmental keys such as current user, domain, computer name, installed programs, and more. Additionally, Ek47 supports packing payloads of .NET assemblies, unmanaged DLLs, and raw shellcode. Ek47 payloads are themselves .NET assemblies and can be uploaded to disk or executed reflectively via any execute-assembly method. By default, a standard AMSI/ETW bypass is executed before the main payload is executed, but Ek47 makes it easy to add custom bypasses for more advanced evasion functionality. Additional miscellaneous features are provided such as entropy management, PE header stomping, and generation of service executables.
Kevin Clark is a Software Developer turned Penetration Tester at TrustedSec. He focuses on initial access and Active Directory exploitation. He contributes to open-source tools such as PowerShell Empire and Metasploit. He also writes his own custom security tools such as Badrats and Ek47. Kevin has a passion for education and volunteers on the Midwest Collegiate Cyber Defense Competition (CCDC) red team. He teaches courses with BC-SECURITY at BlackHat and other venues about Evasion, Red Teaming, Empire Operations, and Active Directory. Kevin authors a cybersecurity blog at https://henpeebin.com/kevin/blog.
Skyler Knecht is a Information Security Specialist who performs a variety of security assessments including, phishing, internal/external penetration tests and red teaming. Skyler Knecht worked as a consultant for three years and has recently pivoted to an internal team at Navy Federal Credit Union. Skyler Knecht is continually researching all fields of study but is primarily focused developing offensive tooling such as command and control frameworks and implants.
Audience — Offense, Red Team
https://forum.defcon.org/node/246229
EvilnoVNC: Next-Gen Spear Phishing Attacks
Friday August 11, 2:00–3:55, Committee Boardroom, Forum
EvilnoVNC is a Ready to go Phishing Platform. Unlike other phishing techniques, EvilnoVNC allows 2FA bypassing by using a real browser over a noVNC connection. In addition, this tool allows us to see in real time all of the victim’s actions, access to their downloaded files and the entire browser profile, including cookies, saved passwords, browsing history and much more.
Joel Gámez Molina is a systems administrator with more than ten years of experience, he currently works as a security consultant at Deloitte Touche Tohmatsu, where he develops adversarial simulation exercises (Red Team Operations). Previously, he was Chief Technology Officer (CTO) of the startup Cyberguard. He also teaches courses and masters in ethical hacking, pentesting and PowerShell for high-level organizations and universities. Creator of the blog darkbyte.net and speaker at renowned national and international conferences, such as Black Hat USA (2020/2021) and Black Hat Europe (2022). Programmer of hacking tools in his spare time, he has developed tools of all kinds, such as: AutoRDPwn, Cloudtopolis, EvilnoVNC, Invoke-DNSteal, PyShell or PSRansom among others.
Audience — Offense & Social Engineering.
https://forum.defcon.org/node/246315
HardHat Command & Control Framework
Saturday August 12, 2:00pm–3:55pm, Committee Boardroom, Forum
HardHat is a multi-platform, multi-user, .NET command and control framework written in C# designed to aid in red team operations and penetration testing. HardHat aims to improve the quality-of-life of operators by providing an easy-to-use but formidable C2 framework by incorporating robust features, ease of data access, and modern UI upgrades to a high-level language that is easily extensible.
Jonathan Owens is a red team operator on the Adversary Simulation team at SpecterOps, where he conducts advanced offensive engagements, such as red teaming exercises, penetration tests, and tool creation. He enjoys C# development and learning new programming languages with a specific focus on command & control framework and agent development. He maintains a tool repo at https://github.com/dragoqcc.
Audience — Offensive
ICS Forensics Tool
Saturday August 12, 2:00pm–3:55pm, Society Boardroom, Forum
Microsoft ICS Forensics Tools is an open source forensic toolkit for analyzing Industrial PLC metadata and project files. Microsoft ICS Forensics Tools enables investigators to identify suspicious artifacts on ICS environment for detection of compromised devices during incident response or manual check. Microsoft ICS Forensics Tools is open source, which allows investigators to verify the actions of the tool or customize it to specific needs, currently support Siemens S7 via Snap7.
Maayan Shaul is a Malware Analyst and Security Researcher in Section52 at Microsoft Defender for IoT (formerly CyberX). Experienced in the fields of malware analysis, reverse engineering and the IoT/OT landscape.
Ori Perez is a Malware Analyst and Reverse Engineer with vast experience in dealing with Nation-sponsored cyber attacks as an ex-officer at the IDF’s CERT. Ori is manager at Microsoft Defender for IoT research team (formerly CyberX) and research IoT/OT protocol research for IoT/OT tools .
Audience — Defense, forensics folks, ICS/OT enthusiastic
https://forum.defcon.org/node/246355
Kraken, a modular multi-language webshell for defense evasion
Saturday August 12, 12:00pm–1:55pm, Society Boardroom, Forum
Kraken is a modular multi-language webshell focused on web post-exploitation and defense evasion. It supports three technologies (PHP, JSP and ASPX) and its core is developed in Python. Kraken follows the principle of “avoiding command execution” by re-implementing it through the functionalities of the programming language in use. Kraken seeks to provide usability, scalability and improve the OPSEC of ongoing operations.
Raul Caro Teixido (OSCP, CRTE) is an Offensive Security Engineer at Telefonica Tech. He is the co-author of Mistica (your friendly data smuggler) presented in BlackHat Arsenal USA 2020, and the creator of Kraken (a modular multi-language webshell).
Audience — offensive (red team) and defensive (blue team and threat hunting) profiles
https://forum.defcon.org/node/246335
Lambda Looter
Saturday August 12, 10:00am–11:55am, Accord Boardroom, Forum
Organizations can have thousands of lines of code that are stored in Lambda on AWS. This application was built to help reduce the amount of time it takes to review that code. On our last Pen Test, we had so much Lambda code to review it was impossible to parse through all of it in the short amount of time assigned to our test. This lack of time created a necessity to automate the review of that lambda code for secrets. Lambda Looter will take a list of profiles and scan through them and download the code you have access to and then process that code for secrets, outputting any potential secrets to a loot directory. Even though this tool can generate a number of false positives it makes looking for secrets much faster than scanning the code manually.
Doug Kent has worked at State Farm for about 20 years. Working on mostly security technologies ranging from Active Directory, PKI, Endpoint protection and finally landing recently on the Pen Testing team. Doug has a passion for identifying vulnerabilities and partnering with control solution teams to protect State Farm data and fulfill our promise to customers. He strives to help others with offensive security skills by providing training, guidance, and kill chain demonstrations.
Rob Ditmer has been on the State Farm PenTesting Team for 2 years. Prior to his time at State Farm, he has worked with various other companies as a penetration testing consultant — enabling him to experience a wide range of technologies and their differing implementations. Rob enjoys the challenge of developing tools and infrastructure to better the skills and abilities of the PenTesting team, ultimately to better the protections around State Farm data.
Audience — Penetration Testers, Red Teamers, AWS Admins, AWS Developers, Threat Hunters
https://forum.defcon.org/node/246323
OWASP crAPI: Completely Ridiculous API
Friday August 11, 2:00pm–3:55pm, Accord Boardroom, Forum
OWASP crAPI is an intentionally vulnerable API designed to teach and demonstrate common API security flaws. It serves as a playground for security enthusiasts, developers, and penetration testers to learn about API vulnerabilities and practice exploiting them in a safe environment. This Demo Lab will showcase the use of crAPI for educational purposes, including how to set it up, identify vulnerabilities, and apply secure API development best practices.
Jayesh Ahire is a passionate security professional and open-source contributor with a strong background in application and API security. They have experience working with numerous organizations to design and implement secure API architectures and integrate security practices into their development processes. Jayesh has been actively involved in the OWASP community and enjoys sharing their knowledge through presentations, workshops, and mentorship.
Roshan Piyush is Security Research Engineer, solving API Security using the powers of Machine Learning and Distributed Tracing. He has 8+ years of research experience mainly focusing on API Security for the last 5+ years. He loves building security stacks, tools, and solutions. He is also a core member of the Owasp Coraza WAF team and a leader of the Owasp crAPI project.
Audience — Offense, Defense, AppSec, and Mobile
https://forum.defcon.org/node/246163
Red Wizard: user-friendly Red Teaming infrastructure
Saturday August 12, 12:00pm–1:55pm, Committee Boardroom, Forum
In this demo I will introduce our new open-source tool called Red Wizard. Red Wizard is the result of years of spinning up repeatable infrastructures for Red Teaming operations. It automates a comprehensive infrastructure deployment with redirectors, backend systems, phishing relays, OSINT machines etcetera. But made easy by providing wizards that walk you through the deployments. Additionally, the infrastructure is self-documenting, making the sharing of all relevant details to your team of operators a breeze. The tool is build to make sure to provide you with a resilient setup that is OPSEC-safe. By retrieving all critical key material from the deployed servers, you will be able to rebuild and keep receiving your shells even if one of your servers crashes and burns. The technology used for Red Wizard is mainly based on Ansible and Docker.
Ben, Secura’s Red Teaming lead, has more than 9 years of experience in the field. With a strong passion for Social Engineering, he enjoys employing initial access techniques and has played a pivotal role in creating Secura’s user friendly and OPSEC-safe Red Teaming infrastructure. In addition to his Red Teaming responsibilities, Ben also serves as a trainer for various courses and frequently shares his expertise as a public speaker at conferences. Having gained invaluable knowledge from the infosec community, he now aims to contribute back by open sourcing a number of tools and delivering presentations at conferences.
Audience — Offense, Red Teamers, Penetration testers, Social Engineers
https://forum.defcon.org/node/246333
RuleProcessorY & Gramify — Rule Optimization & Password Analysis tools
Saturday August 12, 2:00pm–3:55pm, Caucus Boardroom, Forum
The RuleProcessorY and Gramify tools are new tools that support password-cracking efforts. RuleProcessorY offers a method of optimizing hashcat rule-files so that you can prevent duplicates across multiple attacks better, leading to a shorter runtime. Additionally it can process rules as hashcat would with an additional support for multi-byte/multi-character rules (inserts & replace primarily). Gramify offers an easy method to create base words and candidates to utilize with wordlist and combination attacks by splitting data by words, characters, or character-set. This can help with password phrases, quotes, sentences, combinator attacks, and extracting base-words from passwordlists.
Working as Pentester Niels Loozekoot has an extensive background in the security field. Niels has a background in web-development and knows his way around C, C++, C#, and Python and is active in the password cracking/research communities of Hashcat, Hashkiller, and HashMob. Winning in the CrackTheCon password cracking contest, and achieving 3rd place in both the CrackMeIfYouCan 2021 & 2022.
Audience — Offense
https://forum.defcon.org/node/246347
Shufflecake, AKA Truecrypt on Steroids for Linux
TBA
Shufflecake is a tool for Linux that allows to create multiple hidden volumes on a storage device in such a way that it is very difficult, even under forensic inspection, to prove the existence of such volumes. This is useful for people whose freedom of expression is threatened by repressive authorities or dangerous criminal organizations, in particular: whistleblowers, investigative journalists, and activists for human rights in oppressive regimes. You can consider Shufflecake a “spiritual successor” of tools such as TrueCrypt and VeraCrypt, but vastly improved: it works natively on Linux, it supports any filesystem of choice, and can manage multiple nested volumes per device, so to make deniability of the existence of these partitions really plausible.
In Shufflecake, each hidden volume is encrypted with a different secret key, scrambled across the empty space of an underlying existing storage medium, and indistinguishable from random noise when not decrypted. Even if the presence of the Shufflecake software itself cannot be hidden — and hence the presence of secret volumes is suspected — the number of volumes is also hidden. This allows a user to create a hierarchy of plausible deniability, where “most hidden” secret volumes are buried under “less hidden” decoy volumes, whose passwords can be surrendered under pressure. In other words, a user can plausibly “lie” to a coercive adversary about the existence of hidden data, by providing a password that unlocks “decoy” data. Every volume can be managed independently as a virtual block device, i.e. partitioned, formatted with any filesystem of choice, and mounted and dismounted like a normal disc. The whole system is very fast, with only a minor slowdown in I/O throughput compared to a bare LUKS-encrypted disk, and with negligible waste of memory and disc space.
Shufflecake is FLOSS (Free/Libre, Open Source Software). Source code is available in the install section and released under the GNU General Public License v2.0 or superior.
https://forum.defcon.org/node/246518
USBvalve — Expose USB activity on the fly
Saturday August 12, 10:00am–11:55am, Unity Boardroom, Forum
USB spreading malware is still a concern today. Over the past few months, we have witnessed an increase in malicious software exploiting USB drives to bypass security measures, even in air-gapped systems. Whenever we connect our USB drive to an “untrusted” system, numerous doubts arise: what happens behind the scenes? Is something accessing, modifying, or encrypting our files? This is where USBvalve comes in. It is an affordable dongle, built using readily available hardware, designed to reveal the true activities occurring when a USB drive is connected to a system. It can also be used to check for “BADUSB” (HID) on USB keys before inserting them into our own systems. The best part is that it’s as compact as a keychain, making it convenient to carry with us at all times!
Cesare Pizzi is a Security Researcher, Analyst, and Technology Enthusiast at Sorint.lab. He develops software and hardware, and tries to share this with the community. Mainly focused on low level programming, he developed a lot of OpenSource software, sometimes hardware related and sometimes not. Doing a lot of reverse engineering too. He likes to share his job when possible (at Defcon, Insomni’hack, Nullcon. etc). Contributor of several OS Security project (Volatility, OpenCanary, PersistenceSniper, Speakeasy, CETUS, etc) and CTF player.
Audience — Malware analysts, Digital Forensic investigator, Security Practitioners
https://forum.defcon.org/node/246327
Vacuum Robot Hacking
Friday August 11, 2:00pm–3:55pm, Unity Boardroom, Forum
In this demo I will show you can root various models of vacuum robots and disconnect them from the cloud. You have the chance to play around yourself with the tools and the rooted robots yourself. Learn why you should not trust your robots cameras and microphones. Pick up a free PCB that allows you to root your vacuum robot easily.
Dennis Giese is currently a PhD student at Northeastern University and focuses on the security and privacy of IoT devices. While being interested in physical security and lockpicking, he enjoys applied research and reverse engineering malware and all kinds of devices. His most known projects are the documentation and hacking of various vacuum robots. His current vacuum robot army consists of over 45 different models from various vendors.
Audience — hardware tinkerers and users of vacuum robots
https://forum.defcon.org/node/246219
Vulnerable by Design:Unguard,The Insecure Cloud-Native Twitter Clone
Friday August 11, 10:00am–11:55am, Accord Boardroom, Forum
Unguard is an intentionally insecure, cloud-native microservices demo application that serves as a playground for cybersecurity enthusiasts to sharpen their skills and for cybersecurity companies to test their software. Designed to mimic a web-based Twitter clone, the platform offers user registration, login, content posting, and social interactions, all with a wide variety of exploitable vulnerabilities. Featuring a wide range of security flaws, including SSRF, Command/SQL Injection, Log4Shell, and Spring4Shell, Unguard challenges security professionals, developers, and students to identify, exploit, and understand these weaknesses. Simultaneously, the platform showcases deceptive elements, such as phony ads and profile management options, which further enhance the real-world experience offered by the demo.
Simon’s Ammer interest in cybersecurity was sparked after listening to the Darknet Diaries podcast, which led him to pursue a career in this fascinating field. He studied Software Engineering and Mobile Computing in Austria, focusing on enhancing web vulnerability scanner reports for his Master’s thesis. Driven by his passion for cybersecurity, Simon decided to further expand his knowledge by enrolling in another Master’s program specializing in Artificial Intelligence. Currently, he holds the position of Research Software Engineer in the cloud-native security team at Dynatrace. There, he leverages his knowledge to employ AI to improve security measures and safeguard digital infrastructures.
Christoph Wedenig always loved to interact with software systems, even more so in unintended ways. He studied Applied Computer Science in the south of Austria, focusing on the detection of server-side request forgery in his Master’s thesis. As a demo environment for this thesis, he created a small distributed application called “Vogelgrippe” which was then later extended for various other use cases until being renamed to Unguard and finally gifted to the community as an Open-Source playground. Currently, he is working in the Application security team at Dynatrace, where he helps build a wide suite of security-related software.
Audience — Offense, Defense
https://forum.defcon.org/node/246023

DEF CON 31 Trainings
When: Monday, August 14th — Tuesday, August 15th
Where: Ceaser’s Ballroom, 9am — 5pm PST
Website: https://training.defcon.org/pages/def-con-trainings-las-vegas-august-2023
Code Of Conduct: https://training.defcon.org/pages/code-of-conduct
DEF CON has been the world’s most influential hacker con for thirty-one years. They work hard to bring interesting, technically rich and actionable information to our community through our speaker tracks, our hands-on Villages, our Workshops and our Demo Labs.
This year they’re bringing back the DEF CON Paid Trainings — intensive, two-day courses of study with world-class instructors aimed at building specific skills. In some cases, these courses will carry a certification.
DEF CON Training is for everyone who wants to hone their skills in a challenging, fast-paced environment with instructors who know their subject down to the metal. It’s the two days after DEF CON, and those two days could change everything
Check out https://defcontrainings.myshopify.com/ to peruse training offerings and to and purchase training tickets!
DCG 201 DEFCON 31 TRAINING HIGHLIGHTS
The SecOps Group — Certified Pentester (CPen) MONDAY ONLY — $1,050 (early bird)
Certified Pentester (CPen) at DEF CON Training 2023
Sign-Up:
Monday: https://training.defcon.org/products/monday-certified-pentester-cpen
Tuesday: https://training.defcon.org/products/tuesday-certified-pentester-cpen-tuesday-only
Defcon has been an industry leader in providing and facilitating cutting edge security research and training for over three decades. Driven by innovation and research, the annual conferences provide attendees various avenues to learn and progress in the different sectors of information security. This year, in partnership with The SecOps Group (https://secops.group/), Defcon is pleased to announce a certification track to allow attendees (and their employers) to validate their skills which in turn will enable them to progress their career.

What is Certified Pentester (CPen) Exam?
The Certified Pentester (CPen) is an intermediate level exam, intended to be taken by professional pentesters, bug-bounty hunters, red and blue team experts, SOC analysts and anyone wanting to evaluate or appraise their existing knowledge in topics involving hands-on pentesting. This practical exam covers a wide variety of topics and in order to successfully complete each section, attendees will have to obtain flags associated with every topic.
The pass criteria is as following:
- Attendees scoring over 60% marks will be deemed to have successfully passed the exam.
- Attendees scoring over 75% marks will be deemed to have passed with merit.
How long is the exam?
The exam will be for 7 hours (9 am to 5pm). However, an hour of lunch break can be taken during the exam. The exam can be taken on any one of the following two days:
- Monday, August 14th, 2023 (in-person exam to be held at Caesars Forum, Las Vegas, NV)
What topics are covered?
The exam will cover the following topics of pentesting:
- Web Hacking (50%) — 3.5 hours (210 mins); 210 Marks*
- Infrastructure Hacking (50%) — 3.5 hours (210 mins); 210 Marks*
The complete list of topics can be found in the exam syllabus section below.
*Note:
The marks allocated for every question also indicates the time that an attendee is expected to spend in solving a question. For e.g. a question worth 30 marks, will require roughly 30 minutes, for it to be solved.
What is the format of the exam?
The exam will be a Capture The Flag (CTF) style Hackathon. It will be a full day event requiring attendees to capture flags as they go on identifying and exploiting various system vulnerabilities and score points, after submitting the flags and answering the associated questions.
What is the experience needed to take the certification and what level of difficulty can be expected from the exam?
We recommend a minimum of 2 years of professional penetration testing/bug bounty experience before taking this exam.
In terms of difficulty, on the scale of beginner, intermediate and advanced, this exam has been rated as intermediate. The exam tests attendees’ practical knowledge in identifying and exploiting vulnerabilities in real life pentesting scenarios.
To explain this a bit more, we expect attendees to be able to identify and exploit vulnerabilities such as SQL Injection and obtain relevant flags, however, we are not testing them on advanced web hacking concepts such as that of Second-order SQL Injection, within this exam. Similarly, to cite another example for infrastructure hacking, attendees are expected to use common hacking tools and techniques to demonstrate how to compromise a Windows Active Directory infrastructure, but they are not expected to write custom exploits, use or create 0-day exploits or perform reverse engineering etc.
Can I participate with my friends and colleagues as a team?
One can only participate in an individual capacity (i.e. teamwork is not allowed).
What tools/laptop do I need to bring?
Attendees must use their own laptop and can use hacking tools of their choice. Internet access will be available during the course of the exam but no assistance will be provided with regards to installation/configuration of any tools. The hacking challenges can be solved using freely available tools and scripts.
What will attendees get?
Each attendee will receive:
A certificate of participation. The certificate will mention pass/fail and merit status. In addition to this, attendees will be able to download a PDF report, which will have detailed scores for each section of the exam, allowing them to identify and focus on areas of improvement for future qualification and training.
Will you provide any training that can be taken prior to the certification?
Being an independent certifying authority, we (The SecOps Group) do not provide any training for the exam. Attendees should carefully go over each topic listed in the syllabus and make sure they have adequate understanding, required experience and practical knowledge of these topics.
What is the exam retake policy?
Candidates who fail the exam must purchase a new exam voucher for every attempt.
How long is the certificate valid for?
The certification does not have an expiration date. However, the passing certificate will mention the details of the exam such as the exam version and the date. As the exam is updated over time, candidates should retake the newer version as per their convenience.
What is the exam syllabus?
The exam syllabus is listed below:
Web Hacking
- Google Hacking, Dorking and OSINT Techniques.
- Identification and Exploitation of OWASP Top 10 Vulnerabilities
- Cross-Site Scripting
- SQL Injection
- XML External Entity attack
- Cross-Site Request Forgery
- Practical Cryptographic Attacks
- Authentication related Vulnerabilities
- Brute force Attacks
- Username Enumeration
- TLS Security
- Identification of TLS security Misconfigurations.
- Server-Side Request Forgery
- Authorization and Session Management related Flaws
- Insecure File Uploads
- Code Injection Vulnerabilities
- Business Logic Flaws
- Directory Traversal Vulnerabilities
- Common Security Misconfigurations.
- Information Disclosure.
- Vulnerable and Outdated Components.
- Common Security Weaknesses affecting Cloud Services such as a S3 Bucket.
- Security Best Practices and Hardening Mechanisms.
Infrastructure Hacking
- Common OSINT Techniques
- Network Mapping and Target Identification
- Brute-force Attacks.
- Vulnerability Identification and Exploitation using Common Hacking Tools.
- Application Server Flaws.
- Insecure Protocols
- *nix Vulnerabilities.
- Insecure File permissions.
- Security Misconfigurations Leading to Privilege Escalation Attacks.
- Windows Active Directory Attacks.
- OS Credential Dumping and Replay.
- Kerberoasting; golden and silver tickets.
- Password Attacks and Password Cracking.
- Administrative Shares Exploitation
- Persistence Techniques
- Lateral Movements
- Cloud Enumeration
- Abusing Serverless Services
- Abusing API Token and Cloud Credentials
- Vulnerability chaining
- Common security misconfigurations allowing docker escape.
About: The SecOps Group
The SecOps Group (https://secops.group) is a globally recognized IT security company having vast experience of providing cyber security consultancy and education services. At The SecOps Group, we believe that security is a continuous process, which has to progress with time and in accordance with the customer needs and constantly evolving threats. Our core business comprises of two units:
1. Consultancy:
Pentesting and Advisory
The SecOps Group are cybersecurity experts offering CREST accredited security consultancy services.
2. Education:
Cyber Security Certifications
Through our exams, we provide an authentic and credible certification program that is modern, relevant and represents real life business risks.
Vulnmachines (A Pentest Learning Platform)
The SecOps Group runs a free pentest learning platform called “Vulnmachines” (www.vulnmachines.com).
DATE: August 14th 2023
TIME: 8am to 5pm PDT
VENUE: Caesars Forum, Las Vegas, NV
TRAINER: Sumit Siddharth
- 2 coffee breaks are provided per day
- Note: Food is not included
Registration terms and conditions:
Trainings and Certifications are refundable before July 1st, the processing fee is $250.
Trainings and Certifications are non-refundable after July 10th, 2023.
Training and Certification tickets may be transferred. Please email us for specifics.
Failure to attend the Training or Certification without prior written notification, will be considered a No-Show. No refund will be given.
By purchasing this ticket you agree to abide by the DCT Code of Conduct and the registration terms and conditions listed above.
Ben Sadeghipour — Hacking Organizations: Phishing Not Required $1,500
Sign-Up: https://training.defcon.org/products/ben-sadeghipour-hacking-organizations-phishing-not-required
Description:
Teach students how to identify vulnerabilities in web applications and digital assets from an external perspective.
Training description:
“Hacking Organizations: Phishing Not Required” is a comprehensive course designed to teach students how to identify vulnerabilities in web applications and digital assets from an external perspective. The first two days of the course is cover the ten most common vulnerabilities found in web applications as well as principles of reconnaissance. On the third day, students will apply these skills to develop a technique for identifying impactful vulnerabilities that potentially allow access to an organization’s internal infrastructure. This training is appropriate for anyone interested in web application penetration testing, bug bounties, or joining a red team with a web and reconnaissance focus.
Past content:
https://hackfest.ca/en/trainings/web/
https://appsecus2018.sched.com/event/EyjH/3-day-training-hacking-your-organization-one-step-at-a-time
Trainer(s) bio:
Ben Sadeghipour, also known as NahamSec, is a hacker, content creator, trainer, public speaker, and conference organizer. He has extensive experience in ethical hacking and bug bounty hunting, having identified and exploited thousands of security vulnerabilities for companies such as Apple, Yahoo, Google, Airbnb, Snapchat, the US Department of Defense, and Yelp. Sadeghipour was formerly the head of Hacker Education at HackerOne. In addition to his professional pursuits, Sadeghipour also creates content on YouTube and Twitch to help others get into ethical hacking, bug bounty, web hacking and reconnaissance.
Trainer(s) social media links:
https://twitter.com/NahamSec
https://youtube.com/NahamSec
Outline:
Day 1:
Burp Suite Basics
HTTP Basic Refresher
Request Types
Headers
Respond Codes
Status Codes
Open Redirects + Labs
Whitelisting
Blacklisting
Basics of open redirects
Cross-Site Scripting (XSS) + Lab Reflected Cross-Site Scripting Stored Cross-Site Scripting Dom Cross-Site Scripting
Blind XSS Break
Cross Site Request forgery (CSRF) + Lab No CSRF token Reusable CSRF token
Insecure Direct Object References (IDOR) + Lab Incrementing IDs Weak encryption (B64) UUID from other vulnerabilities
Local file Read & Path Traversal + Lab
Path Traversal Basics
Local File read
Path traversal bypasses
Advanced Path Traversal and local file read
Server-Side Request Forgery (SSRF) + Lab
Understanding SSRF + Protocols
Local File Read
Blind SSRF and Port Scan
Accessing Local Network via SSRf
White Listing and Black Listing
Exploiting PDF Generators and Similar
Day 2:
Privilege Escalation + Lab
Understanding user roles
Priv Esc through IDOR
Priv Esc via password brute force
Elevating user access roles
Arbitrary file upload + Lab
Unvalidated upload (php, asp, etc)
Path Traversal in uploaders
XML external entity (XXE) + Lab
Basics of XXE XXE in excel, docx, etc
XXE in PDF Generators
Remote Command / Code Execution
Understanding RCE
RCE via file uploads
Remote Command Injection in URL parsing
Weak or default credentials
Weak or default credential Basics
Wordlists
Looking through previous password dumps
Default Credentials
Password Guessing
Components with Known Vulnerabilities
SSRF
RCE via known vulnerabilities
Image Magick
Tomcat
Struts2
Shellshock
log4j
Reconnaissance — Asset Discovery + Hands on demo
DNS Basics
ASN Ranges (Cloud vs in house)
Subdomain Brute Forcing
Certificate Transparency
3rd Party tools (Shodan, Censys, etc)
Permutation and Environments
Automation Demo
Reconnaissance — Content Discovery + Lab
Creating and maintaining word list
Contextualizing directory/file brute forcing
Port scanning
Information gathering using https
Approaching APIs
Leveraging search engines for reconnaissance
Google Dorking
Leaked credentials
Finding additional information about your target
Methodology
Understanding company infrastructure
Identifying and prioritizing interesting assets
Combining asset discovery and content discovery
Looking for leads (documentation, API specs, etc)
Looking for patterns of mistake across an infrastructure
DNS Misconfigurations (subdomain or DNS takeover)
Understanding SSO
SSO Bypass or priv escalation
Final Lab + Test
Technical difficulty:
Beginner to intermediate
Suggested Prerequisites:
While this training will offer and cover the foundations of web application hacking, it is highly suggested that students have a solid foundation in web application hacking and in web development.
HTTP Basics:
https://developer.mozilla.org/en-US/docs/Web/HTTP
How to set up burp suite:
https://portswigger.net/burp/documentation/desktop/getting-started/download-and-install
Understanding DNS:
https://www.cloudflare.com/learning/dns/what-is-dns
What students should bring:
Students should bring in a laptop (Mac OS, Windows, or a Linux distribution of your choice) with a working browser. Please make sure you have installed Burp Suite and are able to intercept your browsers traffic.
DATE: August 14th-15th 2023
TIME: 8am to 5pm PDT
VENUE: Caesars Forum, Las Vegas, NV
TRAINER: Ben Sadeghipour
- 16 hours of training with a certificate of completion.
- 2 coffee breaks are provided per day
- Note: Food is not included
Registration terms and conditions:
Trainings are refundable before July 1st, the processing fee is $250.
Trainings are non-refundable after July 10th, 2023.
Training tickets may be transferred. Please email us for specifics.
Failure to attend the Training without prior written notification, will be considered a No-Show. No refund will be given.
By purchasing this ticket you agree to abide by the DCT Code of Conduct and the registration terms and conditions listed above.
Jayson E. Street — Simulated Adversary — Tactics & Tools Training $2,400
Name of Training:
Simulated Adversary — Tactics & Tools Training
Description:
Attendees will learn how adversaries can attack in non-traditional ways.
Training description:
This class covers all aspects of an engagement, starting with online
research in a quick and efficient manner. Attendees will learn how
adversaries can attack in non-traditional ways. Jayson’s style focuses on
education over compromise by helping show how to move past finding
vulnerabilities into educating and improving the security of the target. The
emphasis for this class will be hands-on, real-world examples and
demonstrations that help companies understand the human side of social
engineering attacks.
Traditional pentest focuses on exposing vulnerabilities and showing how they
can be exploited. A Red Team engagement does a more in-depth simulation of
an advanced targeted attack with once again focusing on not just discovering
potential weaknesses in the target’s defenses but giving proof of concepts
showing they can be exploited. Jayson has created the Security Awareness
Engagement methodology for a way to show real world threats without actually
compromising or exploiting discovered vulnerabilities in a way that might
negatively impact the company. Instead simulations use non-intrusive
demonstrations that work in tandem with direct and immediate education of
Through the use of hands-on, real-world examples and demonstrations. This
class will go beyond Metasploit, popping shells and zero day exploits,
focusing on the most considerable threat a company faces, the human factor.
This class is not just for pentesters but also for security teams who want
to educate their employees. Class activities will introduce students to real
world simulations of how Social Engineering and Physical Compromise attacks
occur. Students will also participate in simulations where they use the
results from their labs to execute the attack, an attack with Jayson playing
the roles of the target to compromise.
Trainer(s) bio:
Jayson E. Street referred to in the past as:
A “notorious hacker” by FOX25 Boston, “World Class Hacker” by National
Geographic Breakthrough Series and described as a “paunchy hacker” by
Rolling Stone Magazine. He however prefers if people refer to him simply as
a Hacker, Helper & Human.
The Chief Chaos Officer of Truesec a global cybersecurity solutions
provider. The author of the “Dissecting the hack: Series” (which is
currently required reading at 5 colleges in 3 countries that he knows of).
Also the DEF CON Groups Global Ambassador. He’s spoken at DEF CON, DEF CON
China, GRRCon, SAINTCON & at several other CONs & colleges on a variety of
Information Security subjects. He was also a guest lecturer for the Beijing
Institute of Technology for 10 years.
He loves to explore the world & networks as much as he can. He has
successfully robbed banks, hotels, government facilities, Biochemical
companies, etc.. on five continents (Only successfully robbing the wrong
bank in Lebanon once all others he was supposed to)!
*He is a highly carbonated speaker who has partaken of Pizza from Bulgaria
to Brazil & China to The Canary Islands. He does not expect anybody to still
be reading this far but if they are please note he was proud to be chosen as
one of Time’s persons of the year for 2006.
Trainer(s) social media links:
https://twitter.com/jaysonstreet : @jaysonstreet
https://defcon.social/@jayson : @defcon.social/@jayson
https://infosec.exchange/@jaysonestreet : @infosec.exchange/@jaysonestreet
https://linkedin.com/in/jstreet/
JaysonEStreet.com & HackerAdventures.World
Outline:
Day 1:
Introduction
Agenda
Differences
Who am I
Who are we
Current State of security awareness
Module 1
What is Social Engineering
Red Teaming or Physical Pentest
The human factor
Module 2 Recon
Recon online
Recon in real life
Presenting findings
Case study
Lab: Conducting your own recon
Module 3 Phishing
Phishing for results
Finding target
Impersonation
Finding emotional trigger
Case study
Lab: Constructing a phish using results from Module
Module 4: Importance of preparedness
Preparing for onsite engagement
Clarifying scope of work
Managing client expectations
Defining success
Get out of jail free card
Case Study
Lab: ‘Creating’ a “Get out of jail free” card
Module 5 Weapons of Mass Education & Learning to code in Ducky script
An overview of the tools such as Bash Bunny, Pineapple, OMG cables & rubber
ducky, Flipper Zero & other useful devices.
Purpose of these tools
Each student will be given a book on programming in Ducky script.
We will go over several chapters that I will teach from. This will give
students the understanding and ability to write their own beginner payloads
for the Rubber Ducky.
Case study
Day 2:
Lab: Configuring the Rubber Ducky
Module 6 Infiltration of the Location
Persona creation
Passive infiltration
Assertive infiltration
Location infiltration
Commitment to your persona
Location
Time of attack
Population onsite
Lab: Creating your persona for your scenario
Module 7 Execution Phase
The attack
The approach
The target
Deployment
The escape
Case Study
Lab: Setting the stage and acting it out
Module 8 What’s next?
The aftermath
Dealing with compromised humans
Educating on the spot
Conveying the lessons to management
Covering the findings in a positive way
Case Study
Lab 7: Consoling and educating the compromised
Closing
Technical difficulty:
Beginners to start. Intermediate & advanced students to learn new techniques.
Suggested Prerequisites:
None
What students should bring:
A laptop and a desire to learn! A Hak5 Rubber Ducky will be provided for all
students.
DATE: August 14th-15th 2023
TIME: 8am to 5pm PDT
VENUE: Caesars Forum, Las Vegas, NV
TRAINER: Jayson E. Street
- 16 hours of training with a certificate of completion.
- Note: Classes that do not meet their minimum class size by July 15 will be canceled, please register early
- 2 coffee breaks are provided per day
- Note: Food is not included
Registration terms and conditions:
Trainings are refundable before July 1st, the processing fee is $250.
Trainings are non-refundable after July 10th, 2023.
Training tickets may be transferred. Please email us for specifics.
Failure to attend the Training without prior written notification, will be considered a No-Show. No refund will be given.
By purchasing this ticket you agree to abide by the DCT Code of Conduct and the registration terms and conditions listed above.
Offensive IoT Exploitation
Sign-Up: https://training.defcon.org/products/offensive-iot-exploitation
Class Description
As IoT becomes more integrated and integral into personal and work lives, there is a growing need to understand the inner workings of IoT devices and ensure these devices are secure. This course teaches security professionals and hackers how to identify and exploit security vulnerabilities in IoT devices. Participants will learn to interact with hardware debug capabilities, communicate with memory devices, and virtualize and analyze firmware. The course also covers various hardware attacks including glitching and side channel attacks, as well as diving into communications protocols, including Bluetooth, Zigbee, Thread and Matter. Participants will gain hands-on experience with industry tools and techniques. This course is suitable for security professionals, penetration testers, and hackers with basic programming and computer system knowledge, and equips them with skills to discover new vulnerabilities in IoT devices.
Course Outline
The course is broken down into the following sections:
- Introduction to IoT and Embedded Device Hacking
- Overview of devices & device architectures
- What is firmware?
- Introduction to digital signals analysis
- Interacting with Hardware Debugging Interfaces
- Overview of hardware debugging interfaces
- UART
- JTAG
- Using UART and JTAG to debug or extract firmware from devices
- Analyzing Firmware for Security Vulnerabilities
- Extracting firmware from binary files
- Tools for analyzing firmware, including disassemblers and debuggers
- Overview of common vulnerabilities found in IoT
- Where to look for vulnerabilities
- Reverse engineering firmware
- Identifying security vulnerabilities using code analysis and fuzzing
- Communicating with Memory Devices
- Overview of memory devices commonly used in IoT systems, such as flash memory, EEPROM, and SD cards
- Communicating with common memory devices
- SPI Flash
- eMMC
- Challenges encountered when communicating with memory devices
- Glitching and Side Channel Attacks
- Overview of glitching and side channel attacks
- Identifying vulnerabilities through glitching and side channel attacks
- Tools for performing glitching and side channel attacks
- Virtualizing Firmware
- Overview of firmware virtualization
- Reasons for virtualizing firmware
- Techniques for virtualizing firmware, such as emulators and hypervisors
- Advantages and disadvantages of firmware virtualization
- Communications Protocols in Embedded Systems
- Overview of communications protocols commonly used in IoT systems, such as Bluetooth, and Zigbee, Thread and Matter
- Overview of application protocols such as MQTT and UPnP
- Analyzing and reverse engineering communications protocols
- Tools and techniques for sniffing and spoofing communications protocols
Trevor Hough
Trevor Hough is a partner and passionate security researcher at Loudmouth Security. With extensive experience participating in large-scale cyber training operations involving embedded systems, Trevor has become a recognized expert in his field. He has an insatiable curiosity and has performed research on some of the weirdest and coolest embedded systems around, discovering and disclosing bugs in the process.
Trevor has a deep technical knowledge and passion for security that’s evident in his work. He won a Black Badge in the IoT CTF at DEF CON 26 and has been a regular contributor to DEF CON ever since. Trevor is part of the team that’s bringing the new Embedded Systems Village to DEF CON 31, where he’s excited to push the envelope of bigger, cooler, and more exotic systems that attendees can interact with. He is a highly skilled trainer who’s always eager to share his knowledge and experience with others.
Nicholas Coad
Nicholas is a consultant at Loudmouth Security and an accomplished PCB designer with extensive knowledge of hardware. He brings his expertise to our training team, where he’s an invaluable asset. Nicholas is also a regular contributor to IoT Village and part of the team behind the new Embedded Systems Village.
Prior to joining Loudmouth Security, Nicholas worked as an IT administrator for industrial and manufacturing companies, where he gained invaluable experience about the practical applications of embedded systems. This hands-on experience gives him a unique perspective that he brings to this training.
Nicholas is an exceptional trainer with a passion for sharing his knowledge and experience with others. He’s a key member of our team, and his expertise in PCB design and embedded systems makes him an invaluable resource to our students.
Patrick Ross
Patrick is a seasoned security expert with a wealth of experience in the field. As a member of the team that won the Black Badge at DEF CON 26 in the IoT CTF, Patrick is recognized as one of the top experts in his field. He’s also a DEF CON goon and an integral part of the team behind the new Embedded Systems Village.
Patrick’s expertise lies in the virtualization of embedded devices, and he’s one of the key researchers behind the MIPS-X project. His deep technical knowledge and experience make him a valuable asset to Loudmouth Security’s training team.
In addition to his technical skills, Patrick is an exceptional teacher with superb teaching skills. He’s passionate about sharing his knowledge and experience with others, and he’s committed to helping organizations stay ahead of the latest cyber threats.
Trainer(s) social media links: Trevor Stevado & Trevor Hough
Class Break Down
Day 1Day 20800Intro to IoT and Embedded DevicesCommunicating with Memory DevicesInteracting with Hardware Debugging InterfacesGlitching and Side Channel AttacksVirtualizing Firmware1200Lunch1300Interacting with Hardware Debugging Interfaces (cont’d)Communications Protocols in Embedded SystemsAnalyzing Firmware for Security Vulnerabilities1800End of Day1hr Proficiency Test
Technical Difficulty of the class:
Beginner to Intermediate. This is a compressed course and will move quickly.
Students should have:
- A willingness and desire to learn
- Understanding of common networking protocols
- Basic familiarity of virtualization technologies
- Basic familiarity of Windows and Linux
- Basic understanding of penetration testing
Students should bring:
- Laptop with 16GB RAM and at least 50GB free disk space
- External ethernet adapter
- VMware Player/Workstation/Fusion installed
- Administrator/Root access to their host Operating
We believe firmly that you learn best from doing, which is why our course is jampacked with approximately 10 hands-on exercises throughout the 2 days of the course.
Many courses either scratch the surface of IoT or go very deep into specific topics. Our course strikes a balance between breadth and depth, giving the student a solid foundation from which to start researching IoT Security
We know our stuff — after winning the DEF CON black badge at DEF CON 26, we have been an integral part of the IoT Village both at DEF CON and other conferences throughout the world. Our team developed the IoT 101 Labs that had lineups out the door of IoT Village at DEF CON 27. We have contributed to the IoT CTF since DEF CON 27, but starting this year our team is launching a completely new DEF CON Village — Embedded Systems Village.
DATE: August 14th-15th 2023
TIME: 8am to 5pm PDT
VENUE: Caesars Forum, Las Vegas, NV
TRAINER: Trevor Stevado, Trevor Hough, Nicholas Coad, Patrick Ross
- 16 hours of training with a certificate of completion
- 2 coffee breaks are provided per day
- Note: Food is not included
Registration terms and conditions:
Trainings are refundable before July 1st, the processing fee is $250.
Trainings are non-refundable after July 10th, 2023.
Training tickets may be transferred. Please email us for specifics.
Failure to attend the Training without prior written notification, will be considered a No-Show. No refund will be given.
By purchasing this ticket you agree to abide by the DCT Code of Conduct and the registration terms and conditions listed above.
Web Hacking Bootcamp — Orange Cyberdefense $2,600
Sign-Up: https://training.defcon.org/products/web-hacking-bootcamp-orange-cyberdefense
Training + Certificate of Completion Training + Certificate of Proficiency
Name of Training:
Web Hacking Bootcamp
Description:
Most organisations utilise web applications. Due to the exposed nature of web applications and complex business logic they contain, they are a valuable target for attackers. Throughout this course focus will be placed on the various vulnerabilities that could affect web applications.
This course will teach you how to analyse web applications for vulnerabilities and teach you how to exploit them in order improve your understanding of the inner workings and the associated risks.
Practical exposure to hacking web application will provide developers a deeper understanding of the potential threats and issues that could find its way into the development lifecycle and furthermore ensure that penetration testers are well versed with the discovery and exploitation of web related issues.
Key Points:
* Greater understanding of the risks associated with web applications
* A good understanding of the tools and techniques for examining web applications
* Practical skills to exploit a wide variety of web application vulnerabilities
We have been conducting penetration tests against web applications for nearly two decades have pulled out the most relevant and fun hacks we could find into this course.
Come join us and hack hard!
Training outline:
Most organisations utilise web applications. Due to the exposed nature of web applications and complex business logic they contain, they are a valuable target for attackers. Throughout this course focus will be placed on the various vulnerabilities that could affect web applications.
This course will teach you how to analyse web applications for vulnerabilities and teach you how to exploit them in order improve your understanding of the inner workings and the associated risks.
Practical exposure to hacking web application will provide developers a deeper understanding of the potential threats and issues that could find its way into the development lifecycle and furthermore ensure that penetration testers are well versed with the discovery and exploitation of web related issues.
Key Points:
* Greater understanding of the risks associated with web applications
* A good understanding of the tools and techniques for examining web applications
* Practical skills to exploit a wide variety of web application vulnerabilities
We have been conducting penetration tests against web applications for nearly two decades have pulled out the most relevant and fun hacks we could find into this course.
Whether you’re a developer looking to better understand how to defend your applications or a penetration tester looking to enhance your web application bug hunting, this course is for you.
This course is highly practical, with a cornucopia different practical exercises. You’ll learn how to hand exploit numerous common web vulnerabilities, and understand the theory behind them. You will be better able to help developers prevent these classes of attacks in their applications. We aim to teach you the trade not just the tricks, and while tools are covered and help, you will be taught how to exploit many of these vulnerabilities by hand.
Details:
* 2-day course
* 60% practical and 40% theoretical
* Immersive practicals with a wide spread of coverage
* Delivered by active penetration testers
Topics covered:
* Web technology fundamentals
* Cookies and sessions abuse
* Web vulnerabilities and exploitation
* Enumeration
* File upload manipulations
* Injection based attacks
Our training facility is delivered via SensePost, the specialist pentesting arm of Orange Cyberdefense.
SensePost have trained thousands of students on the art of network and application exploitation for the past two decade. It’s safe to say we enjoy teaching others how to own networks and applications. Our courses are developed from the work we perform for clients, so that you get a better understanding of how to exploit real-world scenarios. As one of Blackhat briefings longstanding training partners since 2002, our courses have taught thousands of students about the art of offensive and defensive approaches.
Come join us and hack hard!
Trainer(s) bio:
Szymon Ziolkowski — @TH3_GOAT_FARM3R
Szymon Ziolkowski is an information security analyst at SensePost. Szymon went straight from university into hacking organizations and has been doing so for a few years. Whenever he presents internally, he often takes the opportunity to lobby for an office in Poland.
SensePost, an elite ethical hacking team of Orange Cyberdefense have been training internationally since 2002. We pride ourselves on ensuring our content, our training environment and trainers are all epic in every way possible. The trainers you will meet are working penetration testers, responsible for numerous tools, talks and 0day releases. This provides you with real experiences from the field along with actual practitioners who will be able to support you in a wide range of real-world security discussions. We have years of experience building environments and labs tailored for learning, after all education is at the core of SensePost and Orange Cyberdefense.
Past content:
A version of this course has been presented at BlackHat in 2022.
This course has been adjusted in 2023 to focus its delivery to be jam packed and a bit of a bootcamp course. Going from zero to hero in two-days.
Here is the 2022 web course details: https://www.blackhat.com/us-22/training/schedule/#applied-web-application-hacking---2-days-25715
Trainer(s) social media links:
https://twitter.com/sensepost_train : @sensepost_train
https://twitter.com/sensepost : @sensepost
https://twitter.com/orangecyberdef : @orangecyberdef
[]
Technical difficulty:
Beginner/Intermediate
Top 3 takeaways you will learn
* Greater understanding of the risks associated with web applications
* A good understanding of the tools and techniques for examining web applications
* Practical skills to exploit a wide variety of web application vulnerabilities
Lecture vs hands on?
Our course aims to be hands-on and practical led education. 40% theoretical content with 60% practical hands-on lab time to solidify the theoretical knowledge.
Who should take this course?
This course is for anyone who wants to understand how to attack and defend web application and the related technologies.
This course is also ideal for any developer looking to further their understanding of where issues can come into play and to widen their understanding of vulnerabilities in web applications.
It’s an offensive course and has obvious benefits for individuals starting a career in pentesting or bug bounty hunting.
Requirements?
Hacking experience isn’t a requirement for this course. However, a technical understanding of how web applications work is required. Development experience isn’t a requirement but can help.
The course is aimed at individuals with beginner knowledge of web applications and hacking.
While not a strict requirement, students will benefit from having an understanding of the following topics before attending the course:
* Fundamentals of programming
* Programming in the following languages:
** HTML
** JavaScript
** SQL
** NoSQL
A familiarity of these topics can be obtained from the following links or other resources:
* https://www.tutorialspoint.com/computer_programming/computer_programming_functions
* https://www.w3schools.com/html/html_intro.asp
* https://www.w3schools.com/js/js_intro.asp
* https://www.w3schools.com/sql/default.asp
* https://www.guru99.com/mongodb-query-document-using-find.html
What should I bring.?
As the bare minimum, you will need to bring along a laptop that is able to run the latest version of Firefox.
What you will be provided with?
* Access to our web class portal containing slides, practicals, walkthroughs and tools and prerequisites. This is accessible during and after the training.
* Access to your own individual lab with numerous targets and capabilities, used for the practicals. This is accessible during the training course.
Suggested Prerequisites:
Requires students to have a solid working understanding of web technologies.
Hacking experience isn’t a requirement for this course. However, a technical understanding of how web applications work is required. Development experience isn’t a requirement but can help.
While not a strict requirement, students will benefit from having an understanding of the following topics before attending the course:
* Fundamentals of programming
* Programming in the following languages:
** HTML
** JavaScript
** SQL
** NoSQL
A familiarity of these topics can be obtained from the following links or other resources:
* https://www.tutorialspoint.com/computer_programming/computer_programming_functions
* https://www.w3schools.com/html/html_intro.asp
* https://www.w3schools.com/js/js_intro.asp
* https://www.w3schools.com/sql/default.asp
* https://www.guru99.com/mongodb-query-document-using-find.html
What students should bring:
As the bare minimum, you will need to bring along a laptop that is able to run the latest version of Firefox.
DATE: August 14th-15th 2023
TIME: 8am to 5pm PDT
VENUE: Caesars Forum, Las Vegas, NV
TRAINER: TBA
- 16 hours of training with a certificate of completion.
- Note: Classes that do not meet their minimum class size by July 15 will be canceled, please register early
- 2 coffee breaks are provided per day
- Note: Food is not included
Registration terms and conditions:
Trainings are refundable before July 1st, the processing fee is $250.
Trainings are non-refundable after July 10th, 2023.
Training tickets may be transferred. Please email us for specifics.
Failure to attend the Training without prior written notification, will be considered a No-Show. No refund will be given.
By purchasing this ticket you agree to abide by the DCT Code of Conduct and the registration terms and conditions listed above.
Davide Cioccia — Hackable.sol: Smart Contract Hacking in Solidity $1,500
Training + Certificate of Completion Training + COC + Certificate of Proficiency
Sign-Up: https://training.defcon.org/products/davide-cioccia-hackable-sol-smart-contract-hacking-in-solidity
Description:
Identify vulnerabilities in Smart Contracts written in Solidity
Training description:
A 2-day full hands-on training where you will learn how to identify vulnerabilities in Smart Contracts written in Solidity. During the course, we will go over 12 labs inspired by the major hacks that saw companies lose millions of dollars, implement Smart Contracts, but also perform security reviews and detect security flaws using manual analysis and automated tools.
Some of the scenarios we will go through:
The list below contains some of the vulnerabilities that we will identify and fix in the labs:
- Any user can cash out the money from the smart contract
- Users can buy the subscription also with any wei amount
- Any user can check the amount of money stored in the contract address
- Reentrancy vulnerability
- Block Timestamp Manipulation Vulnerability
- Tx.origin: Authorization bypass
- Integer Overflow and Underflow
- BatchTransfer Overflow (CVE-2018–10299)
- Unprotected SELFDESTRUCT
- DelegateCall vulnerabilities
- ….more
Trainer(s) bio:
Davide Cioccia is the founder of dcodx, a cybersecurity firm focusing on bridging the gap between development and security, working together with development teams to create and promote the DevSecOps security culture.
He is one of the first contributors to the OWASP Mobile Security Testing Guide and member of the SANS advisory board and Chapter Lead of DevSecCon Netherlands. He is also a speaker at international security conferences like BlackHat, OWASP AppSec, DevSecCon, Hacktivity and regional OWASP security events, where he presented different approaches and tools to automate mobile security testing in CI/CD, detect and prevent phishing attacks and automate infrastructure security in the release cycles.
On the personal side he loves to play racket sports, from tennis to padel, from ping pong to beach tennis. So hit him up for a match if you are in the Netherlands.
https://www.devseccon.com/chapters/dsc-netherlands/
https://appsecus2018.sched.com/event/F02G/mobile-bdd-security-tests-on-steroids-a-new-framework-to-automate-mstg-and-masvs-in-your-cicd-pipeline
https://www.blackhat.com/eu-18/arsenal/schedule/presenters.html#davide-cioccia-36753
Trainer(s) social media links:
https://www.linkedin.com/in/davidecioccia/
https://twitter.com/davide107
Outline:
Intro to Ethereum and smart contracts
Course introduction
Bitcoin vs Ethereum
ETH history: The Four stages of development
POW vs POS
Sharding and Beacon Chain
Docking
Smart Contracts part 1
Smart Contracts basics
Ethereum Smart Contracts and Solidity
EVM
Accounts, Transactions and Gas
Storage, Memory and Stack
VSCode and Remix IDE
LAB: Functions visibility in Solidity
LAB: Our first smart contract
Smart Contracts part 2
Types, Enum and Events
Mappings
Inheritance
Modifiers
SCW registry: the Smart Contracts CWE
Reentrancy vulnerability: the DAO hack
LAB: Steal all my money (Reentrancy attack)
The Open Zeppelin ReentrancyGuard Smart Contract
Interfaces
LAB: Block Timestamp Manipulation Vulnerability
Authorization
Authorization in Smart Contracts
The Open Zeppelin Authorization Contracts
LAB: Authorization done properly
LAB: Tx.origin: Authorization bypass
DoS
SELFDESTRUCT
DoS With Block Gas Limit
DoS with Failed Call
More vulnerabilities
Integer Overflow and Underflow
LAB: Integer Overflow exploitation to drain smart contracts
LAB: BatchTransfer Overflow (CVE-2018–10299)
Libraries
Introduction to embedded and linked libraries
LAB: Delegatecall vs Call
LAB: Exploiting Proxy contracts and Delegate calls
Security auditing
Manual vs automated audit.
Introduction to Smart Contract reverse engineering
LAB: Tools: mythril
LAB: Tools: slither
How to build a comprehensive security auditing report
Hack them all
Final Smart Contract Hacking Challenge
Technical difficulty:
The course is for beginners/intermediate that have some knowledge about smart contracts
Knowledge of the topics below is only recommended but not mandatory for this course.
Blockchain
Smart contracts and Remix IDE
Basic understanding of decentralized applications and their applicability
Suggested Prerequisites:
The course starts from the basics of the blockchain and smart contracts.
Useful resources:
— https://docs.soliditylang.org/en/v0.8.13/
— https://ethereum.org/
What students should bring:
- Laptop with at least:
8 GB RAM
- Chrome Browser
DATE: August 14th-15th 2023
TIME: 8am to 5pm PDT
VENUE: Caesars Forum, Las Vegas, NV
TRAINER:Davide Cioccia
- 16 hours of training with a certificate of completion.
- 2 coffee breaks are provided per day
- Note: Food is not included
Registration terms and conditions:
Trainings are refundable before July 1st, the processing fee is $250.
Trainings are non-refundable after July 10th, 2023.
Training tickets may be transferred. Please email us for specifics.
Failure to attend the Training without prior written notification, will be considered a No-Show. No refund will be given.
By purchasing this ticket you agree to abide by the DCT Code of Conduct and the registration terms and conditions listed above.
Ruben Gonzalez — Hacking Cryptography $2,000
Training + Certificate of Completion Training + CoC + Certificate of Proficiency
Hacking Cryptography
Sign-Up: https://training.defcon.org/products/ruben-gonzalez-hacking-cryptography
Cryptography is everywhere, whether you like it or not. Our laptops, phones, printers, cars, bank cards and washing machines use cryptography to authenticate, keep things confidential and make sure messages aren’t tampered with. However, very often developers, pentesters, system designers and code auditors are confronted with cryptography without having the gear to properly assess security of a specific use case.
During this training we’ll deep-dive into modern cryptography. We’ll learn how it works, how it is often times misused and how that leads to exploitable bugs. Moreover, participants will learn how common cryptography screwups can be exploited. To foster skills, participants will write their own exploits and use them on real world systems provided by us.
The first day will prepare you for (ab)using cryptography in products and services by going over the basic terminology, explaining modern primitives and showing common misuses of those primitives. You’ll learn about tools and techniques to abuse such misuses along the way. On day two, we’ll move on to more advanced primitives used in asymmetric cryptography and see how everything we have learned is employed in protocols and standards (such as TLS, JWT and FIDO).
Trainers
Ruben Gonzalez (Lead Trainer, He/Him):
- 10 years in offensive security research
- Bug hunter for cryptography code
- Lead trainer at Neodyme.io
- Auditor of crypto code for multiple large industry projects
- Part-time PhD candidate for cryptographic implementations at the Max Planck Institute
- Multi-time DEFCON CTF finalist (team Sauercloud)
- Twitter: redrocket_ctf
Tim Schmidt (Support Trainer, He/Him):
- 5 years in vulnerability research
- Tinkerer and Hardware Hacker
- Profound interest in real-world attacks on cryptography
- Multi-time DEFCON CTF finalist (team Sauercloud)
- Trainer at Neodyme.io
Technical Difficulty
Beginner to intermediate
Prerequisites
This is a beginner to intermediate course. The contents are compressed, but no prior knowledge of cryptography is needed. Every subject is introduced before attacks are presented. Students should be familiar with at least one scripting language (e.g. Bash or Python) and have a basic understanding of computer networks.
Equipment Requirements
Participants should bring a laptop with administrator/root access to install software.
Certificate
At the end of the course participants can take a test to certify their knowledge.
Previous Training
This training was previously held at private corporations.
DATE: August 14th-15th 2023
TIME: 8am to 5pm PDT
VENUE: Caesars Forum, Las Vegas, NV
TRAINER: Ruben Gonzalez
- 16 hours of training with a certificate of completion.
- 2 coffee breaks are provided per day
- Note: Food is not included
Registration terms and conditions:
Trainings are refundable before July 1st, the processing fee is $250.
Trainings are non-refundable after July 10th, 2023.
Training tickets may be transferred. Please email us for specifics.
Failure to attend the Training without prior written notification, will be considered a No-Show. No refund will be given.
By purchasing this ticket you agree to abide by the DCT Code of Conduct and the registration terms and conditions listed above.

EHIBITORS & VENDORS
EXHIBITORS
Capitol Technology University
Silver Exhibitor
Capitol Technology University (Capitol Tech), an esteemed non-profit institution, is a beacon of excellence in the realm of STEM-based learning. With an impressive roster of over 17 cybersecurity degree programs spanning bachelors, masters, and doctoral levels, Capitol Tech has consistently been at the forefront of cyber education for more than two decades. Our unique course offerings extend beyond the ordinary, as we are among the select few universities in the nation with programs in the niche fields of cyberpsychology and offensive cyber engineering. Our commitment to providing top-tier education has not gone unnoticed. The National Security Agency (NSA) and Department of Defense (DoD) have recognized us as a National Center of Academic Excellence in Cyber Defense (NCAE-CD), and we take pride in leading the CAE Northeast Regional Hub. With Capitol Tech, you are not just pursuing a degree; you’re stepping into the future of cybersecurity.
Hack The Box
Silver Exhibitor
Hack The Box is a leading gamified cybersecurity upskilling, certification, and talent assessment platform enabling individuals, businesses, government institutions, and universities to sharpen their offensive and defensive security expertise. Launched in 2017, Hack The Box brings together the largest global cybersecurity community of more than 2M platform members and is on a mission to create and connect cyber-ready humans and organizations through highly engaging hacking experiences that cultivate out-of-the-box thinking. Offering a fully guided and exploratory skills development environment, Hack The Box is the ideal solution for cybersecurity professionals and organizations to continuously enhance their cyber-attack readiness by improving their red, blue, and purple team capabilities. Rapidly growing its international footprint and reach, Hack The Box is headquartered in the UK, with additional offices in Greece and the US. For more information, please visit hackthebox.com.
University of Advancing Technology
Silver Exhibitor
University of Advancing Technology (UAT) is an intimate technology University focused on educating students in advancing technology who desire to innovate for our future. UAT is the technophile’s college experience — a community uniquely suited to provide students passionate about technology an ideal place to live and grow.
Ascent-Portal
Bronze Exhibitor
Ascent-Portal provides an automated governance, security, and compliance platform that simplifies risk management and streamlines compliance. With the Ascent-Portal platform’s real-time compliance scoring, you can easily monitor your compliance posture and immediately identify areas for improvement, all while ensuring team accountability and reducing the compliance workload.
Black Hills Information Security
Bronze Exhibitor
Black Hills Information Security specializes in penetration testing, red teaming, threat hunting, Active SOC services, and educational webinars, workshops, and training. We take the knowledge we have and continue to learn through our engagements and share it with the overall information security community because we believe we’re all better together. Also… the creators of the Backdoors & Breaches, incident response card game.
Lacework
Bronze Exhibitor
Lacework offers the data-driven security platform for the cloud and is the leading cloud-native application protection platform (CNAPP) solution. Only Lacework can collect, analyze, and accurately correlate data — without requiring manually written rules — across an organization’s cloud and Kubernetes environments, and narrow it down to the handful of security events that matter. Security and DevOps teams around the world trust Lacework to secure cloud-native applications across the full lifecycle from code to cloud. Get started at www.lacework.com.
OpenVPN
Bronze Exhibitor
OpenVPN® is a leading global private networking and cybersecurity company that allows organizations to truly safeguard their assets in a dynamic, cost effective, and scalable way. OpenVPN solutions help organizations to easily create secure, virtualized, reliable networks that ensure secure communications between on-premise applications, SaaS applications, a remote workforce, business partners, IoT/IIoT devices, and specialized global applications. We offer two secure networking solutions for small, medium, and enterprise businesses. CloudConnexa™, our managed solution, provides secure communication between an organization’s distributed workforce, loT/lloT devices, and the online services they rely on daily with a secure virtualized network. Access Server, our self-hosted solution, simplifies the rapid deployment of a secure remote access solution with a web-based graphic user interface and built-in OpenVPN Connect Client installer. Both allow you to secure your business at scale and provide a seamless experience for your team — no matter the size.
Transportation Security Administration
Bronze Exhibitor
Just like there’s more than one way to peel a banana, there’s myriad ways to protect a computer network. Cyber threats against the nation’s transportation system is increasing. The Transportation Security Administration — with support from the White House, the Cybersecurity and Infrastructure Security Agency and Congress — is hacking traditional cybersecurity policy to improve resiliency for the growing connected transportation sector. Attend DEFCON to learn more about how TSA is working differently in an effort to achieve better outcomes. Come to our booth for more about TSA and the future of cybersecurity in transportation.
VENDORS
1BitSquared LLC
1BitSquared’s mission is to provide high quality, cutting edge, affordable, Open-Source Hardware and Software for Embedded Hardware engineers and hackers. Our systems are designed for advanced hobbyists, as well as University and civilian research programs as well as educational programs.
Bizarre Magic Inc.
Brian Brushwood, host of National Geographic’s Hacking the System, Discovery’s Scam School, The Modern Rogue on YouTube, and most importantly: the podcast “World’s Greatest Con.” We can’t say why, but you should probably get caught up on that podcast before DEF CON.
BoardSRC LLC
Boardsource offers custom mechanical keyboards and accessories for mechanical keyboard enthusiasts. With products ranging from DIY kits to premium aluminum boards, you’re sure to find something that interests you whether you’re new to the hobby or a seasoned veteran.
Cigent Technology, Inc.
/>
Cigent, leaders in data recovery and removal, have built a storage device (for laptops, desktops, external media) with built-in data security. The drive by default makes data “invisible” — unreadable at the sector level, requiring MFA and Cigent software to access the storage. Advanced key creation and storage methodology have been implemented making it virtually impossible(?) to access the key. Additionally there is a dedicated microprocessor that monitors for attempts to wipe or clone the drive, boot off of an alternate OS, or ransom the drive — the drive automatically protects the data if it is attacked. It also has full drive erasure with unique firmware verification that confirms every block was truly wiped. Oh and wait — there’s more…!
DesignFlaw
https://shadowvexindustries.com
Purveyors of limited edition clothing, music, art, stickers and more. Unique 0-day swag just for DEF CON 31. Follow the music in the vending area to find our booth!
Electronic Frontier Foundation (EFF)
EFF is the leading defender of online civil liberties. We promote innovator rights, defend free expression, fight illegal surveillance, and protect rights and freedoms as our use of technology grows.
Hacker Warehouse
HACKER WAREHOUSE is your one stop shop for hacking equipment. We understand the importance of tools and gear which is why we carry only the highest quality gear from the best brands in the industry. From RF Hacking to Hardware Hacking to Lock Picks, we carry equipment that all hackers need. Check us out at HackerWarehouse.com.
HackerBoxes (legal business entity is CrateCrew, LLC)
HackerBoxes is the monthly subscription box for hardware hacking, DIY electronics, cybersecurity, and hacker culture. Each monthly HackerBox includes a carefully curated collection of projects, components, modules, tools, supplies, and exclusive items. HackerBox hackers connect online as a community of experience, support, and ideas. Your HackerBox subscription is like having a tiny hacker convention in your mailbox every month.
Hak5 LLC
Discover the devices that have found their way into the hearts and tool-kits of the modern hacker. Notable for ease of use. Celebrated by geek culture. From comprehensive WiFi audits to covert network implants and physical access mayhem — Hak5 Gear gets the job done.
HotWAN
HotWAN is offering 3 main products: 1) Video Jig (Prototype) — Protect the Human Against Intrusive AI 2) Pen Test Assistant (rev 3) — Automation of Open Source Hacker Tools, Mind Maps, Manual Testing Aid for Red Teams and Penetration Testers. Now, Virtual Machine and Raspberry Pi4 options 3) Boot Monkey (rev 2) — Wireless Robotic Finger for laptop’s power button and anti- screenlocking mechanism
Keyport, Inc.
Keyport® combines keys, pocket tools, & smart tech into one secure everyday multi-tool. We will be selling our latest modular product line (co-branded DEFCON 31 Editions) including the Keyport Pivot, Slide, Modules, Inserts, and accessories.
Mar Williams
Mar Williams is DEFCON’s resident artist, created this year’s official DEFCON badge, and has had a hand in informing the aesthetic of the conference since DC17. You can find their art throughout the hallways, on defcon tshirts, stickers and other swag. Mar will have high quality, signed prints of their DEFCON art available, as well as a selection of other art, stickers, plushes, and vaguely cat shaped baubles. Follow @spuxo on IG or patreon.com/spux
Miscreants LLC
Miscreants is creating clothing for hackers heavily influenced by streetwear and security culture, looking to document the past, present, and future of cybersecurity history. As a brand, we strive to deliver original pieces that belong in your closet for decades.
Monero Devices OÜ
Experience modern finance technology first hand by visiting the Cryptocurrency Hackers stand at the Defcon vendor area. We distribute items relating to a number of projects including Monero, Bitcoin, Ethereum, and others. Show your cryptohacker colours with high quality wearables and custom badges. Try new devices and electronics, with access to the designers on site. Inform yourself of cryptocurrency science by exploring our infocard display rack. Our stand is your one stop shop for cryptocurrency hacker items and information.
Netool LLC
The netool.io Pro2, network engineering in your pocket. Connects to your iOS or Android device to detect a list of protocol including Tagged VLANs, CDP, LLDP, DHCP and more. Configure switches by a press of a button.
NO STARCH PRESS, INC
No Starch Press has been publishing the finest in geek entertainment since 1994. Come by to see our latest books, t-shirts and swag, and meet some of authors and our founder, Bill Pollock. Everything is discounted!
Nuand LLC
Nuand is proud to join DEFCON this year and present new bladeRF products! Our versatile and high-performance bladeRF platform empowers researchers, developers, and security professionals to explore the wireless spectrum like never before. With capabilities that extend from radio-frequency analysis to security, our open-source ecosystem fosters innovation in radio communication and cybersecurity. Visit our booth to experience firsthand the power of bladeRF and meet our team of experts, who are passionate about providing the tools necessary to unlock new frontiers in wireless technology.
PhysSec Education Education PhysSec (Physical Security Village)
The Physical Security Village (formerly Lock Bypass Village) will be present in the vendor area too this year, loaded with physical hacking gear! We will have bypass tools, common keyed-alike keys, handcuffs, village swag, and more. We’ll have hands-on exhibits in the Village area where you can go and try out your new toys right away, without ever leaving DEF CON! Whether you’re new to hacking the physical world, or a seasoned pro, we’re sure we’ll have something for your needs (or at least… something you really want but totally don’t need). All proceeds go towards the cost of putting on the village each year.
Salty Security
Salty Security offers uniquely themed and originally designed merchandise that caters to the hacker mindset and lifestyle. Come by our booth for all your sticker, apparel and tech gadget needs, or find us online at https://saltysecurity.com!
Science & Design, Inc.
Science & Design is a new non-profit that builds free and open-source, public-interest software and helps other non-profits do the same. Our members have worked on ubiquitous software, including OnionShare, DDoSecrets, CalyxOS, Signal, Riseup, and more. Stop by our booth to learn about our organization, get a free usability consultation for your software, and participate in user research!
SLNT Inc.
SLNT Faraday products empower humanity to reclaim their right to disconnect. Our effortless signal blocking gear fits into everyday routines, making navigating modern life safer and healthier.
SPARROWS Lock Picks
https://www.sparrowslockpicks.com
SPARROWS LOCK PICKS www.sparrowslockpicks.COM Manufacturer of Lock Picks & COVERT ENTRY TOOLS With the largest selection of lock picks, covert entry and SERE tools available at DEF CON it¹s guaranteed we will have gear you have not seen before. New tools and classics will be on display and available for sale in a hands on environment. Our Product range covers Custom toolsets, Dimple picks, Disc Picks, Entry Tools, Practice locks, Bypass tools, Urban Escape & Evasion hardware and items that until recently were sales restricted. SPARROWS LOCK PICKS will be displaying a full range of gear including the newly released All Access bump keys, Dimple picks and The Monkey Paw. The “Folder” prototype will also be available for its first public viewing. All products will be demonstrated at various times and can be personally tested for use and Efficacy.
SquareX Pte Ltd
SquareX presents “Hackers: Superheroes of the Digital Age” — a hacker comic book series that explores the often-misunderstood world of Hackers and Hacking. The series challenges the negative portrayal of hackers in mainstream media and showcases them as individuals who want to take on world problems with the one weapon they have — knowledge! Follow along as our protagonists navigate the complexities of being vigilante hackers and learn about the inner workings of real-life hacks. This thrilling series will have you on the edge of your seat, but beware: not everything goes as expected! Get a glimpse into the world of hacking and see these superheroes in a whole new light.
Start9 Labs, Inc
Privacy and free speech are fundamental human rights and essential ingredients for a free society. Human history demonstrates that, when entrusted to others, these rights are invariably denied, resulting in great suffering. As such, it is necessary for individuals to protect their own privacy and right to speak freely. Fortunately, modern technologies, in the form of personal computers, encryption, and open, decentralized network protocols such as the Internet and Bitcoin, make this a real possibility. What is needed is a revolution in personal computing away from the current, hosted, custodial model that breeds dependency and corruption, towards a decentralized model, where individuals have absolute control over their data and communications. Start9 is empowering the community behind this movement with open source tools and education.
The Calyx Institute
The Calyx Institute’s mission is to educate the public about privacy in digital communications and to develop tools that anyone can use. By embracing “privacy by design,” we help make digital security and privacy more accessible to everyone. Members who support our nonprofit mission receive great membership perks like a hotspot with unlimited mobile data, a Pixel phone with CalyxOS privacy-focused operating system pre-installed, and more. Visit https://calyxinstitute.org/ or stop by our booth to learn more!
The Open Organisation of Lockpickers

The Open Organisation Of Lockpickers is back as always, offering a wide selection of tasty lock goodies for both the novice and master lockpicker! A variety of commercial picks, handmade picks, custom designs, practice locks, handcuffs, cutaways, and other neat tools will be available for your perusing and enjoyment! Stop by our table for interactive demos of this fine lockpicking gear or just to pick up a T-shirt and show your support for locksport. All sales exclusively benefit Toool, a 501(c)3 non-profit organization. You can purchase picks from many fine vendors, but ours is the only table where you know that 100% of your money goes directly back to the hacker community.
The OWASP Foundation Inc.
“The Open Web Application Security Project® (OWASP) is a nonprofit foundation that works to improve the security of software. Through community-led open-source software projects, hundreds of local chapters worldwide, tens of thousands of members, and leading educational and training conferences, the OWASP Foundation is the source for developers and technologists to secure the web.”
The SecOps Inc.
The SecOps Group (https://secops.group) is a globally recognized IT security company having vast experience of providing cyber security consultancy and education services. Our core business comprises two units, consultancy and education. The SecOps Group offer CREST accredited security consultancy services and through our exams, we provide an authentic and credible certification program that is up-to-date and represents real life business risks. The SecOps Group also runs a free pentest learning platform called “Vulnmachines”. Please see our booth at Defcon and ask us how you can take a FREE exam.
The Tor Project, Inc.
The Tor Project is a nonprofit developing free and open source software to protect people from tracking, censorship, and surveillance online. Tor’s mission is to advance human rights and freedoms by creating and deploying free and open source anonymity and privacy technologies, supporting their unrestricted availability and use, and furthering their scientific and popular understanding. Stop by our table to learn more, pick up some gear, and find out how you can get involved.
Women in Security and Privacy
Women in Security and Privacy is a global non-profit committed to advancing women and underrepresented communities to lead the future of privacy and security. WISP’s annual programming includes educational and skills workshops, mentoring and networking events, and career advancement and leadership training. WISP also provides stipends and scholarships for women and people from underrepresented communities to attend conferences and to receive training and certifications.
Xcape, Inc.
Pentesting products and services made by hackers for hackers. Cellular products and services for the sneakiest out of band connectivity on engagements.
XXX.VPN
We all know the only VPN you can 100% trust is the one you setup yourself. The next best option is VPN.XXX! No accounts and no storage of personal information and no logging ever! Whether you’re a hacker, security professional, or simply someone who wants to protect their personal information, our VPN client is the solution for you. Our VPN client also features a direct connection to the TOR network, giving you even more options for anonymous browsing.
DEF CON X WHITE HOUSE GENERATIVE AI RED TEAM
Largest annual hacker convention to host thousands to find bugs in large language models built by Anthropic, Google, Hugging Face, NVIDIA, OpenAI, and Stability. This event is supported by the White House Office of Science, Technology, and Policy, the National Science Foundation’s Computer and Information Science and Engineering (CISE) Directorate, and the Congressional AI Caucus.
Said the White House, the DEF CON 31 event “will allow these models to be evaluated thoroughly by thousands of community partners and AI experts to explore how the models align with the principles and practices outlined in the Biden-Harris Administration’s Blueprint for an AI Bill of Rights and AI Risk Management Framework.”
It added, “This independent exercise will provide critical information to researchers and the public about the impacts of these models, and will enable AI companies and developers to take steps to fix issues found in those models.”
The evaluations would be done on provided laptops with timed access to multiple large language models from the vendors listed.
The event will feature a capture-the-flag styled point system to promote testing different types of potential harms, and the community members participating are expected to abide by the hacker hippocratic oath.
While the prize for the winner seemingly pales in comparison to the arduous task ahead of them — the one with the highest number of points wins a high end NVIDIA graphics card — it’s likely the real winners here will be the average person who will be most affected by an AI that isn’t as secure or is more harmful without the intervention of an ethical hacking community.
AI Village (AIV) is hosting the first public generative AI red team event at DEF CON 31 with our partners at Humane Intelligence, SeedAI, and the AI Vulnerability Database. We will be testing models kindly provided by Anthropic, Google, Hugging Face, NVIDIA, OpenAI, and Stability with participation from Microsoft, on an evaluation platform developed by Scale AI.
We love the explosion of creativity that new generative large language models (LLMs) allow. They can help people get their ideas out faster and better than ever before. They can lower barriers to entry in creative fields, and allow for new kinds of creative content. However, we’re only beginning to understand the embedded and emergent risks that come from automating these new technologies at scale. Hallucinations, jailbreaks, bias, and a drastic leap in capabilities are all new issues security professionals and the public have to deal with.
According to Sven Cattell, the founder of AI Village, “Traditionally, companies have solved this problem with specialized red teams. However this work has largely happened in private. The diverse issues with these models will not be resolved until more people know how to red team and assess them. Bug bounties, live hacking events, and other standard community engagements in security can be modified for machine learning model based systems. These fill two needs with one deed, addressing the harms and growing the community of researchers that know how to help.”
At DEF CON 2023, we are conducting the largest red teaming exercise ever for any group of AI models. Thousands of people will experience hands-on LLM red-teaming for the first time — and we’re bringing in hundreds of students from overlooked institutions and communities. This is the first time anyone is attempting more than a few hundred experts to assess these models, so we will be learning together. We’ll publish what we learn from this event to help others who want to try the same thing. The more people who know how to best work with these models, and their limitations, the better. This is also an opportunity for new communities to learn skills in AI by exploring its quirks and limitations.
We will be providing laptops and timed access to multiple LLMs from the vendors. We will also be providing a capture the flag (CTF) style point system to promote testing a wide range of harms. Red teamers will be expected to abide by the hacker hippocratic oath. The individual who gets the highest number of points wins a high end NVIDIA GPU.
This is a collaborative effort. In addition to thousands of hackers, we are also bringing in partners from community groups and policy-oriented nonprofits as well as supporters in government.
The DEF CON community has extensive experience evaluating a huge range of technologies. AIV hosted the first public bias bounty at DEF CON 29 which has grown into the Bias Buccaneers and Humane Intelligence and we’re working with that team again on this event.
Our nonprofit community partners include Houston Community College — which participated in an educational pilot of this exercise; Black Tech Street from Tulsa, OK; the Internet Education Foundation’s Congressional App Challenge; and the AI Vulnerability Database. In addition to Humane Intelligence and SeedAI, the Wilson Center Science and Technology Innovation Program (STIP) is joining as policy partner.
This challenge is supported by the White House Office of Science, Technology, and Policy (OSTP) and is aligned with the goals of the Biden-Harris Blueprint for an AI Bill of Rights and the NIST AI Risk Management Framework. The National Science Foundation’s Computer and Information Science and Engineering (CISE) Directorate will also participate, and the Congressional AI Caucus is collaborating on this initiative as part of their AI Primer series. This exercise will be adapted into educational programming for the Congressional AI Caucus and other officials — as well as for the national networks of our community partners.
The participants are using an evaluation platform that is developed and provided by Scale AI. Our CTF challenge is built by Humane Intelligence. Do you want to participate? We are seeking a laptop sponsor, sponsorship, and travel support for community partners.

DCG 201 TALK HIGHLIGHTS FOR DEF CON 31 (PST)
This is the section where we have comb through the entire list of talks on both days and list our highlights for the talks that stand out to us. Note that this does not invalidate any talks we didn’t list, in fact, we highly recommend you take a look at the full convention scheduel beforehand and make up your own talk hilight lists. These are just the talks that for us had something stand out, either by being informative, unique or bizzare. (Sometimes, all three!)
Thursday, August 10th
10:00 AM
Track 2
Boston Infinite Money Glitch: Hacking Transit Cards Without Ending Up In Handcuffs
Who likes paying to ride the subway? Sure, you could hop the fare gates, but that can be athletically challenging and simply isn’t cool enough for our tastes. What’s a mischievous and miserly rider to do, then? Hack the fare system of course!
In this talk we’ll walk you through how we, four high school students and cybersecurity noobs became the first to fully reverse engineer Boston’s CharlieCard fare system and earn ourselves free rides for life… or at least until the system gets fixed, whichever comes first.
We’ll start by exploring the trials and tribulations of exploring the hardware behind the CharlieCards. Next, we’ll dive into the emotional rollercoaster of reverse engineering the black box that is a transit card system older than us. We’ll then explain the process of disclosing our findings to a government agency without having to hire a legal team. Finally, we’ll show you a demo of some of the tools we made, including our own portable fare machine!
By the end of our talk, regardless of whether you’re an avid RFID hackerman, or a complete noob, we’ll leave you with useful reverse engineering strategies, tips for working with a government agency, and if nothing else, a fun story.
Matthew Harris: A 17 year old and lead hackerman of the group. He likes breaking stuff and doesn’t take kindly to being told what to do. He’s a proud (and maybe annoying) neovim and Linux user, knows how to ride a bike (without training wheels), and is a very opinionated Rustacean despite barely knowing how to use the language.
Zachary Bertocchi: He holds a learners permit, is a seasoned fare machine maker, and even graduated 11th grade! He has successfully made it to the ripe old age of 17, and is an enthusiastic 3D modeler.
Scott Campbell: A heathen who writes things in Bash, holder of a fishing license in the Commonwealth of Massachusetts, and the proud angler of several minnows. Refuses to learn Rust even though it is better than his silly little non memory safe languages in every way.
Noah Gibson: A soccer fan and web developer. In his free time he enjoys kicking a ball, drawing, and programming.
11:00 AM
UNConventional Cybercrime: How a Bad Anti-Hacking Treaty is Becoming a Law
Heads up DEFCON! The future of hacking, cybersecurity, and human rights are at risk as the United Nations negotiates a draft UN cybercrime treaty that has the potential to substantively reshape anti-hacking law around the world. The proposed Treaty could change the game for security researchers and coders like you. With Russia and China playing an initial role in pushing for this treaty, the future for security researchers’s rights could be at risk.
Join us as we deep dive into the murky waters of these negotiations, exploring its risks for security and human rights, including the universal criminalization of network and device intrusion without any protections for legitimate security research. The lack of legal shield for security researchers could hinder bug bounties, responsible vulnerability disclosure, and pentesting. We’ll discuss the geopolitical complexities, and the vital role you can play.
EFF has been on the front lines in Vienna, attending the negotiations and representing the interests of our members since the start, and we need your help. Your insights and experiences are crucial. Together we will review the text, identify new challenges that you may face so we can better understand the community concerns. Let’s champion together a future where security research and human rights can thrive!
Katitza Rodriguez is EFF’s Policy Director for Global Privacy. She concentrates on comparative policy of global privacy issues, with special emphasis on cross-border data flows. Katitza’s work also focuses on cybersecurity and government access to data held by the private sector at the intersection of international human rights law and standards. In 2018, CNET named Katitza one of the 20 most influential Latinos in technology in the United States.
@txitua
Bill Budington is a Senior Staff Technologist on EFF’s Public Interest Technology team. Their research has been featured in the The New York Times, The Los Angeles Times, The Guardian, and cited by the US Congress. They are the lead developer of Cover Your Tracks.
Mastodon: @legind@mastodon.social
11:30 AM
Cracking Cicada 3301: The Future of Collaborative Puzzle-Solving
This talk will explore the ongoing efforts of the CicadaSolvers community to solve Cicada3301’s Liber Primus, a book of elder futhark runes and codes that has challenged cryptographers and puzzle-solvers since 2014. Using our experiences as leaders within the community, we will delve into the cultural significance of the puzzle and discuss the various strategies and techniques employed by members to crack its code, and the story of their struggle to maintain motivation through 9 years of solving one of the most difficult puzzles ever released. Attendees will gain insights into the future of collaborative puzzle-solving and the challenges that the Liber Primus presents for the future of cryptography. This presentation is suitable for anyone interested in cryptography, puzzle-solving, internet mysteries, and the persistence of collaborative communities. No prior technical knowledge or tools are required.
Taiiwo, a CicadaSolvers founding member, with a background in software development, sees the community’s work as an example for the future of problem-solving. With a pragmatic, and sceptical approach to the puzzle, he aims to preserve the community so that it can continue to impact the lives of others as immensely as it did for him.
@Cicada_Solvers
https://discord.gg/cicadasolvers-572330844056715284
Reddit: r/cicada
Artorias is the creator of CicadaSolvers.com, co-host of the CicadaCast podcast, and moderator of r/cicada and the CicadaSolvers discord. Well-versed in the complex history of the Cicada 3301 puzzles, he labors both to document the mystery of Cicada 3301, and to unravel the labyrinth of its interconnected topics.
Puck is a 19-year-old rising junior computer science major and Cicada 3301 puzzle enthusiast. He has been involved in the community for four years, finding inspiration to pursue cryptography and cybersecurity. Puck has focused his work on promoting community solving efforts, mainly in the form of innovative events.
TheClockworkBird With a background in anthropology and teaching, TheClockworkBird creates collaborative spaces where people of all skill levels and interests can engage with the puzzle. He has gained a multifaceted understanding of Cicada’s impact on the individual, and the impacts of collaborative puzzle solving on the growth of privacy awareness.
12:30 PM
New Isn’t Always Novel: Grep’ing Your Way to $20K at Pwn2Own, and How You Can Too
The year is 2023 and we’re still finding very basic vulnerabilities in enterprise software.
In this presentation, we detail how the hacker mindset can be applied to seemingly daunting tasks to make them more approachable. We will show how we approached our first Pwn2Own contest and how we discovered a command injection RCE vulnerability affecting nearly every Lexmark printer. We’ll take a look at why we think it went unnoticed in previous research and why current open-source static analysis tools miss this simple bug.
Finally we’ll release the exploit POC and an additional POC to dump credentials during engagements.
James Horseman loves low-level systems programming and reverse engineering. Has a history of developing implants and weaponizing n-days. He is a vulnerability researcher and attack engineer at Horizon3.ai. twitter.com/JamesHorseman2
Zach Hanley has been hooked on exploit development and offensive security since introduced to the world of hacking as an On-Net Operator for DoD and IC organizations. He’s since developed implants and exploits for both the government and commercial sector. He currently is a vulnerability researcher and attack engineer for Horizon3.ai.
twitter.com/hacks_zach
2:30 PM
Designing RFID Implants — How flipping the bird opens doors for me
RFID implants are basically RFID credentials that can be installed under your skin. When I discovered there was nothing on the market that worked with my employers badging system I decided that I would just have to make my own. This talk will cover the basics of RFID implants, my journey to design my own implant despite having no electronics experience, and some of the future implications of this technology.
Miana is a lifelong tinkerer who likes breaking things almost as much as she likes building them. She is a bio-hacker and info-sec researcher by night, and a professional software nerd during the day.
@NiamhAstra
3:30 PM
Nuthin But A G Thang: Evolution of Cellular Networks
4G? LTE? 3GPP? A lot of telecommunications terminology gets thrown around, but what does it actually mean? While terms like “5G”, and “packet core” may be in common use, it’s hard to understand what they mean in terms of attack surface, or even as a consumer. Very often even network diagrams will show “Core Network” as a big blob, or stop at the Radio Access Network. It’s hard to have insight into the cellular network. So, I’ll explain generation by generation!
In this talk we will walk through each step of cellular evolution, starting at 2G and ending at 5G. The never-ending attack and defend paradigm will be clearly laid out. In order to understand the attack surface, I’ll cover network topology and protocol.
For each cellular generation, I will explain known vulnerabilities and some interesting attacks. In response to those vulnerabilities, mitigations for the subsequent cellular generation are put in place. But as we all know, new mitigations mean new opportunities for attackers to get creative.
While I will explain most cellular-specific terminology, a familiarity with security concepts will help to better understand this talk. Basic foundations of communications systems, information theory or RF definitely make this talk more enjoyable, but are absolutely not necessary. It’s a dense topic that is highly applicable to those working on anything that touches the cellular network!
Tracy is a New York City based Lead Security Research Engineer at Trenchant (formerly known as Azimuth Security). With a degree in Computer Engineering and over 10 years in the industry, Tracy has predominantly focused on vulnerability research, reverse engineering and development for embedded devices. She has led teams focused on telecommunications equipment and contributed to teams large and small working on routers and various types of embedded devices.
Her first degree is in theatre performance, with a vocal performance minor. Vocal technique, performance and understanding the vocal mechanism are what drew her into telecommunications. You may have seen her presenting at conferences, attending trainings, dancing the night away or performing on stage.
Twitter: @hackerpinup
Mastodon: hackerpinup@infosec.exchange
4:30 PM
Small Leaks, Billions Of Dollars: Practical Cryptographic Exploits That Undermine Leading Crypto Wallets
Multi-Party Computation (MPC) has become a common cryptographic technique for protecting hundreds of billions of dollars in cryptocurrency wallets. MPC algorithms are currently powering the wallets of Coinbase, Binance, Zengo, BitGo, Fireblocks and many other fintechs/banks servicing hundreds of millions of consumers and thousands of financial institutions.
This presentation examines the most common MPC protocols and implementations and shows that securing MPC remains a challenge for most companies.
We show practical key-exfiltration attacks requiring no more than a couple of hundred signatures. Namely, we show three different attacks on different protocols/implementations requiring 256, 16, and *one* signature, respectively.
Oren Yomtov (@orenyomtov), Blockchain Research Lead at Fireblocks, is a security researcher with over a decade of experience. In the past year, focusing on the blockchain space, he disclosed a critical vulnerability in a blockchain with a market cap of $100 million and created the first open-source, trustless Bitcoin NFT marketplace, OpenOrdex.
Nikolaos Makriyannis (Nikos), Cryptography Research Lead at Fireblocks, is a cryptography PhD, specializing in the areas of multiparty computation (MPC). Nikos is the co-inventor of the CMP20 and CGGMP21 protocols published in ACM CCS’20 and used by multiple wallet providers.
5:00 PM
Snoop on to them, as they snoop on to us.
BLE devices are now all the rage. What makes a purpose built tracking device like the AirTag all that different from the majority of BLE devices that have a fixed address? With the rise of IoT we’re also seeing a rise in government and corporate BLE surveillance systems. We’ll look at tools that normal people can use to find out if their favorite IoT gear is easily trackable. If headphones and GoPro’s use fixed addresses, what about stun guns and bodycams? We’ll take a look at IoT gear used by authorities and how it may be detectedable over long durations, just like an AirTag.
Nullagent is a robotics hacker. He built his first internet connected robot in 2004 and since then he’s been hooked on embedded hacking. He’s building a hacker collective that fuses artistic expression to bring cyber security tools to a broader audience.
5:30 PM
DEF CON 101 — Welcome to DEF CON Panel
DEF CON 101 began as a way to introduce n00bs to DEF CON. The idea was to help attendees get the best experience out of DEF CON (and also tell them how to survive the weekend!). The DEF CON 101 panel has been a way for people who have participated in making DEF CON what it is today to share those experiences and, hopefully, inspire attendees to expand their horizons. DEF CON offers so much more than just talks and the DEF CON 101 panel is the perfect place to learn about DEF CON so you can get the best experience possible. Come watch us talk about what we love about DEF CON, give you tips and tricks, and maybe even make some new friends!
More Panel members & Bios to be listed soon!
Nikita works to ensure DEF CON runs as smoothly as one can expect from a hacker conference. In addition to planning a vast array of details prior to DEF CON and thwarting issues while onsite, she is the (soon to be retired) Director of Content for the CFP Review Board. This year will be her 20th anniversary.
Nikita is not on the social mediaz.
Kirsten is the Talent Engagement Lead at Accenture Federal. She joined AFS through the acquisition of Novetta, after serving there as Director of Recruiting for 6 years. Her career started in IT building and running helpdesks, and she later moved into Technical Recruiting. She is best known in the community for both her role in the Car Hacking Village and her efforts as a speaker and volunteer across multiple events throughout the year. Kirsten offers over 20 years in technology services space and 15 in the hacker community and conference scene.
Friday, August 11th
9:00 AM
Track 1
The Internals of Veilid, a New Decentralized Application Framework
Veilid is an open-source, peer-to-peer, mobile-first networked application framework, with a flagship secure messaging application named VeilidChat. Veilid is conceptually similar to IPFS + Tor, but faster and designed from the ground-up to provide all services over a privately routed network. The network also enables development of distributed applications without a ‘blockchain’ or a ‘transactional layer’ at their base. Veilid can be included as part of user-facing applications or run as a standalone server for power users who wish to help build the network.
Architecturally, it is written in Rust, uses strong encryption, and nodes can run on Linux, Mac, Windows, Android, iOS, and in-browser WASM. Low-level protocols over UDP, raw TCP, Websockets and Secure Websockets. Nodes are optimized for low latency, high node churn, and are particularly capable of dealing with low level network changes, such as switching from cellular to wifi networks mid-communication.
This talk will focus on the internals of Veilid:
* How it works as a protocol
* How it leverages strong cryptography to provide private communications
* How it provides decentralized storage and cryptographically sound data structures
* How applications are written to leverage the Veilid Network
We will demonstrate Veilid Server, and VeilidChat, the application.
Christien ‘DilDog’ Rioux is a member of The Cult Of The Dead Cow, the author of remote-access utility Back Orifice 2000, and a thorn in Microsoft’s side for over a decade. DilDog is the creator of StuntBanana, a caller-id spoofing system, and is proprietor of the hacker-fashion line HACK.XXX. He is also Co-Founder and former Chief Scientist of Veracode, on the founding team of @stake, as well as a member of L0pht Heavy Industries. DilDog is a staunch believer that if you want to change the present you need to build the future, and is very sorry for having helped create “InfoSec” from hacking, and would like to undo the damage.
@dildog
Katelyn Bowden is a hacker, activist, and CULT OF THE DEAD cow member, who embraces the human side of hacking and tech. She also creates strange furby art and has over 60 dead things on display in her house. @medus4_cdc
Track 2
Welcome to DEF CON 31
The Dark Tangent, Michael and Katie Whiteley (Mkfactor)
Track 4
Growing the Community of AI Hackers with the Generative Red Team
We’re running the largest live AI hacking event ever in the AI village this year. Anthropic, Google, HuggingFace, Meta, NVIDIA, OpenAI, and Stability, have all provided models to attack and Scale AI have built the platform. This event is orders of magnitude bigger than any previous AI red team effort. There are observers from the White House, NIST, NSF, and the EU coming to learn from hackers. We built this event to grow the community that knows how to effectively evaluate Large Language Models as it is much more than prompt injections and jailbreaks.
AI works fundamentally differently to traditional software and only forms a part of a product. Trust and Security of AI in a system thus has to work fundamentally differently to traditional software. This is especially true for generative AI systems. The core difference is AI is a stochastic component of software and is allowed to make a small amount of mistakes. This changes bug hunting, reporting, and payouts.
Come to this talk to hear about how and why we organized this, and the history of algorithmic & bias bounties that led up to the largest one ever at DEFCON 31. We’ll also give you some tips to help you in the contest.
Sven founded the AI Village in 2018 and has been running it ever since. Sven is also the founder of nbhd.ai, a startup focused on the security and integrity of datasets and the AI they build. He was previously a senior data scientist at Elastic where he built the malware model training pipeline. He has a PhD in Algebraic Topology, and a postdoc in geometric machine learning where he focused on anomaly and novelty detection.
@comathematician
Austin co-founded the Congressional Tech Staff Association, co-led the Congressional Cybersecurity Caucus and the Congressional High Tech Caucus, and is a founding fellow of the Internet Law and Policy Foundry. Currently Austin is the President and Founder of SeedAI, a nonprofit established to work with a diverse group of policymakers, academics, and private sector experts to help communities across the United States access the resources they need to engage with AI.
Rumman has built solutions in the field of applied algorithmic ethics since 2017. She is a Responsible AI Fellow at Harvard Berkman Klein’s Center for Internet and Society and the co-founder of Humane Intelligence, a nonprofit dedicated to algorithmic access and transparency. Previously, she was the Director of the ML Ethics, Transparency and Accountability team at Twitter, where she conducted their bias bounty, which was hosted at DEFCON.
9:30 AM
Track 2
Secretary of the Department of Homeland Security Alejandro Mayorkas
The Secretary of US Homeland Security, Alejandro Mayorkas, joins DEF CON for a fireside chat. Secretary Mayorkas will lay some foundational groundwork on some of DHS’ priorities in cybersecurity and how they address pressing IS and global issues, then sit down to talk with The Dark Tangent, in a casual conversation with thousands of their closest hacker friends.
Alejandro Mayorkas was sworn in as Secretary of the Department of Homeland Security by President Biden on February 2, 2021.
A political refugee born in Havana, Cuba, Mayorkas is the first Latino and immigrant confirmed to serve as Secretary of Homeland Security. He has led a distinguished 30-year career as a law enforcement official and a nationally recognized lawyer in the private sector. Mayorkas served as the Deputy Secretary of the U.S. Department of Homeland Security from 2013 to 2016, and as the Director of U.S. Citizenship and Immigration Services from 2009 to 2013. During his tenure at DHS, he led the development and implementation of DACA, negotiated cybersecurity and homeland security agreements with foreign governments, led the Department’s response to Ebola and Zika, helped build and administer the Blue Campaign to combat human trafficking, and developed an emergency relief program for orphaned youth following the tragic January 2010 earthquake in Haiti. Mayorkas also created the Fraud Detection and National Security Directorate to better ensure the integrity of the legal immigration system.
Mayorkas began his government service in the Department of Justice, where he served as an Assistant United States Attorney in the Central District of California, specializing in the prosecution of white collar crime. After nearly nine years as a federal prosecutor, he became the youngest United States Attorney in the nation, overseeing prosecutions of national significance, including the investigation and prosecution of financial fraud, violations of the Foreign Corrupt Practices Act, public corruption, violent crime, cybercrime, human trafficking, environmental crime, international narcotics money laundering, and securities fraud.
Mayorkas received his bachelor’s degree with distinction from the University of California at Berkeley and a law degree from Loyola Law School.
10:00 AM
Track 4
Look Ma I’m the CEO! Real-Time Video and Audio Deep-Fake!
Hey you, yeah you! Do you want to become a big company CEO but are too lazy to invest your life in chasing that position?
Now introducing DEFCON VIDEO-ART — DEep Fake CONversation for VIDEO and Audio in Real-Time! With DEFCON VIDEO-ART you can impersonate your favorite big-company CEO without doing the hard work! You can video call anyone in the company and tell them what to do because you look and sounds like the big boss! Reset passwords, ask for the latest confidential business reports, fire people, you name it!
Deep fake has been around for years, but only recently we have reached a point where real-time deep fake has become easy and accessible to execute. Join my talk where I show how I impersonate my company’s CEO with videos and audio I found online. Then I’ll share how with open-source tools and a decent GPU you can also impersonate your company’s CEO!
Gal Zror (@waveburst) acts as the vulnerability research manager in CyberArk labs. Gal has over 12 years of experience in vulnerability research and he specializes in embedded systems and protocols. Besides research, he is also an amateur boxer and a tiki culture enthusiast.
War Stories @ Harras
A Different Uber Post Mortem
The federal criminal case of United States v. Joseph Sullivan, NDCA 3–20-CR-337 WHO, has been covered and debated quite publicly since I was fired by the new Uber CEO in November 2017, a year after the incident. Most discussion has focused on questions of my guilt or innocence, the culpability of other executives at the company, and the implications of the case for other security executives.
Less has been written about the guilt or innocence of those who accessed Uber’s AWS environment in October 2016 and triggered an incident response by emailing me and asking for payment. After we met them, my team and I did not consider those 19- and 20-year-old kids to be criminal actors and treated them as security researchers. Yet both also faced federal criminal charges.
During my talk I will review the extraordinary investigation done by my team at Uber and put it into the context of other historical cases we and I had worked on. Whether or not you consider them to be security researchers, there are many lessons to be learned related to the dynamics between researchers and companies and the dynamics between companies and the government.
Joe Sullivan is the CEO of Ukraine Friends, a nonprofit providing humanitarian aid to the people of Ukraine. He also advises a number of startups and mentors security leaders. Joe has worked at the intersection of government, technology, and security since the mid-1990s. He spent 8 years working for the US DOJ, eventually as a federal prosecutor 100% focused on technology-related crimes, received national recognition from the DOJ for outstanding service as a federal prosecutor, and worked on many first-of-their-kind cybercrime cases, including supporting the digital aspects of the 9/11 investigation. Joe was recruited to eBay in 2002 to build out their eCrime team, and later took on responsibilities at PayPal. In 2008 Joe moved to Facebook where he became their CSO, building a small security org into a team of hundreds. He was recruited from there to join Uber in 2015 to be their first CSO. After Uber, Joe spent 2018 through 2022 as the CSO at Cloudflare. He has also advised a significant number of companies over the years, including AirBnB and DoorDash. Joe has testified as an expert before the US Congress twice, been a commissioner on the National Action Alliance for Suicide Prevention, a board member on the National Cyber Security Alliance, a many-time opening plenary speaker at the Dallas Crimes Against Children Conference, a participant in a White House anti-online-bullying effort, an advisor to the Department of Homeland Security, and in 2016 accepted an appointment from President Obama to his Commission on Enhancing National Cybersecurity.
10:30 AM
Track 2
The Making of the DEF CON 31 Badge
Speaker(s)
Mar Williams
11:00 AM
Track 2
SpamChannel: Spoofing Emails From 2 Million+ Domains and Virtually Becoming Satan
Ever wake up and ask yourself: “Damn, how could I make email security suck even more today”?Tired of your Red Teams phishing emails not landing in your targets inbox?
Do you dislike Boston (the city) and love Satan?
If you answered yes to any of those questions you should come to this talk!
I’ll be showing you how to spoof emails from 2 million+ domains (while also “bypassing” SPF & DMARC!) by (ab)using a partnership between Cloudflare and the “biggest transactional email service” on the interwebs. We’ll be diving into “edge” serverless applications and the magical world of email security where everything is (still) held up by duct tape, pasta, and marinara sauce. Finally, I’ll be dropping code and releasing a tool that demonstrates how to impersonate emails from 2million+ domains.
Marcello Salvati (byt3bl33d3r) is a hacker & entrepreneur with over a decade of experience as an Offensive Security Researcher, Blue/Purple/Red Teamer and Open Source developer. Marcello is known for creating a number of Open Source tools such as CrackMapExec and weaponizing unorthodox programming languages for malware purposes.
Github: @byt3bl33d3r (https://github.com/byt3bl33d3r)
LinkedIn: @byt3bl33d3r (https://www.linkedin.com/in/byt3bl33d3r/)
Track 3
The Nightmare of Apple’s OTA Update: Bypassing the Signature Verification and Pwning the Kernel
Ding~ A new software update is available for your Mac!
System updates are always considered a silver bullet to protect users against the latest security vulnerabilities. As is common practice, Apple keeps publishing monthly updates, sometimes even within a few weeks. And end users have been continuously educated to keep their devices up to date. Once they see Apple’s system update notification, they may blindly click on the update.
But wait, are you sure you’re getting the right system update?
During my research, I discovered a few critical vulnerabilities in the Apple OTA (over-the-air) update process. Apple had addressed them as CVE-2022–42791, CVE-2022–46722, and more.
CVE-2022–42791 is the one that can bypass the update package signature verification and infect the new OS kernel.
On Intel Macs without the T2 Chip, they can be exploited to bypass the SIP protection and SSV (Signed System Volume) protection, infect the OS kernel, and execute arbitrary kernel code in Ring 0!
And there is one more vulnerability that can infect the OS firmware and execute arbitrary code before the kernel boots!
During this session, I’d like to share with you how a crafted system update can infect your device and inject malicious code into your OS kernel, dominating your device completely without your awareness.
Mickey Jin (@patch1t) works for Trend Micro as a security researcher with a keen interest in malware analysis, threat campaign research, and vulnerability research.
In the past two years, he has received over 100 CVEs from Apple, Inc.
Twitter: https://www.twitter.com/patch1t
website: https://jhftss.github.io/
War Stories @ Harras
Warshopping — further dalliances in phreaking smart shopping cart wheels, RF sniffing and hardware reverse engineering.
Smart shopping cart wheels are electronic wheels with a mechanical braking mechanism meant to prevent cart removal or shoplifting, as well as electronics to provide other tracking functions. In a past talk, I’ve discussed the ultra-low-frequency communication these systems use and how to sniff and replay them (and even use your phone’s speaker to “phreak” your shopping cart!
This talk explores a new type of smart wheel (the Rocateq system), and focuses on a deeper exploration of the hardware and firmware. On top of capturing new sets of ultra-low-frequency control signals, we’ll look at the 2.4 GHz “checkout” signal that it receives from the register and reverse engineer the PCB — soldering on “fly-wires” to look at the chip-to-chip communication with a logic analyzer. We’ll also use a PICKIT programmer to dump the firmware from the main microcontroller for basic analysis using Ghidra.
In addition to the talk, the website where you can play the control signals as audio files on your phone will be updated to include the control codes for the Rocateq brand wheels.
Joseph is a robotics engineer turned hacker — inspired by curiosity of the small systems in our everyday world, he went from developing products to performing security assessments of them. He specializes in embedded systems, circuit reverse engineering, and mechatronics.
His other hobbies include skydiving, multi-medium fabrication, and collecting strange domain names. He is also the founder and Chief Lunatic of the Flat Moon Society, who would like to ask you: isn’t it weird we never see the other side of the moon?
11:30 AM
Track 4
Civil Cyber Defense: Use Your Resources to Defend Non-Profits as they Combat Human Trafficking and Subvert Authoritarian Regimes
ALSO AT BLACK HAT USA
Civil Cyber Defense volunteers and students challenge high-risk adversaries and threats such as human traffickers, authoritarian regimes, and surveillance being conducted on journalists. By utilizing academic resources, OSINT skills, and free/open-source tools, civil cyber defenders are supporting vulnerable non-profits, protecting volunteers, journalists, and activists while defending human rights. There is a need in the cybersecurity industry for more civil cyber defenders. Recommendations will be made as to how your organization can support and/or volunteer your time and tools to provide protection to vulnerable organizations who have high risks, face advanced and persistent adversaries, but have modest resources.
Tiffany Strauchs Rad (BS, MA, MBA, JD) has presented cybersecurity research — both technical and legal topics — at many security conferences such as Black Hat USA, Black Hat Abu Dhabi, Defcon (17, 18, 19), H.O.P.E., 27C3 & 28C3, and has been featured in media such as Wired, Washington Post, CNN, Reuters, 60 Minutes, Der Spiegel, CNN, Wired Magazine, and NPR. Her independent security research was listed as DEF CON Groups in “Top 10 White Hat Hacks” by Bloomberg, and her critical infrastructure research was featured on the USA network series, “Mr. Robot.” In addition to being a car hacker and doing transportation infrastructure security consulting, she is also an adjunct instructor at the University of Maine and U.C. Berkeley teaching classes such as the “Citizen Clinic.”
Austin Shamlin is the CEO and founder of Traverse Project, a nonprofit founded in 2023 to combat human trafficking networks. He has served in the law enforcement/security industry for over 20 years, most recently serving as director of operations with an anti-human trafficking nonprofit under the Tim Tebow Foundation. Austin is a professionally recognized geopolitical security subject matter expert on Haiti and has previously served as a special advisor to the Haitian Minister of Justice. Prior to his nonprofit work, he served as a police executive with the D.C. government. Prior to working for the District of Columbia, Austin joined Redstone Strategies — a start-up life support company operating in Mogadishu, Somalia. His role was to cultivate relationships with the U.S. and Somali governments and direct ground-level business operations. Austin also served in Kandahar, Afghanistan, as a deputy provincial officer for Global Strategies Group, where he directed security operations. Prior to that, he worked for EOD Technology (EODT) in both Baghdad, Iraq, and Port au Prince, Haiti. While assigned to Haiti with EODT, he served as country manager and directed humanitarian efforts, such as recovery operations and medical support, following the earthquake.
12:00 NOON
Track 2
Still Vulnerable Out of the Box: Revisiting the Security of Prepaid Android Carrier Devices
Prepaid Android smartphones present an attractive option since they can be used and discarded at will without significant financial cost. The reasons for their use are manifold, although some people may use them to dissemble their true identity. Prepaid smartphones offer value, but there may be an additional “cost” for their cheap price. We present an examination of the local attack surface of 21 prepaid Android smartphones sold by American carriers (and 11 unlocked smartphones). While examining these devices, we discovered instances of arbitrary command execution in the context of a “system” user app, arbitrary AT command execution, arbitrary file write in the context of the Android System (i.e., “system_server”), arbitrary file read/write in the context of a “system” user app, programmatic factory reset, leakage of GPS coordinates to a loopback port, numerous exposures of non-resettable device identifiers to system properties, and more.
The only user interaction that our threat model assumes is that the user installs and runs a third-party app that has no permissions or only a single “normal” level permission that is automatically granted to the third-party app upon installation. The installed third-party app can leverage flaws in pre-loaded software to escalate privileges to indirectly perform actions or obtain data while lacking the necessary privileges to do so directly. Due to a wide range of local interfaces with missing access control checks and inadequate input validation, a third-party app’s behavior is not truly circumscribed by the permissions that it requests. Due to the common inclusion of pre-loaded software from Android vendors, chipset manufacturers, carriers, and vendor partners, exploit code can have significant breadth. The inter-app communication used to exploit these vulnerabilities may be difficult to classify as inherently malicious in general since it uses the standard communication channels employed by non-malicious apps.
We pick up again where we left off from our DEF CON 26 talk … raiding the prepaid Android smartphone aisles at Walmart. We provide another snapshot on the state of security for Android carrier devices. In this talk, we examine 21 different prepaid Android smartphones being sold by the major American carriers, and we also cover 11 unlocked Android devices, which are primarily ZTE smartphones. We identified vulnerabilities in multiple layers of the Android software stack. For each discovered vulnerability, we step through the attack requirements, access vector, and attack workflow in order to help developers and bug hunters identify common software flaws going forward.
Dr. Ryan Johnson is a Senior Director, R&D at Quokka (formerly Kryptowire). His research interests are static and dynamic analysis of Android apps and reverse engineering. He is a co-founder of Quokka and has presented at DEF CON, Black Hat (USA, Asia, & MEA), IT-Defense, and Hack. His research in Android security has been assigned dozens of CVEs and is responsible for discovering the Adups spyware that affected millions of Android smartphones.
https://www.quokka.io/
Dr. Angelos Stavrou is Founder and Chief Scientist of Quokka (formerly Kryptowire), a Virginia based Mobile Security company. He is also a Professor at the Bradley Department of Electrical & Computer Engineering at Virginia Tech. Dr. Stavrou has served as principal investigator on research awards from NSF, DARPA, IARPA, DHS, AFOSR, ARO, ONR. He is an active member of NIST’s Mobile Security team and has written more than 130 peer-reviewed conference and journal articles. Dr. Stavrou received his M.Sc. in Electrical Engineering, M.Phil. and Ph.D. (with distinction) in Computer Science all from Columbia University. He also holds an M.Sc. in theoretical Computer Science from the University of Athens and a B.Sc. in Physics with distinction from the University of Patras, Greece. Stavrou is an Associate Editor of IEEE Transactions on Computers, IEEE Security & Privacy, and IEEE Internet Computing magazines and a previous co-chair of the IEEE Blockchain initiative. Over the past few years, Dr. Stavrou’s research has focused on two aspects of security: Systems’ Security and Reliability. Dr. Stavrou is a member of USENIX, and a senior member of ACM and IEEE.
Dr. Mohamed Elsabagh leads the research and development efforts at Quokka (formerly Kryptowire). He specializes in automated static/dynamic binary security analysis and reverse engineering for Android, ARM, and x86 platforms. He has created several tools that helped detect and prevent hundreds of zero-day vulnerabilities in the wild. Mohamed holds a PhD in CS during which he developed automated binary hardening techniques for COTS systems.
War Storiese @ Harras
You’re Not George Clooney, and This Isn’t Ocean’s Eleven
One common thread runs through a recent wave of (initially, successful) targeted malware attacks I’ve investigated: The attackers communicated with their targets, personally, using social engineering in real-time, in order to lay the groundwork for the rest of the attack to succeed. Throughout the course of several post-breach investigations, it became apparent that — for a certain kind of target and a particular class of attacker — engaging the victim in direct conversation was far more effective at assuring the target infected their computer than crafting a believable-looking “malspam” email that would “fool” the target into clicking a link or opening a file.
The attackers did not need to be charismatic for the technique to succeed. In fact, so long as the attacker “got into character” and treated the interaction as a normal, everyday event (from their perspective), the targets went along for the ride, and in many cases, self-infected with malware that was capable of snooping through their most sensitive files. In this session, we’ll discuss both the social engineering and technical aspects of the attacks, and why this combination of tactics is particularly dangerous and hard to defend against.
Andrew Brandt is a former investigative reporter turned network forensics investigator and malware analyst, who serves as a Principal Researcher for Sophos X-Ops. Brandt has worked in information security since 2006 and, prior to working in the industry, covered it extensively as the security editor for PC World for nearly a decade. He has applied his knowledge about the behavior of malicious software and threat actors to profile identifiable characteristics of undesirable or criminal activity, specializing in attackers who target the finance, energy, and government sectors. His analysis techniques seek to determine general principles that can help analysts and defenders rapidly and comprehensively identify the root cause of infection and data loss, putting real-time network data analysis at the front line of prevention.
Mastodon: @threatresearch@infosec.exchange (https://infosec.exchange/@threatresearch)
https://news.sophos.com/en-us/author/andrew-brandt/
12:30 PM
Track 3
Backdoor in the Core — Altering the Intel x86 Instruction Set at Runtime
In this work, we present the novel results of our research on Intel CPU microcode. Building upon prior research on Intel Goldmont CPUs, we have reverse-engineered the implementations of complex x86 instructions, leading to the discovery of hidden microcode which serves to prevent the persistence of any changes made. Using this knowledge, we were able to patch those discovered sections, allowing us to make persistent microcode changes from userspace on Linux. We have developed and improved microcode tracing tools, giving us deeper insight into Intel Atom microcode than was previously possible, by allowing more dynamic analysis of the ROM.
Along with this presentation, we provide a C library for making microcode changes and documentation on the reverse-engineered microcode.
We show that vendor updates to the microcode, which cannot be verified by the user, impose a security risk by demonstrating how a Linux system can be compromised through a backdoor within a CPU core’s microcode.
Alexander Dalsgaard Krog is a Vulnerability Researcher at Vectorize with a focus on the low level, close to the hardware, and this talk will be no exception. He has a passion for binary exploitation and together with his prior team at Lyrebirds discovered the critical bug Cable Haunt, affecting millions of devices with a vulnerability allowing remote code execution. Both him and his co-speaker Alexander Skovsende are also heavily invested in CTF and have played a big role in putting the Danish team Kalmarunionen on top of the scoreboard in many CTFs.
https://twitter.com/alexanderkrog
https://www.linkedin.com/in/alexander-dalsgaard-krog
Track 4
Defender-Pretender: When Windows Defender Updates Become a Security Risk
The signature update process is critical to EDR’s effectiveness against emerging threats. The security update process must be highly secured, as demonstrated by the Flame malware attack that leveraged a rogue certificate for lateral movement. Nation-state capabilities are typically required for such an attack, given that signature update files are digitally signed by Microsoft.
We wondered if we could achieve similar capabilities running as an unprivileged user without possessing a rough certificate, instead we aimed to turn the original Windows Defender process to our full control.
In this talk we will deep dive into Windows Defender architecture, the signature database format and the update process, with a focus on the security verification logic. We will explain how an attacker can completely compromise any Windows agent or server, including those used by enterprises, by exploiting a powerful 0day vulnerability that even we didn’t expect to discover.
We will demonstrate Defender-Pretender, a tool we developed to achieve neutralization of the EDR. allowing any already known malicious code to run Fully Un-Detected. It can also force Defender to delete admin’s data. OS and driver files, resulting in an unrecoverable OS. We will also explain how an attacker can alter Defender’s detection and mitigation logic.
Tomer Bar is a hands-on security researcher with 20 years of unique experience in cyber security. He leads SafeBreach Labs as the VP of security research. In the past, he ran research groups for the Israeli government and then led the endpoint malware research for Palo Alto Networks. His main interests are vulnerability research, reverse engineering, and APT research.
Among his recent discoveries are the PrintDemon vulnerabilities in the Windows Spooler mechanism which were a candidate in the best privilege escalation of Pwnie awards and several research studies on Iranian APT campaigns. He presented his research at DEF CON (28–30), BlackHat USA, ReCon, Sector, Confidence, Security Fest and HackCon conferences.
https://www.safebreach.com/safebreach-labs/
https://www.linkedin.com/in/tomer-bar-878a348b/
Omer Attias
With a background in the Ministry of Defense and the Israeli Defense Forces (IDF), Omer has honed his skills in network research, including a deep understanding of Windows internals and Linux kernel components.
In addition to his professional pursuits, Omer is a passionate technology and science enthusiast who is always eager to explore emerging trends and innovations in these fields.
https://www.linkedin.com/in/omer-attias-209a9a127/
1:00 PM
War Stories @ Harras
Living Next Door to Russia
Russia is the world’s largest country. I’ve lived all my life in Finland, about a hundred miles from the Russian border. Finland has learned to live next to a very large and very unpredictable neighbor. Both my grandfathers fought Russia in the second world war. Today, Finland ranks as one of the least corrupted countries in the world, while Russia ranks as one of the most corrupted countries. How is that even possible?
As Russia has grown more aggressive over the last decade and as it violently attacked Ukraine, attitudes about neutrality changed quicky in my home country. When Finland joined NATO in April 2023, NATO more than doubled its land border with Russia — which is probably not what Putin had in mind.
This talk will summarize the developments of the Russian cyber programs and about Russian patriotic hacker groups that got us into where we are today and makes educated guesses about where Russia will be headed next.
Mikko Hypponen is a malware researcher and a best-selling author. He has written for the New York Times, Wired and Scientific American. Mikko has spoken 8 times at Black Hat, and he has 3 TED Talks. Mikko works as the Chief Research Officer for WithSecure and sits in the advisory boards of EUROPOL and Verge Motorcycles.
https://twitter.com/mikko
https://mikko.com
Track 2
Over the Air, Under the Radar: Attacking and Securing the Pixel Modem
ALSO AT BLACK HAT USA
To ensure Google Pixel devices are always at their most secure, the Android Red Team continuously attacks the riskiest areas of the phone. This allows us to proactively get ahead of bugs and protect the phone, before it’s even shipped to users.
The modem — or baseband — is considered a fundamental component of smartphones, and is at high risk because it is a privileged system component that accepts data from an untrusted remote source (cell towers). A vulnerability in the modem exposes end-users to scalable attacks carried out remotely, which may lead to many kinds of compromise on a phone.
Modem security is currently a hot topic of research, attracting growing interest from security researchers, both in the industry and in academia. This wasn’t the case up until recently for a couple of reasons: most modem code is closed source, and testing it requires expensive hardware equipment. With some of these barriers being removed in recent years, due the invention of software-defined radio (SDR) devices and public toolkits, the entry level into baseband security analysis has become more affordable. In this session the Android Red Team will be describing some findings from its offensive evaluation of modems used in Pixel devices.
Farzan Karimi has over 15 years experience in offensive security. He is the Android Offensive Security Manager at Google. In this role, he manages red team operations targeting low-level components within the Android ecosystem. Farzan has specialized in exploiting game development consoles (devkits). His work on PlayStation and Xbox led to the development of key security features for next generation platforms. Farzan is a speaker at security conferences such as Black Hat USA, LABSCON, Microsoft STRIKE, and EA Team Blue.
Xuan Xing is the tech lead of the Android Red Team at Google. For the past years, Xuan focused on finding security vulnerabilities in various low level components of Android/Pixel devices. He is passionate about software fuzzing for security research. In BlackHat USA 2022 Xuan presented the “Google Reimagined a Phone. It was Our Job to Red Team and Secure it” talking about Pixel ABL security auditing. ,
Xiling Gong is a Security Researcher at Google on the Android Red Team. Xiling focuses on finding and exploiting vulnerabilities in the low-level components of Android platform and Pixel devices. Xiling is the speaker of CanSecWest 2018, BlackHat USA 2019, Def Con 27, BlackHat Asia 2021.
Eugene Rodionov, PhD, is a Security Researcher at Google on the Android Red Team. In his current position, Eugene focuses on finding and exploiting vulnerabilities in the low-level components of Android platform and Pixel devices. Prior to that, Rodionov performed offensive security research on UEFI firmware for Client Platforms at Intel, and ran internal research projects and performed in-depth analysis of complex threats at ESET. His fields of interest include reverse engineering, vulnerability analysis, firmware security and anti-rootkit technologies. Rodionov is a co-author of the “Rootkits and Bootkits: Reversing Modern Malware and Next Generation Threats” book and has spoken at security conferences such as Black Hat, REcon, ZeroNights, and CARO.
2:00 PM
War Stories @ Harras
Tracking the Worlds Dumbest Cyber-Mercenaries
For the last 6 years my colleagues and I have been tracking the activities of the cyber-mercenaries we call Dark Caracal. In this time we have observed them make a number of hilarious mistakes which have allowed us to gain crucial insights into their activities and victims. In this talk we will discuss the story of Dark Caracal, the mistakes they have made, and how they have managed to remain effective despite quite possibly being the dumbest APT to ever exist.
Cooper Quintin is a security researcher and senior public interest technologist with the EFF Threat Lab. He has worked on projects including Privacy Badger, Canary Watch, and analysis of state sponsored malware campaigns such as Dark Caracal. Cooper has given talks at security conferences including Black Hat, DEFCON, Enigma Conference, and ReCon about issues ranging from IMSI Catcher detection to fem tech privacy issues to newly discovered APTs. He has also been published or quoted in publications including: The New York Times, Reuters, NPR, CNN, and Al Jazeera. Cooper has given security trainings for activists, non profit workers, and vulnerable populations around the world. He previously worked building websites for nonprofits, including Greenpeace, Adbusters, and the Chelsea Manning Support Network. Cooper was also an editor and contributor to the hacktivist journal, “Hack this Zine.” In his spare time he enjoys making music, visualizing a solar-punk anarchist future, and playing with his kids.
cooperq
https://www.cooperq.com
mastodon: cooperq@infosec.exchange
2:30 PM
Track 1
How I Ransomwared Your [REDACTED] Car
In this talk we’ll discuss a 0-day RCE vulnerability found in [REDACTED] 3rd party legacy proprietary SoftMAC Wifi driver, which is integrated into a popular infotainment system of a major vendor, affecting millions of cars that have been shipped as early as 2015. We’ll deep dive into the details of the research process, such as firmware extraction from a physical device, setting up a lab environment for salvage infotainment off eBay for exploit development, and remote exploitation via maliciously crafted 802.11 Wifi management packet injection to achieve code execution on this QNX based system, which I later used to deploy a persistent, factory-reset-proof car ransomware on a brand-new crossover. I’ll also demonstrate a fingerprint technic to get the specific infotainment firmware version installed on almost every device only by knowing the vehicle’s license plate number.
Omri Ben-Bassat is a security researcher with over a decade of hands-on experience in reverse engineering, vulnerability research, malware/network analysis and incident response. Omri has presented his work at several security conferences including Black Hat USA and RSA Conference. He is currently pursuing a Master’s degree in Computer Science while breaking IoT devices at the Cyber-Physical Systems Research Group (formerly CyberX) at Microsoft Threat Intelligence.
War Stories @ Harras
“You can’t cheat time” — Finding foes and yourself with latency trilateration.
Since the dawn of time, humans have been driven to discover new ways of determining their location, and the location of potential threats. In the realm of cyber threat intelligence, the ability to geolocate servers, for instance the one a C2 is running on, is crucial.
As a research in its early stages, this speech will delve into the exciting world of offensive geolocation. By leveraging inviolable physical laws, we can measure the time it takes for a signal to travel from an adversary to multiple network sensors, and use this information to accurately calculate their position. This technique is known as latency trilateration has never been used before in the cyber realm, and has significant implications for threat intelligence, sandbox evasion, and even malware self-geolocation. I will also discuss potential limitations and challenges of this approach, as well as its broader implications and potential future developments in this emerging field.
Lorenzo Cococcia was born and raised in Italy, the son of two worlds: computer science and physics. Specialized in malware analysis, cyber security and threat intelligence, Lorenzo began his career as a threat intelligence analyst for large industrial companies, where he developed a rigorous approach to the field. He is particularly interested in the intersection of physics and mathematics with the world of hacking and cyber security.
3:00 PM
War Stories @ Harras
CON trolling the weather
Nearly 1,800 weather balloons are launched across the world on any given day.
As the balloon goes up it expands and pops at an altitude up to 33 Km (110K feet) above the earth.The flight payload is called a radiosonde. It measures pressure, temperature, relative humidity, position, and velocity during its flight, and transmits the data to a sounding receiver.
One or two missing weather balloons won’t impact the daily forecast.
However, many missing balloons could lead to errors in weather models and forecasts.
Weather balloons are also important for gathering weather data for satellite launches and human spaceflights, as launches are often delayed or scrubbed due to upper-level wind shear.
In this talk, I present a simulation framework for the most popular radiosonde model.
It enables an attacker to generate radiosonde messages or alter logged messages for retransmission. I also present simulations of a jamming attack and a spoofing attack on a sounding receiver:
During a jamming attack, the receiver is unable to receive transmissions from active radiosondes.
During a spoofing attack, the transmitter sends fake radiosonde messages to a target receiver,
identifying as an active radiosonde.
I’ll talk about the shortcomings of the military variant of the radiosonde model and suggest a simple way to cope with spoofing attacks.
Paz started his professional life more than 30 years ago, hacking games and developing tools in his teen years. Since then, he has worked in several companies, developing both hardware and software. Paz has six years of experience with telecommunication systems design and circuits.
For 14 years, Paz led multidisciplinary systems development as a systems engineer in the aerospace industry. At home, Paz explores ideas he finds interesting.
In 2019 he published a work on a body-tracking device that records keystrokes on a safe’s keypad in Hakin9 Magazine. In 2021 he developed software that used a GPU as a digital radio transmitter and presented his work at DEF CON 29. In 2015 and 2019 he launched weather balloons with elementary school pupils.
https://il.linkedin.com/in/paz-hameiri-251b11143
3:30 PM
Track 3
Turning my virtual wallet into a skimming device: mPOS solutions.
In third-world economies, cheaper often means more accessible. In recent years, there has been a growing interest in modern mobile wallet solutions that allow you to save money, make transactions, payments, and transfer funds to friends or clients with the help of MPOS devices. These small, durable, and simple devices can be used to read credit card information. However, these solutions have vulnerabilities that can be exploited. In this talk, we will provide real-life examples of money theft, credit card information skimming, Bluetooth communication tampering, and hardware hacking associated with these solutions.
Dan Borgogno is a security engineer, backend developer, security researcher and international speaker with years of experience on mobile, hardware, IoT and web application hacking. Security engineer@LATU Seguros.
@dborgogno
https://www.linkedin.com/in/danborgogno
Ileana Barrionuevo is a security engineer, security researcher and international speaker with years of experience in Android mobile hacking and web application hacking. Security researcher @Labsis UTN FRC
@accio_bugs
https://www.linkedin.com/in/ileana-maricel-barrionuevo/
4:00 PM EST
Track 2
Visual Studio Code is why I have (Workspace) Trust issues
Developers are threat actors’ targets of choice because of their access to business-critical services. After compromising a single developer, they could push code changes or obtain sensitive information. For instance, a recent campaign attributed to North Korea set up social network profiles to social engineer and infect prominent figures of the developer community with malicious Visual Studio projects and browser exploits.
At the same time, modern development tools offer increasingly advanced features and deep integration with ecosystems, sometimes at the cost of basic security measures. Code editors tried to counterbalance it by introducing new lines of defense (e.g., “Workspace Trust”), leading to a cat-and-mouse game to restrict access while keeping most features available by default.
In this talk, we present the state of the art of Visual Studio Code’s security. We go in-depth into its attack surface, how its extensions work, and the technical details of two vulnerabilities we found in Visual Studio Code. These findings, CVE-2021–43891 and CVE-2022–30129, led to a $30.000 bounty with an unexpected twist. We also present 1-days discovered by other researchers to develop the audience’s intuition. These concepts apply to most IDEs of the market so everybody will now think twice before opening third-party code! ,
Thomas Chauchefoin (@swapgs) is a Vulnerability Researcher in the Sonar R&D team. With a strong background in offensive security, he helps uncover and responsibly disclose 0-days in major open-source software. He also participated in competitions like Pwn2Own or Hack-a-Sat and was nominated for two Pwnies Awards for his research on PHP supply chain security.
@swapgs@infosec.exchange
Paul Gerste (@pspaul95) is a Vulnerability Research in the Sonar R&D team. In the last months, he has been hunting bugs in popular JavaScript and TypeScript applications, yielding critical vulnerabilities in projects such as Rocket.Chat, NodeBB, and Blitz.js. Paul has also been a CTF player and organizer for some years and loves to hack all web-related things.
War Stories @ Harras
A Series of Unfortunate Events
This talk includes a series of favorite hacking stories. From hacking into a prison system to having the ability to publish “fake news” on a major tech companies website to even breaking into some of the largest entertainment and online casinos. This talk will take a look at the identification, exploitation, and escalation paths as well as the possible impact based on the company’s organization and nature of work.
Ben Sadeghipour AKA NahamSec is a security researcher and content creator. He’s currently in the top 100 for both HackerOne(25) and Bugcrowd’s (95) leaderboards. He has helped identify over a thousand vulnerabilities in companies like Amazon, Apple, Airbnb, Lyft, Snapchat and more. Prior to doing content creation full time, he worked as a research and community education executive at Hadrian and HackerOne. Ben has presented many talks and workshops at cons such DEFCON, BSides, OWASP AppSec, RSA, Red Team Village, and more. He also enjoys hosting and organizing hacker meetups or virtual conferences such as NahamCon and Hacktivitycon!
Corben and Ben have been hacking for nearly a decade on platforms such as HackerOne and Bugcrowd.
Corben Leo is a top–100 bug bounty hunter on HackerOne. He’s worked with Facebook, Google, Microsoft, Apple, PayPal, Yahoo, Epic Games, AT&T, the Department of Defense, and many more. He’s also a co-founder of Boring Mattress Co.
4:30 PM
Track 1
Nothing but Net: Leveraging macOS’s Networking Frameworks to Heuristically Detect Malware
ALSO AT BLACK HAT USA
As the majority of malware contains networking capabilities, it is well understood that detecting unauthorized network access is a powerful detection heuristic. However, while the concepts of network traffic analysis and monitoring to detect malicious code are well established and widely implemented on platforms such as Windows, there remains a dearth of such capabilities on macOS.
This talk aims to remedy this situation by delving deeply into a myriad of programmatic approaches capable of enumerating network state, statistics, and traffic, directly on a macOS host. We will showcase open-source implementations of relatively overlooked low-level APIs, private frameworks, and user-mode extensions that provide insight into all networking activity. And, by leveraging these techniques, you will learn how to efficiently and generically detect both known and unknown threats targeting macOS!
Patrick Wardle is the creator of the non-profit Objective-See Foundation, author of the “The Art of Mac Malware” book series, and founder of the “Objective by the Sea” macOS Security conference.
Having worked at NASA and the NSA, as well as presenting at countless security conferences, he is intimately familiar with aliens, spies, and talking nerdy.
Patrick is passionate about all things related to macOS security and thus spends his days finding Apple 0days, analyzing macOS malware, and writing books and free open-source security tools to protect Mac users.
Track 3
certmitm: automatic exploitation of TLS certificate validation vulnerabilities
TLS is the de facto way of securing network connections. It provides an easy way of ensuring confidentiality, integrity and authentication for any type of communication. However, like most things in life, this is also too good to be true.
TLS allows communicating parties to uniquely authenticate each other by validating each other’s certificate. However, many TLS libraries and frameworks have insecure default settings or allow for the developers to skip important aspects of certificate validation in their client implementations.
This talk explores issues in TLS client certificate validation and the underlying reasons why developers still fail to implement TLS correctly. Most importantly, we hack all the things with a new TLS mitm tool: certmitm.
certmitm automatically discovers and exploits insecure certificate validation vulnerabilities in TLS clients. Let’s use the tool to hack iOS, Windows 11 and more while we deep dive into the world of insecure TLS certificate validation.
Aapo Oksman is a Senior Security Specialist at Nixu Corporation working with application, network and device security. His background is in electrical engineering, embedded devices, and test automation. Combining his background with a hobby in hacking lead to a career in cybersecurity focusing on industrial IoT.
In his free time, Bug Bounties and security research keep Aapo motivated and learning. His work in PKI and TLS has resulting in multiple CVEs from vendors such as Microsoft and Apple. Outside work and research Aapos passion is in the community. He takes part in organizing local security meetups and coaches the Finnish national youth CTF team to the yearly European Cybersecurity Challenge competition.
5:00 PM
Track 2
HL7Magic: Medical Data Hacking Made Easy
In recent years, the use of internet-connected devices has become more prevalent in the healthcare sector, particularly as a means to communicate patient data. Therefore, it is essential that security testing is carried out against these devices to identify misconfigurations that could cause a severe impact, such as the prescription of incorrect drugs.
Modern healthcare protocols such as FHIR (Fast Healthcare Interoperability Resources) use the HTTP protocol to communicate, making security testing relatively straightforward. However, the use of older protocols such as HL7 (Health Level Seven) is more widespread across medical devices in the industry. These protocols are bespoke and difficult to read or intercept using current commercial and open-source security tooling, making testing of these devices challenging and cumbersome.
To address this challenge, I have developed a tool (HL7Magic) to provide security testers with an easier method of intercepting and changing HL7 messages sent to and from medical devices. This tool was created for the purpose of being integrated into Burp Suite as an extension, although it can exist independently.
After talking about how the HL7Magic was created, I will give a short demonstration using the tool for security research purpose or to identify existing CVE’s across your estate. HL7Magic will be open sourced and collaborations to improve it further will be welcomed.
Katie Inns is a Security Consultant in the Attack Surface Management (ASM) team at WithSecure. Katie has 6 years’ experience in the security industry, working in consulting and within an in-house security team focusing on vulnerability management and application security. Katie has spoken about the topic of ASM at conferences such as BlueTeam Con and conINT and holds the OSCP certification. Dancing has been Katie’s hobby for 25 years and she also loves to listen to and play music.
https://www.linkedin.com/in/katie-inns/
War Stories @ Harras
Legend of Zelda: Use After Free (TASBot glitches OoT)
How can a Use After Free exploit in Ocarina of Time lead to a cute robot taking over an entire N64 to put the future (and the Triforce) in the game using only button presses? This talk dives into the technical details of how a Use After Free exploit, Arbitrary Code Execution, and multiple bootstrap stages allowed TASBot to take full control of an original, unmodified cart and console in front of a live audience during SGDQ 2022 with the help of Sauraen and Savestate, helping raise more than $228k for charity. This talk uses engaging explainer graphics courtesy of RGME to dig into how a Use After Free vulnerability can be exploited as well as a live demo showing the significant social impact of the exploit Here Together, in the past year and into the future.
Allan Cecil (dwangoAC) is the founder and BDFL of the TASBot online community. He is part of the senior staff for TASVideos.org, a website devoted to using emulators to find glitches and techniques to play video games perfectly. He is a published journal author, patent holder, and presenter with talks at DEF CON, GeekPwn, Thotcon, May Contain Hackers, and other hacker conferences. He uses his combined hacking interests for good at charity events like Games Done Quick to entertain viewers with never-before-seen glitches in games, with events he’s led raising more than $1.3m for various charities.
https://twitter.com/MrTASBot
https://TAS.Bot
https://Discord.gg/TASBot
https://YouTube.com/dwangoAC
https://Twitch.tv/dwangoAC
Sauraen is a systems and low-level software engineer with experience in GPU programming, high-performance computing, and audio. He directed Triforce% and has been developing tools for the N64 community for nearly a decade. He is also an accomplished music arranger, primarily in the video game music space.
Social media: https://www.youtube.com/@sauraen
Website: https://sauraen.com
Liam Taylor (MLink) is a speedrunner who loves to challenge themselves. Liam has performed several different types of Ocarina of Time speedruns. Aside from speedrunning video games, Liam has also begun learning to solder, always looking to broaden his horizons with different types of hobbies, usually ones that tend to be difficult. He aspires to one day be able to use his talents and skills for a future career in either hardware hacking or speedrunning.
Social media: https://www.youtube.com/@MLink23
Website: https://twitch.tv/MLink23
5:30 PM
Track 3
Fireside Chat with the National Cyber Director Kemba Walden” Kemba Walden
ALSO AT BLACK HAT USA
A fireside chat with Director Walden. Director Walden is the current acting National Cyber Director for the Biden-Harris Administration.
@ONCD, @KembaWalden46
8:00 PM
Track 3
Ask the EFF
ALSO AT BLACK HAT USA
Electronic Frontier Foundation (EFF) is thrilled to return to DEF CON 31 to answer your burning questions on pressing digital rights issues. Our panelists will provide updates on current EFF work, including the fight against government surveillance and protecting creative expression, before turning it over to attendees to pose questions and receive insights from our panelists on the intersection of technology and civil liberties. This is a valuable opportunity to learn from policy experts and engage in a lively discussion rooted in the problems you face. This year you’ll meet: Corynne McSherry, EFF’s Legal Director specializing in intellectual property and free speech; Hannah Zhao, staff attorney focusing on criminal justice and privacy issues; Mario Trijillo, staff attorney with an expertise in privacy law; Rory Mir, Associate Director of Community Organizing; and Cooper Quintin, security researcher and public interest technologist with the EFF Threat Lab.
Corynne McSherry: As EFF’s Legal Director, McSherry has extensive experience in advocating for digital civil liberties and promoting net neutrality. Her perspective on the legal frameworks shaping the digital landscape will provide DEF CON attendees with insights on regulatory issues affecting technology users.
Corynne McSherry @cmcsherr
Hannah Zhao: As a staff attorney at EFF, Zhao brings a legal expertise on criminal justice and privacy issues, with a unique background in international law and Computer Science and Management. Her breadth of expertise can offer DEF CON attendees a new way of thinking about privacy, security, and coders rights.
Hannah Zhao https://www.eff.org/about/staff/hannah-zhao
Mario Trujillo: As a Staff Attorney on EFF’s civil liberties team, he has an expertise focusing on the Fourth Amendment and privacy rights. He is also part of EFF’s Coders’ Rights Project. Prior to joining EFF, he was an attorney at the privacy law firm ZwillGen and clerked for a federal magistrate judge on the southern border.
Mario Trujillo https://www.eff.org/about/staff/f-mario-trujillo
Cooper Quintin: As a senior public interest technologist at EFF, Quintin has a technical expertise on security, privacy, and civil liberties. He has worked on developing tools that empower users to control their online data and has researched state-sponsored malware campaigns. Quintin roots his digital security expertise in a civil liberty framework mindful of the impacts these tools have on people on the margins.
Cooper Quintin https://www.eff.org/about/staff/cooper-quintin
@cooperq,
@cooperq@infosec.exchange
Rory Mir: As EFF’s Associate Director of Community Organizing, Rory works on the EFF activism team to engage community groups on tech policy issues and building community around our issues. This includes our work with the Electronic Frontier Alliance, which directly supports these groups — including a number of local DEFCON groups. Immersed in the community, Rory is familiar with the needs and issues commonly faced by the community. and how it connects to EFF issues.
Rory Mir, https://www.eff.org/about/staff/
falsemirror@octodon.social
Saturday, August 12th
9:00 AM
Track 3
ELECTRONizing macOS privacy — a new weapon in your red teaming armory
MacOS is known for an additional layer of privacy controls called TCC — Transparency, Consent, and Control (TCC) that restricts access to sensitive personal resources: documents, camera, microphone, emails, and more. Granting such access requires authorization, and the mechanism’s main design concern was clear user consent.
Despite many vulnerabilities in that mechanism found in the past, using 0-days during red teaming engagements is impractical. Apple fixes TCC vulnerabilities but red teams still have to get access to files saved on the victim’s desktop or be able take a screenshot.
What if I tell you that there are many open doors to resolve all the TCC problems that are already installed on your target machines?! Electron apps are everywhere. And you probably heard the joke that: ‘S’ in Electron stands for security.
In this talk I will share a new tool that, by abusing Electron default configuration, allows executing code in the context of those Electron apps and thus inherit their TCC permissions.
The audience will leave with a solid understanding of the macOS privacy restrictions framework (TCC) and its weaknesses. The part of the audience interested in macOS red teaming will also get to know my new, free and open source tool. Blue teams on the stage will also see some ideas regarding detections.
Wojciech is a Principal Security Specialist working at SecuRing. He specializes in application security on Apple devices. Wojciech created the iOS Security Suite — an opensource anti-tampering framework. Bugcrowd MVP, found vulnerabilities in Apple, Facebook, Malwarebytes, Slack, Atlassian, and others. In free time he runs an infosec blog — https://wojciechregula.blog. Shared research on among others Black Hat (Las Vegas, USA), Objective by the Sea (Hawaii, USA), AppSec Global (Tel Aviv, Israel), AppSec EU (London, United Kingdom), CONFidence (Cracow, Poland), BSides (Warsaw, Poland).
https://wojciechregula.blog/
https://www.linkedin.com/in/wojciech-regula/
Track 4
Hack the Future: Why Congress and the White House are supporting AI Red Teaming
On May 4th, the White House announced the AI Village at DEF CON’s Generative AI Red Team and their participation, followed by announcements from the House and Senate AI Caucus leadership and the National Science Foundation.
In this panel, we’ll hear from top officials and executives about how they’re balancing the explosion of creativity and entrepreneurship from the advent of GenAI with the known & unknown risks of deployment at scale.
We’ll also hear how this exercise is viewed as a model for enhancing trust & safety through democratizing AI education. Panelists will also discuss why it’s meaningful to bring together thousands of people from different communities to conduct the exercise across the available AI models.
Austin Carson is the Founder and President of SeedAI, a nonprofit established to work with a diverse group of policymakers, academics, and private sector experts to help communities across the United States access the resources they need to engage with AI.
Previously, Austin established and led the DC government affairs operation for NVIDIA [translating NVIDIA’s expertise in artificial intelligence and high performance computing for policymakers]. Prior to joining NVIDIA, he held a number of public sector and NGO positions, serving as Legislative Director for Chairman Michael McCaul and Executive Director for the Technology Freedom Institute. Austin co-founded the Congressional Tech Staff Association, co-led the Congressional Cybersecurity Caucus and the Congressional High Tech Caucus [and is a founding fellow of the Internet Law and Policy Foundry.]
9:30 AM
Track 3
J4 Gate, The Hustler Poker Cheating Scandal investigation and how Hacking helped me do it.
On September 29th, 2022, one of the most controversial poker hand was played, winning an all-in $240K cash pot on the Hustler Casino Live poker stream (HCL) by newcomer Robbi Jade Lew. The controversy and accusations of cheating took the poker and media world by storm! Conspiracy theories emerged immediately within the media, podcasts and the internet sleuths, including crossover theories from the Chess cheating scandal, accusations of collusion with HCL employees, and advanced technology being used. This is the wild tale of my investigation into cheating live stream poker if it was done and what are all the ways I would do it.
I will also show how I utilized my experience from attending hacking conferences such as Defcon for over 26 years, the competitions and how I tapped into a broad range of resources throughout the years of making friends in the hacking community, reaching out to discord groups and doing that which isn’t covered in the academic world. This is why I am here; this is why you are here.
This war story contains treachery, wild technology theories, drama and current criminals on the run. But you, the audience must all decide. Is Robbi innocent or guilty? Was something missing? How would you have cheated?
“Duckie, aka “Scott Melnick,” started his shenanigans War Dialing on his Apple ][+ at an early age and has been attending Defcon and other hacking conferences for over 26 years. Scott currently heads the Security R&D team for Bulletproof, a part of Gaming Laboratories International. Specializing in casino gaming security, he spends his time hacking and reverse engineering electronic gaming devices such as slot machines, sneaking around casinos, getting kicked out of casinos, and speaking at gaming security and regulation events. Over the years, he has worked on many gaming fraud and security breach cases. Before joining Bulletproof, he served as the Vice President of Systems Software Development for a slot and table game maker and held various positions in the slot industry, leading mechanical and electrical engineering projects, overseeing security, and managing IT gaming operations, among other things. He is excited to be delivering his first Defcon presentation this year and contributing back to the hacker community.”
@duckie37
@duckie37@23.illuminati.org
10:00 AM
Track 4
Defeating VPN Always-On
VPN Always-On is a security control that can be deployed to mobile endpoints that remotely access corporate resources through VPN. It is designed to prevent data leaks and narrow attack surface of enrolled end-user equipment connected to untrusted networks. When it is enforced, the mobile device can only reach the VPN gateway and all connections are tunneled.
We will review the relevant Windows API, the practicalities of this feature, look at popular VPN software ; we will then consider ridiculously complex exfil methods and… finally bypass it with unexpectedly trivial tricks. We will exploit design, implementation and configuration issues to circumvent this control in offensive scenarios. We will then learn how to fix or harden VPN Always-On deployment to further limit the risks posed by untrusted networks.
Maxime Clementz is a Senior Manager within the Cybersecurity Advisory team of PwC Luxembourg. He develops his ethical hacker skills by committing himself to various assignments for big companies, banks and European institutions. As a technical specialist, he leads penetration tests, red-teaming, digital forensics and incident response missions.
He contributes to the development of the team’s hacking capabilities by sharing the results of his technology watch and R&D and is now leading the CSIRT and Threat Intelligence initiatives of PwC Luxembourg. He especially enjoys sharing knowledge by presenting the results of each mission or by giving talks (Hack.lu 2012, 2015, 2017) and training courses. Maxime teaches IT security at a French engineering school and organizes a Capture the Flag event for the students.
War Stories @ Harras
D0 N0 H4RM: A Healthcare Security Conversation
In 2016 a bunch of hackers took a break from DEF CON festivities to gather in a hotel room with a bathtub full of beer and talk about shared interests in a brave new world of connected healthcare. Trailblazers were popping pacemakers and pharmaceutical pumps, and we worried that instead of embracing such efforts as opportunities to make tech safer for patients, folks in charge would repeat mistakes of the past and double down on the status quo.
Fast forward to the 2022 passage of the Omnibus spending bill- the FDA is now locked and loaded with expanded authority to regulate cybersecurity requirements for medical devices. What changed? *Keanu voice:* “Policy. Lots of Policy.” Turns out when we get in with the right people, hackers can help get things done. This is the core of Policy @ DEFCON.
Challenges persist. We now have threats from state actors and ransomware blasts delaying lifesaving medical care while costing hospitals hundreds of millions of dollars they don’t have (been in an ER lately?). So once again, come join quaddi and r3plicant, your favorite ripper docs, for another round of D0 No H4rm- this time with special guests from Congress, FDA, and the White House as we figure out what policy patches have the best chance to save lives.
It starts here, in rooms like this, with hackers like you. And it ends with us changing the world.
Christian (quaddi) Dameff MD is an Assistant Professor of Emergency Medicine, Biomedical Informatics, and Computer Science (Affiliate) at the University of California San Diego. He is also a hacker, former open capture the flag champion, and prior DEF CON/RSA/Blackhat/HIMSS speaker. Published works include topics such as therapeutic hypothermia after cardiac arrest, novel drug targets for myocardial infarction patients,and other Emergency Medicine related works. Published security research topics including hacking critical healthcare infrastructure,medical devices and the effects of malware on patient care. This is his nineteenth DEF CON.
Jacqueline Burgette DMD PhD is a White House Fellow at the Office of the National Cyber Director. Jacqueline is a clinician, educator, health policy expert and researcher working at the forefront health and cybersecurity. Jacqueline earned her DMD from the Harvard School of Dental Medicine as a Presidential Scholar and Ph.D.in Health Policy and Management from the University of North Carolina. She served on the faculty at the University of Pittsburgh where she led multi-site studies that amplified the voices of vulnerable families to improve child health in Appalachia. As an expert in health services and highly-published author, she brings her systems perspective and data-driven approach to achieve cross-agency priorities in health and cybersecurity for the Federal government.
Jeff (r3plicant) Tully is a security researcher with an interest in understanding the ever growing intersections between healthcare and technology. His day job focuses primarily on the delivery of oxygen to tissues.
Nitin Natarajan serves as the Deputy Director for the Cybersecurity and Infrastructure Security Agency (CISA). Prior to joining CISA, Natarajan served in a variety of public and private sector positions spanning over 30 years. Natarajan also held a number of federal government roles to include Deputy Assistant Administrator at the U.S.Environmental Protection Agency, the Director of Critical Infrastructure Policy at the White House/National Security Council, and as a Director at the U.S. Health and Human Services overseeing healthcare and public health programs. At the beginning of his career, Natarajan spent 13 years as a first responder in New York, which included service as a flight paramedic. He was the Commander of a federal medical response team, based in New York, and has extensive experience deploying to natural and man-made disasters throughout the nation. He holds an under graduate degree from the State University of New York and a graduate degree from the United States Naval Postgraduate School.
Sen. Warner was elected to the U.S. Senate in November 2008 and reelected to a third term in November 2020. He serves as Chairman of the Select Committee on Intelligence and as a member of the Senate Finance, Banking, Budget, and Rules Committees. He also co-chairs the Senate Cybersecurity Caucus. From 2002 to 2006, he served as Governor of Virginia. He has served as a key author and negotiator of several pieces of critical legislation aimed at rebuilding our nation’s infrastructure, improving cybersecurity, restoring domestic manufacturing, protecting national security, rebounding from the COVID-19 crisis, and investing in under served and underbanked communities.
Dr. Suzanne Schwartz is the director of the Office of Strategic Partnerships &Technology Innovation in the Center forDevices & Radiological Health. Among other public health concerns, her portfolio has most notably included medical device cybersecurity, for which she chairs CDRH’s Cybersecurity Working Group. She also co-chairs the Government Coordinating Council for Healthcare & Public Health critical infrastructure sector. Before FDA, Suzanne was a full time surgical faculty member at Weill Cornell Medical College.
10:30 AM
Track 1
Calling it a 0-Day — Hacking at PBX/UC Systems
PBX (Private Branch Exchange) and UC (Unified Communications) servers are the big communication brokers in enterprise environments where they love on-prem. They do everything to enable internal and external communications including voice, video, conferencing and messaging. But a broader scope also means a broader attack surface.
In this talk, we’ll give an overview PBX/UC systems, what kind of attack surface they have, as well as several bugs that we recently found in two popular PBX/UC products. The journey includes deep-diving Java’s Runtime.exec(), decrypting encrypted PHP, bypassing license restrictions, pretending to be a phone, and (of course) getting some shells.
good_pseudonym, Hacker
Track 3
Unlocking Doors from Half a Continent Away
Contactless credentials have become increasingly popular for secure authentication and access control systems due to their convenience and efficiency. In this talk, we will discuss a specific weakness in the ISO 14443A protocol that enables replay attacks over moderate latency connections, leading to the potential for long-range relay attacks.
During the presentation, we will delve into the history of contactless credential attacks, how manufacturers have adapted, and discuss why we focused on a relay attack. We will provide an
overview of the ISO 14443A protocol and explain how the relay attack is executed and the ‘features’ of the underlying protocol that make it possible. Finally, we will demonstrate and release a new tool to make this relay attack feasible with the Proxmark, as we attempt to unlock a door in Ottawa, ON with a card on-stage in Vegas.
In addition, we will discuss the response from HID Global following our responsible disclosure against their SEOS readers and suggest mitigations to prevent these attacks on your access control systems.
Trevor Stevado is a security researcher and the founder of Loudmouth Security, with over 15 years of experience in the industry. In 2018, Trevor won a Black Badge in the IoT CTF at DEF CON 26, and since then he has been a regular contributor to IoT Village and is now one of the founders of the new Embedded Systems Village, where he continues to push the boundaries of embedded security research.
Sam Haskins is an honors student at Carleton University, in Ottawa ON, and hacker at Loudmouth Security. Sam is a security researcher in their spare time with several CVEs to their name, with a keen interest in cryptography and RFID hacking.
11:00 AM
Track 4
Spread spectrum techniques in disposable drones for anti drone evasion
The popularity of cheap and DIY drones has made them a target for attackers using radiofrequency (RF) signals. Frequency hopping is a technique that can be used to mitigate the risks associated with RF warfare. However, implementing frequency hopping in cheap and DIY drones presents several technical challenges, such as the need for a stable clock and synchronization between the transmitter and receiver without rising hardware costs. Despite these challenges, frequency hopping can significantly enhance the security of consumer and DIY drones making much more challenging or even useless anti-drone systems’ role.
David Melendez is an R&D Embedded Systems Engineer, with over twelve years of experience in cybersecurity and hardware hacking. He has a proven track record of presenting his groundbreaking investigations at prestigious conferences around the world, including DEFCON, BLACKHAT, and ROOTEDCON.
David is also a drone creator and author of the book “Hacking with Drones,” which showcases his innovative use of drones in cybersecurity research. With his passion for pushing the boundaries of technology, David is constantly seeking new ways to improve the security and functionality of embedded systems
@taiksontexas
http://taiksonprojects.blogspot.com/
https://www.linkedin.com/in/david-me...cano-0b195712/
Gabriela (Gabs) García is a university professor and mentor, Secure Software Developer and coding and cybersecurity instructor for organizations such as LinkedIn, Cyber Hunter Academy and Kschool. She teaches, whether that’s in a lecture hall or over the internet, about software development, with a keen eye for secure practices.
Gabriela is also an active member in hacker communities such as HackMadrid%27 and Hack%27, both at home in Spain and across the world. And as an independent professional, she gets to work with a wide variety of clients, crafting custom cybersecurity solutions to fit their specific needs.
11:30 AM
Track 1
Physical Attacks Against Smartphones
(ALSO AT BLACK HAT USA)
Android devices are constantly improving their security to protect against attackers with physical access, with new protection techniques being added year-by-year. This talk aims to demonstrate vulnerabilities in modern Android smartphones that are still viable, despite the mitigations in place.
In the first phase of this talk, we will discuss analysis and exploitation of vendor-customised versions of Android’s Recovery mode, demonstrating weaknesses that allow for privilege escalation to root, and traversal from Recovery to Android, without Bootloader access, using nothing but a Micro SD card.
In the second phase, we will discuss weaknesses in the Secondary Bootloader of devices produced by a popular smartphone manufacturer. We will demonstrate how, using a vulnerability in the core USB stack, code execution can be achieved, and a modified Android image can be booted, without compromising the functionality of the device.
Christopher (@Iskuri1) is a seasoned security researcher. His main focuses are in reverse engineering firmware and fingerprinting USB and NFC vulnerabilities, with his key strength lying in bootloader exploitation.
https://twitter.com/Iskuri1
War Stories @ Harras
Mass Owning of Seedboxes — A Live Hacking Exhibition.
“No one hacks at DEFCON any more.” is what I’ve heard. That is, until
now.
Seedboxes/seedhosts are used by thousands of pirates to download and distribute Movies/TV/Music via USENET and Torrents. The thing is, these systems are horribly insecure. Like, they are wide open. In this talk, I am going to open up a xterm, And a FireFox window, and hack into seedhosts. LIVE. No Demos. No Powerpoint. No introduction slides. Just port scan, attack, 0wn, extract credentials, download all content, obtain other users’ credentials, etc. For literally thousands of accounts.
Did you know people store their Google Drive tokens on seedhosts?
Did you know that your seedbox provider has no idea how to properly configure docker?
Did you know that your plain-text password is sitting in multiple places on these machines, accessible to all other users?
Did you know that administrators for very-large private torrent sites re-use the same password for all their accounts, and leave them on seedhosts?
Let’s hack!
The presenter has been attending DEFCON for ~20 years, and has run
various villages and contests for over 10 years. A professional
pentester for over 24 years, his previously released research and tools
are present in MetaSploit, blog posts, blah blah blah. The hacker is a
long-time member of AHA (Austin Hackers Anonymous — takeonme.org )
and is well known for their “this one time on a pentest” stories.
The thing is though. We aren’t going to tell you their handle/name. It’s
not important. You don’t need it. Don’t pick a talk by how famous someone
is.
12:00 NOON
Track 2
Internet censorship: what governments around the globe have in store for you
The internet is still largely centralized, and not every country
has strong institutional controls preserving the right to access
information or speak freely. Heck, even many “liberal democracies”
are backsliding. While this may sound like an infosec talk suited for
the think tank crowd, these developments are impacting hackers and the results they present at hacker cons.
Internet freedom tools are about empowering users to have the safety to make their own priorities. While China, Iran, and Russia are obviously key concerns in this space, many other countries are seeking to enact new laws and regulations that impact all types of users — some with nefarious intent and others just accidentally harmful.
This conversation will explore the reasons, the symptoms, and some
ideas about how to preserve our ability to set our own priorities. We
will offer a holistic and detailed picture of how censorship affects
our work and that of our colleagues — how even if you feel secure in
the freedom you have where you are right now, government censorship and surveillance in other places will unquestionably affect us all.
Roger Dingledine is president and co-founder of the Tor Project, a nonprofit that develops free and open source software to protect people from tracking, censorship, and surveillance online. Roger works with journalists and activists on many continents to help them understand and defend against the threats they face, and he is a lead researcher in the online anonymity field. EFF picked him for a Pioneer Award, and Foreign Policy magazine chose him as one of its top 100 global thinkers.
Chris Painter is the President of the Global Forum on Cyber Expertise. He served as the first top cyber diplomat in the U.S. State Department, in the White House as Senior Director for Cyber Policy in the National Security Council, and in the Justice Department and the FBI. Awards include the RSA Award for Excellence in the Field of Public Policy (2016), the Attorney General’s Award for Exceptional Service, and the Intelligence Community Legal Award (2008).
Jeff Moss created DEF CON.
Joel Todoroff works for the Office of the National Cyber Director, where he provides legal and policy support on a range of issues, including commercial spyware and securing the foundations of the internet. He has previously worked with the Department of Defense, intelligence community, and the Privacy and Civil Liberties Oversight Board.
12:30 PM
Track 1
Video-based Cryptanalysis: Extracting Secret Keys from Power LEDs of Various Non-compromised Devices Using a Video Camera
ALSO AT BLACK HAT USA
In this talk, we present video-based cryptanalysis, a new method to recover secret keys from a non-compromised device by analyzing video footage obtained from a device’s power LED. We show that cryptographic computations performed by the device’s CPU change the power consumption of the device which affects the brightness/color of the device’s power LED. The changes in the brightness can be detected at a sufficient sampling rate for cryptanalysis by obtaining video footage from a device’s power LED (by filling the frame with the LED) and exploiting the video camera’s rolling shutter, to increase the sampling rate by three orders of magnitude. The frames of the video footage are analyzed in the RGB space, and the RGB values are used to recover the secret key. We demonstrate the recovery of: (1) a 256- bit ECDSA key from a smartcard using video footage obtained from the power LED of the smartcard reader via a hijacked Internet-connected security camera located 16 meters away from the smartcard reader, and (2) a 378-bit SIKE key from a Samsung Galaxy S8 using video footage obtained from the power LED of Logitech Z120 USB speakers (that were connected to the same USB Hub of the Galaxy S8) via iPhone 12.
We discuss countermeasures, limitations, and the future of video-based cryptanalysis.
Dr. Ben Nassi is a postdoctoral researcher at Cornell Tech. He is interested in building robust systems and investigates the security and privacy of cyber-physical systems and hardware/devices in the topics of side-channel attacks and AI security using signal processing and machine learning techniques. His research has been presented at top academic conferences, published in journals and Magazines, and covered by international media. Ben has spoken at prestigious industrial conferences (Black Hat Asia and USA, RSAC USA, AI Week, CodeBlue, SecTor, and CyberTech) and he serves as a PC member in ACM CCS (22 and 23) and BlackHat Asia (22 and 23). His research entitled him to two nominations for the Pwnie Award.
Twitter: https://twitter.com/ben_nassi
LinkedIn: https://www.linkedin.com/in/ben-nassi-68a743115/
Website: https://www.nassiben.com
Ofek Vayner is an M.Sc student at Ben-Gurion University of the Negev and a security researcher at BGU’s Cyber Security Research Center. He holds a B.Sc. degree from the Department of Electrical Engineering at Ben-Gurion University of the Negev. His primary research interests are side-channel attacks and cryptanalysis.
Track 3
An Audacious Plan to Halt the Internet’s Enshittification
The enshittification of the internet follows a predictable trajectory: first, platforms are good to their users; then they abuse their users to make things better for their business customers; finally, they abuse those business customers to claw back all the value for themselves. Then, they die.
It doesn’t have to be this way. Enshittification occurs when companies gobble each other up in an orgy of mergers and acquisitions, reducing the internet to “five giant websites filled with screenshots of text from the other four” (credit to Tom Eastman!), which lets them endlessly tweak their back-ends to continue to shift value from users and business-customers to themselves. The government gets in on the act by banning tweaking by users — reverse-engineering, scraping, bots and other user-side self-help measures — leaving users helpless before the march of enshittification.
We don’t have to accept this! Disenshittifying the internet will require antitrust, limits on corporate tweaking — through privacy laws and other protections — and aggressive self-help measures from alternative app stores to ad blockers and beyond!
Cory Doctorow (craphound.com) is a science fiction author, activist and journalist. He is the author of many books, most recently RED TEAM BLUES, a science fiction crime thriller; CHOKEPOINT CAPITALISM, nonfiction about monopoly and creative labor markets; the LITTLE BROTHER series for young adults; IN REAL LIFE, a graphic novel; and the picture book POESY THE MONSTER SLAYER. In 2020, he was inducted into the Canadian Science Fiction and Fantasy Hall of Fame.
http://craphound.com/bio
Twitter: @doctorow
1:30 PM
Track 1
Meduza: How an exiled pirate media outlet breaks through the Kremlin’s propaganda firewall
Meduza is an independent international Russian- and English-language publication that still reaches millions of people inside Russia. The newsroom is operating from exile for 8 years now with headquarters in Latvia. Despite being completely outlawed and banned by the Kremlin, Meduza continues to work even under such enormously tough circumstances and still delivers the truths about the war in Ukraine along with an unbiased reporting on the situation inside Russia.
But at DEF CON Meduza will not be presented as a media. The team tries to resist the total state control of the Internet in Russia and fight not only for the freedom of speech, but for the freedom of information for millions of people.
Meduza CTO will explain how one of the most free internet has become one of the most regulated and censored ones within just a couple of years. Alex will share the practical experience of resisting censorship along with his (pessimistic) forecast for the future of the Internet in Russia (a new “Iron Curtain’)’. He will describe how the authorities were once again able to “deceive the people’’ (before all that happened, there were no abrupt blockings in Russia and the habit of using VPN was not formed among internet users). This is important to not to let this scenario be repeated in whatever part of the world.
Tech Dept has always been an important part of Meduza newsroom, but in 2022 the tech guys became an even more crucial part of it. It is thanks to their work that the newsroom is able to successfully bypass blocking and retain the audience in Russia. And to protect the journalists and to repel various DDoS attacks on the infrastructure and products.
Alex is CTO at Meduza. He joined the team in 2019. It was a rather crazy and brave decision to give up the job in a stable global corporation and join an independent media company in the times when it was already obvious that independent journalism is not welcome in Russia any more.
Alex’s main topics of expertise:
Media company digital security. Protection of both employees and infrastructure against cyber threats, government run attacks, surveillance. Circumvention tools and technologies. Practical experience of reaching the audience in state-controlled countries. Government methods and approaches against media organizations. How they discover and block “forbidden” content, legal and physical pressure, surveillance. Risk analysis and research-based forecast for the further elaboration of censorship, i.e. sovereignization, criminalization of content etc.
Track 3
The GitHub Actions Worm: Compromising GitHub repositories through the Actions dependency tree
ALSO AT BSIDES LAS VEGAS
GitHub is the most popular platform to host Open Source projects therefore, the popularity of their CI/CD platform — GitHub Actions is rising, which makes it an attractive target for attackers.
In this talk I’ll show you how an attacker can take advantage of the Custom GitHub Actions ecosystem by infecting one Action to spread malicious code to other Actions and projects by showing you a demo of POC worm.
We will start by exploring the ways in which Actions are loosely and implicitly dependent on other Actions. This will allow us to create a dependency tree of Actions that starts from a project that we want to attack and hopefully ends in a vulnerable Action that we can take control of.
We will then dive down to how GitHub Actions is working under the hood and I’ll show you how an attacker that is in control of an Action can utilize the mechanism of the GitHub Actions Runner to infect other Actions that are dependent on their Action and eventually infect the targeted project.
Finally, after we’ve gained all of the theoretical knowledge I’ll show you a demo with POC malware that is spreading through Actions and we will talk on how to defend against this kind of attack.
Asi has 8 years of experience in the security field, including security architecture, SOC management, incident response, and application security research. Asi has gained his experience working for major organizations in the financial and government sectors. Today, Asi is a security researcher that focuses on revolutionizing CI/CD security at Palo Alto Networks. During his free time, Asi likes to read, invest in the stock market and to snowboard.
@TupleType
https://il.linkedin.com/in/asi-greenholts
2:00 PM
Track 4
Power Corrupts; Corrupt It Back! Hacking Power Management in Data Centers
Our current administration lists “Defend Critical Infrastructure” as the DEF CON Forums item in the 2023 National Cybersecurity Strategy. At the intersection of governmental and corporate concerns is data center security, a trend that is bound to continue as more and more operations move to the cloud. This talk details our findings in the domain of power management, the first category in a broader effort to investigate the security of critical data center components. We will reveal nine vulnerabilities in two integral data center appliances: a Power Distribution Unit (PDU) and a Data Center Infrastructure Management (DCIM) system. Continuing, we will delve into the technical details of the most impactful vulnerabilities and highlight the potential impact on their respective operations. The talk will challenge the misconception that data centers are inherently more secure than on-prem by exposing how attackers could leverage these vulnerabilities. This presentation will be valuable to data center professionals, security researchers, and anyone interested in understanding the characteristic vulnerabilities associated with modern data centers.
Sam Quinn is a Senior Security Researcher on the Advanced Research Center Vulnerability team, focused on finding new vulnerabilities in both software and hardware. Sam has a focus on embedded devices with knowledge in the fields of reverse engineering and exploitation. He has had numerous vulnerability findings, published CVEs in IOT and enterprise software, and has spoken at multiple industry conferences such as Def Con, BlackHat, North Sec, and Hardwear.io.
Jesse Chick is a Security Researcher with the Advanced Research Center’s vulnerability team. Jesse focusses on vulnerability discovery and exploit development for all things connected to the internet and is credited with numerous CVEs affecting popular embedded devices. He is passionate about reverse engineering, full system emulation, and educating others in offensive security techniques.
2:30 PM
Track 3
Contactless Overflow: Code execution in payment terminals and ATM’s over NFC.
We conducted a research to assess the current security of NFC payment readers that are present in most of the major ATM brands, portable point of sales, gas stations, vending machines, transportation and other kind of point of sales in the US, Europe and worldwide. In particular, we found code execution vulnerabilities exploitable through NFC when handling a special application protocol data unit (APDU) that affect most NFC payment vendors. The vulnerabilities affect baremetal firmware devices and Android/Linux devices as well.
After waiting more than 1 year and a half once we disclosed it to all the affected vendors, we are ready to disclose all the technical details to the public. This research was covered in the media by wired.com but without the technical details that we can share now
https://www.wired.com/story/atm-hack...point-of-sale/
Some of the affected vendors are:
IDtech — https://idtechproducts.com/
Ingenico — https://www.ingenico.com/
Verifone — https://www.verifone.com/
CPI — https://www.cranepi.com/
BBPOS — https://www.bbpos.com/
Wiseasy — https://www.wiseasy.com/
Nexgo — https://www.nexgoglobal.com/
In this presentation we will describe the vulnerabilities and also demo how the readers can be compromised, using a special Android app we created, by just tapping an Android phone to the reader. We will discuss the consequences such as financial impact in reader’s users/owners and card data stealing once the firmware is compromised. Also, we will show how to compromise the host that is connected to the reader through USB by manipulating the reader’s firmware, chaining stack buffer overflow vulnerabilities in the SDK provided by the vendor that is running in the host machine.
Finally, since one of the affected vendors (IDtech) is present in most ATM brands in the world, the talk will cover different scenarios of how possible can be jackpotting ATMs just tapping a smartphone into the reader of the ATM. We have many years of experience jackpotting all brands of ATMs in multiple different ways and we will show how this is technically possible.
Josep Pi Rodriguez is experienced in network penetration and web application testing, reverse engineering, industrial control systems, transportation, RF, embedded systems, AMI, vulnerability research, exploit development, and malware analysis. As a principal consultant at IOActive, Mr. Pi Rodriguez performs penetration testing, identifies system vulnerabilities, and researches cutting-edge technologies. Mr. Pi Rodriguez has performed security services and penetration tests for numerous global organizations and a wide range of financial, technical, and educational institutions. He has presented at international conferences including Defcon, Immunity infiltrate, Hack in Paris, Japan CCDS and Confidence Conference.
@Josep_pi
3:30 PM
Track 3
ndays are also 0days: Can hackers launch 0day RCE attack on popular softwares only with chromium ndays?
Chromium is not only the most popular browser in the world but also one of the most widely integrated supply chain components. Nowadays, a large number of popular software is built on frameworks based on Chromium, such as CEF and Electron. This means that vulnerabilities in Chromium will directly affect popular software. In addition, according to Google’s vulnerability disclosure policy, most of the details of Chromium vulnerabilities will be publicly disclosed 14 weeks after being fixed, and many of these vulnerabilities are high-impact and may lead to RCE. Unfortunately, we have found that much downstream software is unable to timely fix the Chromium vulnerabilities. This creates a window of opportunity for attackers to carry out RCE attacks on popular software. The cost for attackers to exploit these vulnerabilities during this window is relatively low, as it falls between the time of the Chromium vulnerability disclosure and the completion of fixes for popular software. We refer to this window as the “RCE window period”.
In this topic, we will first evaluate the “RCE window period” of more than 20 popular software. In the upcoming section, we will showcase how to transform Chromium nday vulnerabilities into popular software 0day vulnerabilities in a low-cost manner within the “RCE window period”. To illustrate this process, we will use over 10 RCE 0day vulnerabilities in popular software that we have discovered as examples. Some software will attempt to enable sandbox to mitigate this problem, so we will also provide examples of how to bypass the sandbox by exploiting vulnerabilities in the software itself rather than a Chromium sandbox bug.
Finally, we will discuss the reasons for the existence of the RCE window period and the lessons learned from it, hoping to help software developers improve the security of their products.
Bohan Liu (@P4nda20371774) is a senior security researcher at Tencent Security Xuanwu Lab. He focuses on browser security research and has discovered multiple Chrome vulnerabilities. He also presented his research results on Kanxue SDC and Black Hat Asia.
@P4nda20371774
Guancheng Li (@atuml1)is a senior researcher at Tencent Security Xuanwu Lab. His research interests are focused on software and system security, IoT security, software engineering and AI. He is also a founder and former captain of r3kapig CTF Team.
Zheng Wang (@xmzyshypnc) is a senior Security Researcher at Tencent Security Xuanwu Lab. He’s mainly engaged in browser and linux kernel security. He is also a speaker attending in Black Hat Asia 2023.
4:30 PM
Track 3
Abortion Access in the Age of Surveillance
In the year since the Supreme Court overturned federal legal protections for reproductive rights, people seeking, providing, and supporting reproductive healthcare are grappling with the challenges of digital surveillance. Multiple services and apps track our movements and communications, and that data can be used by law enforcement and private parties to police and punish abortion access. Lawsuits and prosecutions are already underway and are likely to increase as states continue to pass or expand anti-abortion laws and undermine legal protections for online expression and privacy.
But the fight is far from over. At the state and federal level, lawmakers, activists, and technologists are taking steps to establish and shore up legal and practical protections for secure and private healthcare access.
This panel brings together legal and security experts to lead a discussion about defending reproductive justice in the digital age Ð what has already been accomplished, whatÕs coming, and how hackers can help. It will build on and update a discussion held last year, also led by EFF and DDF.
Corynne McSherry is the Electronic Frontier Foundation’s Legal Director. In addition to leading the legal team, Corynne specializes in litigation defending online expression.
@cmcsherr; @cmcsherr@sfba.social
Kate Bertash is the founder of the Digital Defense Fund, a digital security organization for the abortion access movement. She is a hacker and designer of the ALPR-jamming clothing line, Adversarial Wear.
@katerosebee
www.eff.org; www.digitaldefensefund.org
Daly Barnett is a staff technologist at the Electronic Frontier Foundation and a digital privacy consultant with Hacking//Hustling. She utilizes her skills as a techie and experience as an activist and educator to undermine the harms that surveillance causes movement-oriented work. Where most information security resources seek to protect capital, her goal is to re-tool those concepts to protect people and liberatory movements.
India McKinney is the Electronic Frontier Foundation’s Director of Federal Affairs. As a former Capitol Hill staffer and a current EFF lobbyist, her main job is to make sure that the laws of the land don’t suck the life out of the internet.
@imck82
5:00 PM EST
Track 2
Polynonce: An ECDSA Attack and Polynomial Dance
ECDSA is a widely used digital signature algorithm. ECDSA signatures can be found everywhere since they are public. In this talk, we tell a tale of how we discovered a novel attack against ECDSA and how we applied it to datasets we found in the wild, including the Bitcoin and Ethereum networks.
Although we didn’t recover Satoshi’s private key (we’d be throwing a party on our private yacht instead of writing this abstract), we could see evidence that someone had previously attacked vulnerable wallets with a different exploit and drained them. We cover our journey, findings, and the rabbit holes we explored. We also provide an academic paper with the details of the attack and open-source code implementing it, so people building software and products using ECDSA can identify and avoid this vulnerability in their systems. We’ve only scratched the surface, there’s still plenty of room for exploration.
Nils is a Security Researcher on Kudelski Security’s research team performing research on various topics including privacy, authentication, big data analytics, and internet scanning. He also writes blog posts on various topics for Kudelski’s research blog. Nils likes open source software and has presented his research at DEF CON and Black Hat Arsenal. He was part of creating a massively distributed system for breaking RSA public keys.
@tmlxs
Marco works as Principal Cryptographer on Kudelski Security’s research team. He has a long experience designing a wide range of HW and SW cryptographic modules, from silicon roots of trust through physically unclonable functions to side-channel resistant cryptographic libraries. Marco likes looking at crypto from different points of view, bridging theory and implementation, to find new paths of attack (and defense).
Sunday, August 13th
10:00 AM
Track 2
Cellular Carriers HATE this Trick: Using SIM Tunneling to Travel at Light Speed
Cellular networks form large complex compounds for roaming purposes. Thus, geographically-spread testbeds for masurements and rapid exploit verification are needed to do justice to the technology’s unique structure and global scope. Additionally, such measurements suffer from a combinatorial explosion of operators, mobile plans, and services. To cope with these challenges, we are releasing an open-source framework that geographically decouples the SIM (subscription) from the cellular modem by selectively connecting both remotely. This allows testing any subscriber with any operator at any modem location within seconds without moving parts. The resulting measurement and testbed platform “MobileAtlas” offers a scalable, controlled experimentation environment. It is fully open-sourced and allows other researchers to contribute locations, SIM cards, and measurement scripts.
Using the above framework, our international experiments in commercial networks revealed exploitable inconsistencies in traffic metering, leading to multiple data “phreaking” opportunities (“free-ride”). We also expose problematic IPv6 firewall configurations, hidden SIM card communication to the home network, and fingerprint dial progress tones to track victims across different roaming networks and countries with voice calls.
Adrian Dabrowski wrote his PhD about large infrastructures including the identifying fake base stations (“IMSI Catchers”). Before his PhD, he was a founding member of two hackerspaces in Vienna, Austria, and on the board of one of them.
https://www.ics.uci.edu/~dabrowsa/
Gabriel Gegenhuber is PhD candidate in Vienna, Austria. Gabriel is conducting research in the area of cellular and mobile networks. This includes Internet measurement technologies, traffic classification systems (e.g., deep packet inspection), and technical measures that are used to detect net neutrality and privacy violations.
https://informatik.univie.ac.at/Gabr...arl.Gegenhuber
Track 4
Vacuum Robot Security and Privacy — Prevent your Robot from Sucking your Data
Exactly 5 years ago we were presenting ways to hack and root vacuum robots. Since then, many things have changed. Back then we were looking into ways to use the robots’ “dumb” sensors to spy on the user (e.g. by using the ultrasonic sensor). But all our predictions were exceeded by the reality: today’s robots bring multiple cameras and microphones with them. AI is used to detect objects and rooms. But can it be trusted? Where will pictures of your cat end up?
In this talk we will look at the security and privacy of current devices. We will show that their flaws pose a huge privacy risk and that certification of devices cannot be trusted. Not to worry, though — we will also show you how to protect yourself (and your data) from your robot friends.
You will learn on how you can get root access to current flagship models of 4 different vendors. Come with us on a journey of having fun hacking interesting devices while preventing them from breaching your privacy. We will also discuss the risks of used devices, for both old and new users.
Finally, we will talk about the challenges of documenting vacuum robots and developing custom software for them. While our primary goal is to disconnect the robots from the cloud, it is also for users to repair their devices — pwning to own in a wholesome way.
Dennis Giese is currently a PhD student at Northeastern University and focuses on the security and privacy of IoT devices.
While being interested in physical security and lockpicking, he enjoys applied research and reverse engineering malware and all kinds of devices.
His most known projects are the documentation and hacking of various vacuum robots. His current vacuum robot army consists of over 45 different models from various vendors.
dgi_DE
11:00 AM
Track 4
Burrowing Through The Network: Contextualizing The Vulkan Leaks & Historical State-Sponsored Offensive Operations
In March 2023, journalists and investigators released analysis of “the Vulkan files.” Consisting of documents associated with a Russian company working with intelligence and military authorities, the papers revealed a variety of ambitious programs such as “Scan-V” and“Amezit.” Both programs, in the sense that they offer capabilities to acquire, maintain, and task infrastructure for cyber and information operations at scale, are deeply concerning, indicating a significant advancement in Russian-linked network warfare and related actions.
Placing these items in context reveals a far more troubling picture.After reviewing the capabilities of Amezit and Scan-V, we can see glimpses of historical programs in the advertised efficacy of these projects. We will consider other items that have leaked over the years offering similar capabilities, albeit in different circumstances.Examples include Russia’s SORM framework for domestic operations,China’s Great Firewall and (more significantly) Great Cannon programs, and items that emerged in the Snowden leaks such as the US’s alleged “Quantum” program.
By analyzing these additional projects, we will observe a decade’s long trend in the systematization and scaling of cyber programs, especially with respect to automated exploitation and infrastructure management. Vulkan and related items, as significant as they are, represent a culmination of operational evolution and an example of the proliferation of capabilities following disclosure. With programs such as Scan-V exposed, we should anticipate other entities seeking to mirror such capabilities, progressing beyond botnets and other distributed systems to effective management of dispersed capabilities for signals intelligence and cyber operations.
Joe Slowik has over 15 years’ experience across multiple cyber domains. Currently, Joe leads threat intelligence, hunting, detection engineering, and purple teaming functions for Huntress. Previously, Joe performed in-depth threat intelligence research for DomainTools and Dragos, and led incident response operations at Los Alamos National Laboratory. Joe started off in information security through various roles in the US Navy and intelligence community.
12:00 NOON
Track 2
Terminally Owned — 60 years of escaping
It is 60 years since the first publication of the ASCII standard, something we now very much take for granted. ASCII introduced the Escape character; something we still use but maybe don’t think about very much. The terminal is a tool all of us use. It’s a way to interact with nearly every modern operating system. Underneath it uses escape codes defined in standards, some of which date back to the 1970s.
Like anything which deals with untrusted user input, it has an attack surface. 20 years ago HD Moore wrote a paper on terminal vulnerabilities, finding multiple CVEs in the process. I decided it was time to revisit this class of vulnerability.
In this talk I’ll look at the history of terminals and then detail the issues I
found in half a dozen different terminals. Even Microsoft who historically
haven’t had strong terminal support didn’t escape a CVE. In order to exploit
these vulnerabilities they often need to be combined with a vulnerability in
something else. I’ll cover how to exploit these vulnerabilities in multiple
ways.
Overall this research found multiple remote code execution vulnerabilities
across nearly all platforms and new unique ways to deliver the exploits.
David is a software engineer for G-Research, his day job is working on
Kubernetes and other cloud technologies. His security interests center around networks and how to break them in surprising ways. He believes that we need to understand more historical vulnerabilities in order to fix current issues and so spends his spare time researching codebases or technologies that no-one else thinks to look at. In addition when he can put it in DNS, he will, creating such hits as “Wikipedia over DNS” and “Wordle over DNS”.
He aims to find more CVEs than he creates and is currently succeeding.
@davidgl, Mastodon: @dgl@infosec.exchange
Track 3
Retro Exploitation: Using Vintage Computing Platforms as a Vulnerability Research Playground and Learning Environment
It can be very difficult for those new to hacking to learn about vulnerability discovery and exploit development on modern operating systems and software. The complexity of a modern computing environment, developer awareness of security risks, and the iterative development of exploit mitigations over the past three decades has put up an intimidating wall in front of those who would be interested in learning about vulnerability research. Vintage computing environments can provide an interesting and fun playground environment for learning and experimenting with reverse engineering, vulnerability discovery, and exploit development.
In this talk, Wesley will discuss the setup of a complete environment for hacking software for the Commodore Amiga line of computers, a 16/32 bit computing platform of the late 80s and early 90s (not to mention a dedicated following of users and software today). He will describe the hardware environment, OS architecture, and the practically endless library of software that can be used as interesting targets of research. On-system development and debugging software will be described, as well as using the modern Ghidra disassembler. A case study of identifying and exploiting a vulnerability in a 1994 vintage FTP client will be discussed in technical detail.
Dr. Wesley McGrew directs research, development, and offensive cyber operations as Senior Cybersecurity Fellow for MartinFederal. He has presented on topics of penetration testing and and malware analysis at DEF CON and Black Hat USA and taught a self-designed course on reverse engineering to students at Mississippi State University, using real-world, high-profile malware samples. Wesley has a Ph.D. in Computer Science from Mississippi State University for his research in vulnerability analysis of SCADA HMI systems.
http://twitter.com/McGrewSecurity
https://defcon.social/@mcgrew
https://www.mixcloud.com/wesmcgrew/stream/
1:00 AM
Track 4
Exploring Linux Memory Manipulation for Stealth and Evasion: Strategies to bypass Read-Only, No-Exec, and Distroless Environments
As cyber threats continue to evolve, attackers constantly develop new methods for exploiting system vulnerabilities and evading detection. In this presentation, we will delve into cutting-edge techniques for manipulating Linux memory in highly constrained environments, such as read-only, no-exec, and distroless setups. These techniques can be utilized by sophisticated malware to remain stealthy and evade traditional security mechanisms.
We will begin by providing an overview of the unique challenges faced in these limited environments and discuss the reasons behind their increasing prevalence. Next, we will explore how attackers can exploit vulnerabilities within these constraints and demonstrate several novel methods for manipulating Linux memory.
Throughout the presentation, we will showcase real-world examples and provide step-by-step explanations for each technique, enabling attendees to gain a deeper understanding of how they can be employed by adversaries. Additionally, we will discuss potential countermeasures and mitigation strategies to help security professionals better defend against these emerging threats.
By attending this presentation, participants will gain valuable insights into the latest advancements in Linux memory manipulation and acquire the knowledge needed to anticipate and counter stealthy attacks in constrained environments. Whether you are a security researcher, a system administrator, or an ethical hacker, this session will equip you with the expertise necessary to stay ahead of the curve in the ever-evolving world of cybersecurity.
Carlos has a degree in Telecommunications Engineering with a Master in Cybersecurity. He has worked mainly as Penetration Tester and Red Teamer for several companies, but also as developer and system administrator. He has several relevant certifications in the field of cybersecurity such as OSCP, OSWE, CRTP, eMAPT and eWPTXv2. He was captain of the Spanish team in the ECSC2021 and member of Team Europe for the ICSC2022.
Since he started learning cybersecurity he has tried to share his knowledge with the infosec community by publishing open source tools such as https://github.com/carlospolop/privi...-scripts-suite and writing a free hacking book that anyone can consult at https://book.hacktricks.xyz.
@hacktricks_live
Website: book.hacktricks.xyz
Github: https://github.com/carlospolop
Yago is currently studying Telecommunications Engineering. He is an experienced C programmer, tolerates python and has extensive knowledge of Linux Internals. He works as a vulnerability researcher on binaries as well as malware on mobile systems. He is an occasional CTF player and has participated in the ECSC2020 as a member of the Spanish team.
@arget1313 https://github.com/arget13
2:00 PM
Track 3
[redacted telecom talk]
This title and abstract will be updated before the event, when we are no longer under an embargo to share details of our research to the public.
In this talk, we will present how we undertook a multi-year journey in order to obtain and extract the well-guarded secret cryptographic components underpinning the security of a prominent telecommunications standard used globally by law enforcement, military, and critical infrastructure in the power, oil & gas, water, and transport sectors and beyond. Since the inner workings of the cryptography are heavily protected, we had to identify and exploit multiple zero-days in a popular communications device and its trusted execution environment (TEE), yielding us no less than 7 CVEs in the radio stack and SoC.
This talk will include a demonstration of the radio exploitation, and will discuss research materials we published in order to enable asset owners and the cyber-security industry at large to conduct further research on this important standard.
Carlo Meijer is a co-founding partner and security researcher at Midnight Blue. His research focuses on the analysis of cryptographic systems deployed in the wild. He is known for his work on the security of so-called Self-Encrypting Drives (SEDs). Furthermore, he is known for breaking a hardened variant of Crypto1, the cipher used in the Mifare Classic family of cryptographic RFID tags. Finally, he co-authored research into default passwords in consumer routers as deployed by ISPs in the Netherlands. He is a PhD researcher and systems security lecturer at the Radboud University (RU) in the Netherlands.
Wouter Bokslag is a co-founding partner and security researcher at Midnight Blue. He is known for the reverse-engineering and cryptanalysis of several proprietary in-vehicle immobilizer authentication ciphers used by major automotive manufacturers as well as co-developing the world’s fastest public attack against the Hitag2 cipher. He holds a Master’s Degree in Computer Science & Engineering from Eindhoven University of Technology (TU/e) and designed and assisted teaching hands-on offensive security classes for graduate students at the Dutch Kerckhoffs Institute for several years.
Jos Wetzels is a co-founding partner and security researcher at Midnight Blue. His research has involved reverse-engineering, vulnerability research and exploit development across various domains ranging from industrial and automotive systems to IoT, networking equipment and deeply embedded SoCs. He has uncovered critical zero-day vulnerabilities in dozens of embedded TCP/IP stacks, Industrial Control Systems (ICS), and RTOSes.
He previously worked as a researcher at the Distributed and Embedded Security group (DIES) at the University of Twente (UT) in the Netherlands where he developed exploit mitigation solutions for constrained embedded devices deployed in critical infrastructure, performed security analyses of state-of-the-art network and host-based intrusion detection systems and has been involved in research projects regarding on-the-fly detection and containment of unknown malware and APTs.
Twitter: @s4mvartaka
Track 4
Hacker Court — Interactive Scenario
Be a member of the jury as two lawyers prosecute and defend a hacker (live on the stand) in a made up scenario. You, the audience, will decide if the hacker was caught in the act, or if the attribution was all a false flag. Learn through the trial what evidence you don’t want to leave behind in an op, what D&R can and should collect, and how criminals who conduct cybercrime actually get prosecuted.
winn0na is a former threat analyst turned policy professional. She has organized policy content at DEFCON and has authored multiple pieces on offensive cyber capability proliferation. She will be facilitating the Mock trial as some of the brightest lawyers in cyber (names to be released) take the stage.
3:30 PM
Track 1 + 2
DEF CON Closing Ceremonies & Awards
The Dark Tangent & DEF CON Senior Staff
Till it ends. minutes
CONTINUE TO: HACKER SUMMER CAMP 2023 — Part Ten: USENIX + SOUPS
