
Welcome to the DCG 201 guide to Hybrid Hacker Summer Camp! This is part of a series where we are going to cover all the various hacker conventions and shenanigans at the end of July to the end of August both In Person & Digital! As more blog posts are uploaded, you will be able to jump through the guide via these links:
HYBRID HACKER SUMMER CAMP — Part One: Surviving Physical + Virtual Vegas
HYBRID HACKER SUMMER CAMP — Part Two: BSides Las Vegas
HYBRID HACKER SUMMER CAMP — Part Three: Ring Zer0
HYBRID HACKER SUMMER CAMP — Part Four: Black Hat USA
HYBRID HACKER SUMMER CAMP — Part Five: FuzzCON
HYBRID HACKER SUMMER CAMP — Part Six: DEFCON 29
HYBRID HACKER SUMMER CAMP — Part Seven: USENIX
HYBRID HACKER SUMMER CAMP — Part Eight: SIGS, EVENTS AND PARTIES

DEFCON 29
Date: Friday August 6th (12:30 PM EST) — Sunday, August 8th (8:00 PM EST)
Website: https://defcon.org/html/defcon-29/dc-29-index.html
Badge Firmware & Updates: https://defcon.org/signal/index.html
On-Site WiFi Registration: https://wifireg.defcon.org/
Location: Paris Las Vegas: 3655 S Las Vegas Blvd, Las Vegas, NV 89109
(877–603–4389), Bally’s: 3645 S Las Vegas Blvd, Las Vegas, NV 89109
(800–358–8777)
Platform(s): Discord via Twitch TV, YouTube using Restream.io in addition to DEF CON FORUMS
Android App: https://play.google.com/store/apps/details?id=com.shortstack.hackertracker&hl=en
iOS App: https://itunes.apple.com/us/app/hackertracker/id1021141595
Schedule: https://defcon.org/html/defcon-safemode/dc-safemode-schedule.html
Live Streams:
YouTube: https://www.youtube.com/user/BlackHatOfficialYT
Twitch: https://www.twitch.tv/defconorg
Chat:
Discord: http://discord.gg/defcon
Accesability: DEFCON 29 is HYBRID this year. The physical con will have $300 tickets purchaseable both in person and for the first time ever online. The virtual event part is a little more complicated. If you were involved in DEF CON Safe Mode last year, you should be grandfathered into the Discord. There were also a limited ammount of tickets online that are now sold out (came with physical badge.) With virtual access you can go to the different rooms, participate in contests, events, listen to DJs and watch talks. Primarily uses text to send messages, uses the system emoji, use reactions, and you can listen to audio and video in channels that support them. Virtual Badges can upgrade to Human Plus ($20). Same as Human with these additional permissions; You get a different role name to show you have supported DEFCON 29, the ability to post pictures and embed links, you can use external emoji, you have the ability to change your nickname, join some Human Plus chill out rooms, and to engage with voice and video in the rooms that support it. Many other aspects of DEFCON 29 are FREE this year, see our guide for more details!
Tickets (In Person): https://shop.defcon.org/products/def-con-29
Code Of Conduct: https://defcon.org/html/links/dc-code-of-conduct.html
DEFCON was started in 1993 by Dark Tangent (Jeff Moss) as a going away party for a friend who never showed. It has since grown to one of the biggest hacker security conventions around the world with over 20,000 attendees yearly.
DEF CON 29 will be a hybrid event this year, we will give hackers a choice in how they wish to experience DEF CON. We will host both an in-person experience in Las Vegas and a virtual con on our official Discord just as we did for DEF CON Safe Mode in 2020.
Either Virtual or In-Person, DEFCON 29 is still what DCG 201 classifies it as a “Mega Convention” aka a convention with smaller mid-sized conventions nested in it. You will be covering a wide area with a diverse mob of people with ten million activities going on all at once. It’s important to plan out your day, take your time and remember that it’s physically impossible to see and do everything in one con year never mind in one day. For those attending Virtually be thankful that unlike the previous this year you can see most of DEFCON 29 at mostly your leisure since most of the content will be pre-recorded and archived.
The convention this year is so massive we plan on listing all the important things to note, not exactly everything that is there. We highly suggest looking at their website and clicking around to give you a sense on what you would like to see.
PREPARE (IN PERSON)
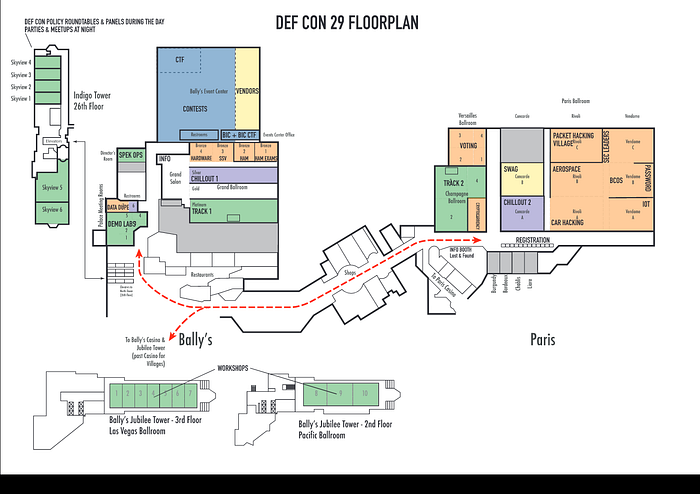
Paris & Bally’s Floorplan: https://defcon.org/images/defcon-29/dc-29-paris-ballys-final-public.pdf
HACKERS WITH DISABILITIES GUIDE @ DEFCON 29

WELCOME TO DEFCON. HDA IS HERE TO HELP!
Hackers with disabilities (HDA) was assembled to provide resources, maps, guides and assistance to people attending DEFCON who need assistance due to disabilities. We acknowledge that not all disabilities are visible and that we are providing this information for all attendees & stand ready to assist anyone with ADA needs to the best of our ability and within the operational scope of DEFCON. If at any time you have questions or would like to suggest things that we should be doing please see the DEFCON forums page dedicated to HDA: https://forum.defcon.org/node/237509/
While our goal is to make DEFCON more accessible to people with disabilities, we are limited in what we can do and provide this information and any assistance we can on a best effort basis.
Due to the complications involved in working with multiple hotels, federal, state, and local regulations, the requirements of operating a public gathering during a global pandemic we cannot promise nor provide accommodations for all people in all situations. Please understand that under no circumstances are we singling out, mocking, or intending to make anyone feel out of place. We want individuals with disabilities to be an active and contributing part of the DEFCON culture. If we must set a blanket rule or cannot provide specific items or services at scale, please understand the limitation is based on resources, legal implications, and restrictions put upon a large-scale social gathering and not from a place of discrimination.
Despite what our badges say at the end of the day we are all HUMAN. We strive to improve with your input and active involvement with the community to bring you the best conference that we can.
FULL GUIDE: https://defcon.org/images/defcon-29/HDA%20DEFCON%2029%20LAS%20VEGAS-V4.2-FINAL.pdf
PREPARE (VIRTUAL)
What you need to access DEFCON 29:
DISCORD Account
You will need a Discord account to participate in the social aspects of DEFCON 29. You can find detailed instructions on getting on the DEF CON Discord server here. There is a FAQ for Humans on Discord as well.
Join with the DEF CON Discord Server signup link: https://discord.gg/defcon
Twitch
You will need to get on the DEF CON Twitch for live streamed talk Q&A sessions, evening fireside talks and evening contests. Not to mention the live entertainment!
YouTube/DEF CON Media Server
The Talks for DEF CON will be released daily on the DEF CON YouTube channel so you might want to susbscribe! They will also be released in torrents on https://media.defcon.org
Accessing Talks
How to Access DEFCON 29 Mode Talks and Q&A Sessions
DEF CON official presentations have been pre-recorded, and pre-released online individually and as a torrent on media.defcon.org and on our official YouTube channel.
The dates and times on the Speaker Page and Schedule Page are special live streamed Q&A sessions for each talk, as well as additional fireside lounges and panels. These sessions will be streamed on Twitch at https://www.twitch.tv/defconorg.
All discussions and attendee to speaker participation will be on the DEF CON Discord Server at: https://discord.com/channels/708208267699945503/733079621402099732
Main Tracks
DEF CON official presentations will be a mix of LIVE In-Person & pre-recorded. We will try to make note to the best of our ability which talks will be In-Person & Virtual.
Also watch the talks released later in the month on YouTube: https://www.youtube.com/user/DEFCONConference
Track 1 Talks Chat
https://discord.com/channels/708208267699945503/733079621402099732
Virtual Sessions will be streamed here
https://www.twitch.tv/defconorg
Speaker Q&A Live Chat — Ask a question
https://discord.com/channels/708208267699945503/733079691145117848
Fireside Lounge Panels
https://discord.com/channels/708208267699945503/733562098315034735
War Story Bunker & No Tech Talks
https://discord.com/channels/708208267699945503/733562098315034735
ALL TWITCH STREAMS
Master Channel (All Channels In One): https://multitwitch.tv/defconorg/defcon_dctv_one/defcon_dctv_four/defcon_music/defcon_chill/aivillage/biohackingvillage/blueteamvillage/bypassvillage/cryptovillage/dcpolicy/hackthesea/dchhv/hamradiovillage/ics_village/iotvillage/monerovillage/passwordvillage/paymentvillage/redteamvillage/roguesvillage/toool_us/votingvillagedc
DEF CON Streams
DEF CON org Twitch Stream // Schedule
Hacker Jeopardy Twitch Stream
DEF CON Music Twitch Stream
DEF CON Youtube Streams
DEF CON Chill Twitch Stream
DEF CON Village Streams
Blue Team Village Twitch Stream // Youtube Stream
Red Team Village Twitch Stream // Youtube Stream
Aerospace Village Twitch Stream // Youtube Stream
BiohackingVillage Twitch Stream // Youtube Stream
Career Hacking Village Twitch Stream // Youtube Stream
Hack The Sea Twitch Stream // Youtube Stream
Car Hacking Village (Track1) Twitch Stream // Youtube Stream
Car Hacking Village (Track2) Twitch Stream // Youtube Stream
Car Hacking Village (CHV 101) Twitch Stream // Youtube Stream
CryptoVillage Twitch Stream // Youtube Stream
Ethics Village Twitch Stream // Youtube Stream
Wall of Sheep/Packet Hacking Village Twitch Steam // Youtube Stream
Recon Village Twitch Stream // Youtube Stream
Cloud Hacking Village Youtube Stream
Ham Radio Village Twitch Stream
ICS Village Twitch Stream
IoT Village Twitch Stream
ByPass Village Twitch Stream
Toool US/Lockpick Village Twitch Stream
Monero Village Twitch Stream
Payments Village Twitch Stream
Password Village Twitch Stream
AppSec Village Youtube Stream
cpxSatAmericas Twitch Stream
Voting Village Twitch Stream
Hardware Hacking Village Twitch Stream
Rogues Village Twitch Stream
AI Village Twitch Stream
- Adversary Village
- Aerospace Village: Videos are linked at their schedule
- AI Village
- Appsec Village: Videos are linked at their schedule
- B.I.C. (Blacks In Cybersecurity) Village
- Bio Hacking Village
- Blue Team Village
- Car Hacking Village
- Career Hacking
- Cloud Village
- Crypto & Privacy Village
- Hack the Sea Village
- Ham Radio Village
- ICS Village
- IoT Village
- Lock Bypass Village
- Packet Hacking Village
- Payment Village
- Recon Village
- Rogues Village
- Social Engineering Village
- Voting Village
Other Streams Related
Second Order Chaos Twitch Stream
Hacker Gameshow Twitch Stream
The Many Hats Club Twitch Stream
ZephrPhish Twitch Stream
(Thanks To AngusRed!)
DEFCON GROUPS @ DEFCON 29

DCG 201 will be streaming various aspects of DEFCON 29 virtually from New Jersey!
Schedule:
DCG 201 Special: Roadtrip To DCG 610 — Wednesday, August 4th @ 7:00 PM EST
DCG 201 Special: DEFCON 29 -y Requirements.sh && sudo ./FUZZCON — Thursday, August 5th @ 12:00 NOON EST — 4:00 PM EST
DCG 201 Special: DEFCON 29 Virtual Tour Day 1 — Friday, August 6th @ 1pm EST -
DCG 201 Special: The East Coast Perspective :: NYC2600 Meet Up — Friday, August 6th @ 6:00 PM EST
DCG 201 Special: Electronic Frontier Alliance VR Broadcast @ EFF — Saturday, August 7th @ 2:00 PM EST
DCG 201 Special: DEFCON 29 Virtual Tour Day 2 — Saturday, August 7th @ 1:00 PM EST
DCG 201 Special: DEFCON 29 Virtual Tour Day 3 — Sunday, August 7th @ 1:00 PM EST
The Master Of Unlocking :: Episode 28 :: Death Defying Doorlocks & DEFCON 29 Locksport Recap — Sunday, August 8th @ 8:00 PM EST
Live Streams:
Twitch: https://www.twitch.tv/defcon201live
dLive: https://dlive.tv/defcon201
YouTube: https://www.youtube.com/c/defcon201
Invidious (TOR): http://grwp24hodrefzvjjuccrkw3mjq4tzhaaq32amf33dzpmuxe7ilepcmad.onion/channel/UCYDQaOHbK5trRU2CDgb0qSg
Facebook: https://www.facebook.com/groups/defcon201/
PeerTube: https://diode.zone/accounts/dc201/video-channels
Hacker Happy Hour at the Tuscany (255 E Flamingo Rd, Las Vegas, NV 89169)
Friday 7:00 PM EST!
Tell all your friends!

NY-METRO AREA :: DCG 610 PRE-CON MEET-UP
DEF CON 610 Monthly Meetup: Discussions on Hacking & Information Security.
Wed, Aug 4, 2021, 6:00 PM EST
For August, DCG 610are having our own MINI-CON!
Many of us are unable to make it to DEF CON so we are bringing a bit of that con feel right here!
Where: Two Rivers Brewing, Easton PA
Schedule:
6pm — 7pm Video games
Soldering Lessons — BiaSciLab (Kits are $10)
Lock Picking Lessons — BiaSciLab
7pm — ??? CTF: They’ll be doing an online CTF as a group, sharing their collective knowledge as they pwn flags! Bring a laptop if you want to participate in the CTF fun!
Lock picking and Soldering lessons will continue as necessary.
____________________________________
General Resources Provided For All:
Lock picking with practice locks. Picks and training provided.
Video games for the kids…okay mostly for adults, but also for the kids.
Great conversation and exchange of ideas.
____________________________________
What to bring:
Having a laptop helps, but not required.
Any hardware you’d like to show off/need help with.
Lock picks.
Children or otherwise adorable animals.
DEF CON 29 Capture The Flag Competition
DEF CON CTF 2021 will run Friday August 6th through Sunday 8th (times below).
Every year we select the best CTF teams through a tough public qualifier game online. They then compete in an even tougher, live attack/defense CTF which will crown the best team in the league.
DEF CON CTF, like the rest of the DEF CON 29, will be hybrid. Players are welcome to join (part of) the Order in Vegas, but the infrastructure and challenges will live 100% on the internet. We’re taking pains to make sure that teams on-site have no advantage over online teams. We would love to see all of you, but it’s still a crazy time around the world, so we’ll accommodate those that can’t (or don’t feel comfortable) making the trip.
Info: https://oooverflow.io
Discord: CTF area
Schedule (PDT GMT -7):
Badge Pickup: Thursday, August 5th, 9:00 – 10:00am.Capture the Flag Hours (all times local to Las Vegas):- Fri, Aug 6, 10am-8pm, set up begins at 9am
- Sat, Aug 7, 10am-8pm, set up begins at 9am
- Sun, Aug 8, 10am-2pm, set up begins at 9am
Qualifying Teams
DiceGang [via pwn2win]
HITCON ⚔️ Balsn
Katzebin [winner of DEF CON CTF 2020 as A*0*E]
mhackeroni
NorseCode
春秋GAME-Nu1L
ooorganizers
pasten [via hxp CTF]
Plaid Parliament of Pwning
PTB_WTL
r3kapig
Shellphish
StarBugs
Perfect ⚔️ Guesser [via HITCON CTF + PlaidCTF (!)]
Tea Deliverers
侍Pre-game Team Communications
Games? You want games, I'll give you games. The Master Control Program
has chosen you to serve your system on the Game Grid. If you fail to
obey commands, you will be subject to immediate de-resolution. Order
of the Overflow will see you in Vegas. Important information is below.What: Before you can get into DEF CON, you must provide an original,
signed, vaccination card, with the final COVID-19 vaccination dose
dated no later than July 22nd, 2021. Once this is verified, you’ll
receive a wristband that must be worn at all times while in DEF CON.
More info can be found here:
https://defcon.org/html/defcon-29/dc-29-faq.htmlDiscord: Plan on it, even in Vegas.
Discord info:
Attention teams! ... will not be heard, except if you're in Vegas and Zardus is in the mood.Instead, game announcements will be made on DEF CON's discord #ctf-announcements-text.
We will mirror some on Twitter, but the canonical source is Discord.Captain meetings will happen on ctf-captains-voice.
There is also a #ctf-captains-text channel. The internal ticketing system remains the chief team-OOO communication system, but we may ask you to post game-wide issues on Discord to keep things fair and visible to all (note that even internal tickets become public after the game together with the rest of the database). You're also welcome to use this channel if #ctf-discussion-text gets too noisy.
You must keep an eye on these sources even if you're physically in Vegas.To get access, each team must reply with a short list of Discord user IDs, like this:
zardus 839381277307830302
crowell 841831894299312168
Each team must send at least one, it's strongly recommended to send at least two, and it's fine to have a few more, just don't exaggerate and make it hard for us to keep track of who's who. Each user will get the 'ctf-captain' role.
To copy the ID: https://support.discord.com/hc/en-us/articles/206346498-Where-can-I-find-my-User-Server-Message-ID-Finally, be nice to noobs that pop up in the channel asking for info on other CTFs. On Discord we have the "ctf-ooo" role. Goons are red. If you don't have an account there yet, remember to complete the captcha after registering. Official info: https://defcon.org/html/defcon-safemode/dc-safemode-discord.html
DEFCON VILLAGES
The core and heart of the convention are the “Villages”. These are spaces inside of DEFCON that act as their own miniature convention, including talks, contests, badges and swag. Many of them focus around a particular special interest. Here is a master list of almost every village at the convention plus a special highlight of one talk or activity they will have there.
NEW VILLAGES IN 2021

Adversary Village (VIRTUAL)
“Adversary Village” is a community which purely focuses on Adversary simulation, Adversary emulation, Threat/APT emulation, Breach and adversarial attack simulation, Supply chain security, Adversary Tactics, Life, Adversary Philosophy, urban survival skills and a bit of Purple teaming.
The goal of the Adversary Village would be, to build an open Security community for the researchers and organizations, who are putting together new means, methodologies towards the simulation and emulation of adversary tactics.
Website: https://adversaryvillage.org/adversary-events/DEFCON-29/
Twitter: https://twitter.com/AdversaryVillag
Twitch LIVE Stream: https://twitch.tv/AdversaryVillage

BLACKS IN CYBERSECURITY (BIC) VILLAGE (IN PERSON)
The Blacks In Cybersecurity Village seeks to bring culturally diverse perspectives to the holistic Cybersecurity community; by way of a series of talks and a capture the flag event.
In providing these activities, we hope to help highlight Black experiences, innovations in the field, Black culture and educate the community about Black history.
This village seeks to highlight Black experiences, innovations in the field, Black culture, Black history as well as provide a platform for the discussion of social justice and its impact on the progression and development of Technology.
Website: https://www.blacksincyberconf.com/bic-village
Twitter: https://twitter.com/BlackInCyberCo1
Twitch LIVE Stream: https://www.twitch.tv/blacksincybersecurity
SECURITY LEADERS VILLAGE (IN PERSON)
We are the Security Leaders Village (SLV) at DEF CON. We came together with the goal to help current and aspiring leaders in cybersecurity to share their challenges, suggest potential solutions, develop leadership skills and perspectives, discuss the good — the bad — and the ugly — and how to make it better. Through collaborative networking, shared learnings, including videos and presentations by leaders in the SLV village community, you will learn and grow, including exploring new security innovations and standards opportunities. Join the SLV to share your journey, use your voice, listen and learn, chart your path, and find a diverse and inclusive community of support in the world of cybersecurity.
Come as you are, all are welcome. DEFCON29 is our inaugural village year! Join us to share, listen, learn, and collaborate. We are hosting two tracks on Saturday, August 7th, 10am to 6pm PST.
Website: https://securityleadersvillage.org/
Twitter: https://twitter.com/securityleader2

CRYPTOCURRENCY VILLAGE
Cryptocurrency is a digital form of peer-to-peer money that is exchanged on decentralized networks independent of any central authority and is cryptographically secured. Networks operate under a set of programmatic rules, which maintains the immutability of a public ledger and ensures against double-spending. Although Bitcoin, Ethereum, and Dogecoin are the most well-known cryptocurrencies, other projects like Monero seek to address scalability, privacy, and censorship resistance in innovative ways.
Formally the Monero Village, the Cryptocurrency Village brings together leading experts in the area to explore substantive issues regarding the current state of blockchain technologies, regulatory landscape, and the general cryptocurrency ecosystem. The village hosts keynote talks, panels, workshops, networking events, and parties.
Website: https://cryptocurrencyvillage.net/
Twitter: https://twitter.com/DEFCONCCVillage

Aerospace Village (HYBRID)
DEF CON 28 Aerospace Village is a researcher led, non-profit whose mission is to build a diverse community focussed on the security of everything from airports, air traffic management, aircraft and space.
Discussion Forum: TBA
Village Schedule: https://aerospacevillage.org/def-con-28-schedule/
More Info:
https://twitter.com/secureaerospace
https://aerospacevillage.org
https://www.linkedin.com/company/aerospace-village
AI Village (VIRTUAL)
Location: AI village Discord Channel
Artificial Learning techniques are becoming more prevalent in core security technologies like malware detection and network traffic analysis. Its use has opened up new vectors for attacks against non-traditional targets, such as deep learning based image recognition systems used in self driving cars. There are unique challenges in defending and attacking these machine learning systems that the security community needs to be made aware of. This AI Village will introduce DEF CON attendees to these systems and the state of the art in defending and attacking them. We will provide a setting to educate DEF CON at large through workshops and a platform for researchers in this area to share the latest research.
Forum Link: https://forum.defcon.org/node/231058
Appsec Village (VIRTUAL)
The AppSec Village welcomes all travelers to choose from talks by expert community members, an awesome AppSec-focused (CTF)2, online workshops, and more. Bring your thirst for knowledge and passion for breaking things, and your visit to AppSec Village will be a thrill!
Discussion Forum: TBA
Village Schedule: https://www.appsecvillage.com/agenda/2020
More Info:
https://twitter.com/appsec_village
https://www.youtube.com/channel/UCpT8Ll0b9ZLj1DeEQQz7f0A
https://www.appsecvillage.com/
BioHacking Village (VIRTUAL)
Borne in 2014, the Biohacking Village started with a small space and a big idea: Bring the forefront of citizen science and biomedical security to the world’s biggest hacker conference. With partners such as the FDA and Mayo Clinic, the Biohacking Village has become a primary conduit for the healthcare community to engage positively and proactively with security researchers.
Device Lab:
A high-collaboration environment to build trust and trustworthiness in healthcare, connecting security researchers, manufacturers, hospitals, and regulators, to learn from each other and develop their skills. Device Lab research benefits patients by providing manufacturers valuable feedback on cyber safety of their devices with high fidelity.
Speaker Lab:
Our speakers hail from varying fields in the biomedical ecosystem to engage security researchers and healthcare stakeholders. We welcome self made entrepreneurs, security researchers, inventors, government regulators makers, innovators to discuss real world solutions to some of humanity’s most pressing challenges and opportunities in the areas of health, security, and technology.
Catalyst Lab:
The Catalyst Lab provides the opportunity to interact with outstanding faculty, thought leaders and cutting edge experts in the biomedical industry who provide up-to-date advice and training in the developing field of translational medicine by fostering leadership, entrepreneurship, and commercialization activities.
Discussion Forum: TBA
Village Schedule: https://villageb.io
More Info:
https://twitter.com/DC_BHV
https://m.twitch.tv/biohackingvillage/profile
https://www.youtube.com/channel/UCm1Kas76P64rs2s1LUA6s2Q/about?view_as=subscriber
Blockchain Village [BCOS Village] (IN PERSON)
https://discord.com/channels/708208267699945503/732733136408019084
Forum Link: https://forum.defcon.org/node/233036
Blue Team Village (VIRTUAL)
Blue Team Village is returning for our third DEF CON! Focusing on the defensive side of hacking, we aim to offer our hybrid community the same kind of talks and workshops that you would experience in person, adapted for this year’s remote circumstances. Likewise, we’ll be seeing the return of our popular OpenSOC CTF — the schedule can be found on our website at blueteamvillage.org. Come join us to learn about defensive-side hacking, and join our community of like-minded hackers for fun, learning, and mentorship.
OpenSOC CTF starts 08/06 at 10:00 PT runs for 65 hours.
BTVMaskCon start 08/06 at 11:00 PT runs for 55 hours.
Discussion Forum: TBA
Village Schedule: https://cfc.blueteamvillage.org/call-for-content-2020/schedule
More Info:
https://twitter.com/BlueTeamVillage
https://twitch.tv/BlueTeamVillage
Car Hacking (VIRTUAL)
Learn, hack, play. The Car Hacking Village is an open, collaborative space to hack actual vehicles (this year virtually) that you don’t have to worry about breaking! Don’t have tools? No worries, since our challenges are virtual this year, you will only need a web browser and terminal access to access our challenges. Never connected to a car? We’ll show you how. Follow our CHV101 section to learn the basics of car hacking.
Additionally, we’ll be hosting multiple talks about the art of hacking automobiles and have launched a really cool Automotive Ethernet badge!!
To find out more about how we will be going virtual this year, please head on over to https://www.carhackingvillage.com/def-con-28
We also have great Car Hacking Village swag!! Head on over to our store and order today!! https://stores.customink.com/carhackingvillage
Discussion Forum: TBA
More Info:
https://www.carhackingvillage.com/def-con-28
https://twitter.com/CarHackVillage
https://stores.customink.com/carhackingvillage
Cloud Village (VIRTUAL)
Cloud village is an open platform for researchers interested in area of cloud security. We plan to organize talks, tool demos, CTF and workshops around Cloud Security and advancements.
Discussion Forum: TBA
Village Schedule: https://cloud-village.org
More Info:
https://cloud-village.org
https://twitter.com/cloudvillage_dc
https://www.youtube.com/channel/UCupKln6fqF9tBTweRE6xNDQ
Crypto & Privacy Village (HYBRID)
A place for puzzles, privacy, and pseudorandom permutations. We will be streaming talks on a variety of cryptography and privacy topics, as well as hosting our annual Goldbug puzzle. The Gold Bug starts Friday at 10am PT until Sunday 12pm PT
Discussion Forum: TBA
Village Schedule: https://cryptovillage.org/dc28/schedule
More Info:
https://twitter.com/cryptovillage
https://twitch.tv/cryptovillage/
https://cryptovillage.slack.com
https://www.youtube.com/channel/UCGWMS6k9rg9uOf3FmYdjwwQ
Data Duplication Village (IN PERSON)
Yes, the Data Duplication Village is back for DC 28! If you’re looking for something to fill up all your unused storage, may I recommend a nice hash table or two with a side of all of the DefCon talks and everything else on infocon.org? It’s all part of our “free-to-you” service of simply handing you terabytes of useful data.
Check the schedule and/or dcddv.org for up-to-date information.
Ethics Village (???)
The DEFCON Ethics Village is focused on fostering a discussion about ethics in the security domain. Unlike the professions of medicine and law, information security does not have a codified standard of ethics. Professionals in information security have yet to agree upon common ethical principles and many remain unconvinced of the possibility of establishing a universal framework that can address the realm of information security.
Forum Link: TBD
Hack the Sea (VIRTUAL)
Reverse-engineers, makers, and hackers of all kinds are welcome to join us as Hack The Sea 2.0 — Voyage to Discovery continues the journey we began at DEF CON 27. Our core partners and volunteers will return to provide an expanded opportunity for attendees to explore the world of maritime industrial control systems, communications, and operational technology.
Our ship-based Capture the Flag (CTF), hands-on workshops, and talks by an international panel of experts, will bring an ocean of learning and fun to Las Vegas. A special focus this year will be on Unmanned Undersea Vehicles (UUVs), autonomous “floaters”, and other technology highlighting the growing role of robots in maritime.
Forum Link: TBA
Ham Radio Village (HYBRID)
Ham Radio is all about overcoming obstacles and communicating over long distances without physical contact. That’s why Ham Radio Village is excited to return for a second year as part of DEFCON 29. Join us on the DEF CON discord where we will be giving everyone the opportunity to learn more about ham radio than they do today.
Discussion Forum: TBD
More Info:
https://twitter.com/HamRadioVillage
https://www.twitch.tv/HamRadioVillage
https://www.hamvillage.org/dc28.html
HHV/SSV (HYBRID)
A basic bar to working with embedded electronics is learning to properly meld metal, creating both a electrical and physical bond. You can only get so far with a breadboard and wires hanging out everywhere. At some point you will need to take the device out of the lab and introduce it to the rigors of the world. We supply the irons and the skills to help you, whether that is your first time fusing metal or getting those lead wires on a UART breakout. Details @ dcssv.org
Forum Link: TBD
ICS Village (VIRTUAL)
Connecting public, industry, media, policymakers, and others directly with ICS systems and experts.
Hack the Plan[e]t Capture the Flag (CTF) contest will feature Howdy Neighbor and the Industrial Control System (ICS) Range. Building off of last year’s, the CTF will integrate both Internet of Things (IoT) and ICS environments with interactive components for competitors to test their skills and knowledge.
Discussion Forum: TBA
Village Schedule: https://www.icsvillage.com/schedule-def-con-28
More Info:
https://twitter.com/ICS_Village
https://www.linkedin.com/company/icsvillage
https://www.youtube.com/channel/UCI_GT2-OMrsqqglv0JijHhw
https://www.twitch.tv/ics_village
IOT Village (HYBRID)
IoT Village advocates for advancing security in the Internet of Things (IoT) industry through bringing researchers and industry together. IoT Village hosts talks by expert security researchers, interactive hacking labs, live bug hunting in the lastest IoT tech, and competitive IoT hacking contests. Over the years IoT Village has served as a platform to showcase and uncover hundreds of new vulnerabilities, giving attendees the opportunity to learn about the most innovative techniques to both hack and secure IoT. IoT Village is organized by security consulting and research firm, Independent Security Evaluators (ISE), and the non-profit organization, Village Idiot Labs (VIL).
Discussion Forum: TBA
Village Schedule: https://www.iotvillage.org/#dc28_schedule
More Info:
https://twitter.com/IoTvillage
https://www.twitch.tv/iotvillage
https://www.iotvillage.org
Lock Bypass Village (VIRTUAL)
The Lock Bypass Village explores the world of hardware bypasses and techniques generally outside of the realm of cyber security and lockpicking. Come learn some of these bypasses, how to fix them, and have the opportunity to try them out for yourself.
Discussion Forum: TBA
More Info:
https://bypassvillage.org/
https://twitter.com/bypassvillage/
https://twitch.tv/bypassvillage/
Lock Picking Village (VIRTUAL)
Want to tinker with locks and tools the likes of which you’ve only seen in movies featuring secret agents, daring heists, or covert entry teams? Then come on by the Lockpick Village, run by The Open Organisation Of Lockpickers, where you will have the opportunity to learn the hands-on how the fundamental hardware of physical security operates and how it can be compromised.
The Lockpick Village is a physical security demonstration and participation area. Visitors can learn about the vulnerabilities of various locking devices, techniques used to exploit these vulnerabilities.
Experts will be on hand to demonstrate and discuss pick tools, and other devices that are generally available. By exploring the faults and flaws in many popular lock designs, you can not only learn about the fun hobby of sportpicking, but also gain a much stronger knowledge about the best methods and practices for protecting your own property.
Discussion Forum: TBA
More Info:
https://toool.us/
https://twitter.com/toool
https://www.twitch.tv/toool_us
Career Hacking (VIRTUAL)
How do you get to the next level in your career? What if you want to drastically change your skill set? The Career Hacking Village isn’t just about getting ready for your next step. We have career coaching, resume reviews, mock interviews, and a great set of speakers representing different opportunities. Don’t just do it for money. Do it for a lot of money! Or experience! Or Fun! Maybe all of the above!
Discussion Forum: TBA
More Info:
https://twitter.com/HackingCareer
Payment Village (VIRTUAL)
Payment technologies are an integral part of our lives, yet few of us know much about them. Have you ever wanted to learn how payments work? Do you know how criminals bypass security mechanisms on Point of Sales terminals, ATM’s and digital wallets? Come to the Payment Village and learn about the history of payments. We’ll teach you how hackers gain access to banking endpoints, bypass fraud detection mechanisms, and ultimately, grab the money!
Discussion Forum: TBA
Village Schedule: https://www.paymentvillage.org/schedule
More Info:
https://www.paymentvillage.org/
https://www.twitch.tv/paymentvillage
https://www.youtube.com/channel/UCivO-5rpPcv89Wt8okBW21Q
https://twitter.com/paymentvillageNEW! The Password Village
https://discord.com/channels/708208267699945503/732733760742621214
Forum Link: https://forum.defcon.org/node/232910
The Password Village (IN PERSON)
The Password Village provides training, discussion, and hands-on access to hardware and techniques utilized in modern password cracking, with an emphasis on how password cracking relates to your job function and the real world . No laptop? No problem! Feel free to use one of our terminals to access a pre-configured GPGPU environment to run password attacks against simulated real-world passwords. Village staff and expert volunteers will be standing by to assist you with on-the-spot training and introductions to Hashcat, as well as other FOSS cracking applications. Already a password cracking aficionado? Feel free to give a lightning talk, show off your skills, help a n00b learn the basics, or engage in riveting conversation with other password crackers. Regardless of whether you’re just a little hash-curious, a veteran cracker still relying on rainbow tables, a novice desiring to learn more, or an expert eager to share, we guarantee there will be something for everyone at the Password Village!
Discussion Forum: TBA
Village Schedule: https://passwordvillage.org/schedule
More Info:
https://passwordvillage.org
https://twitter.com/passwordvillage
https://twitch.tv/passwordvillage
https://www.youtube.com/channel/UCqVng_SmexXf4TW3AVdMIyQ
Packet Hacking Village (HYBRID)
The Packet Hacking Village welcomes all DEFCON 29 attendees and we have something for every level of security enthusiast, from beginners to those seeking a black badge. PHV Speakers, Workshops, and Walkthrough Workshops delivers high quality content for all skill levels. Packet Detective and Packet Inspector offers hands-on exercises to help anyone develop or improve their Packet-Fu. WoSDJCo has some of the hottest DJs at con spinning virtual for your enjoyment. And finally… Capture The Packet, the ultimate cyber defense competition that has been honored by DEF CON as a black badge event for nearly a decade.
Discussion Forum: TBA
Village Schedule: https://www.wallofsheep.com/pages/dc28
Policy Village (???)
DEF CON Policy supports education and dialogue across the security researcher and public policy communities.
Village Schedule: TBA
More Info:
Twitter: #DC28Policy
https://www.twitch.tv/dcpolicy
https://www.youtube.com/channel/UClXeKHqRs3YboEe3qkPWeBA
Recon Village (VIRTUAL)
Recon Village is an Open Space with Talks, Live Demos, Workshops, Discussions, Beginner Sessions, CTFs with a common focus on Reconnaissance. The village is meant for professionals interested in areas of Open Source Intelligence (OSINT), Threat Intelligence, Reconnaissance, and Cyber Situational Awareness, etc. with a common goal of encouraging and spreading awareness around these subjects.
For DEFCON 29 we will be running a bunch of OSINT / RECON talks as well as our RECON CTF.
Website: https://reconvillage.org
Twitter: https://twitter.com/reconvillage
Recon CTF — Friday 10 AM to Saturday 11 PM Talks Schedule (To be published soon on the website, I will ill share the link as we announce it).
Discussion Forum: TBA
Red Team Village (VIRTUAL)
The DEF CON Red Team Village is a community-driven effort for and by the offensive security community members (red teams and ethical hackers). The goal of the village is to expand the spectrum of red team and offensive security training, as well as to create opportunities for individuals to both, present and learn. The DEF CON Red Team Village community creates different activities including many technical presentations, hands-on workshops, trainings, demos, capture the flag (CTF), games, and other activities from participants.
Discussion Forum: TBA
Village Schedule: https://RedTeamVillage.io/schedule.html
More Info:
https://twitter.com/VillageRedTeam
https://RedTeamVillage.io/YouTube
https://www.twitch.tv/redteamvillage
Rogues Village (VIRTUAL)
Rogues Village is a place to explore alternative approaches to existing security concepts by looking to non-traditional areas of knowledge. Incorporating expertise from the worlds of magic, sleight of hand, con games, and advantage play, this village has a special emphasis on Social Engineering and Physical Security.
Discussion Forum: TBA
More Info:
www.foursuits.co/roguesvillage
www.twitter.com/roguesvillage
www.twitch.tv/roguesvillage
Social Engineering Village (VIRTUAL)
Established at DEF CON 18 the SEVillage at DEF CON has been the one-stop shop for all things social engineering. From our humble beginnings with a small room and our sound proof booth to now running 4 events and a “Human Track” where social engineering talks are given. The SEVillage at DEF CON is the place for not only our flag ship event, the Social-Engineer Capture The Flag (The SECTF), but also Mission SE Impossible, the SECTF4Kids and the SECTF4Teens!
Discussion Forum: TBA
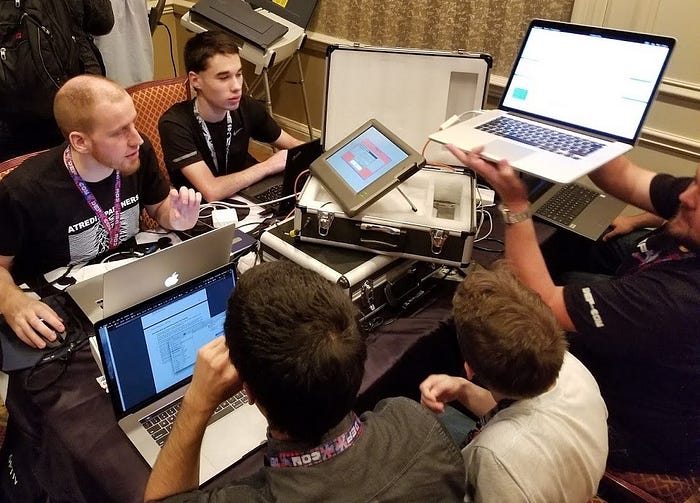
Voting Machine Hacking Village (IN PERSON)
The Voting Machine Hacking Village (“Voting Village”) returns for its fourth year at DEF CON! As the only public third-party assessment of voting infrastructure in the world, the Voting Village attracts thousands of white hat hackers, government leaders, and members of the media to partake in the mission of rigorously researching voting systems and raising awareness of voting vulnerabilities.
The Voting Village gives hackers a unique opportunity to directly audit voting machines and other election equipment. With the 2020 elections looming and efforts to combat election vulnerabilities ongoing at the state and federal levels, the educational mission of the Voting Village remains as critical as ever.
Discussion Forum: TBA
Wireless Village (VIRTUAL)
The Wireless Village is run by the RF Hackers Sanctuary as an environment where people come to learn about the security of radio frequency (RF) transmissions which includes wireless technology, applications of software defined radio (SDR), Bluetooth (BT), Zigbee, WiFi, Z-wave, RFID, and all other protocols within the useable RF spectrum. RF Hackers Sanctuary is supported by a group of experts in the areas of information security as it relates to RF technologies. RF Hackers Sanctuary’s common purpose is to provide an environment in which participants may explore these technologies with a focus on improving their skills through offense and defense. These learning environments are provided in the form of guest speakers, panels, and Wireless Capture the Flag games.
Discussion Forum: TBA

DEFCON 29 WORKSHOPS
DEF CON WORKSHOPS IS BACK LIVE AND IN-PERSON ONLY AT BALLY’S!
Master List: https://defcon.org/html/defcon-29/dc-29-workshops.html
Workshops are a great way for instructors from the community to share information with others on a variety of subjects. Pre-registration for all DEF CON Workshops will open at 0900 PDT on Tuesday, July 6, and stay open until the last ticket is spoken for. We will be using EventBrite again to handle pre-registration and are anticipating the same level of response that we have seen in previous years, so be sure to check back here for the event links so you can be ready for Tuesday!
To keep everyone safe while participating in workshops, we are making the following changes:
- Max capacities listed, below, take into account keeping rooms at 80% capacity of the room.
- More space between attendees while still ensuring there are power strips available.
- Staggered check-in times in the morning in evening and an hour in-between sessions to reduce the number of people in the hallways at any given time.
Please note that all workshops are going to be in-person only with no parts of it streamed. Out of consideration for others, we ask that you do not pre-register unless you are certain you are able to attend.
DCG 201 WORKSHOP HIGHLIGHTS
Digital Forensics and Incident Response Against the Dark Arts: The Battle of Malicious Email and Downloaders
Saturday from 1000 to 1400 in Las Vegas 5+6
Capacity: 67 | Beginner — Intermediate
Michael Solomon Threat Hunter
Michael Register Threat Hunter
Ever wondered what it is like being a cybersecurity or incident response analyst? Here is your chance to experience an exciting 4-hour class taught by mR_F0r3n51c5 and S3curityN3rd. Phishing and malicious spam attacks continue to pose a significant risk in today’s cyber threat landscape. Using forensic and malware analysis fundamentals, this class will teach students how to analyze malicious downloaders, phishing emails, and malicious spam.
Upon successful class completion, students will be able to:
- Build analysis skills that leverage complex scenarios and improve comprehension.
- Demonstrate an understanding of forensic fundamentals used to analyze an email.
- Use open-source information to collect and analyze threat actor data; identify indicators of compromise, and demonstrate how to pivot on that information.
- Demonstrate how to analyze a malicious downloader; to include but not limited to debugging and deobfuscation.
- Participate in a hand to keyboard combat capstone. Students will be given a malicious file sample and demonstrate how to analyze it.
Registration Link: https://www.eventbrite.com/e/digital-forensics-and-ir-against-the-dark-arts-las-vegas-5-6-tickets-162218185961
Prerequisites:
None
Materials needed:
Students will be required to download two virtual machines (OVA files). Students will be given a URL for download access. In regards to the downloaded virtual machines, these should be imported into your virtual machine software and ready before the start of class. If any additional technical support is needed, the instructors will make themselves available online.
Students must have a laptop that meets the following requirements:
- A 64 bit CPU running at 2GHz or more. The students will be running two virtual machines on their host laptop.
- Have the ability to update BIOS settings. Specifically, enable virtualization technology such as “Intel-VT.”
- The student must be able to access their system’s BIOS if it is password protected. This is in case of changes being necessary.
- 8 GB (Gigabytes) of RAM or higher
- At least one open and working USB Type-A port
- 50 Gigabytes of free hard drive space, allowing you the ability to host the VMs we distribute
- Students must have Local Administrator Access on their system.
- Wireless 802.11 Capability
- A host operating system that is running Windows 10, Linux, or macOS 10.4 or later.
- Virtualization software is required. The supplied VMs have been built for out of the box comparability with VMWare Workstation or Player. Students may use other software if they choose, but they may have to troubleshoot unpredictable issues.
At a minimum, the following VM features will be needed:
- NATted networking from VM to Internet
- Copy Paste of text and files between the Host machine and VM
Michael Solomon
Michael Solomon (mR_F0r3n51c5) is currently a Threat Hunter for a large managed security service provider. He has ten years of experience conducting Cyber Operations, Digital Forensics & Incident Response (DFIR), and Threat Hunting. He is very passionate about helping grow and inspire cybersecurity analysts for a better tomorrow.
Michael Register
Michael Register (S3curityN3rd) has 5 years of combined experience across IT, Networking, and Cybersecurity. He currently holds multiple certifications, including the GCIH. S3curityN3rd spent the last 3 years working in Incident Response before a recent transition into a Threat Hunting role. His areas of focus have been on forensics, malware analysis, and scripting.
Hacking the Metal: An Introduction to Assembly Language Programming
Saturday from 1000 to 1400 in Las Vegas 3+4
Capacity: 60 | Beginner — Intermediate
eigentourist Programmer
Deep below the surface of the web, the visible desktop, and your favorite mobile apps, lies a labyrinth where the rules of most programming languages cease to exist. This is the world of the reverse engineer, the malware analyst, and the veteran systems programmer. Here, we write code in assembly language, the lowest level at which a computing machine can be programmed. This workshop will introduce you to the world of assembly language programming, give you the opportunity to write some real-world code, and finally, to play the role of reverse engineer and try your hand at some guided malware analysis.
Registration Link: https://www.eventbrite.com/e/hacking-the-metal-an-introduction-to-assembly-language-programming-lv-34-tickets-162218563089
Prerequisites:
Some previous programming experience is helpful but not vital.
Materials needed:
Laptop
eigentourist
Eigentourist is a programmer who learned the craft in the early 1980s. He began formal education in computer science when the height of software engineering discipline meant avoiding the use of GOTO statements. Over the course of his career, he has created code of beautiful simplicity and elegance, and of horrific complexity and unpredictability. Sometimes it’s hard to tell which was which. Today, he works on systems integration and engineering in the healthcare industry.
Evading Detection a Beginner’s Guide to Obfuscation
Saturday from 1500 to 1900 in Las Vegas 3+4
Capacity: 60 | Intermediate
Anthony “Cx01N” Rose Lead Security Researcher
Jake “Hubbl3” Krasnov Red Team Operations Lead
Vincent “Vinnybod” Rose Lead Tool Developer
Defenders are constantly adapting their security to counter new threats. Our mission is to identify how they plan on securing their systems and avoid being identified as a threat. This is a hands-on class to learn the methodology behind malware delivery and avoiding detection. This workshop explores the inner workings of Microsoft’s Antimalware Scan Interface (AMSI), Windows Defender, and Event Tracing for Windows (ETW). We will learn how to employ obfuscated malware using Visual Basic (VB), PowerShell, and C# to avoid Microsoft’s defenses. Students will learn to build AMSI bypass techniques, obfuscate payloads from dynamic and static signature detection methods, and learn about alternative network evasion methods.
In this workshop, we will:
i. Understand the use and employment of obfuscation in red teaming.
ii. Demonstrate the concept of least obfuscation.
iii. Introduce Microsoft’s Antimalware Scan Interface (AMSI) and explain its importance.
iv. Demonstrate obfuscation methodology for .NET payloads.
Registration Link: https://www.eventbrite.com/e/evading-detection-a-beginners-guide-to-obfuscation-las-vegas-3-4-tickets-162219734593
Prerequisites:
Basic level of PowerShell or C# experience.
Materials needed:
Laptop VMWare or Virtual Box Windows Dev machine or other Windows VM Kali Linux VM
Anthony “Cx01N” Rose
Anthony “Cx01N” Rose, CISSP, is the Lead Security Researcher at BC Security, where he specializes in adversary tactic emulation planning, Red and Blue Team operations, and embedded systems security. He has presented at numerous security conferences, including Black Hat, DEF CON, and RSA conferences. Cx01N is the author of various offensive security tools, including Empire and Starkiller, which he actively develops and maintains. He is recognized for his work, revealing wide-spread vulnerabilities in Bluetooth devices and is the co-author of a cybersecurity blog at https://www.bc-security.org/blog/.
Jake “Hubbl3” Krasnov
Jake “Hubbl3” Krasnov is the Red Team Operations Lead at BC Security. He has spent the first half of his career as an Astronautical Engineer overseeing rocket modifications for the Air Force. He then moved into offensive security, running operational cyber testing for fighter aircraft and operating on a red team. Hubbl3 has presented at DEF CON, where he taught courses on offensive PowerShell and has been recognized by Microsoft for his discovery of a vulnerability in AMSI. Jake has authored numerous tools, including Invoke-PrintDemon and Invoke-ZeroLogon, and is the co-author of a cybersecurity blog at https://www.bc-security.org/blog/.
Vincent “Vinnybod” Rose
Vincent “Vinnybod” Rose is the Lead Tool Developer for Empire and Starkiller. He is a software engineer with expertise in cloud service and has over a decade of software development and networking experience. Recently, his focus has been on building ad-serving technologies, web and ad-tracking applications. Vinnybod has presented at Black Hat has taught courses at DEF CON on Red Teaming and Offensive PowerShell. He currently maintains a cybersecurity blog focused on offensive security at https://www.bc-security.org/blog/.
Learning to Hack Bluetooth Low Energy with BLE CTF
Friday from 1500 to 1900 in Las Vegas 3+4
Capacity: 80 | Beginner — Intermediate
Ryan Holeman Global Security Overlord
BLE CTF is a series of Bluetooth low energy challenges in a capture the flag format. It was created to teach the fundamentals of interacting with and hacking Bluetooth Low Energy services. Each exercise, or flag, aims to interactively teach a new concept to the user. For this workshop, we will step through a series of exercises to teach beginner students new concepts and allow more seasoned users to try new tools and techniques. After completing this workshop, you should have a good solid understanding of how to interact with and hack on BLE devices in the wild.
If you have done BLE CTF in the past, this class is still valuable. For advanced users we offer BLE CTF Infinity which is a sequel to BLE CTF. BLE CTF Infinity offers new exercises where each flag challenge is hosted in a completely separate GATT service. The new version allows for more advanced challenges which were not possible in the past.
To prepare for the workshop, please follow the setup documentation located at https://github.com/hackgnar/ble_ctf/blob/master/docs/workshop_setup.md
Registration Link: https://www.eventbrite.com/e/learning-to-hack-bluetooth-low-energy-with-ble-ctf-las-vegas-3-4-tickets-162217343441
Prerequisites:
To prepare for the workshop, please follow the setup documentation located at https://github.com/hackgnar/ble_ctf/blob/master/docs/workshop_setup.md
Materials needed:
Preferably a Linux box with a bluetooth controller or a bluetooth usb dongle. An OSX or Windows machine with a Linux VM and usb passthough works as well but should be setup and tested before the workshop.
Ryan Holeman
Ryan Holeman resides in Austin Texas where he works as the Global Security Overlord on Atlassian’s Security team. He is also an advisor for the endpoint security software company Ziften Technologies. He received a Masters of Science in Software Engineering from Kent State University. His graduate research and masters thesis focused on C++ template metaprograming. He has spoken at many respected venues such as Black Hat, DEF CON, Lockdown, BSides, Ruxcon, Notacon, and Shmoocon. He has also published papers though venues such as ICSM and ICPC . You can keep up with his current activity, open source contributions and general news on his blog. His spare time is mostly spent digging into various network protocols, random hacking, creating art, and shredding local skateparks.
Writing Golang Malware
Friday from 1500 to 1900 in Las Vegas 5+6
Capacity: 15 | Intermediate
Benjamin Kurtz Hacker
Participants will learn how to design and build their own multi-platform Golang-based implants and c2 frameworks by building on samples provided.
Topics will include:
- Communication between the implant and the command and control system including encrypted darknets with pluggable transports, covert exfiltration methods, detection evasion, and fault tolerant infrastructure design.
- Binary transformation techniques designed to allow offensive practitioners the freedom of writing conventional binaries, yet maintaining the mobility of shellcode-like operating conditions.
- Parsing and rewriting all binary formats to inject shellcode using a variety of reconfigurable methods.
- On-the-wire modification of binaries and archives from a man-in-the-middle or malicious server perspective.
- Methods of avoiding EDR with your implant, including loading modules direct from the c2 to memory without touching disk (on all platforms), customizable encrypting packers, and direct system calls/DLL unhooking (on Windows).
Registration Link: https://www.eventbrite.com/e/writing-golang-malware-las-vegas-5-6-tickets-162217403621
Prerequisites:
Programming experience required, some experience with Golang would be helpful.
Materials needed:
Laptop (any operating system)
Benjamin Kurtz
Ben Kurtz is a hacker, a hardware enthusiast, and the host of the Hack the Planet podcast (https://symbolcrash.com/podcast). After his first talk, at DefCon 13, he ditched development and started a long career in security. He has been a pentester for IOActive, head of security for an MMO company, and on the internal pentest team for the Xbox One at Microsoft. Along the way, he volunteered on anti-censorship projects, which resulted in his conversion to Golang and the development of the ratnet project (https://github.com/awgh/ratnet). A few years ago, he co-founded the Binject group to develop core offensive components for Golang-based malware, and Symbol Crash, which focuses on sharing hacker knowledge through trainings for red teams, a free monthly Hardware Hacking workshop in Seattle, and podcasts. He is currently developing a ratnet-based handheld device for mobile encrypted mesh messenging, planned for release next year.
Secure messaging over unsecured transports
Friday from 1500 to 1900 in Las Vegas 1+2
Capacity: 40 | Intermediate
Ash Hacker
Summarize what your training will cover, attendees will read this to get an idea of what they should know before training, and what they will learn after. Use this to section to broadly describe how technical your class is, what tools will be used, and what materials to read in advance to get the most out of your training. This abstract is the primary way people will be drawn to your session.
You need to send a message, avoiding traditional channels like email and SMS, to someone who’s on a different network, somewhere else in the world. The tools at your disposal are Python, DNS, and an unauthenticated MQTT broker. This message must be end-to-end encrypted, and the recipient must be able to confirm that it was undeniably you who sent it. Now add another constraint: you can’t communicate directly with this other party to perform a public key exchange before signing, encrypting, and transmitting the message. This can be a difficult problem to solve, and many specialized secure messaging apps have sprung up to address the challenge of end-to-end secured messaging. We will build our own. While our application won’t be as sophisticated as Signal, you’ll leave the workshop with an understanding of how DNS can be used to enable end-to-end authenticated and encrypted communication across nearly any public system that can be made to support the publisher/subscriber communication pattern.
Registration Link: https://www.eventbrite.com/e/secure-messaging-over-unsecured-transports-las-vegas-1-2-tickets-162214713575
Prerequisites:
Students should have a good understanding of DNS, Docker, and the Python programming language. An understanding of how to configure DNSSEC with their DNS server/provider of choice is necessary, and a basic understanding of how PKI works (roots of trust and the use of public keys to secure the conveyance of public keys) will be beneficial.
Materials needed:
- Hardware: Laptop with 4GB of RAM, 20GB hard drive space free after installing software prerequisites
- Software: Please arrive with git, Docker engine, and docker-compose already installed
Other:
- Attendees must have administrative access to a public DNS zone on a server which supports the TLSA record type. Many SaaS DNS services support this, and PowerDNS supports the record type as well. Configure this zone for DNSSEC before class.
- If for some reason you cannot configure DNSSEC for your zone, you must be able to host static content over HTTPS under your domain. For example: if you’re bringing mydomain.example to the workshop, you must be able to host static content on a server at https://device.mydomain.example/. If you can’t do DNSSEC, bring a web server.
Ash
Ash is just some dude. In the past he’s been a network engineer, created a variety of security tools, and is currently working in R&D and protocol development in spaces adjacent to email security. He has spoken at DEFCON, Black Hat, and Bsides San Diego. He has recently developed a weird fascination with hacking vintage electromechanical tech.

DEFCON 29 DEMO LABS
Demo Labs will be held in the Demo Labs section of the DEF CON Discord Server on the channels listed in the descriptions.
Full List: https://forum.defcon.org/node/236373
DEMO LAB HIGHLIGHTS
Depthcharge: A Framework for U-Boot Hacking (IN-PERSON)
Discord Channel: #dl-depthcharge
Location: In-person Demolab 2
When: Sat 10:00–11:50
Presenter(s): Jon Szymaniak
Abstract: In modern embedded systems that implement a “secure boot” flow, the boot loader plays a critical role in establishing the integrity and authenticity of software and data required to boot an operating system. Given the role and vantage point of boot loaders, they are a particularly interesting target for hardware hackers seeking to root a device and instrument it for further vulnerability hunting and reverse engineering. Although the vast majority of devices leveraging the ubiquitous and open source U-Boot boot loader leave it unprotected and trivially exploited, more product vendors are finally implementing secure boot and (attempting to) lock down their U-Boot builds. These less common specimen offer exciting opportunities to pursue creative bypasses and explore underappreciated U-Boot functionality. The Depthcharge framework was developed to help hardware hackers methodically (ab)use some of that underappreciated U-Boot functionality in novel ways to circumvent boot-time protections, as well as expedite the identification and exploitation of “the usual suspects” within exposed U-Boot device consoles. The project includes a Python 3 library for interfacing with devices, reading and writing memory via available primitives, deploying executable payloads, and analyzing various data structures. A collection of scripts built atop of library make this functionality readily available via the command line, and “Depthcharge Companion” firmware allows the tooling to extend its vantage point by presenting itself as a peripheral device connected to the target. This Demo Lab will introduce the basics of Depthcharge and explore how attendees can leverage and expand upon it when seeking to circumvent boot-time protections or just to further explore a system from within the U-Boot environment. For those wishing to protect their (employer’s) products from fellow DEF CON attendees, we’ll also cover the configuration checker functionality that can be used to avoid common U-Boot pitfalls.
Audience: Hardware / Embedded Systems — Both “offense” and “defense” within this audience
Links: GitHub: https://github.com/nccgroup/depthcharge Documentation: https://depthcharge.readthedocs.io
Bio(s): Jon Szymaniak is Principle Security Consultant in NCC Group’s Hardware & Embedded Systems Services team and a former embedded systems engineer. His areas of interest include U-Boot, Linux, Yocto, and firmware reverse engineering. Through both his day job and hobby hacking adventures, he’s enjoyed exploring and exploiting boot ROMs, automotive ECUs, Android-based platforms, and a myriad of Internet-connected things that shouldn’t be.
Empire (IN PERSON)
Discord Channel: #dl-empire
Location: In-person Demolab 2
When: Fri 14:00–15:50
Presenter(s): Vincent “Vinnybod” Rose, Anthony “Cx01N” Rose
Abstract: Empire is a Command and Control (C2) framework powered by Python 3 that supports Windows, Linux, and macOS exploitation. It leverages many widely used offensive security tools through PowerShell, Python 3, and C# agents. At the same time, it offers cryptologically-secure communications and flexible modular architecture that links Advanced Persistent Threats (APTs) Tactics, Techniques, and Procedures (TTPs) through the MITRE ATT&CK database. Empire has evolved significantly since its introduction in 2015 and has become one of the most widely used open-source C2 platforms. Through this time, Empire has advanced from a single user experience to allowing multiple user operations through an API with Empire acting as a teamserver. Currently, 2 different applications are available to connect to the Empire teamserver: Empire Command Line Interface (CLI) and Starkiller. The Empire CLI is built from the ground up as a replacement to the embedded legacy CLI and gives users a familiar feel of the legacy CLI, but is portable and connects through the Empire API. While Starkiller is a cross-platform UI available in Linux, Windows, and macOS powered by ElectronJS. The framework’s flexibility to easily incorporate new modules allows for a single solution for red team operations with the aim for Empire to provide an easy-to-use platform for emulating APTs. Customization is essential to any successful red team operation, which has driven the expansion of user plugins. These plugins allow any custom program to run side-by-side with the Empire teamserver. In addition, the commonality between other C2 platforms allows profiles and modules to be easily dropped in without the need for additional development. These features allow both red and blue teams to easily emulate and defend against the APT attack vectors.
Audience: Offense
Links: https://github.com/BC-SECURITY/Empire https://github.com/BC-SECURITY/Empire-Cli https://github.com/BC-SECURITY/Starkiller
Bio(s): Vincent “Vinnybod” Rose is the Lead Tool Developer for Empire and Starkiller. He is a software engineer with expertise in cloud service and has over a decade of software development and networking experience. Recently, his focus has been on building ad-serving technologies, web and ad-tracking applications. Vinnybod has presented at Black Hat has taught courses at DEF CON on Red Teaming and Offensive PowerShell. He currently maintains a cybersecurity blog focused on offensive security at https://www.bc-security.org/blog/.
Anthony “Cx01N” Rose, CISSP, is the Lead Security Researcher at BC Security, where he specializes in adversary tactic emulation planning, Red and Blue Team operations, and embedded systems security. He has presented at numerous security conferences, including Black Hat, DEF CON, and RSA conferences. Cx01N is the author of various offensive security tools, including Empire and Starkiller, which he actively develops and maintains. He is recognized for his work, revealing wide-spread vulnerabilities in Bluetooth devices and is the co-author of a cybersecurity blog at https://www.bc-security.org/blog/.
Git Wild Hunt A tool for hunting leaked credentials (IN PERSON)
Discord Channel: #dl-git-wild-hunt
Location: In-person Demolab 2
When: Sat 12:00–13:50
Presenter(s): Rod Soto @rodsoto, José Hernandez @d1vious
Abstract: Git Wild Hunt is a tool designed to search and identify leaked credentials at public repositories such as Github. Git Wild Hunt searches for footprints and patterns of over 30 of the most used secrets/credentials on the internet, especially those used in Devops and IT Operations. This tool helps developers and security operation departments discover leaked credentials in public repositories. This tool is also a recon tool for red teamers and pentesters, as it also provides metadata from leaks such as usernames, company names, secret types and dates.
Audience: Offense, Vulnerability Assessment
Links: https://github.com/d1vious/git-wild-hunt
Bio(s): Rod — Principal Security Research Engineer at Splunk. Worked at Prolexic Technologies (now Akamai), and Caspida. Cofounder of Hackmiami and Pacific Hackers meetups and conferences. Creator of Kommand && KonTroll / NoQrtr-CTF.
Jose — Principal Security Researcher at Splunk. He started his professional career at Prolexic Technologies (now Akamai), fighting DDOS attacks against Fortune 100 companies perpetrated by “anonymous” and “lulzsec.” As an engineering co-founder of Zenedge Inc. (acquired by Oracle Inc.), José helped build technologies to fight bots and web-application attacks. He has also built security operation centers and run a public threat-intelligence service.
Kubestriker — a blazing fast security auditing tool for kubernetes (VIRTUAL)
Discord Channel: #dl-kubestriker
Location: virtual Video 1
When: Fri 14:00–15:50
Presenter(s): Vasant Chinnipilli
Abstract: Kubestriker is a platform-agnostic tool designed to tackle Kuberenetes cluster security issues due to misconfigurations and will help strengthen the overall IT infrastructure of any organisation. It performs numerous in depth checks on a range of services and open ports on Kubernetes platform to identify any misconfigurations which make organisations an easy target for attackers. In addition, it helps safeguard against potential attacks on Kubernetes clusters by continuously scanning, monitoring and alerting of any anomalies. Furthermore, it comprises the ability to see some components of kubernetes infrastructure and provides visualised attack paths of how hackers can advance their attacks.
Audience: Offensive and Defensive Security Professionals, Security Auditors, Developers, Devops, Sysadmins, Devsecops and SRE professionals
Links: https://github.com/vchinnipilli/kubestriker
Bio(s): Vasant is a security enthusiast and speaker, currently working as a Security Architect and DevSecOps Practitioner. His technical abilities span a wide range of technologies across various domains of information security including cloud and container security and penetration testing. He is passionate about cloud and cloud native security, devsecops and security automation.
Open Bridge Simulator (IN PERSON)
Discord Channel: #dl-open-bridge-simulator
Location: In-person Demolab 1
When: Fri 14:00–15:50
Presenter(s): Constantine Macris, James Campbell
Abstract: Open Bridge Simulator provides a platform to explore the NMEA 2000 protocol, maritime electronics and CAN interfaces in a cost effective (under $50) software/hardware suite.
Audience: Hardware, Education, Defense
Links: https://github.com/thedini/openBridge
Bio(s): Constantine is an instructor at the US Coast Guard Academy where he teaches Cyber Systems. On the side he breaks things…
Principal Mapper (PMapper) — Mapping Privilege Escalation and More in AWS IAM (IN PERSON)
Discord Channel: #dl-pmapper
Location: In-person Demolab 1
When: Sat 10:00–11:50
Presenter(s): Erik Steringer
Abstract: Principal Mapper (PMapper) is an open-source tool and library for looking at AWS IAM and AWS Organizations for risks related to permissions. It can find and store information on how different users and roles can access each other as a way to expand their effective permissions. If you need to double-check your work on locking away your stuff in S3 or Secrets Manager, or if you need to make sure that an EC2 instance can’t be used to bring down your whole AWS account, PMapper is the tool for you.
Audience: Defense, Cloud
Links: https://github.com/nccgroup/PMapper/wiki
Bio(s): Erik Steringer is a security professional currently with NCC Group.
Ruse (VIRTUAL)
Discord Channel: #dl-ruse
Location: virtual Video 2
When: Sat 10:00–11:50
Presenter(s): Mike Kiser
Abstract: Facial recognition is eroding privacy and other human rights. Industry and government have ethical responsibilities to prevent this, but what if there were a way to enhance privacy for individuals without waiting for the cavalry? Adversarial technology gives people a way to protect this biometric. Ruse is an open-source mobile app that uses some of the research from the past year to enable “normal” people to protect the photos that they put online from being processed by commercial facial recognition products.
Audience: Consumer Mobile Offense
Links: https://github.com/derrumbe/Ruse
Bio(s): Mike Kiser is insecure. He has been this way since birth, despite holding a panoply of industry positions over the past 20 years — from the Office of the CTO to Security Strategist to Security Analyst to Security Architect — that might imply otherwise. In spite of this, he has designed, directed, and advised on large-scale security deployments for a global clientele. He is currently in a long-term relationship with fine haberdashery, is a chronic chronoptimist (look it up), and delights in needlessly convoluted verbiage. He speaks regularly at events such as the European Identity Conference and the RSA Conference, is a member of several standards groups, and has presented identity-related research at Black Hat and Def Con. He is currently a Senior Identity Strategist for SailPoint Technologies.
Solitude: A privacy analysis tool (VIRTUAL)
Discord Channel: #dl-solitude
Location: virtual Video 1
When: Fri 12:00–13:50
Presenter(s): Dan Hastings
Abstract: Solitude is an open-source privacy analysis tool that aims to help people inspect where their private data goes once it leaves their favorite mobile or web applications. Whether a curious novice or a more advanced researcher, Solitude makes the process of evaluating an app’s privacy accessible for everyone without the need for time-consuming app instrumentation and analysis, which we’ve abstracted away from the user. Privacy policies are often difficult to understand when trying to identify how your private data is being shared and with whom it’s being shared. My previous research1 has even shown that privacy policies don’t always tell the truth of what an app’s actual data collection practices actually are. What’s more, prior to Solitude, tooling to find this out efficiently didn’t exist for security researchers, let alone nontechnical users. Solitude was built to help give users more transparency to understand where their private data goes by the process of proxying HTTP traffic and inspecting HTTP traffic more straightforward, and can be configured to look for arbitrary datatypes captured by a mobile or web application. In its early release, this tool has already been used by journalists to help investigate privacy abuses by mobile app vendors.
Audience: Mobile, Offense, Privacy enthusiasts.
Links: https://github.com/nccgroup/Solitude
Bio(s): Dan Hastings is a senior security consultant at NCC Group. He spends his time performing mobile and web application penetration tests for fortune 500 companies. Dan has spoken at the Defcon Crypto and Privacy village on his research on discrepancies in iOS Robocall blocking apps privacy policies and their actual data collection practices.
The WiFi Kraken Lite (VIRTUAL)
Discord Channel: #dl-wifi-kraken-lite
Location: In-person Demolab 2
When: Fri 10:00–11:50
Presenter(s): Mike Spicer, Henry Hill
Abstract: D4rkm4tter and Henry have been obsessed with monitoring wireless networks and have built hardware to meet the challenges of scanning and testing in the most busy and client dense environments. The WiFi-Kraken Lite contends with these issues in a smaller package without sacrificing any monitoring performance. This project is the results of years of research into the most effective way to scan and audit wireless in a single box that can be easily deployed or used as a hardened terminal in the most rugged conditions. The WiFi-Kraken Lite consists of a single-board computer which connects 12 wireless radios that enables scanning and auditing WiFi, Bluetooth, LoRaWAN and other commonly used wireless protocols. The number of wireless devices is growing as well as the way those devices are being connected. Having an all-in-one wireless monitoring solution will give you the ability to track this data across these bands and give you the best picture of what’s happening in the air around you. This demonstration will provide you the information so that you can build your own all-in-one monitoring device. You will also gain an overview of capture technologies including Kismet that will help you perform this type of analysis in your own environments. Finally once the data is capture, you will get an understanding of efficient data processing using tools like Wireshark and d4rkm4tter’s own PCAPinator tool.
Audience: Offense, Defense and Hardware
Links: Palshack.org/wifi-kraken-lite
Bio(s): Mike Spicer (d4rkm4tter) is a mad scientist hacker who likes to meddle with hardware and software. He is particularly obsessed with wireless. He has a degree in computer science which he has put to use building and breaking a wide array of systems. These include web application pentesting, wireless monitoring and tracking as well as reverse engineering. He is the creator of the #WiFiCactus and has been seen presenting and demoing at a number of conferences including DEF CON. He is a Kismet cultist and active in the wireless and wardriving communities.
Henry Hill is an expert with computer hardware and is able to design and build the most bleeding edge systems that are the fastest in the world. His internal knowledge of architecture and system bottlenecks help him build systems capable of extreme processing and even faster storage. Henry is also an expert with mechanical engineering and fabrication. When his modifications aren’t appearing in d4rkm4tter’s projects, they can be seen in his race car at the track.
USBsamurai (VIRTUAL)
Discord Channel: #dl-usb-samurai
Location: virtual Video 2
When: Sat 12:00–13:50
Presenter(s): CyberAntani
Abstract: During this talk, after a bit of history of hardware implants, will be presented a new hacking device: USBsamurai. A remotely-controlled USB HID injecting cable that costs less than 10 EUR to produce from off-the-shelf components (a cable and a USB radio transceiver) that can be used to compromise targets remotely (i.e. over a 2.4GHz undetectable protocol) in the stealthiest way ever seen & also bypass Air-Gapped Environments like a boss!
Audience: Offense, Hardware, ICS
Links: https://medium.com/@LucaBongiorni/us...s-4bd47abf8f87
Bio(s): Luca Bongiorni is working as Head of Offensive Security. He is also actively involved in InfoSec where his main fields of research are: Radio Networks, Reverse Engineering, Hardware Hacking, Internet of Things, and Physical Security. He also loves to share his knowledge and present some cool projects at security conferences around the globe.

DCG 201 TALK HIGHLIGHTS FOR DEFCON 29 (PST)
This is the section where we have comb through the entire list of talks on both days and list our hilights for the talks that stand out to us. Note that this does not invalidate any talks we didn’t list, in fact, we highly recommend you take a look at the full convention scheduel beforehand and make up your own talk hilight lists. These are just the talks that for us had something stand out, either by being informative, unique or bizzare. (Sometimes, all three!)
Making the DEF CON 29 Badge
45 minutes | Demo
Michael Whiteley MKFactor.com
Katie Whiteley MKFactor.com
Speaker(s) will be at DEF CON!
Come meet the new badge makers and hear the story of how this year’s badge was created amidst a global pandemic. We’ll share tales of chip shortages, delayed parts, and late nights, as well as discuss how the badge works and what you can do with it. Maybe even some hints about the challenges within…
Michael Whiteley
Michael is a husband, father, and electronics geek. He doesn’t like long walks on the beach, but prefers to be indoors with a fast internet connection.
Katie Whiteley
Katie is a wife, mother, and graphic designer. She likes long walks on the beach because there’s no internet connection.
@ktjgeekmom
Combined they are MK Factor, a husband/wife badgemaker team. They’ve created badges for many conferences and groups like OpenWest, Saintcon, DC801, Car Hacking Village, and many unofficial DEF CON badges. Together they earned a black badge for Car Hacking at DEF CON 24.
HTTP/2: The Sequel is Always Worse
45 minutes | Demo, Tool, Exploit
James Kettle Director of Research, PortSwigger Web Security
Virtual only presentation
ALSO AT: BLACK HAT USA 2021
HTTP/2 is easily mistaken for a transport-layer protocol that can be swapped in with zero security implications for the website behind it. Two years ago, I presented HTTP Desync Attacks and kicked off a wave of request smuggling, but HTTP/2 escaped serious analysis. In this presentation, I’ll take you beyond the frontiers of existing HTTP/2 research, to unearth horrifying implementation flaws and subtle RFC oversights.
I’ll show you how these flaws enable HTTP/2-exclusive desync attacks, with case studies targeting high-profile websites powered by servers ranging from Amazon’s Application Load Balancer to WAFs, CDNs, and bespoke stacks by big tech. I’ll demonstrate critical impact by hijacking thick clients, poisoning caches, and stealing plaintext passwords to net multiple max-bounties.
After that, I’ll unveil novel techniques and tooling to crack open a widespread but overlooked request smuggling variant affecting both HTTP/1 and HTTP/2 that is typically mistaken for a false positive.
Finally, I’ll drop multiple exploit-primitives that resurrect a largely-forgotten class of vulnerability, and use HTTP/2 to expose fresh application-layer attack surface.
I’ll leave you with an open-source scanner, a custom, open-source HTTP/2 stack, and free interactive labs so you can hone your new skills on live systems.
REFERENCES:
The HTTP/2 RFC is essential reading: https://tools.ietf.org/html/rfc7540
This research is built on my previous work on this topic:
https://portswigger.net/research/http-desync-attacks-request-smuggling-reborn
This presentation by defparam has good explanations of response queue poisoning and self-desync attacks:
https://www.youtube.com/watch?v=3tpnuzFLU8g
I had a partial research collision with Emil Lerner. His work provides an alternative perspective on certain techniques:
https://github.com/neex/http2smugl
James Kettle
James Kettle is Director of Research at PortSwigger Web Security, where he cultivates novel web attack techniques. Recent work has focused on HTTP Request Smuggling, and using web cache poisoning to turn caches into exploit delivery systems. Past research includes server-side RCE via Template Injection, client-side RCE via malicious formulas in CSV exports, and abusing the HTTP Host header to poison password reset emails and server-side caches. He is also the author of multiple popular Burp Suite extensions including HTTP Request Smuggler, Param Miner and Turbo Intruder. He has spoken at numerous prestigious venues including DEF CON, both BlackHat USA and EU, and OWASP AppSec USA and EU.
@albinowax
https://skeletonscribe.net/
Gone Apple Pickin’: Red Teaming macOS Environments in 2021
45 minutes | Demo
Cedric Owens Offensive Security Engineer
Speaker(s) will be at DEF CON!
Though the vast majority of US companies are enterprise Windows shops, there is a growing percentage of companies that are shifting away from this model. Most of these types of companies tend to be based in the SF Bay Area and are often tech companies. This talk will provide a glimpse into what common attack paths in these environments look like in the absence of typical enterprise Active Directory implementations. Examples include techniques for targeting macOS endpoints, cloud and IdaaS, CI/CD pipeline, and other fun approaches. I will begin by discussing common tech stacks and macOS deployments and then move into macOS initial access (including the Gatekeeper bypass I found) and post exploitation options in these modern tech environments as well as detection opportunities.
Cedric Owens
Cedric is currently an offensive security engineer who came from a blue team background. His passion revolves around red teams and blue teams working closely together to improve each other’s tradecraft. Cedric enjoys researching techniques and writing tools related to macOS post exploitation and infrastructure automation.
His blogs can be found here: https://medium.com/@cedowens
His tools can be found here: https://github.com/cedowens
Between Two Servers — A Q&A with Sec. Mayorkas and Dark Tangent
45 minutes
Alejandro Mayorkas Secretary of the Department of Homeland Security
ALSO AT: BLACK HAT USA 2021
Dark Tangent
At DEF CON 29 DHS Secretary Alejandro Mayorkas will be doing a ‘between two servers’ style interview with Dark Tangent. We’re planning to engage with the new Secretary, and we hope you’ll engage with us — drop questions you want Jeff to ask by emailing info@defcon.org. SFW only please.
Do you like to read? I know how to take over your Kindle with an e-book
20 minutes
Slava Makkaveev Security Researcher, Check Point
Virtual only presentation
Since 2007, Amazon has sold tens of millions of Kindles, which is impressive. But this also means that tens of millions of people can be hacked through a software bug in those same Kindles. Their devices can be turned into bots, their private local networks can be compromised, and perhaps even information in their billing accounts can be stolen.
The easiest way to remotely reach a user’s Kindle is through an e-book. A malicious book can be published and made available for free access in any virtual library, including the Kindle Store, or sent directly to the end-user device via Amazon services. While you might not be happy with the writing in a particular book, nobody expects to download one that is malicious. No such scenarios have been publicized. Antiviruses do not have signatures for e-books. But… we succeeded in making a malicious book for you. If you open this book on a Kindle device, it causes a hidden piece of code to be executed with root rights. From this moment on, you lost your e-reader, account and more.
Want to know the details?
Slava Makkaveev
Slava Makkaveev is a Security Researcher at Check Point Software Technologies Ltd. Holds a PhD in Computer Science. Slava has found himself in the security field more than ten years ago and since that gained vast experience in reverse engineering and vulnerability research. Recently Slava has taken a particularly strong interest in mobile platforms and firmware security.
The Mechanics of Compromising Low Entropy RSA Keys
20 minutes
Austin Allshouse Staff Research Scientist / BitSight
Speaker(s) will be at DEF CON!
Over the past decade, there have been a number of research efforts (and DEFCON talks!) investigating the phenomenon of RSA keys on the Internet that share prime factors with other keys. This can occur when devices have poorly initialized sources of “randomness” when generating keys; making it trivial to factor the RSA modulus and recover the private key because, unlike large integer factorization, calculating the greatest common divisor (GCD) of two moduli can be fast and efficient. When describing their research, past hackers and researchers have attested that they “built a custom distributed implementation of Batch-GCD;” which seems like one hell of a detail to gloss over, right? This talk will detail a hacker’s journey from understanding and implementing distributed batch GCD to analyzing findings from compromising RSA keys from network devices en masse.
REFERENCES:
Amiet, Nils and Romailler, Yolan. “Reaping and breaking keys at scale: when crypto meets big data.” DEF CON 26, 2018.
Heninger, Nadia, et al. “Mining your Ps and Qs: Detection of widespread weak keys in network devices.” 21st {USENIX} Security Symposium ({USENIX} Security 12). 2012.
Hastings, Marcella, Joshua Fried, and Nadia Heninger. “Weak keys remain widespread in network devices.” Proceedings of the 2016 Internet Measurement Conference. 2016.
Kilgallin, JD. “Securing RSA Keys & Certificates for IoT Devices.” https://info.keyfactor.com/factoring-rsa-keys-in-the-iot-era. 2019
Daniel J. Bernstein. Fast multiplication and its applications, 2008.
Austin Allshouse
Austin Allshouse is a Research Scientist at BitSight where he applies information security, statistical modeling, and distributed computing concepts to develop quantitative methods of assessing security risk. He has a decade of experience researching the technologies and methodologies underpinning digital network surveillance systems.
eBPF, I thought we were friends !
45 minutes | Demo, Tool
Guillaume Fournier Security Engineer at Datadog
Sylvain Afchain Staff Engineer at Datadog
Sylvain Baubeau Staff Engineer at Datadog
Virtual only presentation
Since its first appearance in Kernel 3.18, eBPF (Extended Berkley Packet Filter) has progressively become a key technology for observability in the Linux kernel. Initially dedicated to network monitoring, eBPF can now be used to monitor and trace any kind of kernel space activity.
Over the past few years, many vendors have started using eBPF to speed up their services or introduce innovative features. Cilium, Calico, Cloudflare, Netflix and Facebook are leading the charge, showing off new complex networking use cases on a monthly basis. On the security side of things, Google recently contributed the Kernel Runtime Security Instrumentation which opens the door to writing Linux Security Modules with eBPF.
In other words, eBPF is the new kid in town and a growing number of companies are running services with eBPF access in production. This leads us to a simple question: how bad can things get if one of those services were to be compromised ? This talk will cover how we leveraged eBPF to implement a full blown rootkit with all the features you would expect: various obfuscation techniques, command and control with remote and persistent access, data theft and exfiltration techniques, Runtime Application Self-Protection evasion techniques, and finally two original container breakout techniques.
Simply put, our goal is to demonstrate that rogue kernel modules might have finally found a worthy opponent. We will also detail how to detect such attacks and protect your infrastructure from them, while safely enjoying the exciting capabilities that eBPF has to offer.
REFERENCES:
Bibliography and documentation links cited in the submission:
1. Russian GRU 85th GTsSS deploys previously undisclosed drovorub malware, NSA / FBI, August 2020 https://media.defense.gov/2020/Aug/13/2002476465/-1/-1/0/CSA_DROVORUB_RUSSIAN_GRU_MALWARE_AUG_2020.PDF
2. Kprobe-based Event Tracing, https://www.kernel.org/doc/html/latest/trace/kprobetrace.html
3. Linux Kernel tracepoints, https://www.kernel.org/doc/html/latest/trace/tracepoints.html
4. “bpf_probe_write_user” bpf helper, https://elixir.bootlin.com/linux/v5.11.11/source/include/uapi/linux/bpf.h#L1472
5. Uprobe-based Event Tracing, https://www.kernel.org/doc/html/latest/trace/uprobetracer.html
6. Cilium’s XDP documentation, https://docs.cilium.io/en/latest/bpf/#xdp
Previous eBPF related talks & projects that helped us build the rootkit:
7. Evil eBPF In-Depth: Practical Abuses of an In-Kernel Bytecode Runtime, Jeff Dileo, DEF CON 27, https://www.defcon.org/html/defcon-27/dc-27-speakers.html#Dileo
8. Process level network security monitoring and enforcement with eBPF, Guillaume Fournier, https://www.sstic.org/2020/presentation/process_level_network_security_monitoring_and_enforcement_with_ebpf/
9. Runtime Security with eBPF, Sylvain Afchain, Sylvain Baubeau, Guillaume Fournier, https://www.sstic.org/2021/presentation/runtime_security_with_ebpf/
10. Monitoring and protecting SSH sessions with eBPF, Guillaume Fournier, https://www.sstic.org/2021/presentation/monitoring_and_protecting_ssh_sessions_with_ebpf/
Guillaume Fournier
Guillaume Fournier is a Security Engineer at Datadog where he focuses on developing a new generation of runtime security tools powered by eBPF. In his free time, he likes to build defensive and offensive security tools such as a chrome-like sandbox for VLC on Linux, or various projects to automate drones and wireless keyboards hacking.
Sylvain Afchain
Sylvain Afchain is a staff software engineer at Datadog. He’s been working on linux for more than 15 years. He mostly worked on distributed systems, cloud infrastructure and SDN solutions. In his spare time, he enjoys cycling, playing tennis and badminton.
Sylvain Baubeau
Sylvain Baubeau is a staff software engineer, mostly working on Linux, cloud and infrastructure technologies. In his spare time, he likes to play drums, reverse engineer old games and build arcades.
Rotten code, aging standards, & pwning IPv4 parsing across nearly every mainstream programming language
45 minutes | Demo, Exploit
Kelly Kaoudis
Sick Codes Hacker
Virtual only presentation
Openness to responsibly disclosed external vulnerability research is crucial for modern software maintainers and security teams. Changes in upstream dependency code may have pulled the safety rug out from underneath widely trusted core libraries, leaving millions of services vulnerable to unsophisticated attacks. The impact of even a single reasonably well-distributed supply-chain security vulnerability will be felt by engineering teams across many applications, companies, and industries.
We’d like to discuss an IP address parsing vulnerability first discovered in private-ip, a small and infrequently maintained yet critically important NodeJS package for determining if an IP address should be considered part of a private range or not. We’ll talk about not only the implications of this CVE but taking the main idea and applying it across multiple programming languages in uniquely disturbing ways.
Sometimes, the effects of code rot are even more far-reaching than we could possibly expect, and if you pull on a thread, it just keeps going. Sometimes, you get lucky when you know exactly what you’re looking for. Sometimes, it’s hard to convince other technically-minded folks that a seemingly trivial implementation flaw is dangerous in capable hands.
This talk is beginner as well as advanced-friendly; we’ll show you the basics a hacker or a programmer needs to know about IP address parsing and how to tell your octal from your decimal along the way.
REFERENCES:
Researchers involved in this work:
— Victor Viale: https://github.com/koroeskohr, koroeskohr
— Sick Codes: https://github.com/sickcodes, sickcodes
— Kelly Kaoudis: https://github.com/kaoudis, kaoudis
— John Jackson: https://www.johnjhacking
— Nick Sahler: https://github.com/nicksahler, tensor_bodega
— Cheng Xu: https://github.com/xu-cheng
Selected press coverage (as of May ‘21)
— https://www.bleepingcomputer.com/news/security/critical-netmask-networking-bug-impacts-thousands-of-applications/
— https://www.theregister.com/2021/03/29/netmask_cve/
— https://www.bleepingcomputer.com/news/security/python-also-impacted-by-critical-ip-address-validation-vulnerability/
Currently released advisories related to this work (as of May ‘21)
— https://sick.codes/sick-2021-011/
— https://vuln.ryotak.me/advisories/6
— https://sick.codes/sick-2021-018/
— https://sick.codes/sick-2020-022/
Additional
— https://sick.codes/universal-netmask-npm-package-used-by-270000-projects-vulnerable-to-octal-input-data-server-side-request-forgery-remote-file-inclusion-local-file-inclusion-and-more-cve-2021-28918/
— https://blog.urth.org/2021/03/29/security-issues-in-perl-ip-address-distros/
— https://blog.dave.tf/post/ip-addr-parsing/
— https://security-tracker.debian.org/tracker/CVE-2021-29424
— https://security-tracker.debian.org/tracker/CVE-2021-29662
— https://www.npmjs.com/package/netmask
— https://github.com/rs/node-netmask
— https://bugs.python.org/issue36384#msg392423
— https://github.com/rust-lang/rust/pull/83652
— https://github.com/rust-lang/rust/issues/83648
Kelly Kaoudis
Kelly Kaoudis is a senior software engineer working in application security in Colorado. Following working with the group to validate and test the node-netmask bypass Viale discovered, Kaoudis wrote many of the proofs-of-concept which demonstrate the critical impact of this cascade of unique vulnerabilities.
@kaoudis
https://github.com/kaoudis
Sick Codes
Sick Codes maintains popular open source projects, publishes high-profile security vulnerabilities in good faith, and administers his namesake https://sick.codes, a security research and tutorial resource for developers. Sick Codes’ work coordinating communication across many companies, foundations, and other open source organisations was invaluable in getting these vulnerabilities patched and responsibly disclosed.
@sickcodes
https://sick.codes
https://github.com/sickcodes
https://www.linkedin.com/in/sickcodes/
Abusing SAST tools! When scanners do more than just scanning
45 minutes | Demo
Rotem Bar Head of Marketplace Integrations @ Cider Security
Speaker(s) will be at DEF CON!
When we write code, we often run many scanners for different purposes on our code — from linters, to testing, security scanning, secret scanning, and more.
Scanning the code occurs on developers’ machines and in CI/CD pipelines, which assumes the code is untrusted and unverified and based on this assumption scanners shouldn’t have the ability to dynamically run code.
Our research focuses on the many static analyzers out there if this is really the case. Many of the scanners allow different ways of interaction — From requesting external resources, overriding the configuration and to remote code execution as part of the process.This talk will be technical and show examples of well-known scanning tools and how we created code that attacks them.
TLDR -
When integrating and using new tools in our CI systems and especially when running on unverified code, Which tools can we trust and how can we scan safe untrusted code in a secure way?
REFERENCES:
https://github.com/jonase/kibit/issues/235 — Issue I raised in the past in one of the tools
Hiroki Suezawa in a thread in cloud security forum talked about exploiting terraform plan https://cloudsecurityforum.slack.com/archives/CNJKBFXMH/p1584035704035800
This reference was released after I’ve started my research but nevertheless a good resource and has interesting perspectives and I will reference it: https://alex.kaskaso.li/post/terraform-plan-rce
Rotem Bar
Rotem Bar has over a decade of experience in the security field including penetration testing both application and network, design reviews, code reviews, architecture reviews, tech management, and of course development.
Over the years Rotem has gained experience in a diversity of industries from the financial services, to insurance, through high-tech & the automotive industry, along with other complex environments.
In the last couple of years Rotem has been working in concept design and development, pen testing and working with hardware in Cymotive, which is a company that focuses on end to end cyber security for the automotive industry, and after that he served as an application security expert at AppsFlyer.
Today Rotem is the Head of Marketplace Integrations at Cider Security, that is focusing on revolutionizing CI/CD security.
During his free time, Rotem plays with robotics, bug-bounty and and enjoys traveling with his family.
Defending against nation-state (legal) attack: how to build a privacy-protecting service in the era of ubiquitous surveillance
45 minutes
Bill “Woody” Woodcock Chair of the Foundation Council, Quad9
Speaker(s) will be at DEF CON!
US diplomacy and the US District Court of Northern California provide a nearly impenetrable shield against legal assault from other countries for the many tech companies that choose the San Francisco Bay Area as their legal domicile. But US domicile has left companies undefended against ECPA, CALEA, Patriot Act and FISA requests and the gag orders which prevent their disclosure, and the US has little or no statutory protections for users’ privacy. So how do you hack the international legal and diplomatic system to defend the privacy of users of Internet services against nation-state legal attacks? The privacy-and-security-oriented non-profit DNS recursive resolver Quad9 spent four years working the system and learning from prior examples like ProtonMail, and Bill Woodcock, the chair of Quad9’s Foundation Council, will talk about the threat model Quad9 is defending against, how legal domicile and physical presence interact, and how Quad9 is building a model that other privacy-respecting services can follow. He’ll discuss the critical differences between jurisdictions and legal regimes that Quad9 uncovered in their four-year selection process, and the key and differentiating protections the Swiss government offers that the US and EU governments do not. And if y’all get tired of that, you might be able to convince him to talk about the injunction Sony Music got against Quad9 in the copyright-troll court in Hamburg and why more privacy may also come at the risk of more censorship.
Bill “Woody” Woodcock
Bundles of Joy: Breaking macOS via Subverted Applications Bundles
45 minutes | Demo
Patrick Wardle Founder, Objective-See
Speaker(s) will be at DEF CON!
A recent vulnerability, CVE-2021–30657, neatly bypassed a myriad of foundational macOS security features such as File Quarantine, Gatekeeper, and Notarization. Armed with this capability attackers could (and were!) hacking macOS systems with a simple user (double)-click. Yikes!
In this presentation we’ll dig deep into the bowels of macOS to uncover the root cause of the bug: a subtle logic flaw in the complex and undocumented policy subsystem. Moreover, we’ll highlight the discovery of malware exploiting this bug as an 0day, reversing Apple’s patch, and discuss novel methods of both detection and prevention.
REFERENCES:
“All Your Macs Are Belong To Us”
https://objective-see.com/blog/blog_0x64.html
“macOS Gatekeeper Bypass (2021 Edition)”
https://cedowens.medium.com/macos-gatekeeper-bypass-2021-edition-5256a2955508
“Shlayer Malware Abusing Gatekeeper Bypass On Macos”
https://www.jamf.com/blog/shlayer-malware-abusing-gatekeeper-bypass-on-macos/
Patrick Wardle
Patrick Wardle is the founder of Objective-See. Having worked at NASA and the NSA, as well as presenting at countless security conferences, he is intimately familiar with aliens, spies, and talking nerdy. Patrick is passionate about all things related to macOS security and thus spends his days finding Apple 0days, analyzing macOS malware, and writing free open-source security tools to protect Mac users.
@patrickwardle
https://objective-see.com/
D0 N0 H4RM: A Healthcare Security Conversation
105 minutes | Demo
Christian “quaddi” Dameff MD Physician & Medical Director of Cyber Security at The University of California San Diego
Jeff “r3plicant” Tully MD Anesthesiologist at The University of California San Diego
Jessica Wilkerson Cyber Policy Advisor at the US Food and Drug Administration FDA
Josh Corman Chief Strategist for CISA, Founder of I am The Cavalry
Gabrielle Hempel Cloud Security Engineer/Medical Security Researcher
Stephanie Domas Director of Cybersecurity Strategy and Communications at Intel
Speaker(s) will be at DEF CON!
Mired in the hell of a global pandemic, hospital capacity stressed to its limit, doctors and nurses overworked and exhausted… surely the baddies would cut us a little slack and leave little ‘ol healthcare alone for a bit, right? Well, raise your hand if you saw this one coming. Another year of rampaging ransomware, of pwned patient care- only this time backdropped by the raging dumpster fire that is COVID. Can we once and for all dispel with the Pollyannas telling us that nobody would knowingly seek to harm patients? And if we can’t convince the powers that be- whether in the hospital C-suite or in DC- that we need to take this $%& seriously now, then what hope do we have for pushing patient safety to the forefront when things return to some semblance of normal? With a heavily curated panel including policy badasses, elite hackers, and seasoned clinicians — D0 N0 H4RM remains the preeminent forum where insight from experts collide with the ingenuity and imagination of the DEF CON grassroots to inspire activism and collaboration stretching far beyond closing ceremonies.
Moderated by physician hackers quaddi and r3plicant, this perennially packed event always fills up fast — so make sure you join us. As always- the most important voice is yours.
Dr. Christian Dameff MD
Christian (quaddi) Dameff MD is an Assistant Professor of Emergency Medicine, Biomedical Informatics, and Computer Science (Affiliate) at the University of California San Diego. He is also a hacker, former open capture the flag champion, and prior DEF CON/RSA/Blackhat/HIMSS speaker. Published works include topics such as therapeutic hypothermia after cardiac arrest, novel drug targets for myocardial infarction patients, and other Emergency Medicine related works with an emphasis on CPR optimization. Published security research topics including hacking critical healthcare infrastructure, medical devices and the effects of malware on patient care. This is his seventeenth DEF CON.
Dr. Jeff Tully MD
Jeff (r3plicant) Tully is an anesthesiologist, pediatrician and security researcher with an interest in understanding the ever-growing intersections between healthcare and technology.
Jessica Wilkerson
Jessica Wilkerson is a Cyber Policy Advisor with the All Hazards Readiness, Response, and Cybersecurity (ARC) team in the Center for Devices and Radiological Health (CDRH) within the Food and Drug Administration (FDA). As part of ARC, she examines issues and develops policy related to the safety and effectiveness of connected medical devices. She received a B.A. in Policy Studies and minors in Computer Science and Mathematics from Syracuse University, and is currently pursuing a J.D. from the Catholic University of America’s Columbus School of Law.
Josh Corman
Joshua Corman is a Founder of I am The Cavalry (dot org), and serves as Chief Strategist for CISA regarding COVID, healthcare, and public safety. He previously served as CSO for PTC, Director of the Cyber Statecraft Initiative for the Atlantic Council, CTO for Sonatype, and other senior roles. He co-founded RuggedSoftware and IamTheCavalry to encourage new security approaches in response to the world’s increasing dependence on digital infrastructure. His unique approach to security in the context of human factors, adversary motivations, and social impact has helped position him as one of the most trusted names in security. He also serves as an Adjunct Faculty for Carnegie Mellon’s Heinz College, and was a member of the Congressional Task Force for Healthcare Industry Cybersecurity.NOTE: My CISA Emergency CARES Act Service may extend/change after July 15.
Gabrielle Hempel
I am a graduate of the University of Cincinnati, where I studied Neuroscience and Psychology with a minor in Criminal Justice. I started out at an institutional review board in regulatory pharmaceutical and medical device compliance, and led specialized committees targeting Phase I research and emergency research. I moved to IT consulting in 2018, and currently work as a Security Engineer in healthcare while pursuing an MS in Global Security, Conflict, and Cybercrime at NYU. I continue to serve as a genetic scientist for NIH-regulated recombinant genetic studies, and sit on multiple advisory boards. My continued areas of focus include medical device security, connected healthcare security, and the intersections of the healthcare and information security industries.
Stephanie Domas
Stephanie Domas is the Director of Cybersecurity Strategy and Communications at Intel. Here, she leads development of complex security strategies for the critical role that hardware and firmware security play in the digital ecosystem. Prior to Intel, Stephanie was spent 8 years focused on medical device cybersecurity, consulting with a broad range of manufacturers from the newest startups to the industry giants. She is the founder and lead trainer for cybersecurity training company DazzleCatDuo. Her past experience includes 10 years of reverse engineering and vulnerability analysis research as a defense contractor. Stephanie is a recognized expert on embedded systems, healthcare and medical device security, a seasoned executive, a prominent consultant, a passionate educator, and x86 enthusiast.
Warping Reality — creating and countering the next generation of Linux rootkits using eBPF
45 minutes | Demo, Tool
PatH Security Researcher
Virtual only presentation
With complete access to a system, Linux kernel rootkits are perfectly placed to hide malicious access and activity. However, running code in the kernel comes with the massive risk that any change to a kernel version or configuration can mean the difference between running successfully and crashing the entire system. This talk will cover how to use extended Berkley Packet Filters (eBPF) to create kernel rootkits that are safe, stable, stealthy, and portable.
eBPF is one of the newest additions to the Linux kernel, designed to easily load safe, constrained, and portable programs into the kernel to observe and make decisions about network traffic, syscalls, and more. But that’s not it’s only use: by creating eBPF programs that target specific processes we can warp reality, presenting a version of a file to one program and a different version to another, all without altering the real file on disk. This enables techniques such as presenting a backdoor user to ssh while hiding from sysadmins, or smuggling data inside connections from legitimate programs. This talk will also cover how to use these same techniques in malware analysis to fool anti-sanbox checks.
These ideas and more are explored in this talk alongside practical methods to detect and prevent this next generation of Linux rootkits.
REFERENCES:
— DEFCON 27 — Evil eBPF Practical Abuses of In-kernel Bytecode Runtime
— A talk about abusing eBPF for exploitation and privilege escalation
— eBPF Website
— https://ebpf.io
— A website by the eBPF community with documentation and links to existing projects
— eBPF Slack
— https://ebpf.io/slack
— A Slack channel run by the eBPF community
— Libbpf Bootstrap
— https://github.com/libbpf/libbpf-bootstrap
— A sample project designed to provide a template to creating eBPF programs with Libbpf
— — — — — — — — — — — — — —
PatH
Pat is a loving partner, a comedian to his daughter, and a dedicated ball retriever to his dog.
When he’s not spending time being those things, he’s a senior security researcher at a public cybersecurity company. Having previously worked as a low-level software dev, he now helps threat hunters uncover and stop advanced actors across the globe.
@pathtofile
https://path.tofile.dev/
Privacy Without Monopoly: Paternalism Works Well, But Fails Badly
45 minutes
Cory Doctorow Author, journalist, activist.
Virtual only presentation
Governments around the world (US, UK, EU) are planning to force interoperability on the biggest tech platforms. Companies like Facebook say that this is a privacy disaster because it would hurt their ability to keep us safe from privacy invasions. Yeah, I know. But even if you DO think Facebook has our best interests at heart, monopoly is a deeply stupid way protect privacy. I will present “Privacy Without Monopoly,” a major EFF white paper I co-authored with Bennett Cyphers, which sets out a framework for understanding how privacy and interop aren’t just compatible — they rely on one another!
https://www.eff.org/wp/interoperability-and-privacy
Cory Doctorow
Cory Doctorow (craphound.com) is a science fiction novelist, journalist and technology activist. He is a contributor to many magazines, websites and newspapers. He is a special consultant to the Electronic Frontier Foundation (eff.org), a non-profit civil liberties group that defends freedom in technology law, policy, standards and treaties. He holds an honorary doctorate in computer science from the Open University (UK), where he is a Visiting Professor; he is also a MIT Media Lab Research Affiliate and a Visiting Professor of Practice at the University of North Carolina’s School of Library and Information Science. In 2007, he served as the Fulbright Chair at the Annenberg Center for Public Diplomacy at the University of Southern California.
His novels have been translated into dozens of languages and are published by Tor Books, Head of Zeus (UK), Titan Books (UK) and HarperCollins (UK). He has won the Locus, Prometheus, Copper Cylinder, White Pine and Sunburst Awards, and been nominated for the Hugo, Nebula and British Science Fiction Awards.
His recent books include ATTACK SURFACE (2020), a standalone sequel to LITTLE BROTHER intended for adults, POESY THE MONSTER SLAYER, a picture book for young children (2020), the nonfiction tech/politics book HOW TO DESTROY SURVEILLANCE CAPITALISM (2020), RADICALIZED (2019) and WALKAWAY (2017), science fiction for adults; and IN REAL LIFE, a young adult graphic novel created with Jen Wang (2014).
His latest young adult novel is HOMELAND, the bestselling sequel to 2008’s LITTLE BROTHER. His New York Times Bestseller LITTLE BROTHER was published in 2008. His latest short story collection is WITH A LITTLE HELP, available in paperback, ebook, audiobook and limited edition hardcover. In 2011, Tachyon Books published a collection of his essays, called CONTEXT: FURTHER SELECTED ESSAYS ON PRODUCTIVITY, CREATIVITY, PARENTING, AND POLITICS IN THE 21ST CENTURY (with an introduction by Tim O’Reilly) and IDW published a collection of comic books inspired by his short fiction called CORY DOCTOROW’S FUTURISTIC TALES OF THE HERE AND NOW. THE GREAT BIG BEAUTIFUL TOMORROW, a PM Press Outspoken Authors chapbook, was also published in 2011.
LITTLE BROTHER was nominated for the 2008 Hugo, Nebula, Sunburst and Locus Awards. It won the Ontario Library White Pine Award, the Prometheus Award as well as the Indienet Award for bestselling young adult novel in America’s top 1000 independent bookstores in 2008; it was the San Francisco Public Library’s One City/One Book choice for 2013. It has also been adapted for stage by Josh Costello.
He co-founded the open source peer-to-peer software company OpenCola, and serves on the boards and advisory boards of the Participatory Culture Foundation, the Clarion Foundation, the Open Technology Fund and the Metabrainz Foundation. He maintains a daily blog at Pluralistic.net.
Crossover Episode: The Real-Life Story of the First Mainframe Container Breakout
45 minutes | Demo
Ian Coldwater Hacker
Chad Rikansrud (Bigendian Smalls) Hacker
Speaker(s) will be at DEF CON!
You’ve seen talks about container hacking. You’ve seen talks about mainframe hacking. But how often do you see them together? IBM decided to put containers on a mainframe, so a container hacker and a mainframe hacker decided to join forces and hack it. We became the first people on the planet to escape a container on a mainframe, and we’re going to show you how.
Containers on a mainframe? For real. IBM zCX is a Docker environment running on a custom Linux hypervisor built atop z/OS — IBM’s mainframe operating system. Building this platform introduces mainframe environments to a new generation of cloud-native developers-and introduces new attack surfaces that weren’t there before.
In this crossover episode, we’re going to talk about how two people with two very particular sets of skills went about breaking zCX in both directions, escaping containers into the mainframe host and spilling the secrets of the container implementation from the mainframe side.
When two very different technologies get combined for the first time, the result is new shells nobody’s ever popped before.
REFERENCES: Getting started with z/OS Container Extensions and Docker: https://www.redbooks.ibm.com/abstracts/sg248457.html
The Path Less Traveled: Abusing Kubernetes Defaults: https://www.youtube.com/watch?v=HmoVSmTIOxM
Attacking and Defending Kubernetes Clusters: A Guided Tour: https://securekubernetes.com
Evil Mainframe penetration testing course :https://www.evilmainframe.com/
z/OS Unix System Services (USS): https://www.ibm.com/docs/en/zos/2.1.0?topic=system-basics-zos-unix-file
z/OS Concepts: https://www.ibm.com/docs/en/zos-basic-skills?topic=zc-zos-operating-system-providing-virtual-environments-since-1960s
Docker overview: https://docs.docker.com/get-started/overview/
Ian Coldwater
Ian is a leading expert on containers and container security.
Chad Rikansrud (Bigendian Smalls)
Chad is the same, but for mainframes and mainframe security.
Hacking Viber Messenger with 0day Vulnerabilities: Sniffing and DoS
45 minutes | Demo, Tool, Exploit
Samarkand CEO at Samarkand Web Studio.
Speaker(s) will be at DEF CON!
Viber is a widely adopted mobile messaging application with over 500 million installations.
Nevertheless, no comprehensive digital forensic analysis has been performed with regards to it.
In this work, we describe how to:
a) decrypt Viber signaling protocol
b) deanonimize members of Viber communities
c) read deleted group messages
d) delete any Viber account with 0day vulnerability
We explain the methods and tools used to decrypt the traffic as well as thoroughly elaborate on our findings with respect to the Viber signaling messages. Furthermore, we also provide the community with a tool that helps in the visualization of the Viber protocol messages.
REFERENCES:
1. https://www.viber.com/app/uploads/Viber-Encryption-Overview.pdf
10. Wireshark protocol analyzer: https://www.wireshark.org/
11. Mitmproxy HTTPS sniffer: https://mitmproxy.org
20. Hacking Cable Modem. DerEngel. No Starch Press.
21. https://media.ccc.de/v/32c3-7133-beyond_your_cable_modem
22. https://hacker-gadgets.com/product/throwing-star-lan-tap/
30. Pro Android 4. Satya Komatineni, Dave MacLean. Apress.
31. Nox Android emulator: https://www.bignox.com/
32. JADX decompiler: https://github.com/skylot/jadx
40. PEiD and Krypto Analyzer (KANAL): https://www.peid.info
41. https://botan.randombit.net/
50. GDB debugger for Android: https://gnutoolchains.com/android/
51. GDB Documentation: http://www.gnu.org/software/gdb/documentation/
52. Perl language: https://www.perl.org/
60. Chris Eagle — The IDA Pro book. The unofficial guide to the world’s most popular disassembler. No Starch Press (2011).
61. IDA — The Interactive Disassembler by Ilfak Guilfanov: https://www.hex-rays.com/
70. Python language: https://www.python.org/
71. Learning Python. Mark Lutz. O’Reilly.
80. The C Programming language. Brian W. Kernighan, Dennis M. Ritchie.
81. The C++ Programming language. Bjarne Stroustrup. AT&T Labs.
90. Fake phone numbers: https://onlinesim.ru
91. CVE-2019–18800 vulnerability by Samarkand: https://nvd.nist.gov/vuln/detail/CVE-2019-18800
92. Hashcat password cracker: https://github.com/hashcat/hashcat
93. https://www.viber.com/en/blog/2019-11-04/communities-vs-group-chats-whats-best-for-you/
94. https://www.viber.com/en/blog/2019-02-17/spark-safer-conversations-with-hidden-number-chats/
95. Michael Howard, David LeBlank. Writing Secure Code. Microsoft Press.
96. https://github.com/mitmproxy/mitmproxy/blob/master/examples/contrib/sslstrip.py
Samarkand
Samarkand is painter, student of Economic faculty and CEO of Samarkand Web Studio. He works as freelance security researcher at https://freelancehunt.com/freelancer/thesamarkand.html
https://samarkand.000space.com/
https://thesamarkand.tumblr.com/
Wibbly Wobbly, Timey Wimey — What’s Really Inside Apple’s U1 Chip
45 minutes | Demo, Tool
ALSO AT: BLACK HAT USA 2021
jiska TU Darmstadt, SEEMOO
Alexander Heinrich TU Darmstadt, SEEMOO
Virtual only presentation
Apple introduced an Ultra Wideband (UWB) chip in the iPhone 11. Its cryptographically secured spatial measurement capabilities are accessible via the Nearby Interaction framework since iOS 14. As of now, it only supports interaction with other Apple devices including the latest Apple Watch and HomePod mini. These are the first steps to support UWB in a larger ecosystem, as measuring precise distance and direction can be an enabler for various future applications. The automotive industry already announced UWB support for mobile car keys on the iPhone.
But what’s really inside Apple’s U1 chip, internally called Rose? In this talk, we will travel through time, space, firmware and kernel components — and fight daemons to modify firmware interaction from user space. This will not only cover one or two, but three firmwares that process or forward each Rose time measurement: The Rose Digital Signal Processor (DSP), Rose Application Processor (AP), and the Always-On Processor (AOP).
REFERENCES:
There’s almost nothing known about UWB on the iPhones… So the only reference is this:
https://support.apple.com/guide/security/ultra-wideband-security-sec1e6108efd/web
jiska
Jiska breaks things.
Alexander Heinrich
Alexander is a security researcher at the Secure Mobile Networking Lab at the Technical University of Darmstadt. Before he joined the university as a researcher he gained a lot of experiences an an app developer on Apple operating systems starting with iOS 5. This deep understanding of the systems naturally resulted in a focus on those systems in his security research. He joined the Secure Mobile Networking Lab 2020 as a PhD student right after his Master Thesis on the security of Apple’s Handoff and Universal Clipboard features. After working with a team of skilled researchers on AirDrop and Apple’s Find My network his focus now shifted to the security and privacy of ultra-wideband and Apple U1 chip.
Bring Your Own Print Driver Vulnerability
45 minutes | Tool, Exploit
Jacob Baines Vulnerability researcher at Dragos
Virtual only presentation
What can you do, as an attacker, when you find yourself as a low privileged Windows user with no path to SYSTEM? Install a vulnerable print driver! In this talk, you’ll learn how to introduce vulnerable print drivers to a fully patched system. Then, using three examples, you’ll learn how to use the vulnerable drivers to escalate to SYSTEM.
REFERENCES:
— Yarden Shafir and Alex Ionescu, PrintDemon: Print Spooler Privilege Escalation, Persistence & Stealth (CVE-2020–1048 & more) — https://windows-internals.com/printdemon-cve-2020-1048/
— voidsec, CVE-2020–1337 — PrintDemon is dead, long live PrintDemon! — https://voidsec.com/cve-2020-1337-printdemon-is-dead-long-live-printdemon/
— Zhipeng Huo and Chuanda Ding, Evil Printer: How to Hack Windows Machines with Printing Protocol — https://media.defcon.org/DEF CON 28/DEF CON Safe Mode presentations/DEF CON Safe Mode — Zhipeng-Huo and Chuanda-Ding — Evil Printer How to Hack Windows Machines with Printing Protocol.pdf
— Pentagrid AG, Local Privilege Escalation in many Ricoh Printer Drivers for Windows (CVE-2019–19363) — https://www.pentagrid.ch/en/blog/local-privilege-escalation-in-ricoh-printer-drivers-for-windows-cve-2019-19363/
— space-r7, Add module for CVE-2019–19363 — https://github.com/rapid7/metasploit-framework/pull/12906
— Microsoft, Point and Print with Packages — https://docs.microsoft.com/en-us/windows-hardware/drivers/print/point-and-print-with-packages
— Microsoft, Driver Store — https://docs.microsoft.com/en-us/windows-hardware/drivers/install/driver-store
— Microsoft, Printer INF Files — https://docs.microsoft.com/en-us/windows-hardware/drivers/print/printer-inf-files
— Microsoft, Use Group Policy settings to control printers in Active Directory — https://docs.microsoft.com/en-us/troubleshoot/windows-server/printing/use-group-policy-to-control-ad-printer
Jacob Baines
Jacob is a vulnerability researcher at Dragos. He enjoys focusing much of his research time on routers and other embedded devices. Occasionally, he finds himself looking at Windows internals. Sometimes he even finds vulnerabilities.
Hack the hackers: Leaking data over SSL/TLS
20 minutes | Demo, Exploit
Ionut Cernica PHD Student @Department of Computer Science, Faculty of Automatic Control and Computer Science, University Politehnica of Bucharest
Speaker(s) will be at DEF CON!
Have you considered that in certain situations the way hackers exploit vulnerabilities over the network can be predictable? Anyone with access to encrypted traffic can reverse the logic behind the exploit and thus obtain the same data as the exploit.
Various automated tools have been analyzed and it has been found that these tools operate in an unsafe way. Various exploit databases were analyzed and we learned that some of these are written in an insecure (predictable) way.
This presentation will showcase the results of the research, including examples of exploits that once executed can be harmful. The data we obtain after exploitation can be accessible to other entities without the need of decrypting the traffic. The SSL/TLS specs will not change. There is a clear reason for that and in this presentation I will argue this, but what will change for sure is the way hackers will write some of the exploits.
Ionut Cernica
Ionut Cernica started his security career with the bug bounty program from Facebook. His passion for security led him to get involved in dozens of such programs and he found problems in very large companies such as Google, Microsoft, Yahoo, AT&T, eBay, VMware. He has also been testing web application security for 9 years and has had a large number of projects on the penetration testing side.
Another stage of his career was to get involved in security contests and participated in more than 100 such contests. He also reached important finals such as Codegate, Trend Micro and Defcon with the PwnThyBytes team. He also won several individual competitions, including the mini CTF from the first edition of Appsec village — Defcon village.
Now he is doing research in the field of web application security, being also a PhD student at University Polytechnic of Bucharest. Through his research he wants to innovate in the field and to bring a new layer of security to web applications. He has also been working as a Security Researcher @Future Networks 5G Lab for a few months now and hopes to make an important contribution to the 5G security area through research.
Defeating Physical Intrusion Detection Alarm Wires
45 minutes | Tool
Bill Graydon Principal, Research, GGR Security
Speaker(s) will be at DEF CON!
Alarm systems are ubiquitous — no longer the realm of banks and vaults only, many people now have them in their homes or workplaces. But how do they work? And the logical follow-up question — how can they be hacked?
This talk focuses on the communication lines in physical intrusion detection systems: how they are secured, and what vulnerabilities exist. We’ll discuss the logic implemented in the controllers and protections on the communication lines including end of line resistors — and all the ways that this aspect of the system can be exploited.
In particular, we’ll release schematics for a tool we’ve developed that will enable measuring end-of-line resistor systems covertly, determining the necessary re-wiring to defeat the sensors, and deploy it without setting off the alarm.
After the talk, you can head over to the Lock Bypass Village to try these techniques out for yourself!
Bill Graydon
Bill Graydon is a principal researcher at GGR Security, where he hacks everything from locks and alarms to critical infrastructure; this has given him some very fine-tuned skills for breaking stuff. He’s passionate about advancing the security field through research, teaching numerous courses, giving talks, and running DEF CON’s Lock Bypass Village. He’s received various degrees in computer engineering, security, and forensics and comes from a broad background of work experience in cyber security, software development, anti-money laundering, and infectious disease detection.
@access_ctrl
https://github.com/bgraydon
https://www.youtube.com/channel/UCzZK3vjJL9rKNPXNoCPFO5g/videos
TEMPEST radio station
45 minutes | Tool
Paz Hameiri Hacker
Virtual only presentation
TEMPEST is a cyber security term that refers to the use of electromagnetic energy emissions generated by electronic devices to leak data out of a target device. The attacks may be passive (where the attacker receives the emissions and recovers the data) or active (where the attacker uses dedicated malware to target and emit specific data).
In this talk I present a new side channel attack that uses GPU memory transfers to emit electromagnetic waves which are then received and processed by the attacker. Software developed for this work encodes audio on one computer and transmits it to the reception equipment positioned fifty feet away. The signals are received and processed and the audio is decoded and played. The maximum bit rate achieved was 33kbit/s and more than 99% of the packets were received.
Frequency selection not only enables maximization of signal quality over distance, but also enables the attacker to receive signals from a specific computer when several computers in the area are active. The software developed demonstrates audio packets transfers, but other types of digital data may be transmitted using the same technique.
REFERENCES:
Eck W. “Electromagnetic radiation from video display units: an eavesdropping risk?” Computers and Security, 4, no. 4: 269–286, 1985.
Kuhn, M. G., and Anderson, R. J. Soft. “Tempest: Hidden Data Transmission Using Electromagnetic Emanations.” In Information Hiding (1998), ed. D. Aucsmith, vol. 1525 of Lecture Notes in Computer Science, (Springer): 124–142.
Thiele, E., “Tempest for Eliza.” 2001. http://www.erikyyy.de/tempest/.
Kania B., “VGASIG: FM radio transmitter using VGA graphics card.” 2009. http://bk.gnarf.org/creativity/vgasig/vgasig.pdf.
Guri M., Kedma G., Kachlon A., Elovici Y. “AirHopper: Bridging the air-gap between isolated networks and mobile phones using radio frequencies.” In Malicious and Unwanted Software: The Americas (MALWARE), 2014 9th International Conference on IEEE, 2014: 58–67.
2pkaqwtuqm2q7djg,”OVERCLOCKING TOOLS FOR NVIDIA GPUS SUCK, I MADE MY OWN”. 2015. https://1vwjbxf1wko0yhnr.wordpress.com/2015/08/10/overclocking-tools-for-nvidia-gpus-suck-i-made-my-own/
nvapioc project: https://github.com/Demion/nvapioc
SDRplay API Specification v3, https://www.sdrplay.com/docs/SDRplay_API_Specification_v3.pdf
Simon Rockliff’s Reed-Solomon encoding-decoding code at http://www.eccpage.com/rs.c
Paz Hameiri
Paz started his professional life 30 years ago, hacking games and developing tools in his teen years. Since then, he has worked in several companies, developing both hardware and software.
Paz has six years of experience with telecommunication systems design and circuits. He explored GPU hardware and software design in his Master’s thesis. For 12 years, Paz led multidisciplinary systems development as a systems engineer in an international homeland security company.
At home, Paz explores ideas he finds interesting. In 2019 he published his work on a body-tracking device that records keystrokes on a safe’s keypad.
Over-the-air remote code execution on the DEF CON 27 badge via Near Field Magnetic Inductance or World’s first NFMI exploitation, sorta or OTARCEDC27NFMIOMGWTFBBQ
45 minutes | Demo, Tool, Exploit
Seth Kintigh Hardware Security Engineer, Dell
Speaker(s) will be at DEF CON!
The DEF CON 27 badge employed an obscure form of wireless communication: Near Field Magnetic Inductance (NFMI). The badges were part of a contest and while poking through the firmware for hints I noticed a buffer overflow flaw. All it required to exploit it was an oversized packet… via a chip with no datasheet and no documentation on the proprietary protocol. Thus started a 2 year odyssey.
I used Software Defined Radio tools to study the signal’s modulations. I built a receiver in GNURadio and Python to convert signals into symbols, symbols obfuscated by a pattern that I had to deduce while only controlling a fraction of the bytes. Data was encoded in those symbols using proprietary convolution for even bits and Trellis Code Modulation for odd bits. I then reversed their bizarre CRC and wrote tools to craft and send packets. Using those tools I chained bugs in 2 chips and remotely crashed the badge. However, limitations in the NFMI protocol made more sophisticated attacks impossible.
But after a year and a half invested, I was not about to give up. I soldered leads to middle layer traces, extracted and reverse engineered the NFMI firmware, fixed their protocol, and patched a badge FW to patch the NFMI FW. At long last I achieved what may be the world’s first, over-the-air, remote code exploit via NFMI.
Seth Kintigh
Seth Kintigh learned to program at age 12 on an IBM PC jr and his grandmother taught him how to crack ciphers. His first hack was to get infinite lives and beat the Atari 2600 game Solaris. He earned a BS EE with minors in CS and physics and a MS EE with concentration in cryptography and information security from WPI. He worked 6 years as a hardware engineer and 17 in security. Hobbies include cracking historical ciphers and restoring a Victorian home.
Sneak into buildings with KNXnet/IP
45 minutes | Demo
Claire Vacherot Senior Security Auditor @ Orange Cyberdefense
Virtual only presentation
Building Management Systems control a myriad of devices such as lighting, shutters and HVAC. KNX (and by extension KNXnet/IP) is a common protocol used to interact with these BMS. However, the public’s understanding and awareness is lacking, and effective tooling is scarce all while the BMS device market keeps on growing.
The ability to craft arbitrary KNXnet/IP frames to interact with these often-insecure BMS provides an excellent opportunity in uncovering vulnerabilities in both the implementation of KNX as well as the protocol itself. From unpacking KNX at a lower level, to using a Python-based protocol crafting framework we developed to interact with KNXnet/IP implementations, in this talk we’ll go on a journey of discovering how BMS that implement KNXnet/IP work as well as how to interact with and fuzz them.
After this talk you could also claim that “the pool on the roof has a leak”!
REFERENCES:
KNX Standard v2.1
https://my.knx.org/fr/shop/knx-specifications?product_type=knx-specifications
Scapy
https://github.com/secdev/scapy
KNXmap
https://github.com/takeshixx/knxmap
Papers & talks:
in)security in building automation how to create dark buildings with light speed
Thomas Brandstetter and Kerstin Reisinger
Presented at BlackHat USA 2017
https://www.blackhat.com/docs/us-17/wednesday/us-17-Brandstetter-insecurity-In-Building-Automation-How-To-Create-Dark-Buildings-With-Light-Speed-wp.pdf
Hacking Intelligent Building — Pwning KNX & ZigBee Networks
HuiYu Wu and YuXiang Li (Tencent)
Presented at HITB Amsterdam 2018
https://conference.hitb.org/hitbsecconf2018ams/materials/D1T2%20-%20YuXiang%20Li,%20HuiYu%20Wu%20&%20Yong%20Yang%20-%20Hacking%20Intelligent%20Buildings%20-%20Pwning%20KNX%20&%20ZigBee%20Networks.pdf
Security in KNX or how to steal a skyscraper
Egor Litvinov
Presented at Zero Nights 2015
http://2015.zeronights.org/assets/files/20-Litvinov.pdf
HVACking: Understanding the Delta Between Security and Reality
Douglas McKee and Mark Bereza
Presented at Defcon 27, 2019
https://www.mcafee.com/blogs/other-blogs/mcafee-labs/hvacking-understanding-the-delta-between-security-and-reality/
Anomaly Detection in BACnet/IP managed Building Automation Systems
Matthew Peacock — 2019
https://ro.ecu.edu.au/cgi/viewcontent.cgi?article=3180&context=theses
Claire Vacherot
Claire Vacherot is a pentester at Orange Cyberdefense. She likes to test systems and devices that interact with the real world and is particularly interested in industrial and embedded device cybersecurity. As a former software developer, she never misses a chance to write scripts and tools.
Central bank digital currency, threats and vulnerabilities
45 minutes | Exploit
Ian Vitek Security, Sveriges Riksbank (Central bank of Sweden)
Speaker(s) will be at DEF CON!
What are the threats and vulnerabilities of a retail central bank digital currency (CBDC)? The central bank of Sweden has built a prototype of a retail CBDC system and I will run through the procurement requirements and design and point out where a two-tier CBDC need protection against attacks. The prototype is built on Corda Token SDK and I have during tests found reliable ways to exploit weaknesses in the design. The presentation will focus on the vulnerabilities that can crash the service that handles the tokens and permanently lock tokens rendering tokens and digital wallets useless. The presentation will also go into detail how tokens are validated and how information from all earlier transactions is needed for this. With D3.js and HTML5 I will visualize the token history (backchain) and describe how this can be a problem with GDPR and the Swedish bank secrecy regulation.
The presentation will end with a summary of identified threats and weaknesses of a two-tier retail central bank digital currency prototype and how to handle them. The goal of the presentation is to give the attendees insight of the security implications, challenges depending on the design and where an attack can be carried out and everything that cannot be missed when designing a CBDC.
REFERENCES:
https://www.ingwb.com/media/3024436/solutions-for-the-corda-security-and-privacy-trade-off_-whitepaper.pdf
https://d3js.org/
Ian Vitek
Ian Vitek has a background as a pentester but has worked with information security in the Swedish financial sector the last 10 years. Currently working with security of the Swedish retail central bank digital currency prototype at the Riksbank, the Swedish central bank. Interested in web application security, network layer 2 (the writer of macof), DMA attacks and local pin bypass attacks (found some on iPhone).
PunkSPIDER and IOStation: Making a Mess All Over the Internet
45 minutes | Demo,Tool
_hyp3ri0n aka Alejandro Caceres Director of Computer Network Exploitation at QOMPLX, former owner of Hyperion Gray
Jason Hopper Hacker
Speaker(s) will be at DEF CON!
We’ve been getting asked a lot for “that tool that was like Shodan but for web app vulns.” In particular WTF happened to it? Punkspider (formerly known as PunkSPIDER but renamed because none of us could remember where tf the capital letters go) was taken down a couple of years ago due to multiple ToS issues and threats. It was originally funded by DARPA. We weren’t sure in which direction to keep expanding, and it ended up being a nightmare to sustain. We got banned more than a 15 year old with a fake ID trying to get into a bar. It became a pain and hardly sustainable without a lot of investment in time and money. Each time we got banned it meant thousands of dollars and countless hours moving sh** around.
Now we’ve solved our problems and completely re-engineered/expanded the system. It is not only far more efficient with real-time distributed computing and checks for way more vulns, we had to take some creative ways through the woods — this presentation covers both the tool itself and the story of the path we had to take to get where it is, spoiler alert: it involves creating our own ISP and data center in Canada and integrating freely available data that anyone can get but most don’t know is available. Come play with us and see what the wild west of the web looks like and listen to our story, it’s fun and full of angry web developers. We’ll also be releasing at least 10s of thousands of vulnerabilities and will be taking suggestions from the audience on what to search. Fun vulns found get a t-shirt, super fun ones get a hoodie thrown at them.
REFERENCES:
https://www.youtube.com/watch?v=AbS_EGzkNgI (Shmoo 2013 talk)
https://hadoop.apache.org/
https://aws.amazon.com/kubernetes/
https://www.docker.com/
https://www.python.org/
https://www.apache.org/licenses/LICENSE-2.0
https://kafka.apache.org/
https://owasp.org/www-project-top-ten/
_hyp3ri0n aka Alejandro Caceres
Bio coming soon!
Jason Hopper
Bio coming soon!
New Phishing Attacks Exploiting OAuth Authentication Flows
45 minutes | Demo, Tool
Jenko Hwong Netskope Threat Research team
Speaker(s) will be at DEF CON!
OAuth 2.0 device authentication gives users on limited-input devices like TVs an easier way to authenticate against a cloud website/app by entering a code on a computer/phone. This authentication flow leads to new phishing attacks that:
— do not need server infrastructure — the login page is served by the authorization provider using their domain and cert
— do not require a client application — application identities can be reused/spoofed
— do not require user consent of application permissions
Since the phish attacks hijack oauth session tokens, MFA will be ineffective as the attacker does not need to reauthenticate. The ability to defend against these attacks is hindered by limited info and functionality to detect, mitigate, and prevent session token compromise.
I’ll demonstrate these new phishing attacks, access to sensitive user data, and lateral movement.
Defensive measures against these phishing attacks will be discussed, specifically the challenges in detection, mitigation, and prevention, and the overall lack of support for managing temporary credentials.
Open-source tools have been developed and will be used to demonstrate how users can:
— self-phish their organizations using these techniques
— audit security settings that help prevent/mitigate the attacks
REFERENCES:
1.0 Evolving Phishing Attacks
1.1 A Big Catch: Cloud Phishing from Google App Engine and Azure App Service:
https://www.netskope.com/blog/a-big-catch-cloud-phishing-from-google-app-engine-and-azure-app-service
1.2 Microsoft Seizes Malicious Domains Used in Mass Office 365 Attacks:
https://threatpost.com/microsoft-seizes-domains-office-365-phishing-scam/157261/
1.3 Phishing Attack Hijacks Office 365 Accounts Using OAuth Apps:
https://www.bleepingcomputer.com/news/security/phishing-attack-hijacks-office-365-accounts-using-oauth-apps/
1.4 Office 365 Phishing Attack Leverages Real-Time Active Directory Validation:
https://threatpost.com/office-365-phishing-attack-leverages-real-time-active-directory-validation/159188/
1.5 Demonstration — Illicit Consent Grant Attack in Azure AD:
https://www.nixu.com/blog/demonstration-illicit-consent-grant-attack-azure-ad-office-365
https://securecloud.blog/2018/10/02/demonstration-illicit-consent-grant-attack-in-azure-ad-office-365/
1.6 Detection and Mitigation of Illicit Consent Grant Attacks in Azure AD:
https://www.cloud-architekt.net/detection-and-mitigation-consent-grant-attacks-azuread/
1.7 HelSec Azure AD write-up: Phishing on Steroids with Azure AD Consent Extractor:
https://securecloud.blog/2019/12/17/helsec-azure-ad-write-up-phishing-on-steroids-with-azure-ad-consent-extractor/ 1.8 Pawn Storm Abuses OAuth In Social Engineering Attack:
https://www.trendmicro.com/en_us/research/17/d/pawn-storm-abuses-open-authentication-advanced-social-engineering-attacks.html
2.0 OAuth Device Code Flow
2.1 OAuth 2.0 RFC:
https://tools.ietf.org/html/rfc6749#page-24
2.2 OAuth 2.0 for TV and Limited-Input Device Applications:
https://developers.google.com/identity/protocols/oauth2/limited-input-device
2.3 OAuth 2.0 Scopes for Google APIs:
https://developers.google.com/identity/protocols/oauth2/scopes
2.2 Introducing a new phishing technique for compomising Office 365 accounts:
https://o365blog.com/post/phishing/#oauth-consent
2.3. Office Device Code Phishing:
https://gist.github.com/Mr-Un1k0d3r/afef5a80cb72dfeaa78d14465fb0d333
3.0 Additional OAuth Research Areas
3.1 Poor OAuth implementation leaves millions at risk of stolen data:
https://searchsecurity.techtarget.com/news/450402565/Poor-OAuth-implementation-leaves-millions-at-risk-of-stolen-data
3.2 How did a full access OAuth token get issued to the Pokémon GO app?:
https://searchsecurity.techtarget.com/answer/How-did-a-full-access-OAuth-token-get-issued-to-the-Pokemon-GO-app
===
Jenko Hwong
Jenko Hwong is on the Netskope Threat Research team, focusing on cloud threats/vectors. He’s spent time in engineering and product roles at various security startups in vulnerability scanning, AV/AS, pen-testing/exploits, L3/4 appliances, threat intel, and windows security.
Hacking the Apple AirTags
45 minutes | Demo, Tool
Thomas Roth Hacker
Speaker(s) will be at DEF CON!
Apple’s AirTags enable tracking of personal belongings. They are the most recent and cheapest device interacting with the Apple ecosystem. In contrast to other tracking devices, they feature Ultrawide-band precise positioning and leverage almost every other Apple device within the Find My localization network.
Less than 10 days after the AirTag release, we bypassed firmware protections by glitching the nRF52 microcontroller. This opens the AirTags for firmware analysis and modification. In this talk, we will explain the initial nRF52 bypass as well as various hacks built on top of this. In particular, AirTags can now act as phishing device by providing malicious links via the NFC interface, be cloned and appear at a completely different location, used without privacy protections that should alert users as tracking protection, act as low-quality microphone by reutilizing the accelerometer, and send arbitrary data via the Find My network. Besides these malicious use cases, AirTags are now a research platform that even allows access to the new Ultrawide-band chip U1.
REFERENCES:
LimitedResults nRF52 APPROTECT Bypass:
https://limitedresults.com/2020/06/nrf52-debug-resurrection-approtect-bypass/
Positive Security’s Send My Research for sending arbitrary data via the find my network:
https://positive.security/blog/send-my
Colin O’Flynn’s notes on the AirTag Hardware:
https://github.com/colinoflynn/airtag-re
Thomas Roth
Thomas Roth, also known as stacksmashing, is a security researcher from Germany with a focus on embedded devices: From hacking payment terminals, crypto wallets, secure processor, the Nintendo Game & Watch, up to Apple’s AirTag he loves to explore embedded & IoT security. On how YouTube channel “stacksmashing” he attempts to make reverse-engineering & hardware hacking more accessible.
@ghidraninja
https://youtube.com/stacksmashing
HACKERS INTO THE UN? Engaging in the cyber discussions on war & peace — DEF CON Policy Panel
45 min panel
Alexander Klimburg DEF CON Policy Dept, Panel Moderator
Chris Painter Global Forum of Cyber Expertise, Former head of US cyber diplomacy
Lauren Zabierek Harvard Belfer Cyber Project
Van Horenbeeck Forum of Incident Responders and Security Teams (VIRTUAL)
Sheetal Kumar Global Partners Digital (VIRTUAL)
Bill “Woody” Woodcock Chair of the Foundation Council, Quad9, Packet Clearing House
Speaker(s) will be at DEF CON!
As if 2020 and 2021 were not bad enough, the Covid-19 pandemic seemed to have been accompanied by a new rash of bad cyber- attacks on major platforms like Solarwinds and Microsoft, infrastructures worldwide subverted in ransomware campaigns, and even the very organizations researching and fighting the pandemic have been hit.
Meanwhile, the hard work of cyber diplomacy continues, with talks on war and peace in the United Nations reaching a new stage as two working groups presented their final report and a third one is in the process of being born. Mostly the topics are on establishing norms on cyber behavior, rules of the road of what states can do in cyberspace. But where are the hackers in all this? The Internet is famously not run by intergovernmental organizations, so the companies, civil society groups and others should somehow be involved — and one of the UN processes did in fact make a small step in that direction. But the staid ways of pin-striped cyber are hard to change. What is the best way for the community to engage?
A Look Inside Security At The New York Times Or A Media Security Primer For Hackers
45 minutes
Jesse “Agent X” Krembs
Speaker(s) will be at DEF CON!
This talk will cover the unique threats and challenges of working in information security for a news organization. Some best practices for journalists, hard technical problems facing media security, and how hackers can get involved. This talk is for both hackers and journalists.
Jesse “Agent X” Krembs
Jesse Krembs is a long term Def Con goon and now a staff information security analyst at The New York Times. He provides security support to journalists, and staff globally. He’s had a variety of jobs over his lifetime, working as a bike messenger, a caterer, a webmaster for a brewery, a wireless engineer, and doing even security work for the phone company. He leads the Def Con 4 X 5K, and climbs rocks for fun.
Hi! I’m DOMAIN\Steve, please let me access VLAN2
45 minutes | Demo, Tool, Exploit
Justin Perdok Security Specialist, Orange Cyberdefense Netherlands
Virtual only presentation
By responding to probing requests made by Palo Alto and SonicWALL firewalls, it’s possible to apply security policies to arbitrary IPs on the network, allowing access to segmented resources.
Segmentation using firewalls is a critical security component for an organization. To scale, many firewall vendors have features that make rule implementation simpler, such as basing effective access on a user identity or workstation posture. Security products that probe client computers often have their credentials abused by either cracking a password hash, or by relaying an authentication attempt elsewhere. Prior work by Esteban Rodriguez and by Xavier Mertens cover this. In this talk I will show a new practical attack on identity-based firewalls to coerce them into applying chosen security policies to arbitrary IPs on a network by spoofing logged in users instead of cracking passwords.
Logged on user information is often gathered using the WKST (Workstation Service Remote Protocol) named pipe. By extending Impacket with the ability to respond to these requests, logged on users on a device can be spoofed, and arbitrary firewall rules applied.
We will dive into the details of how client probing has historically been a feature that should be avoided while introducing a new practical attack to emphasize that fact.
REFERENCES
https://www.coalfire.com/the-coalfire-blog/august-2018/the-dangers-client-probing-on-palo-alto-firewalls
https://isc.sans.edu/forums/diary/The+Risk+of+Authenticated+Vulnerability+Scans/24942/
https://github.com/SecureAuthCorp/impacket
https://www.rapid7.com/blog/post/2014/10/14/palo-alto-networks-userid-credential-exposure/
https://knowledgebase.paloaltonetworks.com/KCSArticleDetail?id=kA10g000000ClXHCA0
Justin Perdok
Justin is a Security Specialist at Orange Cyberdefense. Prior to working in ‘The Cybers’ he has worked at multiple MSPs as a jack of all trades with a focus on security and automation. Stuck in his old ways he’s always trying to learn new things; Followed up by him spending 6 hours automating the ‘new thing’ instead of relying on 5 minutes of manual labor.
Fuzzing Linux with Xen
45 minutes | Demo, Tool
Tamas K Lengyel Senior Security Researcher, Intel
Virtual only presentation
Last year we’ve successfully upstreamed a new feature to Xen that allows high-speed fuzzing of virtual machines (VMs) using VM-forking. Recently through collaboration with the Xen community external monitoring of VMs via Intel(r) Processor Trace has also been upstreamed. Combined with the native Virtual Machine Introspection (VMI) capability Xen now provides a unique platform for fuzzing and binary analysis.
To illustrate the power of the platform we’ll present the details of a real-world fuzzing operation that targeted Linux kernel-modules from an attack-vector that has previously been hard to reach: memory exposed to devices via Direct Memory Access (DMA) for fast I/O. If the input the kernel reads from DMA-exposed memory is malformed or malicious — what could happen?
So far we discovered: 9 NULL-pointer dereferences; 3 array index out-of-bound accesses; 2 infinite-loops in IRQ context and 2 instances of tricking the kernel into accessing user-memory but thinking it is kernel memory. The bugs have been in Linux for many years and were found in kernel modules used by millions of devices. All bugs are now fixed upstream.
This talk will walk you through how the bugs were found: what process we went through to identify the right code-locations; how we analyzed the kernel source and how we analyzed the runtime of the kernel with Xen to pinpoint the input points that read from DMA. The talk will explain the steps required to attach a debugger through the hypervisor to collect kernel crash logs and how to perform triaging of bugs via VM-fork execution-replay, a novel technique akin to time-travel debugging. Finally, we’ll close with the release of a new open-source tool to perform full-VM taint analysis using Xen and Intel(r) Processor Trace.
REFERENCES:
https://github.com/intel/kernel-fuzzer-for-xen-project
https://www.youtube.com/watch?v=3MYo8ctD_aU
Tamas K Lengyel
Tamas works as Senior Security Researcher at Intel. He received his PhD in Computer Science from the University of Connecticut where he built hypervisor-based malware-analysis and collection tools. In his free time he is maintainer of the Xen Project Hypervisor’s VMI subsystem, LibVMI & the DRAKVUF binary analysis project. He currently serves as the Chief Research Officer at The Honeynet Project, a leading international non-profit organization that coordinates the development of open-source tools to fight against malware. Tamas gave prior talks at conferences such as BlackHat, CCC and Hacktivity.
DoS: Denial of Shopping — Analyzing and Exploiting (Physical) Shopping Cart Immobilization Systems
20 minutes
Joseph Gabay Hacker
Speaker(s) will be at DEF CON!
Many supermarkets and shopping centers have implemented devices that “lock” their shopping carts if they’re taken outside of an approved boundary (e.g, a parking lot). This talk examines some of the technology that’s used to do this, as well as ways to capture and spoof the control signals to defeat these devices.
We will go over the anatomy of remotely lockable shopping cart wheels, their basic theory, and get into how they’re controlled. We’ll deconstruct some samples of the lock and unlock signals captured using a homemade antenna and a HackRF, and briefly discuss methods of rebroadcasting them — as well as the challenges inherent to this process.
DISCLAIMER
This talk is the result of a personal project.
Any views, opinions, or research presented in this talk are personal and belong solely to the presenter. They do not represent or reflect those of any person, institution, or organization that the presenter may or may not be associated with in a professional or personal capacity unless explicitly stated otherwise.
REFERENCES
— The ARRL handbook for radio communications, 2007. Newington, CT: American Radio Relay League, 2006. Print.
— https://www.tmplab.org/2008/06/18/consumer-b-gone/
— http://www.woodmann.com/fravia/nola_wheel.htm
-The wonderful people over at /r/rfelectronics
-FCC.gov
Joseph Gabay
Joseph is a robotics engineer in Boston, Massachusetts where he works on a variety of projects ranging from electromechanical designs to embedded systems.
His passion lies in further understanding the way the world works and uncovering the small secrets that we encounter in our day to day lives. This project started as an idle curiosity and grew into an opportunity to further explore the complex and deep world of RF communications and embedded systems.
Joseph is an avid part of the local maker community, with extensive experience in 3D printing, rapid-fabricobbling, and breaking stuff for fun and profit. Outside of his day job, he enjoys woodworking and metalworking and is constantly collecting new hobbies and interests.
No Key? No PIN? No Combo? No Problem! P0wning ATMs For Fun and Profit
45 minutes | Demo
Roy Davis Senior Security Engineer, Zoom Video Communications
Speaker(s) will be at DEF CON!
Since the late great Barnaby Jack gave us “Jack Potting” in the late 2000s, there have been several talks on ATM network attacks, USB port attacks, and digital locks attacks which apply to several brands of ATM safes. In this session, I’ll discuss and demonstrate how most of these known attack vectors have been remediated, while several fairly simple attacks against the machine and the safe still remain. We’ll dive into how ATMs work, the steps I went through to become a “licenced ATM operator” which enabled my research, and how I identified the vulnerabilities. I’ll show how, with very little technical expertise and 20 minutes, these attacks lead directly past “secure” and allow attackers to collect a lot more than $200.
REFERENCES
Barnaby Jack — “Jackpotting Automated Teller Machines” — (2010) from DEFCON — https://www.youtube.com/watch?v=FkteGFfvwJ0
Weston Hecker — “Hacking Next-Gen ATM’s From Capture to Cashout” — (2016) from DEFCON — https://www.youtube.com/watch?v=1iPAzBcMmqA
Trey Keown and Brenda So — “Applied Cash Eviction through ATM Exploitation” (2020) from DEFCON — https://www.youtube.com/watch?v=dJNLBfPo2V8
Triton — “Terminal Communications Protocol And Message Format Specification” (2004) from Complete ATM Services — tinyurl.com/7nf2fdy5
Rocket ATM — “Hyosung ATM Setup Part 1 — Step by Step” (2018) from Rocket ATM — https://www.youtube.com/watch?v=abylmrBkOGM&t=3s
Rocket ATM — “Hyosung ATM Setup Part 2 — Step by Step” (2018) from Rocket ATM — https://www.youtube.com/watch?v=IM9ZG46fwL8
Hyosung — “NH2600 Service Manual v1.0” (2013) From Prineta — https://tinyurl.com/c6jd4hd9
Hyosung — “NH2700 Operator Manual v1.2” (2010) From AtmEquipment.com — https://tinyurl.com/rp2cad8
Roy Davis
Roy Davis is a security researcher and engineer with 15 years of pentesting, security research and programming experience. He has worked on security teams at Zoom, Salesforce, Apple, Barclays Bank, and Thomson Reuters. He holds a B.S. degree in Computer Science from Purdue University and an M.S. in Cybersecurity and Digital Forensics from WGU. Roy has presented at several security conferences from 2008 to his most recent talk at the “HackerOne Security@” conference in San Francisco.
@hack_all_things
https://www.linkedin.com/in/roy-davis/
https://www.davisinfosec.com
Extension-Land: exploits and rootkits in your browser extensions
45 minutes | Demo, Tool, Exploit
Barak Sternberg Senior Security Researcher
Speaker(s) will be at DEF CON!
Browser extensions are installed anywhere, they serve as an integral part of our day-to-day web routine, from AdBlockers to Auto-Translators. But — do we know what is running inside of them? Do we know what goes deep-down inside their communication routines? How do they use their internal API’s? And how do their different JS execution contexts work?
In this session, I will explore these unique internal extension API’s, hidden attack-surfaces and show how these concepts can be broken & exploited using new ways! I start showing how an attacker can “jump” from one low-permissions chrome-app/extension to another, hence elevating its permissions. Then, I will show how to gain full “browser-persistency” inside extensions’ background-scripts context.
Chaining it all together, I show how attacker, starting from low permissions chrome-app, gains a fully-armed “extension-rootkit”, a persistent JS-malware running inside of a “good” extension, along with C&C features, JS injection techniques to any tab/origin, obfuscation-techniques and more. Eventually, I will present a generic technique, targeting all chrome-users, for taking over any previously installed chrome extension and implant an “extension-rootkit” in it.
REFERENCES:
[1] Chrome Developers: Chrome extensions API Reference, https://developer.chrome.com/docs/extensions/reference/
[2] Chrome Developers: Chrome extensions Manfiest v2/v3 Security References, https://developer.chrome.com/docs/extensions/mv2/getstarted/ & https://developer.chrome.com/docs/extensions/mv3/security/
[3] “Websites Can Exploit Browser Extensions to Steal User Data”, 2019 — https://www.securityweek.com/websites-can-exploit-browser-extensions-steal-user-data / https://www-sop.inria.fr/members/Doliere.Some/papers/empoweb.pdf
[4] “Web Browser Extension User-Script XSS Vulnerabilities”, 2020 — https://ieeexplore.ieee.org/document/9251185
[5] “Detecting DOM-Sourced Cross-Site Scripting in Browser Extensions”, 2017 — https://ieeexplore.ieee.org/document/8094406
[6] “Attacking browser extensions”, Nicolas Golubovic, 2016 — https://golubovic.net/thesis/master.pdf
[7] “A Combined Static and Dynamic Analysis Approach to Detect Malicious Browser Extensions”, 2018 — https://www.hindawi.com/journals/scn/2018/7087239/
[8] “Chrome Extensions: Threat Analysis and Countermeasures”, 2012 — https://citeseerx.ist.psu.edu/viewdoc/download?doi=10.1.1.374.8978&rep=rep1&type=pdf
[9] “Extension Breakdown: Security Analysis of Browsers Extension Resources Control Policies”, Usenix Security 2017 — https://www.usenix.org/system/files/conference/usenixsecurity17/sec17-sanchez-rola.pdf
[10] “Protecting Browsers from Extension Vulnerabilities”, 2010 — https://static.googleusercontent.com/media/research.google.com/en//pubs/archive/38394.pdf
Barak Sternberg
Barak Sternberg is an Experienced Security Researcher who specializes in Offensive Security. Founder of “WildPointer”, and previously an author at SentinelLabs (“Hacking smart devices for fun and profit”, Defcon 2020 IoT Village) and leading innovative cybersecurity research.
Barak spent more than six-years at Unit 8200, IDF, as a team leader of 5–10 security researchers. He is highly skilled in offensive cyber-security, from vulnerabilities research in various areas: Linux, IoT, embedded and web-apps to analyzing malware in the wild. Barak is also a CTF’s addict, posting write-ups and technical vulnerabilty analysis in its blog (livingbeef.blogspot.com). Barak also acquires BSc, MSC (in CS) focused on algorithms from Tel-Aviv University and a DJ certificate from BPM college.
@livingbeef
https://livingbeef.blogspot.com/
https://www.linkedin.com/in/barakolo/
https://www.barakolo.me
Why does my security camera scream like a Banshee? Signal analysis and RE of a proprietary audio-data encoding protocol
45 minutes | Demo, Tool
Rion Carter
Speaker(s) will be at DEF CON!
All I wanted was a camera to monitor my pumpkin patch for pests, what I found was a wireless security camera that spoke with an accent and asked to speak with my fax machine. Join me as I engage in a signals analysis of the Amiccom 1080p Outdoor Security Camera and hack the signal to reverse engineer the audio tones used to communicate and configure this inexpensive outdoor camera. This journey takes us through spectrum-analysis, APK decompiling, tone generation in Android and the use of Ghidra for when things REALLY get hairy.
REFERENCES:
— JADX: Dex to Java Decompiler — https://github.com/skylot/jadx
— Efficiency: Reverse Engineering with ghidra — http://wapiflapi.github.io/2019/10/10/efficiency-reverse-engineering-with-ghidra.html
— Guide to JNI (Java Native Interface) — https://www.baeldung.com/jni
— JDSP — Digital Signal Processing in Java — https://psambit9791.github.io/jDSP/transforms.html
— Understanding FFT output — https://stackoverflow.com/questions/6740545/understanding-fft-output
— Spectral Selection and Editing — Audacity Manual — https://manual.audacityteam.org/man/spectral_selection.html
— Edit>Labelled Audio>everything greyed out — https://forum.audacityteam.org/viewtopic.php?t=100856
— Get a spectrum of frequencies from WAV/RIFF using linux command line — https://stackoverflow.com/questions/21756237/get-a-spectrum-of-frequencies-from-wav-riff-using-linux-command-line
— How to interpret output of FFT and extract frequency information — https://stackoverflow.com/questions/21977748/how-to-interpret-output-of-fft-and-extract-frequency-information?rq=1
— Calculate Frequency from sound input using FFT — https://stackoverflow.com/questions/16060134/calculate-frequency-from-sound-input-using-fft?rq=1
— Intorduction — Window Size — https://support.ircam.fr/docs/AudioSculpt/3.0/co/Window%20Size.html
— Android: Sine Wave Generation — https://stackoverflow.com/questions/11436472/android-sine-wave-generation
— Android Generate tone of a specific frequency — https://riptutorial.com/android/example/28432/generate-tone-of-a-specific-frequency
— Android Tone Generator — https://gist.github.com/slightfoot/6330866
— Android: Audiotrack to play sine wave generates buzzing noise — https://stackoverflow.com/questions/23174228/android-audiotrack-to-play-sine-wave-generates-buzzing-noise
Rion Carter
Rion likes to solve interesting problems- the more esoteric and niche the better! He has varied interests ranging from software development and reverse-engineering to baking and recipe hacking. Rion currently works in DevSecOps where he and his colleagues wonder how they’ll be rebranded next (DevSecBizFinOps?). Rumor has it that he bakes a mean batch of fudge brownies.
Robots with lasers and cameras (but no security): Liberating your vacuum from the cloud
45 minutes | Tool, Exploit
Dennis Giese Hacker
Speaker(s) will be at DEF CON!
Vacuum robots are becoming increasingly popular and affordable as their technology grows ever more advanced, including sensors like lasers and cameras. It is easy to imagine interesting new projects to exploit these capabilities. However, all of them rely on sending data to the cloud. Do you trust the companies promise that no video streams are uploaded to the cloud and that your personal data is safe? Why not collect the dust with open-source software?
I previously showed ways to root robots such as Roborock and Xiaomi, which enabled owners to use their devices safely with open-source home automation. In response, vendors began locking down their devices with technologies like Secure Boot, SELinux, LUKS encrypted partitions and custom crypto that prevents gaining control over our own devices. This talk will update my newest methods for rooting these devices.
The market of vacuum robots expanded in the past 2 years. In particular, the Dreame company has recently released many models with interesting hardware, like ToF cameras and line lasers. This can be a nice alternative for rooting. I will show easy ways to get root access on these devices and bypass all security. I will also discuss backdoors and security issues I discovered from analysis. You will be surprised what the developers left in the firmware.
REFERENCES:
Unleash your smart-home devices: Vacuum Cleaning Robot Hacking (34C3)
https://dontvacuum.me/talks/34c3-2017/34c3.html
Having fun with IoT: Reverse Engineering and Hacking of Xiaomi IoT Devices
https://dontvacuum.me/talks/DEFCON26/DEFCON26-Having_fun_with_IoT-Xiaomi.html
https://linux-sunxi.org/Main_Page
Dennis Giese
Dennis is a PhD student and a cybersecurity researcher at Northeastern University. He was a member of one european ISP’s CERT for several years.
While being interested in physical security and lockpicking, he enjoys applied research and reverse engineering malware and all kinds of devices.
His most known projects are the rooting and hacking of various vacuum robots
Old MacDonald Had a Barcode, E-I-E-I CAR
45 minutes | Demo
Richard Henderson
Speaker(s) will be at DEF CON!
For decades, the EICAR test string has been used by antivirus and security vendors to safely test their detection engines without having to use live virulent samples which could cause harm. What would happen if you took that string, encoded it into a machine readable format like a QR code and started scanning various devices with the QR code? This talk shows how there are a lot of systems out there that aren’t expecting an input string like EICAR and how many of them just collapse when shown the code. We will also discuss the types of systems you can target and how you may be able to extend this to more than a nuisance attack.
REFERENCES:
EICAR test string: https://www.eicar.org/?page_id=3950
EICAR wikipedia entry: https://en.wikipedia.org/wiki/EICAR_test_file
QR codes: https://en.wikipedia.org/wiki/QR_code
Risks surrounding QR codes: https://en.wikipedia.org/wiki/QR_code#Risks
Richard Henderson
Richard Henderson is a writer, researcher, and ham radio/electronics nerd who has worked in infosec and technology for almost two decades. Richard has taught multiple times at DEF CON and leads the annual DEF CON Ham Radio Fox Hunt Contest. Richard is currently co-authoring a book on cybersecurity for ICS/Scada systems.
Instrument and Find Out: Writing Parasitic Tracers for High(-Level) Languages
20 minutes | Demo, Tool
Jeff Dileo Technical Director, NCC Group
Virtual only presentation
Modern programming languages are, more and more, being designed not just around performance, ease-of-use, and (sometimes) security, but also performance monitoring and introspectability. But what about the languages that never adopted such concepts from their peers? Or worse, what about the languages that tacked on half-hearted implementations as an afterthought? The answer is simple, you write your own and instrument them into the language dynamically.
In this talk, we will discuss the process for developing generalized parasitic tracers targeting specific programming languages and runtimes using Ruby as our case study. We will show how feasible it is to write external tracers targeting a language and its runtime, and discuss best practices for supporting different versions over time.
REFERENCES:
* https://github.com/ruby/ruby
* https://frida.re/docs/javascript-api/
Jeff Dileo
Jeff Dileo (chaosdata) is a security consultant by day, and sometimes by night. He hacks on embedded systems, mobile apps and devices, web apps, and complicated things that don’t have names. He likes candy and arguing about text editors and window managers he doesn’t actually use.
The Agricultural Data Arms Race: Exploiting a Tractor Load of Vulnerabilities In The Global Food Supply Chain.
20 minutes | Demo, Exploit
Sick Codes
Virtual only presentation
How I hacked the entire American Food Supply Chain over the course of 3 months, assembled a team of hacker strangers, and how we used a “full house” of exploits on almost every aspect of the agriculture industry. See the process in which it happened, the private exploits we used, the vectors we attacked from, and how it could happen again, or be happening right now.
How the ongoing analytics arms race affects everyone, and how Tractor companies have metastasized into Tech companies, with little to no cyber defenses in place. Learn how farms are not like they used to be; telemetry, crop & yield analytics, and more telemetry.
REFERENCES:
https://github.com/sickcodes/Docker-OSX
https://github.com/sickcodes/osx-serial-generator
https://www.vice.com/en/article/akdmb8/open-source-app-lets-anyone-create-a-virtual-army-of-hackintoshes
https://www.bleepingcomputer.com/news/security/python-also-impacted-by-critical-ip-address-validation-vulnerability/
https://sick.codes/sick-2021-012/
https://sick.codes/sick-2021-031/
https://sick.codes/leaky-john-deere-apis-serious-food-supply-chain-vulnerabilities-discovered-by-sick-codes-kevin-kenney-willie-cade/
https://www.vice.com/en/article/4avy8j/bugs-allowed-hackers-to-dox-all-john-deere-owners
https://www.youtube.com/watch?v=rB_SleNKBus
wabaf3t https://twitter.com/wabafet1
D0rkerDevil https://twitter.com/D0rkerDevil
ChiefCoolArrow https://twitter.com/ChiefCoolArrow
johnjhacking https://twitter.com/johnjhacking
rej_ex https://twitter.com/rej_ex
w0rmer https://twitter.com/0x686967
https://climate.com/press-releases/transform-data-into-value-with-climate-fieldview/14
https://www.agriculture.com/news/business/john-deere-to-acquire-precision-plting_5-ar50937
https://www.reuters.com/article/us-monsanto-m-a-deere-idUSKBN17X2FZ
https://twitter.com/sickcodes/status/1385218039734423565?s=20
Sick Codes
Sick Codes: I am a Hacker, an Independent Security Researcher, an Australian, and an Open Source maintainer. I regularly publish nasty vulnerabilities in everyone’s favorite products, from all the best vendors. I’ve published CVEs in Smart TV’s, Browsers, missile design software, and entire programming languages. Freelance automation specialist by day and hacker by trade. I publish weaponized code on GitHub, namely Docker-OSX, which was my first big “thing,” which now has 15k stars, and my biggest project, Docker-OSX has over 100,000 downloads on DockerHub.
@sickcodes
https://github.com/sickcodes
https://www.linkedin.com/in/sickcodes/
https://sick.codes

