HACKER SUMMER CAMP 2023 GUIDES — Part Eight: SquadCon by Black Girls Hack

Welcome to the DCG 201 Guides for Hacker Summer Camp 2023! This is part of a series where we are going to cover all the various hacker conventions and shenanigans both In-Person & Digital! This year in 2023 somehow bigger than it was in 2022 and thus we will have a total of 15 guides spanning 3 Months of Hacker Insanity!
As more blog posts are uploaded, you will be able to jump through the guide via these links:
HACKER SUMMER CAMP 2023 — Part One: Surviving Las Vegas & Virtually Anywhere
HACKER SUMMER CAMP 2023 — Part Two: Capture The Flags & Hackathons
HACKER SUMMER CAMP 2023 — Part Three: SummerC0n
HACKER SUMMER CAMP 2023 — Part Four: Zero Gravity by RingZero
HACKER SUMMER CAMP 2023 — Part Five: The Diana Initiative
HACKER SUMMER CAMP 2023 — Part Six: BSides Las Vegas
HACKER SUMMER CAMP 2023 — Part Seven: Black Hat USA
HACKER SUMMER CAMP 2023 — Part Eight: SquadCon by Black Girls Hack
HACKER SUMMER CAMP 2023 — Part Nine: DEFCON 31
HACKER SUMMER CAMP 2023 — Part Ten: USENIX + SOUPS
HACKER SUMMER CAMP 2023 — Part Eleven: Chaos Computer Camp
HACKER SUMMER CAMP 2023 — Part Twelve: Wikimania 2023
HACKER SUMMER CAMP 2023 — Part Thirteen: HackCon XI
HACKER SUMMER CAMP 2023 — Part Fourteen: Blue Team Con
HACKER SUMMER CAMP 2023 — Part Fifteen: Hack Red Con
HACKER SUMMER CAMP 2023 — Part Sixteen: SIGS, EVENTS & PARTIES

#SquadCon by Black Girls Hack
Date: Thursday, August 10th (9:00 AM PST) — Saturday, August 12th (2:00 PM PST)
Website: https://squadcon.me/
Location: The Industrial Event Space (2330 S Industrial Rd, Las Vegas, NV 89102)
Platform(s): HopIn
Schedule: https://squadcon.me/
Live Streams:
TBA
Chat: TBA
Accessibility: Offers Online Virtual & In-Person Attendance. Basic Virtual Tickets are FREE but LIMITED (https://hopin.com/events/squadcon/registration?code=DnNiZ3lruZk8vFgINPl5McBSk), only $80.50 VIP Virtual (they send you a physical badge in the mail) is available. General Admission In-Person is $172.50 and prices go up with VIP & VIP+
Tickets: https://www.eventbrite.com/e/girls-hack-village-presents-squadcon-tickets-634358692927
Code Of Conduct: TBA
Girls Hack Village presents SquadCon is a three-day conference that seeks to bring gender diverse perspectives of the contributions, experiences, and issues facing the industry’s other. Hackers that are new or from underrepresented communities may not often feel comfortable in existing conferences. SquadCon is a forum for conversations about topics that impact girls, women, and LGBTQ+ individuals, including mental health and all the factors that shape the experiences of marginalized groups in the industry. SquadCon is a cybersecurity conference that will include talks, labs, workshops, discussions, CTFs and panels to move towards our mission of improving diversity in ethical hacking.
SquadCon is an independent conference event in Las Vegas during Hacker Summer Camp scheduled for August 10–12th. It is run by the makers of Girls Hack Village and exists to help foster diversity and inclusion in cybersecurity.
BlackGirlsHack Foundation (BGH Foundation) is a registered non-profit organization in the state of Virginia with a 501(c)(3) designation. We are a training-focused organization that was created to help increase diversity in cybersecurity by helping to bridge the gap between what is taught in educational institutions and what is necessary for careers in cybersecurity.
While several organizations cater to the interests of women and minorities in cybersecurity, black women are still severely underrepresented both in the field and by existing infrastructures. BlackGirlsHack meets the needs left unmet by existing services by providing hands-on skills that are focused on people who are upskilling and reskilling in cybersecurity.
To that end, BGH provides weekly hands-on ethical hacking workshops and training programs aimed at helping to provide technical skills and certifications to one of cybersecurity’s most underserved populations. BGH partners with some of the world’s best training organizations to offer introductory to advanced-level training through our BGH Training program.
The newest hacker convention to burst onto the Las Vegas strip, #SquadCon was started by Black Girls Hack, who had a successful booth at DEFCON 30 last year, due to some infuriating boneheaded news:

Being the absolute girl bosses & chad hackers that they are, they literally did this:
And now what was going to just be yet another booth at DEFCON 31 turned into a three day circus extravaganza DURING DEF CON weekend!
The focus on what has been presented seems to be a mid-sized Goldielock zone; not super massive like Black Hat and DEF CON but not super niche and small like the previous Fuzzcons. Small enough to be intimate and social but large enough to be a three day tour-de-force. Focus similar to their booths is on diversity and inclusion in race, gender and sexuality. Balancing the business carrier side of InfoSec with the insane tricks of 1337 hackers, we welcome this new convention and can’t wait to see it in action come August!
Because remember…behind every great black man, is a black woman that got shit done.
PHYSICAL LOCATION RECON


The Industrial Event Space
2330 S Industrial Rd, Las Vegas, NV 89102,
United States of America
(702) 423–3946
TICKET TIER SYSTEM
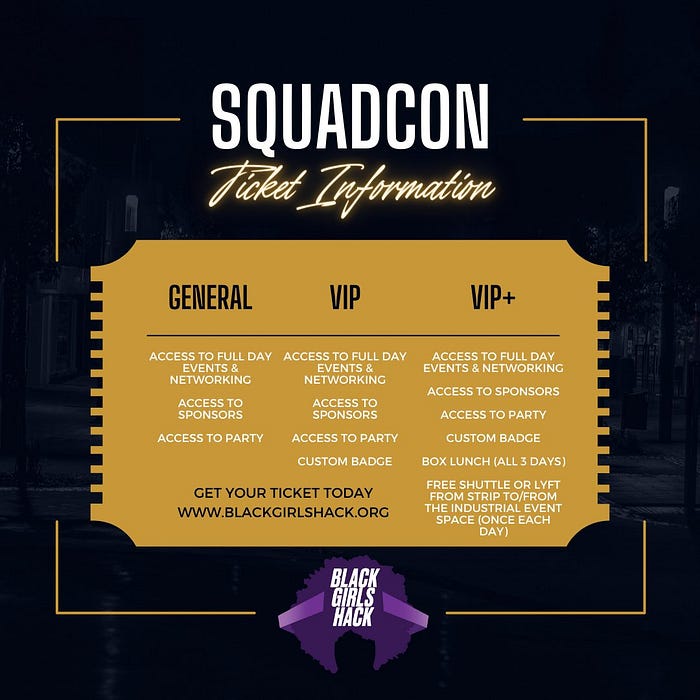
General Admission Ticket ($150) includes:
Access to full day events and networking
Access to sponsors
Access to Party
VIP Admission Ticket ($200) includes:
Access to full day events and networking
Access to sponsors
Access to Party
Custom Badge
Free Shuttle or Lyft from Strip To/From the Industrial Event Space (Once each day)
VIP+ Admission Ticket ($250) includes:
Access to full day events and networking
Access to sponsors
Access to Party
Custom Badge
Box Lunch all three days
Free Shuttle or Lyft from Strip To/From The Industrial Event Space (Once each day)

Virtual Only Ticket (Free) includes:
Access to live streamed talks
Virtual+ Ticket ($70) includes:
Access to live streamed talks
Custom Badge (Shipped to U.S. addresses)
HOW TO HOP INTO HOPIN

BLACK GIRLS HACK WORKSHOPS
The first 15 to sign up for a workshop will have a reserved spot and the last 15 can sign up in person if you choose. For the preregistered spots, your registration will be held for 10 minutes at the start of the workshop and will be released to others wishing to participate if you do not show up.
Intro to CTF Workshop
If you think CTFs sound cool, but aren’t sure how to even get started, then come join us for this interactive session! We’ll walk you through everything you need to know to get started. Learn how to set up your workspace and discover useful tools and techniques to solve common challenges in open-source intelligence and cryptography. No cyber or CTF experience required — all you need is your laptop.
Protect the Pi Workshop
Girls Hack Village annual Protect the Pi workshop is back for its second year. It’s Red Team vs. Blue Team, who will win? In this workshop you will be place on either the Red or Blue team according to your desired preference. Either you will have to stop the Red Team from stealing your flags or you will go full Red Team and use exploits to gather as many flags from the Blue Team as possible. There will be a moderator and helpers for those that need it during this challenge in order to get the full experience of the workshop. Newbies are definitely welcomed and encouraged to participate as you will learn new defensive and offensive skills in cybersecurity as you protect your Pi or use it as a weapon against the Blue Team.
Join us for a mobile app workshop focused on hacking Android WebViews with Frida! Improper implementation can expose WebViews to attacks, compromising user data. This workshop will include Android security fundamentals, with a focus on WebViews, and will leverage the Frida dynamic instrumentation toolkit to analyze and manipulate WebViews in real-time. This hands-on session will provide participants of all skill levels with practical knowledge and skills to assess and exploit Android WebViews and Frida fundamentals for conjuring their own scripts.
Requirements:
- Laptop with administrative privileges
- Corellium virtual device will be provided
Optional:
- Android emulator with Frida installed
WIRESHARK & PASSWORD CRACKING WORKSHOP
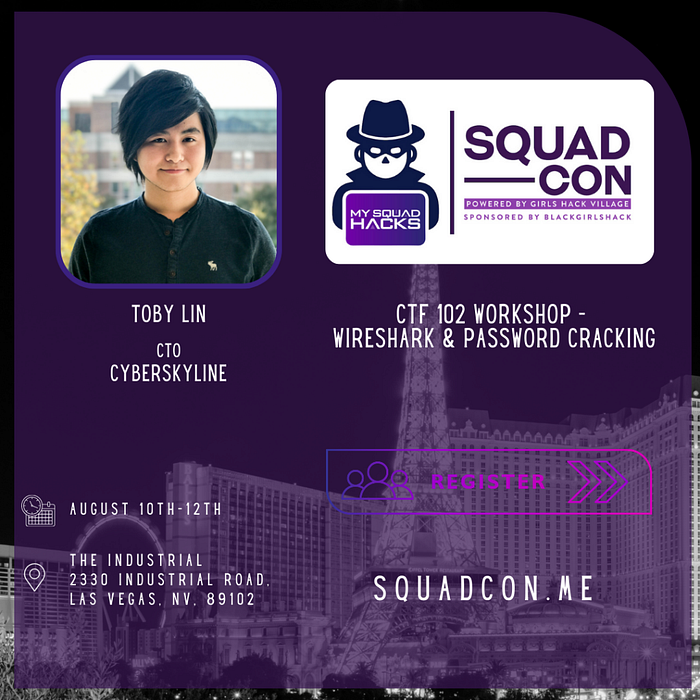
If you’ve got the basics down and want to find out how you can strengthen your CTF game, then you’ll want to join us. In this interactive session, we’ll show you how you can use Wireshark to dive deep into packets and find out what hidden data is being sent on the wire. We’ll also show you the Linux command line to help you solve CTF challenges and teach you some password cracking techniques. Make sure to come prepared with your laptop and a Kali Linux virtual machine!
Write Up/ Read Out Workshop
Writing pentesting reports and bug findings is equally as important as finding the bugs themselves. This workshop will discuss note taking, appropriate level of detail, writing up reports and how to do an executive level readout.
CONTEST & PARTIES
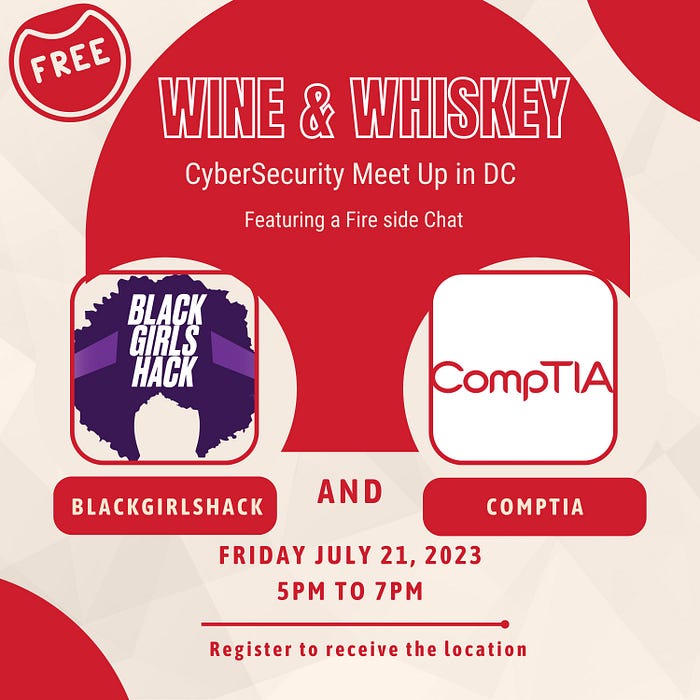
📅 Date: July 21,2023
⏰ Time: 5pm to 7PM
BlackGirlsHack presents Wine and Whiskey DC event sponsored by CompTIA. The event will be in Washington DC and will include food and drinks and a fireside chat with BGH leadership.
Do you live in the Washington D.C, Maryland, or Virginia area? Do you want to network with other professionals in cybersecurity or the technology field? BlackGirlsHack and CompTIA are partnering for an exciting meet-up, so mark your calendars!


Due to the con’s smaller size and newness to the scene, we wanted to highlight these two special events! Repeat & More Detailed Info are listed in our CTF Guide & Party Guide respectively.

DCG 201 TALK HIGHLIGHTS FOR #SQUADCON 2023 (EST)
This is the section where we have comb through the entire list of talks on both days and list our highlights for the talks that stand out to us. Note that this does not invalidate any talks we didn’t list, in fact, we highly recommend you take a look at the full convention schedule beforehand and make up your own talk highlight lists. These are just the talks that for us had something stand out, either by being informative, unique or bizarre. (Sometimes, all three!)

This talk explores the journey of pursuing and navigating executive leadership, focusing on overcoming challenges and driving success in today’s dynamic and competitive market.
This talk specifically targets security leaders and explores the detrimental effects of a lack of vision or direction on employee burnout. Over 35% of burned-out workers experience uncertainty about their goals and how to achieve them, leading to anxiety and a sense of aimlessness. Security leaders play a crucial role in mitigating burnout and fostering a healthier work environment. The talk provides strategies for security leaders to provide clear vision, establish goals, and combat uncertainty-induced stress among their teams. By creating a supportive work environment and promoting leadership accountability, security leaders can enhance employee resilience and decrease burnout rates. Attendees will gain insights into the correlation between uncertainty, burnout, and organizational performance, and learn practical strategies for fostering a positive work environment tailored to the unique challenges of the security field.
The very idea of public speaking strikes fear into the hearts of even the bravest people, creating clammy hands and pounding hearts. But when fear of speaking keeps diverse voices and perspectives off Security conference stages, the lack of diversity and inclusion in the Security industry is reinforced by the absence of those voices.
Attendees will take away effective and actionable techniques to ensure that they fearlessly crush it and hone their public speaking skills. More specifically, how to rehearse for talks and other preparation.
Yes, another talk about preparing and dealing with ransomware. Just sit back and listen.
Many cloud security breaches start from implementation mistakes: whether it be bad coding practices, misconfiguration, etc. Before (best case) your security team or (worst case) an outside attacker finds them; how can you be proactive about finding and fixing common security mistakes?
This talk explores my preliminary thoughts about AI as a site of knowledge production and its implications for everyday people who seek to understand Black History. How accessible is Black History within the AI? How accurate is Black History within AI? What kind of tools/products could be useful in future iterations of this technology? Why do such questions matter?
Modern ransomware has become synonymous with some of the most devastating cyber attacks of our time.. But it hasn’t always been so. 30 years ago, ransomware was born as a wild scheme, devised by a man armed with 10,000 floppy disks and a virus. How has this evolved into the most impactful form of cybercrime today, and what can this surprising, untold history teach us about our present and future?
(ALSO AT BSIDES LV)
As AI becomes integral to business operations and cybersecurity tooling, the technology will dramatically reshape infosec teams’ processes and impact its people.But the crucial question remains, who will be the guiding force when these decisions are made? The existing gatekeeping issues coupled with the prevalent homogeneity in the leadership within AI and cybersecurity realms threaten to compound challenges for defenders from traditionally marginalized communities. In this talk, we will challenge this potential future state and provide a way forward for today’s defenders.
With the technology terrain increasingly veering towards AI, what does it take to ascend into a leadership role? Is it a deep dive into specialization or a broader approach via generalization? The aim of this talk is to empower you to take the initiative, provide you with a blueprint of today’s AI security landscape, and show you how to develop strategies to lead and influence the integration of AI into business and security tools within your organization.
This talk is not just about informing you; it’s about empowering you to become a leader as we step toward the era of AI-driven cybersecurity risks and defense.
Throughout time, folks looking for love (or lust) found and formed relationships with one another by leveraging community networks — relatives, clergy, nosy neighbors, even matchmakers. For the first time in human history, our relationships are no longer being mediated by other people but rather by technology. From social media and circuit boards to algorithms and artificial intelligence, tech is influencing the way humans form intimate bonds in ways never seen before. In this talk, Certified Sex Therapist and Clinical Sexologist Stefani Goerlich will talk about the emerging themes in mental health and relationship counseling and how these have been influenced by the explosion in SexTech, online dating, and the pervasiveness of erotica, among other topics. She will explore the potential positives and emerging drawbacks of transitioning one’s most intimate relationships into the cloud. This session offers a framework for health and safety for the first generation of digital natives entering into adult relationships.
I am going to talk about Content Engineer being a new and thriving career within cybersecurity. I will also talk about the state of cybersecurity and how can we become better professionals.
The Unique Advantages of Women in Tackling Cybersecurity Problems

Now, he engages in full time philanthropy, focusing on helping and protecting the people who help and protect our country. That includes cybersecurity, trustworthy journalism, and support for military families and veterans.
He was greatly influenced by his Sunday School teachers who had escaped the Holocaust, set his moral compass, and taught him to treat people like you want to be treated, and how to know when enough is enough.
Craig might be #nerdpatient0, having worn plastic pocket protectors, thick black glasses, taped together, and being poorly socialized. He remains poorly socialized but can simulate social skills as needed.
He originally intended to study Large Language Models like ChatGPT in the early seventies, but decided he wanted gainful employment, and went into software development.
Since then, he’s worked at IBM, Charles Schwab, Bank of America, and worked at craigslist for about 25 years. He retired from craigslist customer service job some years ago.
He ascribes any success to accidentally being in the right place at the right time, making him the Forrest Gump of the Internet.

A pentest is only as good as the pentester! For a pentester to successfully cover a client’s needs, it’s important that a thorough pentesting methodology is utilized. Methodologies typically expand as we gain more hands-on experience. In this talk, we’ll cover elevating our methodology as pentesters within a shorter time frame while also addressing the barriers that can get in the way of learning new tools & techniques that will ultimately expand our methodology.

iOS is considered to be one of the most secure operating systems in the world.
Apple puts a lot of effort to maximize security on their platforms
They are building layers on layers of protections in order to make exploitation much harder
But how are they doing it?
In this talk we will go through some of iOS security mechanisms and the way they complete each other for maximum coverage.
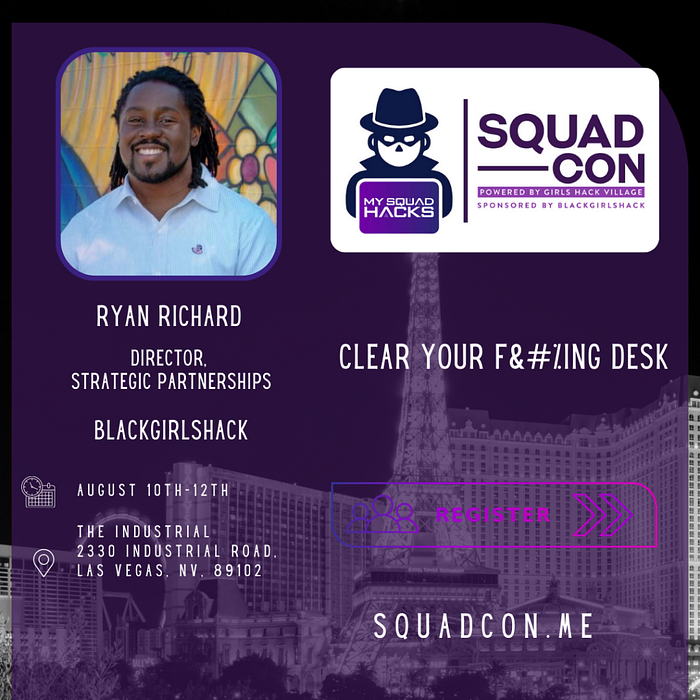
How our most mundane security policies can lead to some of our most meaningful security maturity wins? Good habits build on one another, just like bad habits. Our good habits tend to encourage other auxiliary good habits. A neat space, cultivates a neat mind. In this talk, we will explore how neatness is the under celebrated linchpin of a mature cybersecurity culture.

CONTINUE TO: HACKER SUMMER CAMP 2023 — Part Nine: DEFCON 31
