HACKER SUMMER CAMP 2023 GUIDES — Part Five: The Diana Initiative

Welcome to the DCG 201 Guides for Hacker Summer Camp 2023! This is part of a series where we are going to cover all the various hacker conventions and shenanigans both In-Person & Digital! This year in 2023 somehow bigger than it was in 2022 and thus we will have a total of 15 guides spanning 3 Months of Hacker Insanity!
As more blog posts are uploaded, you will be able to jump through the guide via these links:
HACKER SUMMER CAMP 2023 — Part One: Surviving Las Vegas & Virtually Anywhere
HACKER SUMMER CAMP 2023 — Part Two: Capture The Flags & Hackathons
HACKER SUMMER CAMP 2023 — Part Three: SummerC0n
HACKER SUMMER CAMP 2023 — Part Four: Zero Gravity by RingZero
HACKER SUMMER CAMP 2023 — Part Five: The Diana Initiative
HACKER SUMMER CAMP 2023 — Part Six: BSides Las Vegas
HACKER SUMMER CAMP 2023 — Part Seven: Black Hat USA
HACKER SUMMER CAMP 2023 — Part Eight: SquadCon by Black Girls Hack
HACKER SUMMER CAMP 2023 — Part Nine: DEFCON 31
HACKER SUMMER CAMP 2023 — Part Ten: USENIX + SOUPS
HACKER SUMMER CAMP 2023 — Part Eleven: Chaos Computer Camp
HACKER SUMMER CAMP 2023 — Part Twelve: Wikimania 2023
HACKER SUMMER CAMP 2023 — Part Thirteen: HackCon XI
HACKER SUMMER CAMP 2023 — Part Fourteen: Blue Team Con
HACKER SUMMER CAMP 2023 — Part Fifteen: Hack Red Con
HACKER SUMMER CAMP 2023 — Part Sixteen: SIGS, EVENTS & PARTIES

The Diana Initiative 2023 Convention
Date & Time: Monday, August 7th 8:00pm PST — 9:00pm PST
Location: Westin Las Vegas Hotel & Spa (160 E Flamingo Road,
Las Vegas, NV 89109)
Website: https://www.dianainitiative.org/
Tickets: https://www.eventbrite.com/e/the-diana-initiative-2023-tickets-500510499377
Virtual Platform(s): N/A
Schedule: https://www.dianainitiative.org/event/event-schedule/
Live Streams:
N/A
Virtual Chat: N/A
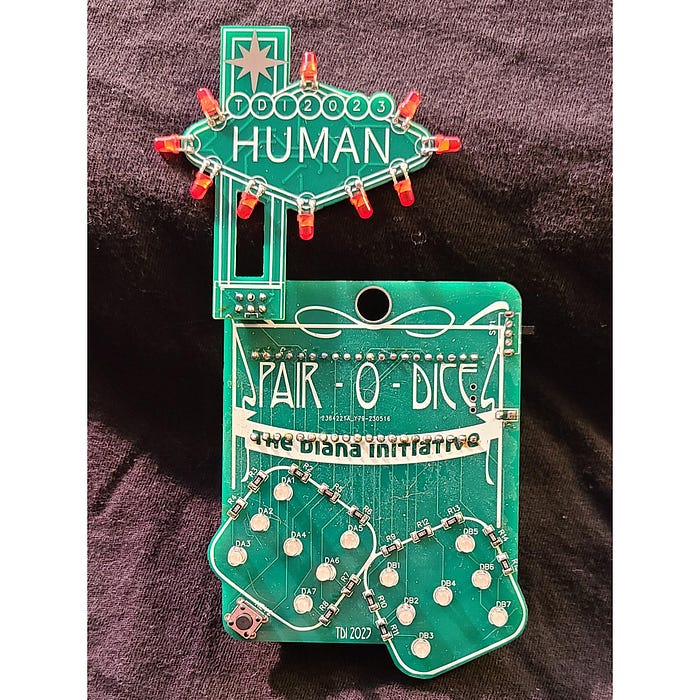
Affordability: The Diana Initiative 2023 is FREE for students, veterans, unemployed and underemployed people. They have many options for various minority demographics which includes in person attendance to the conference Monday August 7, 2023 in Las Vegas. All these options do not include an electronic badge (available as an add-on), swag, shirt, or meals. These are paid add on’s unless you get a 1337 Badge $204.80 or above. Kids under 18 get in for FREE.
Code Of Conduct: https://www.dianainitiative.org/about/policies/
A diversity-driven conference committed to helping all underrepresented people in Information Security. The Diana Initiative features multiple speaker tracks, villages with hands-on workshops, and multiple social event.
Back for the 7th year, The Diana Initiative is hosting a one-day diversity-driven conference committed to helping all underrepresented genders, sexuality, races and cultures in Information Security. The Diana Initiative features multiple speaker tracks, fully expanded villages with hands-on workshops, and women-led cybersecurity trainings.
This year our theme is “Lead The Change.” Our discussions will focus on impactful ways large and small that each of us can advance information security, diversity initiatives, and ourselves, both professionally and personally — whether gender, race, sexuality, skill level and neurodiversity.
Originally known as TiaraCon, this matured and harden version of the original concept has evolved so much over time that it has emerged from DEF CON’s shadow and has grown into it’s own thing. As a group that is made up and led by various minorities on the fringes of society (New Jersey standard approved), we completely understand the need and creation of a space to discuss issues in a demographic of technology-minded people. If you identify as a woman, an ally or want to learn amazing technology skills while getting a broader social impact picture, this convention is for you.
HOW TO INTERACT VIRTUALLY FOR DIANA INITIATIVE WITHOUT LOOKING LIKE A SCRUB
STUDENT TICKETS
ABOUT THE VENUE

Westin Las Vegas Hotel & Spa (160 E Flamingo Road,
Las Vegas, NV 89109)
Use our group link to book your stay (at least 2 days) and save. Space is limited — [Book your room today!]
You must book before Friday July 7, 2023 — all rooms booked in our room block get 2 free human badges at check in.
If you run into problems (like arriving too early or staying too long for our block) feel free to book [at the Westin directly] and [email our registration staff] your reservation number.
If you book through a service other than TDI, just [email our registration staff] your reservation number so we can let Westin know you’re with us.
Hotel check in is 4:00 PM (PST) / Check out is 12:00 PM (PST). Hotel cannot guarantee early check-in without room guarantee and payment for the night prior. Late check-out request must be approved by front office on the day of departure. Hotel will store attendees’ baggage at no cost, based on availability.
Guest must cancel room reservation 72 hours prior to confirmed arrival date to avoid a non-refundable cancellation fee equal to one night’s room and tax.
A mandatory Destination Fee will apply to all guest rooms. This fee is $35.00 (plus 13.38% tax) per room, per day. .
Group attendees can renew with a special 20% discount at Hibiscus Spa. Relax and rejuvenate in our spa including soothing treatment rooms, and comfortable locker room. Choose from many spa treatments and services to help you look your best and feel rested. To confirm appointment attendees may call 702–836–5945.
Adversary Adventure Game
The Diana Initiative excited to bring you the Adversary Adventure Game from Adversary Village!
Choose your own path in this single player game — as a Adversary or a Defender
See how your path progresses by making choices until it reaches the conclusion:

Career Fair & Village
10:00pm — 4:30pm
The Career Fair is a dedicated space for the Diana Initiative sponsors to have HR and Recruiting Personnel at their booths to discuss specific opportunities they have with a potential for same day screening interviews
The Career Fair will be a walk up event, no RSVP’s required!
Career Village will offer advice and resources below for building both your professional career and yourself. These life skills can help you keep your professional career alive and healthy! These available services will be offered during and around talks about personal development during the conference.
- Networking Session
- Resume Reviews
- Mock Interviews
- Career Coaching
Career Village 10am — 5pm with a lunch break 12:30pm–1:30pm
Career Village will offer advice and resources below for building both your professional career and yourself. These life skills can help you keep your professional career alive and healthy! These available services will be offered during and around talks about personal development during the conference.
- 8:00am–8:45am — No-Host Early Bird Career Networking Session
- 10:00am–1:00pm — Resume Review, Interview Coaching, Career Coaching & Other Career assistance
- 1:00pm–1:30pm — Lunch Break for CV
- 1:30pm–4:30pm — Resume Review, Interview Coaching, Career Coaching & Other Career assistance
We will take walk-ups or sign-ups throughout the day for whatever career assistance you need, no RSVP needed!
(All times pacific)
Career Village Resources
Resume templates, salary information, and other resources.
Don’t miss your career village lead John hosting Cyber Trivia at the social after the event ends!
Career Fair & Job Board
This year we will be having a [Career Fair]!
We would love to have someone donate some (branded) supplies to our Career Village — If you want your logo on some of our stuff we are seeking “Hiring/looking” bracelets, and Career Village badge ribbons. Please reach out!

Lockpick Village
10:00pm–5:00pm with a lunch break 12:30pm–1:30pm
Lockpick Extreme is back again with us hosting our lock picking village!
Come in between and learn how to pick, as well as browse some items available for purchase!
Maker Village
10:00pm–5:00pm with a lunch break 12:30pm–1:30pm
- Learn to solder
- “Stitch & Bi**H” hangout area
- Sticker exchange table

ABOUT WORKSHOP REGISTRATION
Please note this is concurrent to the conference.
This is available as an add-on when you purchase your ticket
If you have previously purchased a ticket and wish to add the workshop please do the following:
- Visit our ticket page https://www.eventbrite.com/e/the-diana-initiative-2023-tickets-500510499377
- Click “Get Tickets”
- Scroll down to “Purchasing add-on only” and select 1 from the drop down menu
- Scroll down to the Workshop you want to attend and select 1 from the drop down menu
- Click “check out”
- Please use the same email as you purchased your original ticket with.
- (Sorry we can’t just add to eventbrite orders!)
If you registered for this workshop and can no longer attend, or if you can not afford the workshop, please let us know registration@dianainitiative.com

Blackhoodie Reverse Engineering Workshop
Monday August 7, 2023
- 9:00am–1:00pm — Theory
- 2:00pm–6:00pm — Practice
Course Description
In this course, we will explore the inner workings of software, while equipping you with the tools that you need to unravel its hidden mysteries. We will learn what happens under the hood of compilation, diving into the process of transforming high-level code into low-level assembly language. We will see how to use Ghidra, a powerful tool which can be used to decipher and comprehend disassembled code, empowering you to understand its inner workings. In the lab component of the course, we will apply our newfound knowledge to reverse engineer cryptographic algorithms through practical exercises.
Instructors
Mathilde Venault is a security researcher at CrowdStrike, specializing in the Windows operating system. While her work mostly focuses on malware analysis and EDR detection capabilities improvements, she also likes reverse engineering undocumented Windows mechanisms. Mathilde has spoken at multiple conferences to share her findings such as Black Hat USA, REcon and c0c0n, for which she is now a review committee member. As a typical French, she’s always up to share a meal with some bread and cheese.
Bea Venzon stumbled into the world of reverse engineering by pure chance, thanks to a chance encounter at a networking event. Sitting beside a security researcher and getting drawn into a captivating conversation, Bea discovered a passion she never knew she had. Currently Bea is a Security Researcher at CrowdStrike, where she focuses on tracking and analyzing botnets, information stealers, and ransomware. As a self-proclaimed forever student, Bea is pursuing her Master’s Degree in Computer Science at Georgia Tech to expand her knowledge and skills to better combat evolving cyber-threats.

Why women only:
Because a girl-to-girl conversation is so much more fruitful than a full classroom with only one or two women hiding in the corners. I’ve done so many things in my life where I was the only girl among X other participants, and I promise I’ve been hiding in the corners more than once.
For the gents it might not be that obvious, but it is not easy for young females who haven’t yet found their place in life to walk into a class room, a university lecture, an office or a conference room full of men. Who, generally speaking, very often very well seem to know their place.
I’ve had girls in my classes before, hiding and holding back although I am so certain they would have been capable to be so much better than what their final results showed. So yeah this will be women only, for every female should feel welcomed and encouraged to do her best and get the most out of it.
Prerequisites for most classes
- Born a woman or identifying as a woman
- Computer science background in a sense you understand programming logic, how a processor works and how an operating system works
- A virtual environment setup containing the required tools (Ghidra, Windbg, the SysInternals suite, etc). A tutorial will be provided in the week prior to the workshop to help with the setup procedure.
- Guts
- (Our classes mean learning a lot in a very short time)
BlackHoodie’s Mission
BlackHoodie is a series of technical trainings aiming to attract more women to the field of cyber security
Our events are women-only, except if individual organizers state otherwise
Whether introduction level or advanced, classes are always challenging
All of our events are free to attend
We do not exert any preference in education level, occupation or corporate affiliation of attendees
BlackHoodie is dedicated to serve the community, we aim to integrate, not separate
BlackHoodie is independent, and cannot be leveraged to promote anything but its own mission
We seek quality over quantity, in number of classes and attendees
We also support/encourage attendees to start giving technical trainings thereby providing a platform to build their confidence

Introduction to Active Directory Exploitation
Monday August 7, 2023–10:00a-12:00p
When attackers successfully gain a foothold within an environment, one of the systems that they typically target is Active Directory (AD). AD acts as a centralized access management system and compromising it would typically give attackers the necessary access to achieve their objectives.
Each AD installation around the world is unique and the main problem that most AD environments face is insecure configuration. Due to their nature, these misconfigurations usually cannot be fixed as part of a vendor update or patch. Instead, these misconfigurations need to be identified and fixed as part of a targeted assessment in each environment. Therefore, it is important for defenders to know how to identify these issues and what remediation steps are needed to secure the environment.
The purpose of this entry-level workshop is to introduce the participants to the fundamental concepts relating to attacking Active Directory. To achieve this, we will be performing a hands-on security assessment against an AD environment. We will start from a compromised user and work our way through the domain until we complete our operational objectives. During the lab we will:
- Collect AD data using open-source tools, such as SharpHound.
- Identify attack paths using BloodHound.
- Exploit multiple misconfigurations using well-known tactics, techniques, and procedures (TTPs).
This training is aimed at people looking to start with Active Directory security. There are no specific requirements for attendees but a basic understanding of fundamental Active Directory concepts such as domains, users and groups would be beneficial.
If you are looking for a hands-on lab experience, you will need to bring a laptop capable of connecting tothe internet over WiFi. The lab environment will be accessible remotely using a web browser. If you do not have a laptop and still want to attend, the lab instructors will be demonstrating the labs via a screen share.
Attendee Equipment Needed
For a hands-on lab experience, you will need to bring a laptop capable of
connecting to the internet over WiFi. If you do not have a laptop and still want to attend, the lab instructors will be demonstrating the labs via a screen share.
After the AAR: Turning Lessons Learned into Actions
Monday August 7, 2023 2:00pm–3:30pm
Your organization just completed a cyber tabletop exercise. Now what?
Things change quickly in a real-life crisis scenario, and flexibility is critical for strong cyber resilience. In this workshop, participants will brainstorm how to improve its cyber processes and policies after a cyber tabletop exercise. Participants will role-play as C-suite decision-makers in a fictitious organization and develop action items to enhance their Tactics, Techniques, and Procedures (TTP).
Workshop Outline
- At the beginning of the workshop, the facilitators will brief participants on a fictitious Cyber Tabletop Exercise, including the goals, observations, potential risks, gaps, vulnerabilities, and Lessons Learned.
- Once the facilitators have provided this information, it’s the participants’ turn to have fun and discuss how to turn the Lessons Learned into an After Action Report (AAR) in small groups.
- All participants will represent the same company. However, the facilitators will divide participants into groups and respond to the cyber Lessons Learned.
- Each group will receive a different list of resources to test how they prioritize business decisions, budget priorities, personnel resource needs, internal due dates, and other factors that will improve business operations.
- For example, some groups will be better funded than others, others will have more “senior” people, and others will be consultants who can be “hired” if a company has the budget to do so. Also, facilitators can manipulate this environment at any time. For example, they can swap the budgets of each group or give a group a Legal department if they do not have one.
- At the end of the workshop, participants will explain to the larger group how they strategically prioritized to help their fictitious organization become more cyber resilient.
Skill Level
Anyone is Welcome
Attendee Equipment Needed
None

DCG 201 TALK HIGHLIGHTS FOR DIANA INITIATIVE 2023 (PST)
This is the section where we have comb through the entire list of talks on both days and list our highlights for the talks that stand out to us. Note that this does not invalidate any talks we didn’t list, in fact, we highly recommend you take a look at the full convention schedule beforehand and make up your own talk hilight lists. These are just the talks that for us had something stand out, either by being informative, unique or bizarre. (Sometimes, all three!)
Shifting Security Everywhere
KEYNOTE • 9:00am — 10:00am
As an Application Security professional, you may feel that marketing has ruined the meaning of ‘shift left’. It was supposed to mean ‘starting security as early as possible in the SDLC’, but was transformed into “buy our product, put it in your CI/CD, then your apps will be secure”. But we can’t just throw a bunch of tools into a CI/CD and call it a day. With this in mind, let’s focus on comprehensive programs, developer buy-in, and making security work for the entire business, by shifting security everywhere.
Tanya Janca, also known as SheHacksPurple, is the best-selling author of ‘Alice and Bob Learn Application Security’. She is also the founder of We Hack Purple, an online learning community that revolves around teaching everyone to create secure software. Tanya has been coding and working in IT for over twenty five years, won countless awards, and has been everywhere from public service to tech giants, writing software, leading communities, founding companies and ‘securing all the things’. She is an award-winning public speaker, active blogger & podcaster and has delivered hundreds of talks on 6 continents. She values diversity, inclusion, and kindness, which shines through in her countless initiatives. Advisor: Nord VPN, Aiya Corp Faculty: IANs ResearchFounder: We Hack Purple, OWASP DevSlop, #CyberMentoringMonday, WoSEC
How I Learned to Stop Worrying and Build a Modern Detection & Response Program
Track 2 • 10:00am — 11:00am
You haven’t slept in days. Pager alerts at all hours. Constant firefights. How do you get out of this mess? This talk gives away all the secrets you’ll need to go from reactive chaos to building and running a finely tuned detection & response program (and finally get some sleep).
Gone are the days of buying the ol’ EDR/IDS/NGAV combo, throwing some engineers on an on-call rotation, and calling it your incident response team. You need a robust and comprehensive detection and response program to fight modern day attackers. But there’s a lot of challenges in the way: alert fatigue, tools are expensive, hiring talent is impossibly difficult, and your current team is overworked from constant firefights.
How do you successfully build a modern detection and response program, all while riding the rocket of never ending incidents and unforgiving on-call schedules?
This talk addresses the lack of a framework, which has led to ineffective, outdated, and after-thought detection and response programs. At the end of this talk, you will walk away with a better understanding of all the capabilities a modern program should have and a framework to build or improve your own.
Allyn Stott is a senior staff engineer at Airbnb on the infosec technology leadership team, where he works on threat detection and incident response. Over the past decade, he has built and run detection and response programs at companies including Delta Dental of California, MZ, and Palantir. Red team tears are his testimonials.
Breaking the Mold: Inspiring Stories of Two Women Who Hacked Their Way into Cybersecurity from Non-Technical Backgrounds
Track 3 • 10:00am — 11:00am
Have you ever heard of women breaking into cybersecurity form non-technical backgrounds with literally no technical experience to lean on? Have you ever heard of them doing it TWICE!? It’s no secret how difficult breaking in to cybersecurity is this talk will feature the inspiring stories of two women who successfully broke into, learned, and excelled in cybersecurity from non-technical backgrounds. One is now a well-known ethical hacker and Purple Team pioneer, who created her own niche. The other is just starting out in her GRC career and is already making waves in the world of Zero Trust. They will share their experiences, including the challenges they faced, the steps they took to learn cybersecurity skills, and their journeys to their current roles. The talk will compare and contrast their journeys, highlighting the similarities and differences and how their non-technical backgrounds influenced their paths. Attendees will gain valuable insights and advice on how to pursue cybersecurity careers from non-technical backgrounds
Maril Vernon, Senior Application Security Architect at Aquia. What does that mean? Maril (@SheWhoHacks) or the “One Woman Purple Team’’ is an award-winning Ethical Hacker and Purple Team Program Manager — a niche in offensive security testing that has recently gained popularity demonstrating cyber resilience in the advanced threat landscape.
Maril is also Co-host of The Cyber Queens Podcast, an all-female podcast aimed at increasing female and LGBTQ diversity in cybersecurity. She also volunteers as the COO of Teach Kids Tech, a non-profit organization with the goal of getting technology and educational resources to children in underprivileged communities and increasing technical capability and cyber awareness in tomorrow’s workforce. Maril has been named one of the ‘Epic Women in Cyber,’ “Top 10 Women Championing Cybersecurity,” and is a 2023 Women’s CyberJustu Award nominee. She is also an SME and contributing writer to CSO Online magazine on cyber resilience, Red Team best practices and industry trends.
Mackenzie “Mack” Wartenberger, has successfully made a mid-career pivot from being an elite NCAA collegiate athletics coach, to an up-and-comer in the field of cybersecurity. In just her first six months as a cyber security technician, Mack grew from a GRC Specialist role into a Zero Trust Security Architect, for both government and commercial services, as well as in SaaS Governance. Mack’s experience and skills are the result of being the inaugural apprentice to graduate from the Aquia Accelerator Program, a paid apprenticeship program started by cybersecurity firm, Aquia Inc, that is receiving national attention for focusing on spinning up new cyber security specialists from underrepresented populations, who bring strong soft skills and new perspectives (but non-technical backgrounds) to the cyber security space.
Tag, You’re It: How to Get Started with RFID
Track 1 • 11:00am — 11:30am
From building fobs to credit cards to clothing tags, RFID technology is all around us in daily life. But how does it work? And how can I manipulate it? This talk aims to share what I learned when I asked those questions and dove into the world of RFID. I will break down the basics of RFID technology, explore real-world applications, and give an overview of different tools for hobby, research, or Red Team use. Audience members will leave with a foundational knowledge of RFID and how to get started with the technology.
Clarissa Bury is a cybersecurity professional and RFID enthusiast who first got excited about this particular type of cybersecurity after wandering into the RF Hackers Village at her very first BSides. She is currently a cybersecurity consultant with CrowdStrike where she gets to play the bad guy by creating custom tabletop exercises. She previously worked as the Security Engineer for a software and services company where she focused on improving security architecture across the organization and its federal contracts.
No Women in Security Group? No Problem
Track 3 • 11:00am — 11:30am
Does your organization lack a Women in Security employee resource group? No problem. In this session we will follow basic steps to establish a Women in Security group, obtain executive sponsorship, and drive engagement amongst members. Learn how to establish leadership, create a charter and yearly goals, all while creating a supportive and inclusive environment for women in the security profession. All this can be done virtually and with little budget. Join this session to learn more!
Katelyn Falk is a high-energy technical security program manager from Seattle with 11+ years of experience. Recently named one of 2023 SIA Women in Security Power 100, Katelyn is a co-founder of Zoom’s “Women in Security” employee resource group, which is aimed at creating a dedicated space for women in, and aspiring to be in, security. Her day job consists of accelerating Zoom’s New Product Introduction Security testing. Katelyn has a passion for the recruitment and retention of women in the security field and works to provide resources and support to Zoom’s Women in Security group. She is raising a tiny human, dog, and cat in her spare time.
Mischievous Goots: Atomic Testing and Gootloader
Track 1 • 11:30am — 12:30pm
Testing out detection capabilities before putting them into operation is important, even if you don’t have a big production environment to protect (yet). That’s where Atomic Red Team comes in! Together, we’ll talk about an open source library of prebuilt tests to evaluate your environment’s visibility and how you can make your own environment to test them in. We’ll walk through a real world threat (Gootloader!), how it works, and how we can test each of its behaviors to see how our environment stands up against it. Then, we’ll talk a little about the differences between this and live environments. If you want to learn about testing detectors in live environments, this is for you!
KillrBunn3 started her career as a student tinkering with old computer hardware, fascinated with programming logic and evidence left on computers after attacks. She first began studying malware and threat intelligence when working in a startup SOC, learning more as she participated in new incidents, trained new analysts, and published new reports on varying industry topics. Today, she uses her technical background to create content that helps educate the information security community.
Unveiling Failures and Forging Change: Combatting Gender Disparities in Cybersecurity for Marginalized Genders
Track 3 • 11:30am — 12:30pm
In this impactful talk, we expose the failures of the cybersecurity field that perpetuate gender disparities and hinder progress for marginalized genders. We delve into the intersectional challenges faced by individuals, recognizing the compounding factors of race, ethnicity, sexuality, and disability. Empowering attendees with actionable strategies, we discuss allyship, advocacy, and amplifying marginalized voices as crucial steps to drive change. Additionally, we address the decreasing support for diversity in red states and the potential impacts of legal changes, like the overturning of Roe v. Wade. By building coalitions and embracing resilience, we encourage individuals to take a stand, contribute to inclusivity, and support initiatives prioritizing diversity, equity, and inclusion. Together, we can dismantle barriers, foster dialogue, and create an empowering cybersecurity field that values and embraces the brilliance of all individuals.
For over ten years, Chloé Messdaghi has advised and developed impactful solutions that have driven growth and innovation while transforming security teams to become resilient. Her work has helped businesses unlock opportunities to enhance trust, mitigate risk, and become purpose-driven. Chloé is a public speaker at major conferences and a trusted source for national and sector reporters and editors, as well as her research, op-eds, and commentary have been featured in numerous outlets, from Forbes and Business Insider to Bloomberg, and TechRepublic. Her work has earned her many distinctions, including being listed by Business Insider and SC Media as a Power Player in cybersecurity.
What the Yandex Leak Tells Us About How Big Tech Uses Your Data
Track 2 • 1:30pm — 2:30pm (ALSO AT BLACK HAT USA & BSIDES LV)
In late January 2023, almost 45 GB of source code from the Russian search giant Yandex was leaked on BreachForums by a former Yandex employee. While the leak itself did not contain user data, it reportedly contained the source code for all major Yandex services, including Metrika, which collects user analytics through a widely used SDK, and Crypta, Yandex’s behavioral analytics technology. While there has been lots of speculation about what big tech companies can do with the massive amounts of data they collect, this is the first time outsiders have been able to peek behind the curtain to confirm it, and what we’ve found is both fascinating and deeply unsettling.
Kaileigh McCrea is a Privacy Engineer at Confiant, where she researches violations of privacy regulations and user rights in ad tech and builds tools to detect them, and consumes huge amounts of cookies. Before joining Confiant she was a software engineer at Swing Left and Vote Forward where she helped volunteers send over 18 million GOTV letters in the 2020 General Election. Her background includes software engineering, comedy writing, and politics, and when she’s not working, she is usually reading excessive amounts and hanging out with her dog.
You’re Busted! Practicing IR Techniques at Home
Track 3 • 2:00pm — 2:30pm
As a fledgling digital investigator, I was always on-the-lookout for opportunities to hone my skills. I had stumbled into security from a career in technology and education, and outside of work I sought opportunities to practice my IR skills anywhere I could.
Little did I know I had my very own APT group operating in my home environment — a set of stealthy, sneaky children obsessed with watching YouTube. These Advanced Persistent (pre) Teens had little regard for device time limits or house rules.
In this talk, I’ll share my journey of Incident Response in the home, tracking violations of the family acceptable use policy and unauthorized access to systems. I’ll describe the exploration and discovery of my children’s unauthorized digital activity and share how I applied IR processes, collected the forensic evidence, and conducted browser forensics and log analysis to bust them good.
Sarah Cox
Trellix
Principal Instructor
Spilling the TEE
Track 1 • 2:30pm — 3:00pm
In the rapidly evolving digital world, security and privacy are (or at least should be) more important than ever. The proliferation of digital devices and the increasing velocity of sensitive data have necessitated the development of better and more secure ways of protecting information. A Trusted Execution Environment (TEE) is one such solution, providing additional authenticable security for devices and applications. This talk will explore what a TEE is, what types exist, how they work, and their benefits and limitations. We will then consider the use case of rebuilding trust in women’s health tracking apps using TEEs.
Deirdre Cleary is a product engineer at Evervault, a Dublin based data encryption company. The first woman to join the engineering team, she has spent the past two years building tools that make it easier for engineers to put security first. Deirdre is passionate about taking complex ideas and making them accessible to everyone, an interest which led to her roles as instructor at Code First Girls and speaker at Stemettes.
Threat Hunting: More than blue, it’s a team sport
Track 2 • 2:30pm — 3:00pm
Threat Hunting are where some of the most badass blue team members I know spend their time — but what if there was a way to support our blue friends without actually being in the Blue Team? I want to take you beyond our beloved Defenders, and show you how many different domains can be involved in developing and tracking our threat hunts, creating repeatable workflows that involve a collaborative approach, and where different skills can be the difference in a successful hunt experience. Threat Modelling, Data Science and Project Management can be all the difference. This talk will help you “Lead the Change” by getting more expertise involved, accelerating learning, which lead to better outcomes for all involved.
Yianna Paris is an Offensive & Application Security specialist who loves to build things and find creative ways to break them. When I’m not developing attacks, I’m teaching how to protect against people like me. I bring red team curiosity into a collaborative approach by redefining purple by highlighting the value in perspectives beyond what we find traditionally red and blue. I’ve had a diverse background in technology — software engineering, computer science, teaching, designing, and co-founder of a business and I’ve always been interested in the human aspect of technology. Discovering how to improve security processes, tackling complex problems, and introducing secure software development practices. I love going detailed and technical, diving deep into problems when I’m doing vulnerability research, threat assessments, breaking video games, and even woodworking! I’m determined to uplift people with diverse perspectives in Security, while learning from everyone I meet.
Come Together: A framework for a shared security language
Track 1 • 3:00pm — 4:00pm
Have you ever tried to do data analysis on all your security issues — results from threat models, pen tests, risk assessments, security incidents, detections, etc. — only to find that no one is using consistent language? Does this impede conversations with product teams on issues, both slowing down development and resolution of issues? How do you bring everyone together? We’ll talk about how we approached this problem while staying focused on our objective to enable everyone to speak a common language to inform product decisions and solve security problems at scale. This talk will walk through the problem statement while engaging the audience through a simple exercise, walk through our approach and outcomes, where we are going next, and provide actionable steps for other security teams looking to replicate this approach.
Lea Snyder is a Principal Security Engineer at Microsoft. She’s worn a lot of hats over her career and mostly worked for companies that begin with the letter ‘A.’ You can read more at: https://tldrsec.com/guides/staffeng-security/stories/lea-snyder. Outside of work she can be found organizing security conferences or enjoying all the PNW has to offer.
Human-Centered Security: Building for Accessibility in Security
Track 2 • 3:00pm — 4:00pm
Security and accessibility are essential to a user’s experience. However, these features are often developed in silos which can lead to vulnerabilities and exploits. An example is the Anubis banking trojan which utilizes the Android’s Accessibility Suite to execute clickjacking attacks. Another is AI bots like ChatGPT posing as a blind person to circumvent anti-bot checks.
By addressing accessibility as part of security, we can create more inclusive experiences for all users. Human-centered security focuses on the needs of individuals and seeks to understand their perspectives and requirements. Through inclusive design, we can ensure that everyone will be able to use digital products and services, including those with disabilities.
Cynthia Taylor is the Founder of WiCyS Interest Group, “People with Disabilities and Caregivers.” She graduated in July 2022 with her Masters in Cybersecurity and Information Assurance from WGU, an NSA Center of Excellence.
In September 2022, she completed Florida’s Center for Cybersecurity’s NSA-funded program, Cyberworks. She’s a 2019 Disability:IN Next Gen Leader and worked in Accessibility at Whatsapp and Vulnerability Management & Application Security for Voya Financial.
She has over 10 years of IT experience and currently works at Southwest Airlines in Application Security.
The Virtuous Cycle of Hunt-Focused Purple Teaming
Track 1 • 4:00pm — 5:00pm
In many organizations, defenders are siloed and operate almost independently from offensive security teams. Why should tasks such as novel attack technique research, custom payload creation, detection capability assessment, and hypothesis-based hunting all be disparately executed?
What if we can reduce duplicate effort and achieve all of this through a holistic approach? In this talk, we will take the listener through our journey to simulate, detect, and proactively hunt for malicious OneNote use, which was exploited widely as an infection vector in early 2023 campaigns.
This case study will illustrate the effectiveness of the cyclical threat hunting methodology we adopt at , powered by insights gathered from cross-team collaboration. For example, we will highlight how pairing blue teamers and red teamers on an exercise enables a positive feedback loop where the blue teamer goes home with a comprehensive set of behavioral detection rules, and the red teamer armed with knowledge of how best to evade them.
Attendees will leave with an appreciation of the value of interconnected, purple-minded workflows in the detection engineering process, alongside actionable ideas for identifying outliers and reducing false positives using data-driven techniques.
Poppaea McDermott has been a Threat Hunter in WithSecure’s Countercept Detection and Response Team since 2021. Prior to her current role, she was a member of the Ethical Hacking team in PwC UK’s Cyber Threat Operations pillar.
She is particularly interested in exploring how data science techniques can be leveraged in threat hunting and detection engineering workflows.
Jojo O’Gorman has been threat hunting for WithSecure’s Detection and Response Team for the last 2 years. Her time is split between data-driven threat hunting, incident response, detection engineering and threat emulation. Passionate about encouraging collaboration, she runs successful internal purple team exercises, bringing together blue and red teamers to improve the service through their shared technical knowledge and practical experiences.
The Why and What it Took to Become an Expert Pentester
Track 3 • 4:00pm — 5:00pm
Learn from a panel of pentesters about how they entered into the profession and built a community to empower others to join in the fun (learning and earning). You will hear about how they have succeeded in this industry, one that is not easy to break into and where you might have to navigate non-technical challenges.
Becoming a part of the Pentester community can be daunting. Whether you are just starting out or have extensive experience in the security space, our panel of experienced Pentesters are ready to answer your questions and share their unique stories.
Gisela Hinojosa is a Cyber Security Manager at Cobalt with over 6 years of experience as a penetration tester. Gisela performs a wide range of penetration tests including, network, web application, mobile application, Internet of Things (IoT), red teaming, phishing and threat modeling with STRIDE. Gisela currently holds the Security+, GMOB, GPEN and GPWAT certifications. Before becoming a penetration tester, Gisela had 6 years of software testing experience which she utilizes as a penetration tester.
Elizabeth Ramirez is a privileged to manage an engaged community of professional and collaborative pentesters who use their technical, interpersonal and communication skills to secure global data and networks. I thrive in a positive and collegial environment that brings joy to our pentesters because they get to have fun doing what they do best, while continuously working together to solve security problems that affect both companies and individuals.
Hacker Summer Camp 101
Monday, August 7 • 8:00pm — 10:00pm
CONTINUE TO: HACKER SUMMER CAMP 2023 — Part Six: BSides Las Vegas
